185.26.59.68
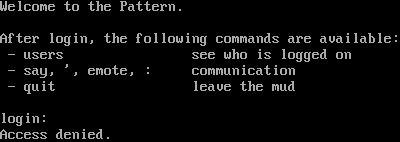
Connection Banner:
Server URLs
- Telnet: telnet://185.26.59.68:6047
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 6 other servers.
Options requested from client: LINEMODE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "98ef96f171413a1c",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"LINEMODE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Access denied.\r\n\r\n",
"banner_before_return": "\r\nWelcome to the Pattern.\r\n\r\nAfter login, the following commands are available:\r\n - users see who is logged on\r\n - say, ', emote, : communication\r\n - quit leave the mud\r\n\r\nlogin: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": false
},
"server_requested": {
"LINEMODE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.666658639907837
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:01:49.135560+00:00",
"host": "185.26.59.68",
"ip": "185.26.59.68",
"port": 6047
},
{
"connected": "2026-04-07T07:05:10.673826+00:00",
"host": "185.26.59.68",
"ip": "185.26.59.68",
"port": 6047
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 185.26.59.68 6047
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=185.26.59.68 port=6047
INFO client_base.py:190 Connected to <Peer 185.26.59.68 6047>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x01' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False,
remote:False, local:True> IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL MSDP, WILL ZMP, WILL GMCP, WILL AARDWOLF, WILL MSP, WILL ATCP, WILL
MCCP3_COMPRESS, WILL MSSP, WILL MCCP2_COMPRESS, DO MXP, DO MSDP, DO ZMP, DO GMCP, DO AARDWOLF, DO MSP, DO ATCP, DO
MCCP3_COMPRESS, DO MSSP, DO MCCP2_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 185.26.59.68 6047>
DEBUG fingerprinting.py:849 connection for server fingerprint 98ef96f171413a1c