haelrahv.com
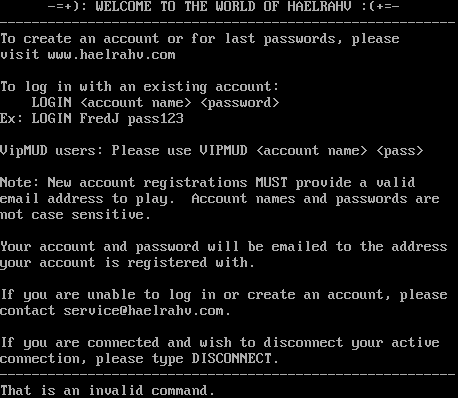
Connection Banner:
Server URLs
- Telnet: telnet://haelrahv.com:3001
- Website: www.haelrahv.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "That is an invalid command.\r\n",
"banner_before_return": " -=+): WELCOME TO THE WORLD OF HAELRAHV :(+=-\r\n---------------------------------------------------------\r\nTo create an account or for last passwords, please \r\nvisit www.haelrahv.com\r\n \r\nTo log in with an existing account:\r\n LOGIN <account name> <password>\r\nEx: LOGIN FredJ pass123\r\n \r\nVipMUD users: Please use VIPMUD <account name> <pass>\r\n \r\nNote: New account registrations MUST provide a valid\r\nemail address to play. Account names and passwords are\r\nnot case sensitive.\r\n \r\nYour account and password will be emailed to the address\r\nyour account is registered with.\r\n \r\nIf you are unable to log in or create an account, please\r\ncontact service@haelrahv.com.\r\n \r\nIf you are connected and wish to disconnect your active\r\nconnection, please type DISCONNECT.\r\n---------------------------------------------------------\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5040762424468994,
"total": 11.054424285888672
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:49.194928+00:00",
"host": "haelrahv.com",
"ip": "72.24.177.106",
"port": 3001
},
{
"connected": "2026-04-07T06:57:54.453475+00:00",
"host": "haelrahv.com",
"ip": "72.24.177.106",
"port": 3001
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug haelrahv.com 3001
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=haelrahv.com port=3001
INFO client_base.py:190 Connected to <Peer 72.24.177.106 3001>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, WILL MSP, WILL AARDWOLF, WILL GMCP,
WILL ZMP, WILL ATCP, WILL MSSP, WILL MSDP, DO MXP, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO MSP, DO AARDWOLF, DO GMCP, DO ZMP,
DO ATCP, DO MSSP, DO MSDP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 72.24.177.106 3001>