216.167.189.34 (coimuck.com)
Chronicles of Ivalice: Emberstrand (coimuck.com:1771)
Connection Banner:
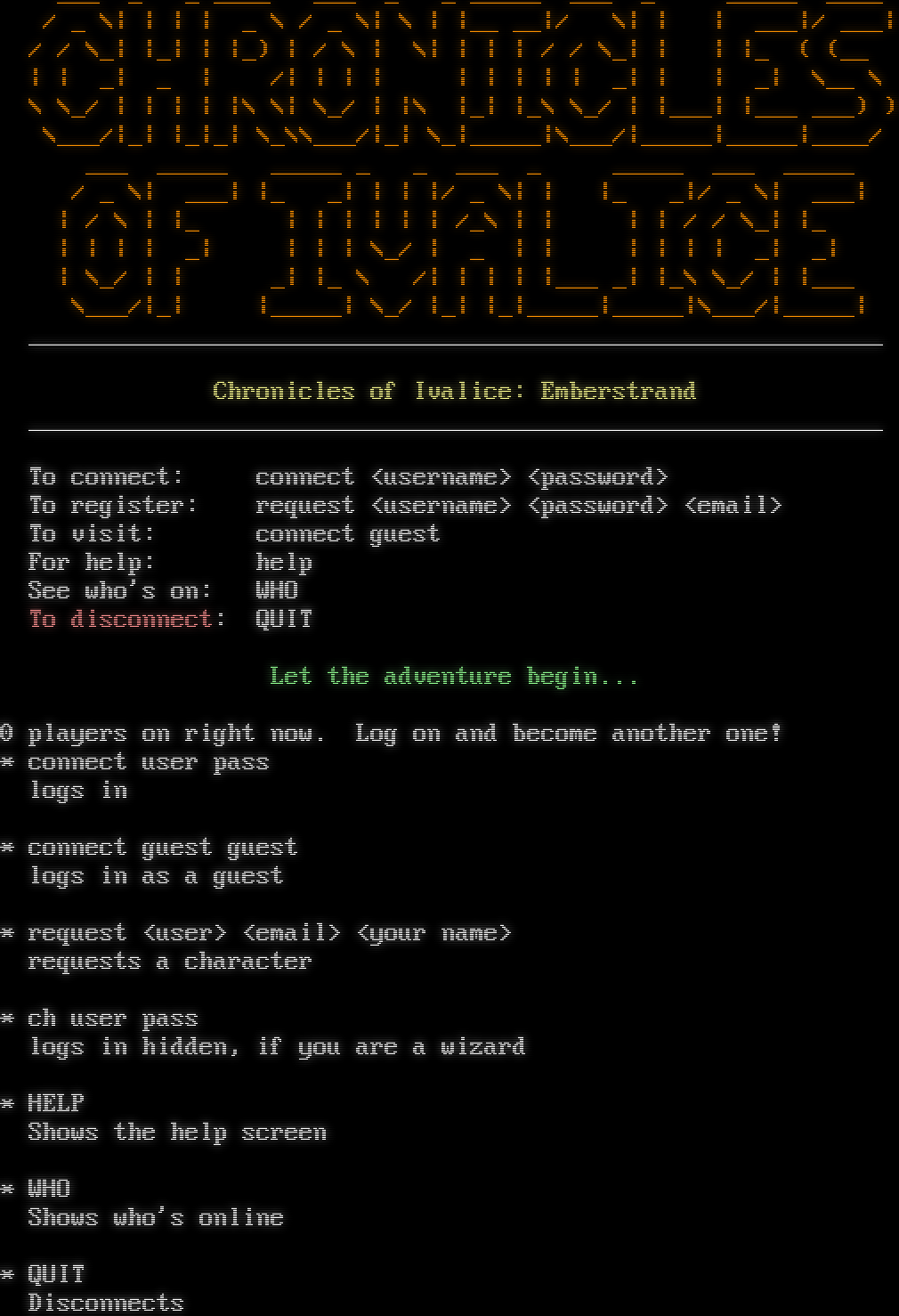
Server URLs
- Telnet: telnet://coimuck.com:1771
- Website: http://www.coimuck.com/
Server Info
Codebase: ProtoMUCK
Players online: 0 [1]
Uptime: 30 days
Created: 2009
Status: Open Beta
Server Location: 🇺🇸 United States (GeoIP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: No
MCCP: Yes (MSSP)
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: MSSP
Options requested from client: NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "3dc27f894ea465a2",
"fingerprint-data": {
"offered-options": [
"MSSP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": " \r\n* connect user pass\r\n logs in\r\n \r\n* connect guest guest\r\n logs in as a guest\r\n \r\n* request <user> <email> <your name>\r\n requests a character\r\n \r\n* ch user pass\r\n logs in hidden, if you are a wizard\r\n \r\n* HELP\r\n Shows the help screen\r\n \r\n* WHO\r\n Shows who's online\r\n \r\n* QUIT\r\n Disconnects\r\n \r\n\r\n",
"banner_before_return": "\n\u001b[0;33m ___ _ _ ____ ___ _ _ _____ ___ _ _____ ____ \u001b[0m\u001b[0m\r\n\u001b[0;33m / _ \\| | | | _ \\ / _ \\| \\ | |__ __|/ \\| | | ___|/ ___| \u001b[0m\u001b[0m\r\n\u001b[0;33m / / \\_| |_| | |_) | / \\ | \\| | | | / / \\_| | | |_ ( (__ \u001b[0m\u001b[0m\r\n\u001b[0;33m | | _| _ | /| | | | | | | | | _| | | _| \\__ \\ \u001b[0m\u001b[0m\r\n\u001b[0;33m \\ \\_/ | | | | |\\ \\| \\_/ | |\\ |_| |_\\ \\_/ | |___| |___ ___) ) \u001b[0m\u001b[0m\r\n\u001b[0;33m \\___/|_| |_|_| \\_\\\\___/|_| \\_|_____|\\___/|_____|_____|____/ \u001b[0m\u001b[0m\r\n\u001b[0;33m ___ _____ _____ _ _ ___ _ _____ ___ _____ \u001b[0m\u001b[0m\r\n\u001b[0;33m / _ \\| ___| |_ _| | | |/ _ \\| | |_ _|/ _ \\| ___| \u001b[0m\u001b[0m\r\n\u001b[0;33m | / \\ | |_ | | | | | | /_\\ | | | | / / \\_| |_ \u001b[0m\u001b[0m\r\n\u001b[0;33m | | | | _| | | | \\_/ | _ | | | | | | _| _| \u001b[0m\u001b[0m\r\n\u001b[0;33m | \\_/ | | _| |_ \\ /| | | | |___ _| |_\\ \\_/ | |___ \u001b[0m\u001b[0m\r\n\u001b[0;33m \\___/|_| |_____| \\_/ |_| |_|_____|_____|\\___/|_____| \u001b[0m\u001b[0m\r\n\u001b[1;37m ____________________________________________________________ \u001b[0m\u001b[0m\r\n \r\n \u001b[1;33mChronicles of Ivalice: Emberstrand\u001b[0m \u001b[0m\r\n\u001b[1;37m ____________________________________________________________ \u001b[0m\u001b[0m\r\n \r\n \u001b[1;37mTo connect\u001b[0m: connect <username> <password> \u001b[0m\r\n \u001b[1;37mTo register\u001b[0m: request <username> <password> <email> \u001b[0m\r\n \u001b[1;37mTo visit\u001b[0m: connect guest \u001b[0m\r\n \u001b[1;37mFor help\u001b[0m: help \u001b[0m\r\n \u001b[1;37mSee who's on\u001b[0m: WHO \u001b[0m\r\n \u001b[1;31mTo disconnect\u001b[0m: QUIT \u001b[0m\r\n \r\n \u001b[1;32mLet the adventure begin...\u001b[0m\u001b[0m\r\n \r\n0 players on right now. Log on and become another one!\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "ProtoMUCK",
