brigandine.org
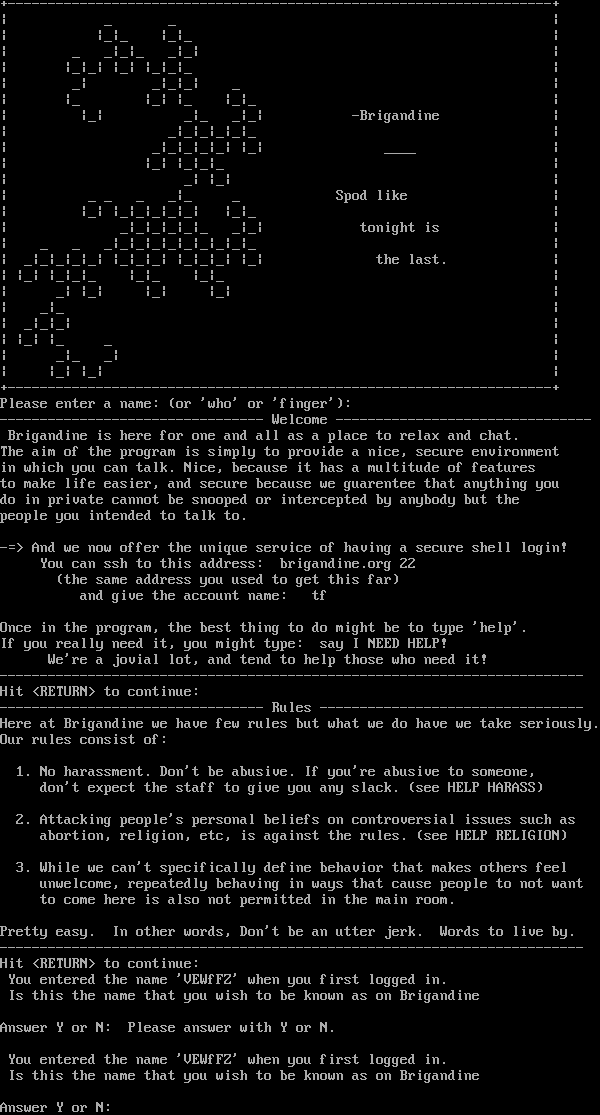
Connection Banner:
Server URLs
- Telnet: telnet://brigandine.org:9390
- Website: brigandine.org
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 5 other servers.
Options offered by server: EOR
Options requested from client: STATUS
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "55d32831c087b3d6",
"fingerprint-data": {
"offered-options": [
"EOR"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"STATUS"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\n\r--------------------------------- Welcome --------------------------------\n\r Brigandine is here for one and all as a place to relax and chat.\n\rThe aim of the program is simply to provide a nice, secure environment\n\rin which you can talk. Nice, because it has a multitude of features\n\rto make life easier, and secure because we guarentee that anything you\n\rdo in private cannot be snooped or intercepted by anybody but the\n\rpeople you intended to talk to.\n\r\n\r-=> And we now offer the unique service of having a secure shell login!\n\r You can ssh to this address: brigandine.org 22\n\r (the same address you used to get this far)\n\r and give the account name: tf\n\r\n\rOnce in the program, the best thing to do might be to type 'help'.\n\rIf you really need it, you might type: say I NEED HELP!\n\r We're a jovial lot, and tend to help those who need it!\n\r-------------------------------------------------------------------------\n\rHit <RETURN> to continue: \n\r--------------------------------- Rules ---------------------------------\n\rHere at Brigandine we have few rules but what we do have we take seriously.\n\rOur rules consist of:\n\r \n\r 1. No harassment. Don't be abusive. If you're abusive to someone,\n\r don't expect the staff to give you any slack. (see HELP HARASS)\n\r \n\r 2. Attacking people's personal beliefs on controversial issues such as\n\r abortion, religion, etc, is against the rules. (see HELP RELIGION)\n\r\n\r 3. While we can't specifically define behavior that makes others feel \n\r unwelcome, repeatedly behaving in ways that cause people to not want \n\r to come here is also not permitted in the main room.\n\r \n\rPretty easy. In other words, Don't be an utter jerk. Words to live by.\n\r-------------------------------------------------------------------------\n\rHit <RETURN> to continue: \n\r You entered the name 'VEWfFZ' when you first logged in.\n\r Is this the name that you wish to be known as on Brigandine\n\r\n\rAnswer Y or N: Please answer with Y or N.\n\r\n\r You entered the name 'VEWfFZ' when you first logged in.\n\r Is this the name that you wish to be known as on Brigandine\n\r\n\rAnswer Y or N: ",
