Cheeseworld
Connection Banner:
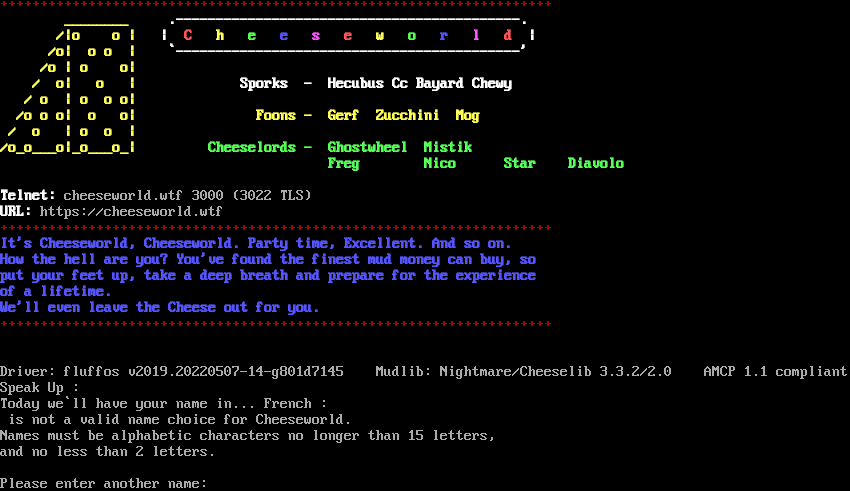
Server URLs
- Telnet: telnet://cheeseworld.wtf:3000
- Website: cheeseworld.wtf
Server Info
Codebase: FluffOS v2021 Nightmare 3 ish
Genre: Shenanigans
Gameplay: Adventure, Hack and Slash
Players online: 1 [1]
Uptime: 4 days
Created: 1996
Status: live
Server Location: 🇺🇸 North America (MSSP)
Language: ENGLISH
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: No
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: CHARSET, ECHO, GMCP, MSP, MSSP, ZMP
Options requested from client: MXP, NAWS, NEW_ENVIRON, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "82a8d53b26a1577c",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"ECHO",
"GMCP",
"MSP",
"MSSP",
"ZMP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"EOR",
"MSDP",
"MXP",
"SGA",
"STATUS"
],
"requested-options": [
"MXP",
"NAWS",
"NEW_ENVIRON",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\nToday we`ll have your name in... French : \r\n is not a valid name choice for Cheeseworld.\r\nNames must be alphabetic characters no longer than 15 letters,\r\nand no less than 2 letters.\r\n\r\nPlease enter another name: ",
"banner_before_return": "\u001b[31m+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++\r\n\u001b[1;33m ________ \u001b[0;37;40m \u001b[1m .-------------------------------------------.\u001b[0;37;40m\r\n\u001b[1;33m /|o o |\u001b[0;37;40m \u001b[1m| \u001b[31mC \u001b[33mh \u001b[32me \u001b[34me \u001b[35ms \u001b[31me \u001b[33mw \u001b[32mo \u001b[34mr \u001b[35ml \u001b[31md \u001b[37m|\u001b[0;37;40m\r\n\u001b[1;33m /o| o o |\u001b[0;37;40m \u001b[1m `-------------------------------------------'\u001b[0;37;40m\r\n\u001b[1;33m /o | o o|\u001b[0;37;40m\r\n\u001b[1;33m / o| o |\u001b[0;37;40m \u001b[1mSporks - Hecubus Cc Bayard Chewy\r\n\u001b[1;33m / o | o o o|\u001b[0;37;40m \r\n\u001b[1;33m /o o o| o o|\u001b[0;37;40m \u001b[1;33mFoons - Gerf Zucchini Mog\r\n\u001b[1;33m / o | o o |\u001b[0;37;40m\r\n\u001b[1;33m/o_o___o|_o___o_|\u001b[0;37;40m \u001b[1;32mCheeselords - Ghostwheel Mistik\r\n \u001b[1;32mFreg Nico Star Diavolo\u001b[0;37;40m\r\n \r\n\u001b[1mTelnet:\u001b[0;37;40m cheeseworld.wtf 3000 (3022 TLS)\r\n\u001b[1mURL:\u001b[0;37;40m https://cheeseworld.wtf\r\n\u001b[31m+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++\u001b[0;37;40m\r\n\u001b[1;34mIt's Cheeseworld, Cheeseworld. Party time, Excellent. And so on.\r\n\u001b[1;34mHow the hell are you? You've found the finest mud money can buy, so\r\n\u001b[1;34mput your feet up, take a deep breath and prepare for the experience\r\n\u001b[1;34mof a lifetime.\r\n\u001b[1;34mWe'll even leave the Cheese out for you.\u001b[0;37;40m\r\n\u001b[31m+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++\u001b[0;37;40m\r\n\r\n\r\nDriver: fluffos v2019.20220507-14-g801d7145 Mudlib: Nightmare/Cheeselib 3.3.2/2.0 AMCP 1.1 compliant\r\nSpeak Up : ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"ACCEPTING BRIBES": "1",
"ANSI": "1",
"CODEBASE": "FluffOS v2021 Nightmare 3 ish",
"CONTACT": "unknown",
"CREATED": "1996",
"FAMILY ": "LPMUD",
"GAMEPLAY": "Adventure, Hack and Slash",
"GAMESYSTEM": "Custom D&D ish",
"GENRE": "Shenanigans",
"GMCP": "1",
"HIRING BUILDERS": "1",
"HIRING CODERS": "1",
"HOSTNAME": "cheeseworld.wtf",
"INTERMUD": "i3",
"LANGUAGE": "ENGLISH",
"LOCATION": "North America",
"MSP": "0",
"MXP": "0",
"NAME": "Cheeseworld",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYERS": "1",
"PORT": "3000",
"SSL": "3022",
"STATUS": "live",
"SUBGENRE": "Cheese",
"UPTIME": "1770666523",
"UTF-8": "1",
"VT100": "0",
"XTERM 256 COLORS": "1"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"0x56": false,
"CHARSET": true,
"GMCP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"MXP": true,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.3149247169494629,
"total": 4.971412658691406
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:44.040906+00:00",
"host": "cheeseworld.wtf",
"ip": "44.224.50.189",
"port": 3000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug cheeseworld.wtf 3000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=cheeseworld.wtf port=3000
ERROR client.py:1318 cheeseworld.wtf:3000: TCP connection to cheeseworld.wtf:3000 timed out after 30.0s