emptynight.aresmush.com
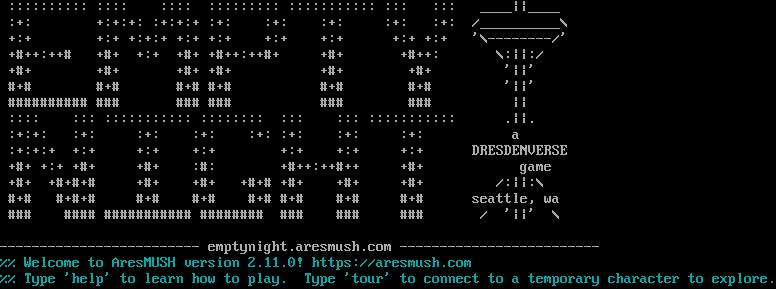
Connection Banner:
Server URLs
- Telnet: telnet://emptynight.aresmush.com:4201
- Play in Browser: LociTerm
- Website: emptynight.aresmush.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 13 other servers.
Options requested from client: CHARSET, NAWS
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "ba94558ba15cc5eb",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"NAWS"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\n :::::::::: :::: :::: ::::::::: ::::::::::: ::: ::: ____||____\n :+: +:+:+: :+:+:+ :+: :+: :+: :+: :+: /__________\\\n +:+ +:+ +:+:+ +:+ +:+ +:+ +:+ +:+ +:+ '\\--------/'\n +#++:++# +#+ +:+ +#+ +#++:++#+ +#+ +#++: \\:||:/\n +#+ +#+ +#+ +#+ +#+ +#+ '||'\n #+# #+# #+# #+# #+# #+# '||' \n ########## ### ### ### ### ### ||\n :::: ::: ::::::::::: :::::::: ::: ::: ::::::::::: .||.\n :+:+: :+: :+: :+: :+: :+: :+: :+: a\n :+:+:+ +:+ +:+ +:+ +:+ +:+ +:+ DRESDENVERSE\n +#+ +:+ +#+ +#+ :#: +#++:++#++ +#+ game\n +#+ +#+#+# +#+ +#+ +#+# +#+ +#+ +#+ /:||:\\\n #+# #+#+# #+# #+# #+# #+# #+# #+# seattle, wa\n ### #### ########### ######## ### ### ### / '||' \\\n\n------------------------- emptynight.aresmush.com -------------------------\u001b[0m\r\n\u001b[36m%% Welcome to AresMUSH version 2.11.0! https://aresmush.com\n%% Type 'help' to learn how to play. Type 'tour' to connect to a temporary character to explore.\u001b[0m\u001b[0m\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"option_states": {
"server_offered": {},
"server_requested": {
"CHARSET": true,
"NAWS": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5040340423583984,
"total": 11.016796827316284
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:36.937574+00:00",
"host": "emptynight.aresmush.com",
"ip": "143.198.230.188",
"port": 4201
},
{
"connected": "2026-04-07T06:52:51.238755+00:00",
"host": "emptynight.aresmush.com",
"ip": "143.198.230.188",
"port": 4201
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug emptynight.aresmush.com 4201
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=emptynight.aresmush.com port=4201
INFO client_base.py:190 Connected to <Peer 143.198.230.188 4201>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: utf-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED utf-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL GMCP, WILL MXP, WILL MSSP, WILL MCCP3_COMPRESS, WILL ATCP, WILL
MSP, WILL AARDWOLF, WILL ZMP, WILL MSDP, DO MCCP2_COMPRESS, DO GMCP, DO MXP, DO MSSP, DO MCCP3_COMPRESS, DO ATCP, DO MSP, DO
AARDWOLF, DO ZMP, DO MSDP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint ba94558ba15cc5eb
INFO client_base.py:122 Connection closed to <Peer 143.198.230.188 4201>