"banner_before_return": "+--------------------------------------------------------------------+\n\r| _ _ |\n\r| |_|_ |_|_ |\n\r| _ _|_|_ _|_| |\n\r| |_|_| |_| |_|_|_ |\n\r| _| _|_|_| _ |\n\r| |_ |_| |_ |_|_ |\n\r| |_| _|_ _|_| -Brigandine |\n\r| _|_|_|_|_|_ |\n\r| _|_|_|_|_| |_| ____ |\n\r| |_| |_|_|_ |\n\r| _| |_| |\n\r| _ _ _ _|_ _ Spod like |\n\r| |_| |_|_|_|_|_| |_|_ |\n\r| _|_|_|_|_|_ _|_| tonight is |\n\r| _ _ _|_|_|_|_|_|_|_|_|_ |\n\r| _|_|_|_|_| |_|_|_| |_|_|_| |_| the last. |\n\r| |_| |_|_|_ |_|_ |_|_ |\n\r| _| |_| |_| |_| |\n\r| _|_ |\n\r| _|_|_| |\n\r| |_| |_ _ |\n\r| _|_ _| |\n\r| |_| |_| |\n\r+--------------------------------------------------------------------+\n\r\u001b[mPlease enter a name: (or 'who' or 'finger'): ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"EOR": true
},
"server_requested": {
"STATUS": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5040228366851807,
"total": 26.442909002304077
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:29.669992+00:00",
"host": "brigandine.org",
"ip": "206.130.99.125",
"port": 9390
},
{
"connected": "2026-04-07T06:50:35.313757+00:00",
"host": "brigandine.org",
"ip": "206.130.99.125",
"port": 9390
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug brigandine.org 9390
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=brigandine.org port=9390
INFO client_base.py:190 Connected to <Peer 206.130.99.125 9390>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC WILL EOR
DEBUG stream_writer.py:789 WILL EOR unsolicited
DEBUG stream_writer.py:2045 handle_will(EOR)
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 remote_option[EOR] = True
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:773 recv IAC DO STATUS
DEBUG stream_writer.py:1887 handle_do(STATUS)
DEBUG stream_writer.py:3384 pending_option[WILL + STATUS] = True
DEBUG stream_writer.py:1024 send IAC WILL STATUS
DEBUG stream_writer.py:2660 send IAC SB STATUS IS DO EOR IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + STATUS] = False
DEBUG stream_writer.py:3384 local_option[STATUS] = True
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL GMCP, WILL MCCP2_COMPRESS, WILL ZMP, WILL MSDP, WILL MCCP3_COMPRESS, WILL
AARDWOLF, WILL MSSP, WILL ATCP, WILL MSP, DO MXP, DO GMCP, DO MCCP2_COMPRESS, DO ZMP, DO MSDP, DO MCCP3_COMPRESS, DO AARDWOLF,
DO MSSP, DO ATCP, DO MSP'
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:773 recv IAC DO STATUS
DEBUG stream_writer.py:1887 handle_do(STATUS)
DEBUG stream_writer.py:2660 send IAC SB STATUS IS DO EOR IAC SE
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 55d32831c087b3d6
INFO client_base.py:122 Connection closed to <Peer 206.130.99.125 9390>