狨諦俴
Connection Banner:
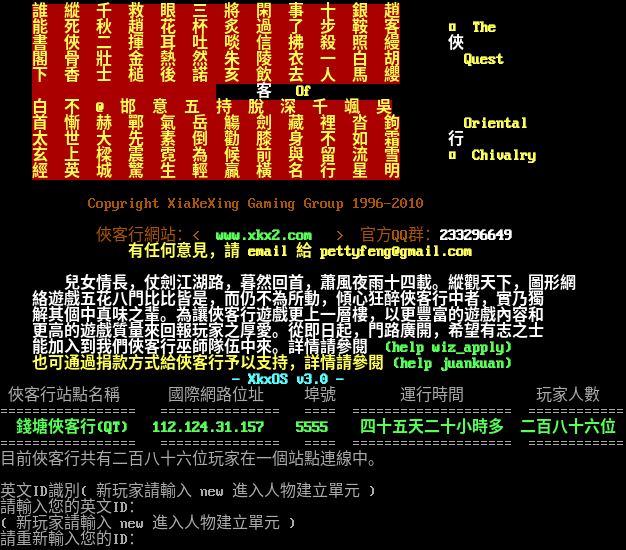
Server URLs
- Telnet: telnet://112.124.31.157:5555
- Website: www.xkx2.com
Server Info
Players online: 286 [1]
Uptime: 45 days
Server Location: 🇨🇳 China (GeoIP)
Encoding: big5
This server uses a legacy encoding:
telnetlib3-client --encoding big5 --force-binary 112.124.31.157 5555
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: No
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 8 other servers.
Options offered by server: MSSP, ZMP
Options requested from client: GMCP, MXP, NAWS, NEW_ENVIRON, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "33ebb6bbdfcdff81",
"fingerprint-data": {
"offered-options": [
"MSSP",
"ZMP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"SGA",
"STATUS"
],
"requested-options": [
"GMCP",
"MXP",
"NAWS",
"NEW_ENVIRON",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Ok, use \u001b[1;32mBIG5\u001b[0;0m code\u3002\r\n\r\n\u001b[2J\u001b[33m\r\n \u001b[41;1m\u8ab0 \u7e31 \u5343 \u6551 \u773c \u4e09 \u5c07 \u9591 \u4e8b \u5341 \u9280 \u8d99\u001b[37;0m\u001b[33m\r\n \u001b[41;1m\u80fd \u6b7b \u79cb \u8d99 \u82b1 \u676f \u7099 \u904e \u4e86 \u6b65 \u978d \u5ba2\u001b[37;0m\u001b[1;37m\u001b[33m \u25a1 The\r\n \u001b[41;1m\u66f8 \u4fe0 \u4e8c \u63ee \u8033 \u5410 \u5556 \u4fe1 \u62c2 \u6bba \u7167 \u7e35\u001b[37;0m \u001b[1;37m \u4fe0\u001b[37;0m\u001b[33m\r\n \u001b[41;1m\u95a3 \u9aa8 \u58ef \u91d1 \u71b1 \u7136 \u6731 \u9675 \u8863 \u4e00 \u767d \u80e1\u001b[37;0m\u001b[1;37m\u001b[33m Quest\r\n \u001b[41;1m\u4e0b \u9999 \u58eb \u69cc \u5f8c \u8afe \u4ea5 \u98f2 \u53bb \u4eba \u99ac \u7e93\u001b[37;0m\u001b[33m\r\n \u001b[41;1m \u001b[37;0m \u001b[1;37m \u5ba2\u001b[37;0m\u001b[1;37m\u001b[33m Of\r\n \u001b[41;1m\u767d \u4e0d \udc9f@ \u90af \u610f \u4e94 \u6301 \u812b \u6df1 \u5343 \u98af \u5433\u001b[37;0m\u001b[33m\r\n \u001b[41;1m\u9996 \u615a \u8d6b \u9132 \u6c23 \u5cb3 \u89f4 \u528d \u85cf \u88e1 \u6c93 \u9264\u001b[37;0m\u001b[1;37m\u001b[33m Oriental\r\n \u001b[41;1m\u592a \u4e16 \u5927 \u5148 \u7d20 \u5012 \u52f8 \u819d \u8eab \u4e0d \u5982 \u971c\u001b[37;0m \u001b[1;37m \u884c\u001b[37;0m\u001b[33m\r\n \u001b[41;1m\u7384 \u4e0a \u6a11 \u9707 \u9713 \u70ba \u5019 \u524d \u8207 \u7559 \u6d41 \u96ea\u001b[37;0m\u001b[1;37m\u001b[33m \u25a1 Chivalry\r\n \u001b[41;1m\u7d93 \u82f1 \u57ce \u9a5a \u751f \u8f15 \u8d0f \u6a6b \u540d \u884c \u661f \u660e\u001b[37;0m\u001b[33m\r\n\r\n \u001b[33m Copyright XiaKeXing Gaming Group 1996-2010 \u001b[37;0m\r\n\r\n \u001b[33m\u4fe0\u5ba2\u884c\u7db2\u7ad9\uff1a< \u001b[1;32m www.xkx2.com \u001b[37;0m\u001b[33m >\u001b[37;0m \u001b[33m\u5b98\u65b9QQ\u7fa4\uff1a\u001b[1;37m233296649\r\n \u001b[33m\u6709\u4efb\u4f55\u610f\u898b\uff0c\u8acb email \u7d66 pettyfeng@gmail.com\u001b[37;0m\r\n\r\n\u001b[1;37m \u5152\u5973\u60c5\u9577\uff0c\u4ed7\u528d\u6c5f\u6e56\u8def\uff0c\u66ae\u7136\u56de\u9996\uff0c\u856d\u98a8\u591c\u96e8\u5341\u56db\u8f09\u3002\u7e31\u89c0\u5929\u4e0b\uff0c\u5716\u5f62\u7db2\r\n \u7d61\u904a\u6232\u4e94\u82b1\u516b\u9580\u6bd4\u6bd4\u7686\u662f\uff0c\u800c\u4ecd\u4e0d\u70ba\u6240\u52d5\uff0c\u50be\u5fc3\u72c2\u9189\u4fe0\u5ba2\u884c\u4e2d\u8005\uff0c\u5be6\u4e43\u7368\r\n \u89e3\u5176\u500b\u4e2d\u771f\u5473\u4e4b\u8f29\u3002\u70ba\u8b93\u4fe0\u5ba2\u884c\u904a\u6232\u66f4\u4e0a\u4e00\u5c64\u6a13\uff0c\u4ee5\u66f4\u8c50\u5bcc\u7684\u904a\u6232\u5167\u5bb9\u548c\r\n \u66f4\u9ad8\u7684\u904a\u6232\u8cea\u91cf\u4f86\u56de\u5831\u73a9\u5bb6\u4e4b\u539a\u611b\u3002\u5f9e\u5373\u65e5\u8d77\uff0c\u9580\u8def\u5ee3\u958b\uff0c\u5e0c\u671b\u6709\u5fd7\u4e4b\u58eb\r\n \u80fd\u52a0\u5165\u5230\u6211\u5011\u4fe0\u5ba2\u884c\u5deb\u5e2b\u968a\u4f0d\u4e2d\u4f86\u3002\u8a73\u60c5\u8acb\u53c3\u95b1 \u001b[1;32m(help wiz_apply)\u001b[33m\r\n \u4e5f\u53ef\u901a\u904e\u6350\u6b3e\u65b9\u5f0f\u7d66\u4fe0\u5ba2\u884c\u4e88\u4ee5\u652f\u6301\uff0c\u8a73\u60c5\u8acb\u53c3\u95b1 \u001b[1;32m(help juankuan)\r\n \u001b[33m\u001b[37;0m\u001b[1;36m\t - XkxOS v3.0 -\r\n\u001b[0;0m \u4fe0\u5ba2\u884c\u7ad9\u9ede\u540d\u7a31\t \u570b\u969b\u7db2\u8def\u4f4d\u5740 \u57e0\u865f\t \u904b\u884c\u6642\u9593\t \u73a9\u5bb6\u4eba\u6578\r\n================= =============== ==== ==================== ============\r\n\u001b[1;32m \u9322\u5858\u4fe0\u5ba2\u884c(QT) 112.124.31.157 5555 \u56db\u5341\u4e94\u5929\u4e8c\u5341\u5c0f\u6642\u591a \u4e8c\u767e\u516b\u5341\u516d\u4f4d\r\n\u001b[0;0m================= =============== ==== ==================== ============\r\n\u76ee\u524d\u4fe0\u5ba2\u884c\u5171\u6709\u4e8c\u767e\u516b\u5341\u516d\u4f4d\u73a9\u5bb6\u5728\u4e00\u500b\u7ad9\u9ede\u9023\u7dda\u4e2d\u3002\r\n\r\n\u82f1\u6587ID\u8b58\u5225( \u65b0\u73a9\u5bb6\u8acb\u8f38\u5165 new \u9032\u5165\u4eba\u7269\u5efa\u7acb\u55ae\u5143 )\r\n\u8acb\u8f38\u5165\u60a8\u7684\u82f1\u6587ID\uff1a\r\n( \u65b0\u73a9\u5bb6\u8acb\u8f38\u5165 new \u9032\u5165\u4eba\u7269\u5efa\u7acb\u55ae\u5143 )\r\n\u8acb\u91cd\u65b0\u8f38\u5165\u60a8\u7684ID\uff1a",
"banner_before_return": "\r\nWelcome to chinese MUD \u001b[1;37mXiaKeXing\u001b[0;0m.\r\n\r\nAre you using BIG5 code?(Yes|No)\r\n>",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "big5",
"mssp": {
"NAME": "\u72e8\u8ae6\u4ff4 ",
"PLAYERS": "286",
"UPTIME": "1771730816"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5037946701049805,
"total": 16.63031554222107
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:58:56.345809+00:00",
"host": "112.124.31.157",
"ip": "112.124.31.157",
"port": 5555
},
{
"connected": "2026-04-07T07:19:05.122723+00:00",
"host": "112.124.31.157",
"ip": "112.124.31.157",
"port": 5555
},
{
"connected": "2026-04-09T00:08:09.750433+00:00",
"host": "112.124.31.157",
"ip": "112.124.31.157",
"port": 5555
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 112.124.31.157 5555
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=112.124.31.157 port=5555
INFO client_base.py:188 Connected to <Peer 112.124.31.157 5555>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': '狨諦俴 ', 'PLAYERS': '286', 'UPTIME': '1771730816'}
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG client_base.py:510 negotiation complete after 1.15s.
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG fingerprinting.py:850 connection for server fingerprint 33ebb6bbdfcdff81
INFO client_base.py:120 Connection closed to <Peer 112.124.31.157 5555>