15.204.237.15
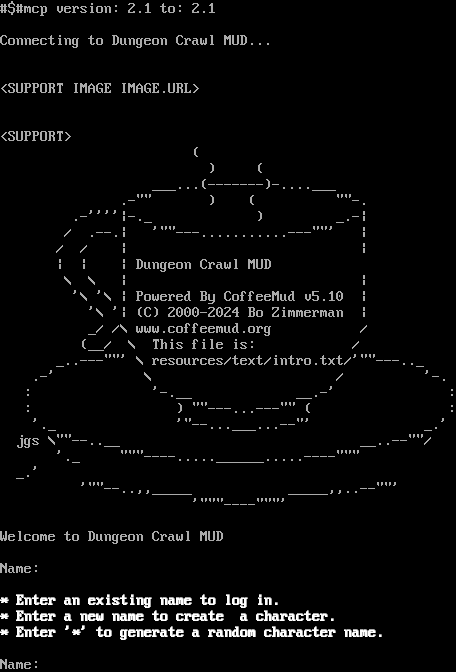
Connection Banner:
This banner is more than 96% similar to 4 other servers:
🇩🇪 172.105.94.5:5555 (97% match)
🇺🇸 scannerhead.pocketmud.com:4444 (97% match)
🇬🇧 dragonage.pocketmud.com:5555 (96% match)
🇬🇧 139.162.249.62:5555 (96% match)
Server URLs
- Telnet: telnet://15.204.237.15:5555
- Website: http://dungeoncrawl.pocketmud.com:27744/
Server Info
Codebase: CoffeeMUD v5.10.3
Genre: Fantasy
Gameplay: Adventure, Social
Players online: 0 [1]
Uptime: 1 days
Created: 2024
Status: Open Beta
Server Location: 🇺🇸 United States (GeoIP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: Negotiated
MCCP: Yes (MSSP)
MCCP2: No
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options offered by server: BINARY, ECHO, GMCP, MSDP, MSP, MSSP, MXP
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "4f99ee0c30791dde",
"fingerprint-data": {
"offered-options": [
"BINARY",
"ECHO",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"CHARSET",
"COM_PORT",
"EOR",
"MCCP2",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[1;37m \u001b[0;37m\n\r\u001b[1;37m* Enter an existing name to log in.\u001b[0;37m\n\r\u001b[1;37m* Enter a new name to create a character.\u001b[0;37m\n\r\u001b[1;37m* Enter '*' to generate a random character name.\u001b[0;37m\n\r\n\rName: ",
"banner_before_return": "\n\r#$#mcp version: 2.1 to: 2.1\n\r\n\rConnecting to Dungeon Crawl MUD...\n\r\n\u001b[6z\n\u001b[6z<SUPPORT IMAGE IMAGE.URL>\n\n\u001b[6z\n\u001b[6z<SUPPORT>\n (\n\r ) (\n\r ___...(-------)-....___\n\r .-"" ) ( ""-.\n\r .-''''|-._ ) _.-|\n\r / .--.| '""---...........---""' |\n\r / / | |\n\r | | | Dungeon Crawl MUD\n\r \\ \\ | |\n\r '\\ '\\ | Powered By CoffeeMud v5.10 |\n\r '\\ '| (C) 2000-2024 Bo Zimmerman |\n\r _/ /\\ www.coffeemud.org /\n\r (__/ \\ This file is: /\n\r _..---""' \\ resources/text/intro.txt/'""---.._\n\r .-' \\ / '-.\n\r : '-.__ __.-' :\n\r : ) ""---...---"" ( :\n\r '._ '"--...___...--"' _.'\n\r jgs \\""--..__ __..--""/\n\r '._ """----.....______.....----""" \r\n _.'\n\r '""--..,,_____ _____,,..--""'\n\r '"""----"""'\n\r\n\rWelcome to Dungeon Crawl MUD\n\r\n\rName: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"AREAS": "2",
"CHARSET": "iso-8859-1",
"CLASSES": "47",
"CODEBASE": "CoffeeMUD v5.10.3",
"CONTACT": "JORDAN.OBRASTOFF@GMAIL.COM",
"CRAWL DELAY": "-1",
"CREATED": "2024",
"EMAIL": "JORDAN.OBRASTOFF@GMAIL.COM",
"FAMILY": "CoffeeMUD",
"GAMEPLAY": [
"Adventure",
"Social"
],
"GAMESYSTEM": "Tick Based",
"GENRE": "Fantasy",
"HELPFILES": "5422",
"HOSTNAME": "dungeoncrawl.pocketmud.com",
"ICON": "http://dungeoncrawl.pocketmud.com:27744/images/cm.jpg",
"INTERMUD": "I3",
"LANGUAGE": "English",
"MCCP": "1",
"MOBILES": "149",
"MSP": "1",
"MXP": "1",
"OBJECTS": "676",
"PLAYERS": "0",
"PORT": "5555",
"RACES": "8",
"ROOMS": "26",
"SKILLS": "1979",
"STATUS": "Open Beta",
"UPTIME": "1772766187",
"WEBSITE": "http://dungeoncrawl.pocketmud.com:27744/",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"NAWS": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.20592665672302246,
"total": 11.956627368927002
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:54:50.454896+00:00",
"host": "15.204.237.15",
"ip": "15.204.237.15",
"port": 5555
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 15.204.237.15 5555
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=15.204.237.15 port=5555
ERROR client.py:1318 15.204.237.15:5555: [Errno 111] Connect call failed ('15.204.237.15', 5555)