The 7th Plane
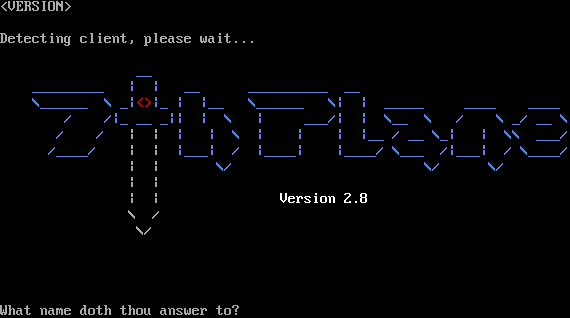
Connection Banner:
Server URLs
- Telnet: telnet://7thplane.net:8888
Server Info
Uptime: 37 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: Negotiated
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "The 7th Plane"
}
],
"banner_after_return": "",
"banner_before_return": "\u001b[7z\u001b[1z<VERSION>\u001b[7z\r\n\r\nDetecting client, please wait...\r\u001b[1;37m\u001b[0m\n\u001b[0m\u001b[0c\r\n \u001b[38;5;68m__\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;68m_________ | | __ __________ __\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;68m\\______ \\ _|\u001b[38;5;160m<>\u001b[38;5;68m|_ | |__ \\______ \\| | _____ ____ ____\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;68m/ /|_ __ _|| | \\ | ___/| | \\__ \\ / \\ _/ __ \\\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;68m/ / \u001b[38;5;248m| |\u001b[38;5;68m | | \\ | | | |__ / __ \\_| | \\\\ ___/\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;68m/____/ \u001b[38;5;248m| |\u001b[38;5;68m |___| / |____| |____/ \\___ /|___| / \\____/\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;248m| | \u001b[38;5;68m\\/ \\/ \\/\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;248m| |\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;248m| |\u001b[0;00m \u001b[38;5;231mVersion 2.8\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;248m\\ /\u001b[0;00m\r\u001b[1;37m\u001b[0m\n \u001b[38;5;248m \\/ \u001b[0;00m\r\u001b[1;37m\u001b[0m\n\r\u001b[1;37m\u001b[0m\n\r\u001b[1;37m\u001b[0m\n\r\u001b[1;37m\u001b[0m\n\r\u001b[1;37m\u001b[0m\n\u001b[38;5;248mWhat name doth thou answer to?\u001b[0;00m\r\u001b[1;37m\u001b[0m\n\u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "The 7th Plane",
"UPTIME": "1772324101"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true,
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.779901504516602
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:09.068469+00:00",
"host": "7thplane.net",
"ip": "23.239.25.183",
"port": 8888
},
{
"connected": "2026-04-07T06:54:39.849860+00:00",
"host": "7thplane.net",
"ip": "23.239.25.183",
"port": 8888
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 7thplane.net 8888
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=7thplane.net port=8888
INFO client_base.py:190 Connected to <Peer 23.239.25.183 8888>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'The 7th Plane'
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'The 7th Plane'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'The 7th Plane', 'UPTIME': '1772324101', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL GMCP, WILL MSDP, WILL ZMP, WILL MSSP, WILL AARDWOLF, WILL MCCP3_COMPRESS,
WILL MCCP2_COMPRESS, DO GMCP, DO MXP, DO ZMP, DO AARDWOLF, DO MCCP3_COMPRESS, DO ATCP'
DEBUG client_base.py:489 MCCP2 decompression ended (server→client)
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 23.239.25.183 8888>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b