dark-legacy.com
Connection Banner:
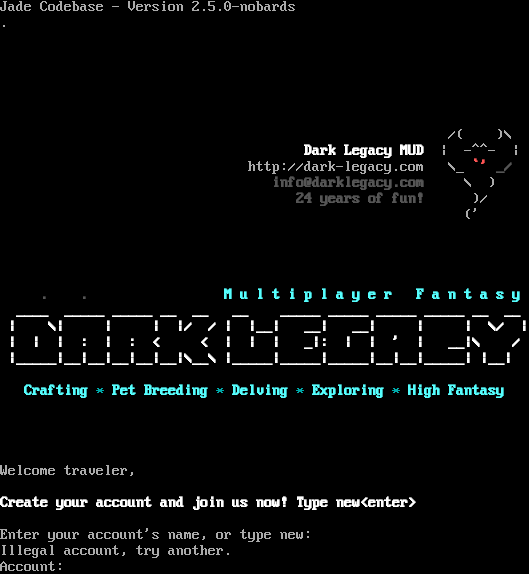
Server URLs
- Telnet: telnet://dark-legacy.com:9898
- Play in Browser: LociTerm
- Website: http://dark-legacy.com
Server Info
Server Location: 🇨🇦 Canada (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: EOR
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9471858421695f58",
"fingerprint-data": {
"offered-options": [
"EOR"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal account, try another.\n\rAccount: ",
"banner_before_return": "\n\rJade Codebase - Version 2.5.0-nobards\n\r. \n\r \n\r \n\r \n\r \n\r \n\r \n\r \u001b[0;37m\u001b[1;37m\u001b[0;37m\u001b[0;37m/( )\\\n\r \u001b[0;37m\u001b[1;37m Dark Legacy MUD \u001b[0;37m\u001b[0;37m| -^^- |\n\r \u001b[0;37m\u001b[1;36m\u001b[0;37m\u001b[0;37mhttp://dark-legacy.com \u001b[0;37m\u001b[1;37m\u001b[0;37m\u001b[0;37m\\_\u001b[0;37m\u001b[1;31m `'\u001b[30m _/\n\r info@darklegacy.com \u001b[37;37m\u001b[0;37m\u001b[0;37m \\ )\n\r \u001b[0;37m\u001b[1;30m 24 years of fun! \u001b[37;37m\u001b[0;37m\u001b[0;37m )/\n\r \u001b[0;37m\u001b[1;37m\u001b[0;37m\u001b[0;37m ('\n\r \n\r \n\r \n\r \n\r \u001b[0;37m\u001b[1;30m . . \u001b[36m M u l t i p l a y e r F a n t a s y\n\r\u001b[30m \u001b[37;37m ____ _____ _____ __ __ __ _____ _____ _____ _____ __ __ \n\r\u001b[30m \u001b[37;37m| \\| | | |/ / | |__| __| __| | | \\/ |\n\r\u001b[30m \u001b[37;37m| | | : | : < < | | | _|: | | ' | __|\\ /\n\r\u001b[30m \u001b[37;37m|_____|__|__|__|__|__|\\__\\ |_____|_____|_____|__|__|_____| |__|\n\r\u001b[30m \n\r \u001b[36mCrafting \u001b[0;37m\u001b[0;36m* \u001b[0;37m\u001b[1;36mPet Breeding \u001b[0;37m\u001b[0;36m* \u001b[0;37m\u001b[1;36mDelving \u001b[0;37m\u001b[0;36m* \u001b[0;37m\u001b[1;36mExploring \u001b[0;37m\u001b[0;36m* \u001b[0;37m\u001b[1;36mHigh Fantasy\n\r\u001b[30m \n\r \n\r \n\r \n\r\u001b[0;37m\u001b[0;37mWelcome traveler,\n\r \n\r\u001b[0;37m\u001b[1;37mCreate your account and join us now! Type new<enter> \n\r\u001b[0;37m\u001b[0;37m \n\rEnter your account's name, or type new: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"0x55": false,
"EOR": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.503312349319458,
"total": 11.106714725494385
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:58:03.189873+00:00",
"host": "dark-legacy.com",
"ip": "167.114.173.63",
"port": 9898
},
{
"connected": "2026-04-07T06:59:23.386900+00:00",
"host": "dark-legacy.com",
"ip": "167.114.173.63",
"port": 9898
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug dark-legacy.com 9898
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=dark-legacy.com port=9898
INFO client_base.py:190 Connected to <Peer 167.114.173.63 9898>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC WILL EOR
DEBUG stream_writer.py:789 WILL EOR unsolicited
DEBUG stream_writer.py:2045 handle_will(EOR)
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 remote_option[EOR] = True
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL ATCP, WILL GMCP, WILL MXP, WILL MSSP, WILL MCCP2_COMPRESS, WILL MSP,
WILL ZMP, WILL MSDP, WILL MCCP3_COMPRESS, DO AARDWOLF, DO ATCP, DO GMCP, DO MXP, DO MSSP, DO MCCP2_COMPRESS, DO MSP, DO ZMP,
DO MSDP, DO MCCP3_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 9471858421695f58
INFO client_base.py:122 Connection closed to <Peer 167.114.173.63 9898>