drygulch.aresmush.com
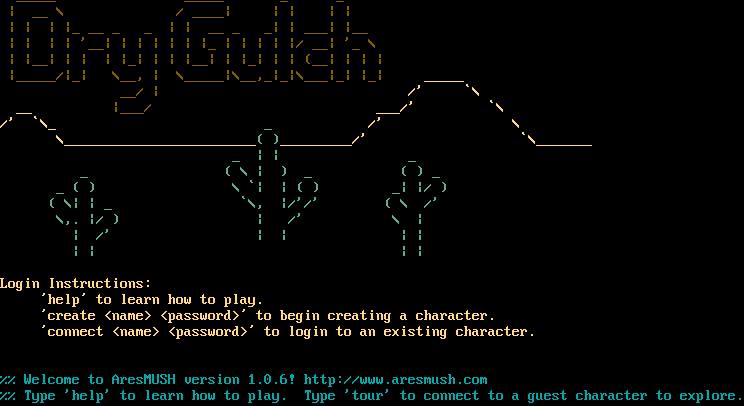
Connection Banner:
Server URLs
- Telnet: telnet://drygulch.aresmush.com:4201
- Website: http://www.aresmush.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options requested from client: CHARSET, NAWS
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "4bf9c4a457402b1d",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"NAWS"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " \u001b[38;5;94m_____ _____ _ _\u001b[0m \n \u001b[38;5;94m| __ \\ / ____| | | | |\u001b[0m \n \u001b[38;5;94m| | | |_ __ _ _ | | __ _ _| | ___| |__\u001b[0m \n \u001b[38;5;94m| | | | '__| | | | | | |_ | | | | |/ __| '_ \\ \n \u001b[38;5;94m| |__| | | | |_| | | |__| | |_| | | (__| | | |\u001b[0m\n\u001b[38;5;94m |_____/|_| \\__, | \\_____|\\__,_|_|\\___|_| |_| \u001b[38;5;222m_____\u001b[0m\n \u001b[38;5;94m__/ | \u001b[38;5;222m/' `\\\n \u001b[38;5;222m__ \u001b[38;5;94m|___/ \u001b[38;5;222m___/' `\\\n\u001b[38;5;222m/' `\\_ \u001b[38;5;72m_ \u001b[38;5;222m/' \\\n \u001b[38;5;222m\\________________________\u001b[38;5;72m( )\u001b[38;5;222m_________/' `\\_______\u001b[0m\n \u001b[38;5;72m_ | | _\n \u001b[38;5;72m_ ( \\ | ) _ ( ) _\n \u001b[38;5;72m_ ( ) \\ `| | ( ) _| |/ )\n \u001b[38;5;72m( \\| | _ `\\, |/'/' ( \\ /'\n \u001b[38;5;72m\\,. |/ ) | /' \\ |\n \u001b[38;5;72m| /' | | | |\n \u001b[38;5;72m| | | |\u001b[0m\n\n\u001b[38;5;222mLogin Instructions:\n \u2019help\u2019 to learn how to play.\n \u2019create <name> <password>\u2019 to begin creating a character.\n \u2019connect <name> <password>\u2019 to login to an existing character.\u001b[0m\n\n \u001b[0m\r\n\u001b[36m%% Welcome to AresMUSH version 1.0.6! http://www.aresmush.com\n%% Type 'help' to learn how to play. Type 'tour' to connect to a guest character to explore.\u001b[0m\u001b[0m\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"option_states": {
"server_offered": {},
"server_requested": {
"CHARSET": true,
"NAWS": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5080363750457764,
"total": 5.016290903091431
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:10:26.339018+00:00",
"host": "drygulch.aresmush.com",
"ip": "104.248.233.39",
"port": 4201
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug drygulch.aresmush.com 4201
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=drygulch.aresmush.com port=4201
ERROR client.py:1318 drygulch.aresmush.com:4201: [Errno 111] Connect call failed ('104.248.233.39', 4201)