gizmomud.com
Connection Banner:
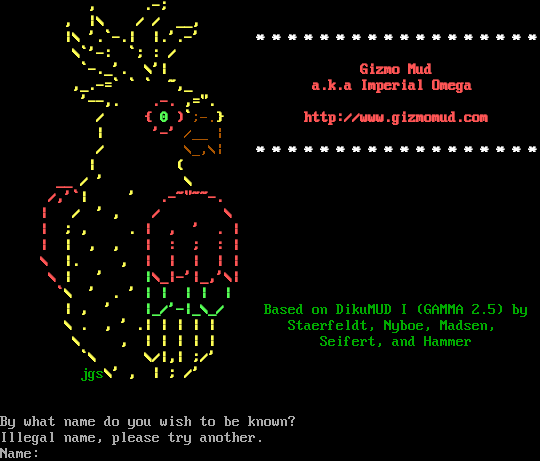
Server URLs
- Telnet: telnet://gizmomud.com:6969
- Website: http://www.gizmomud.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal name, please try another.\n\rName: ",
"banner_before_return": "\u0000\r\n\r\n\u001b[1m\u001b[33m , .-;\r\n\u001b[1m\u001b[33m , |\\ / / __,\r\n\u001b[1m\u001b[33m |\\ '.`-.| |.'.-' \u001b[1m\u001b[37m* * * * * * * * * * * * * * * * * *\r\n\u001b[1m\u001b[33m \\`'-: `; : /\r\n\u001b[1m\u001b[33m `-._'. \\'| \u001b[1m\u001b[31mGizmo Mud\r\n\u001b[1m\u001b[33m ,_.-=` ` ` ~,_ \u001b[1m\u001b[31ma.k.a Imperial Omega\r\n\u001b[1m\u001b[33m '--,. \u001b[1m\u001b[31m.-. \u001b[1m\u001b[33m,=\".\r\n\u001b[1m\u001b[33m / \u001b[1m\u001b[31m{ \u001b[1m\u001b[32m0 \u001b[1m\u001b[31m)\u001b[1m\u001b[33m`\u001b[0m\u001b[33m;-.\u001b[1m\u001b[33m} \u001b[1m\u001b[31mhttp://www.gizmomud.com\r\n\u001b[1m\u001b[33m | \u001b[1m\u001b[31m'-' \u001b[0m\u001b[33m/__ |\r\n\u001b[1m\u001b[33m / \u001b[0m\u001b[33m\\_,\\| \u001b[1m\u001b[37m* * * * * * * * * * * * * * * * * *\r\n\u001b[1m\u001b[33m | (\r\n\u001b[1m\u001b[31m __ \u001b[1m\u001b[33m/ ' \\ \r\n\u001b[1m\u001b[31m /,'`\u001b[1m\u001b[33m| ' \u001b[1m\u001b[31m.-~\"~~-.\r\n\u001b[1m\u001b[31m | \u001b[1m\u001b[33m/ ' , \u001b[1m\u001b[31m/ \\ \r\n\u001b[1m\u001b[31m | \u001b[1m\u001b[33m; , . \u001b[1m\u001b[31m| , ' . |\r\n\u001b[1m\u001b[31m | \u001b[1m\u001b[33m| , , \u001b[1m\u001b[31m| : ; : |\r\n\u001b[1m\u001b[31m \\ \u001b[1m\u001b[33m|. , \u001b[1m\u001b[31m| | | | |\r\n\u001b[1m\u001b[31m \\ \u001b[1m\u001b[33m| ' \u001b[1m\u001b[32m|\u001b[1m\u001b[31m\\_|-'|_,'\\|\r\n\u001b[1m\u001b[31m `\u001b[1m\u001b[33m\\ ' . ' \u001b[1m\u001b[32m| | | | |\r\n\u001b[1m\u001b[33m | , ' \u001b[1m\u001b[32m|_/'-|_\\_/ \u001b[0m\u001b[32mBased on DikuMUD I (GAMMA 2.5) by\r\n\u001b[1m\u001b[33m \\ . , ' .| | | | | \u001b[0m\u001b[32mStaerfeldt, Nyboe, Madsen,\r\n\u001b[1m\u001b[33m \\ , | | | | | \u001b[0m\u001b[32mSeifert, and Hammer\r\n\u001b[1m\u001b[33m `\\ \\/|,| ;/'\r\n\u001b[0m\u001b[32m jgs\u001b[1m\u001b[33m\\' , | ; /' \u001b[0m\r\n\r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5042896270751953,
"total": 11.136465549468994
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:46.000768+00:00",
"host": "gizmomud.com",
"ip": "147.160.225.77",
"port": 6969
},
{
"connected": "2026-04-07T06:57:29.091430+00:00",
"host": "gizmomud.com",
"ip": "147.160.225.77",
"port": 6969
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug gizmomud.com 6969
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=gizmomud.com port=6969
INFO client_base.py:190 Connected to <Peer 147.160.225.77 6969>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:1447 IAC NOP: Null Operation (unhandled).
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MSSP, WILL MXP, WILL AARDWOLF, WILL MSDP, WILL GMCP, WILL ZMP,
WILL ATCP, WILL MCCP2_COMPRESS, WILL MSP, DO MCCP3_COMPRESS, DO MSSP, DO MXP, DO AARDWOLF, DO MSDP, DO GMCP, DO ZMP, DO ATCP,
DO MCCP2_COMPRESS, DO MSP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 147.160.225.77 6969>