Exile
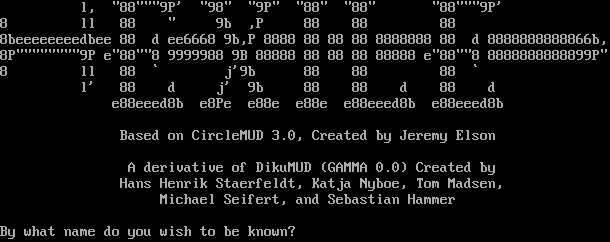
Connection Banner:
Server URLs
- Telnet: telnet://exilemud.com:4000
- Website: http://exilemud.com
Server Info
Codebase: CircleMUD 3.0
Genre: Fantasy
Gameplay: Hack and Slash
Players online: 6 [1]
Uptime: 14 days
Created: 1996
Status: Live
Server Location: 🇺🇸 United States of America (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Yes (MSSP)
MCCP: No
MCCP2: No
MXP: Yes (MSSP)
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Exile"
}
],
"banner_after_return": "",
"banner_before_return": "\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\r\n\r\n l, \"88\"\"\"9P' \"98\" \"9P\" \"88\" \"88\" \"88\"\"\"9P'\r\n8 ll 88 \" 9b ,P 88 88 88\r\n8beeeeeeeedbee 88 d ee6668 9b,P 8888 88 88 88 8888888 88 d 8888888888866b,\r\n8P\"\"\"\"\"\"\"\"9P e\"88\"\"8 9999988 9B 88888 88 88 88 88888 e\"88\"\"8 8888888888899P\"\r\n8 ll 88 ` j'9b 88 88 88 `\r\n l' 88 d j' 9b 88 88 d 88 d\r\n e88eeed8b e8Pe e88e e88e e88eeed8b e88eeed8b\r\n\r\n Based on CircleMUD 3.0, Created by Jeremy Elson\r\n\r\n A derivative of DikuMUD (GAMMA 0.0) Created by\r\n Hans Henrik Staerfeldt, Katja Nyboe, Tom Madsen,\r\n Michael Seifert, and Sebastian Hammer\r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ADULT MATERIAL": "0",
"ANSI": "1",
"AREAS": "159",
"CLASSES": "9",
"CODEBASE": "CircleMUD 3.0",
"CRAWL DELAY": "-1",
"CREATED": "1996",
"EQUIPMENT SYSTEM": "Level",
"EXITS": "49135",
"EXTRA DESCRIPTIONS": "1216",
"FAMILY": "DikuMUD",
"GAMEPLAY": "Hack and Slash",
"GAMESYSTEM": "Custom",
"GENRE": "Fantasy",
"GMCP": "0",
"HELPFILES": "1111",
"HIRING BUILDERS": "0",
"HIRING CODERS": "0",
"HOSTNAME": "exilemud.com",
"INTERMUD": "",
"IP": "198.58.123.126",
"LANGUAGE": "English",
"LEVELS": "180",
"LOCATION": "United States of America",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "0",
"MOBILES": "3404",
"MSDP": "1",
"MSP": "0",
"MUDTRIGS": "761",
"MULTICLASSING": "1",
"MULTIPLAYING": "Restricted",
"MXP": "1",
"NAME": "Exile",
"OBJECTS": "5800",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYER CITIES": "0",
"PLAYER CLANS": "1",
"PLAYERKILLING": "Restricted",
"PLAYERS": "6",
"PORT": "4000",
"PUEBLO": "0",
"QUEST SYSTEM": "Immortal Run",
"RACES": "7",
"RESETS": "35982",
"ROLEPLAYING": "Accepted",
"ROOMS": "20593",
"SKILLS": "188",
"STATUS": "Live",
"SUBGENRE": "Medieval Fantasy",
"TRAINING SYSTEM": "Level",
"UPTIME": "1774308691",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "http://exilemud.com",
"WORLD ORIGINALITY": "All Original",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.617316246032715
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:46.815740+00:00",
"host": "exilemud.com",
"ip": "198.58.123.126",
"port": 4000
},
{
"connected": "2026-04-07T06:55:45.327154+00:00",
"host": "exilemud.com",
"ip": "198.58.123.126",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug exilemud.com 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=exilemud.com port=4000
INFO client_base.py:190 Connected to <Peer 198.58.123.126 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'Exile'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'Exile'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Exile', 'PLAYERS': '6', 'UPTIME': '1774308691', 'CRAWL DELAY': '-1', 'HOSTNAME':
'exilemud.com', 'PORT': '4000', 'CODEBASE': 'CircleMUD 3.0', 'CREATED': '1996', 'IP': '198.58.123.126', 'LANGUAGE': 'English',
'LOCATION': 'United States of America', 'MINIMUM AGE': '0', 'WEBSITE': 'http://exilemud.com', 'FAMILY': 'DikuMUD', 'GENRE':
'Fantasy', 'GAMEPLAY': 'Hack and Slash', 'STATUS': 'Live', 'GAMESYSTEM': 'Custom', 'INTERMUD': '', 'SUBGENRE': 'Medieval
Fantasy', 'AREAS': '159', 'HELPFILES': '1111', 'MOBILES': '3404', 'OBJECTS': '5800', 'ROOMS': '20593', 'CLASSES': '9',
'LEVELS': '180', 'RACES': '7', 'SKILLS': '188', 'ANSI': '1', 'GMCP': '0', 'MCCP': '0', 'MCP': '0', 'MSDP': '1', 'MSP': '0',
'MXP': '1', 'PUEBLO': '0', 'UTF-8': '1', 'VT100': '0', 'XTERM 256 COLORS': '1', 'PAY TO PLAY': '0', 'PAY FOR PERKS': '0',
'HIRING BUILDERS': '0', 'HIRING CODERS': '0', 'EXITS': '49135', 'EXTRA DESCRIPTIONS': '1216', 'MUDTRIGS': '761', 'RESETS':
'35982', 'ADULT MATERIAL': '0', 'MULTICLASSING': '1', 'PLAYER CITIES': '0', 'PLAYER CLANS': '1', 'EQUIPMENT SYSTEM': 'Level',
'MULTIPLAYING': 'Restricted', 'PLAYERKILLING': 'Restricted', 'QUEST SYSTEM': 'Immortal Run', 'ROLEPLAYING': 'Accepted',
'TRAINING SYSTEM': 'Level', 'WORLD ORIGINALITY': 'All Original'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, WILL MSP, WILL MCCP2_COMPRESS, WILL AARDWOLF, WILL ZMP, WILL MSDP, WILL MSSP,
WILL MCCP3_COMPRESS, DO MXP, DO GMCP, DO MCCP2_COMPRESS, DO AARDWOLF, DO ZMP, DO ATCP, DO MCCP3_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 198.58.123.126 4000>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b