cave.extricate.org
Connection Banner:
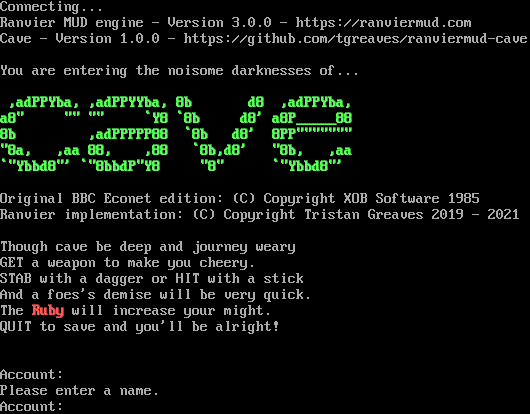
Server URLs
- Telnet: telnet://cave.extricate.org:4000
- Website: https://ranviermud.com
Server Info
Server Location: 🇬🇧 United Kingdom (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: EOR
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9471858421695f58",
"fingerprint-data": {
"offered-options": [
"EOR"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Please enter a name.\r\nAccount: ",
"banner_before_return": "\r\nConnecting...\n\u001b[0m\u001b[37mRanvier MUD engine - Version 3.0.0 - https://ranviermud.com\r\nCave - Version 1.0.0 - https://github.com/tgreaves/ranviermud-cave\r\n\r\nYou are entering the noisome darknesses of...\r\n \r\n\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[32m ,adPPYba, ,adPPYYba, 8b d8 ,adPPYba,\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m \r\n\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[32ma8\" \"\" \"\" `Y8 `8b d8' a8P_____88\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m \r\n\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[32m8b ,adPPPPP88 `8b d8' 8PP\"\"\"\"\"\"\" \u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m \r\n\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[32m\"8a, ,aa 88, ,88 `8b,d8' \"8b, ,aa \u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m \r\n\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[32m`\"Ybbd8\"' `\"8bbdP\"Y8 \"8\" `\"Ybbd8\"' \u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m \r\n\r\nOriginal BBC Econet edition: (C) Copyright XOB Software 1985\r\nRanvier implementation: (C) Copyright Tristan Greaves 2019 - 2021\r\n\r\nThough cave be deep and journey weary\r\nGET a weapon to make you cheery.\r\nSTAB with a dagger or HIT with a stick\r\nAnd a foes's demise will be very quick.\r\nThe \u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m\u001b[1m\u001b[31mRuby\u001b[0m\u001b[37m\u001b[1m\u001b[0m\u001b[37m will increase your might.\r\nQUIT to save and you'll be alright!\r\n\r\n\r\n\u001b[0mAccount: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"EOR": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5041413307189941,
"total": 11.330107927322388
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:01.225311+00:00",
"host": "cave.extricate.org",
"ip": "80.229.19.209",
"port": 4000
},
{
"connected": "2026-04-07T07:21:01.406465+00:00",
"host": "cave.extricate.org",
"ip": "80.229.19.209",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug cave.extricate.org 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=cave.extricate.org port=4000
INFO client_base.py:190 Connected to <Peer 80.229.19.209 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:773 recv IAC WILL EOR
DEBUG stream_writer.py:789 WILL EOR unsolicited
DEBUG stream_writer.py:2045 handle_will(EOR)
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 remote_option[EOR] = True
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSDP, WILL ZMP, WILL MXP, WILL MSP, WILL ATCP, WILL MCCP3_COMPRESS, WILL GMCP, WILL
AARDWOLF, WILL MSSP, WILL MCCP2_COMPRESS, DO MSDP, DO ZMP, DO MXP, DO MSP, DO ATCP, DO MCCP3_COMPRESS, DO GMCP, DO AARDWOLF,
DO MSSP, DO MCCP2_COMPRESS'
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG fingerprinting.py:849 connection for server fingerprint 9471858421695f58
INFO client_base.py:122 Connection closed to <Peer 80.229.19.209 4000>