"CREATED": "2009",
"FAMILY": "MUCK",
"HOSTNAME": "coimuck.com",
"IP": "66.207.168.118",
"LANGUAGE": "English",
"MCCP": "1",
"NAME": "Chronicles of Ivalice: Emberstrand",
"PLAYERS": "0",
"PORT": "1771",
"STATUS": "Open Beta",
"UPTIME": "1768456412",
"WEBSITE": "http://www.coimuck.com/"
},
"option_states": {
"server_offered": {
"0x56": false,
"MSSP": true
},
"server_requested": {
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.2568974494934082,
"total": 5.036858081817627
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:10:11.596963+00:00",
"host": "coimuck.com",
"ip": "216.167.189.34",
"port": 1771
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug coimuck.com 1771
Show Logfile
DEBUG client.py:965 Fingerprint client: host=coimuck.com port=1771
INFO client_base.py:175 Connected to <Peer 216.167.189.34 1771>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:707 recv IAC WILL MSSP
DEBUG stream_writer.py:723 WILL MSSP unsolicited
DEBUG stream_writer.py:1900 handle_will(MSSP)
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 remote_option[MSSP] = True
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:707 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:723 WILL MCCP2_COMPRESS unsolicited
DEBUG stream_writer.py:1900 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:3174 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:950 send IAC DONT MCCP2_COMPRESS
WARNING stream_writer.py:2008 Unhandled: WILL MCCP2_COMPRESS.
DEBUG stream_writer.py:707 recv IAC DO TTYPE
DEBUG stream_writer.py:1770 handle_do(TTYPE)
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:950 send IAC WILL TTYPE
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3174 local_option[TTYPE] = True
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:707 recv IAC DO NAWS
DEBUG stream_writer.py:1770 handle_do(NAWS)
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:950 send IAC WILL NAWS
DEBUG stream_writer.py:2346 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3174 local_option[NAWS] = True
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:699 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:686 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2065 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1673 MSSP: {'CREATED': '2009', 'HOSTNAME': 'coimuck.com', 'IP': '66.207.168.118', 'LANGUAGE': 'English',
'NAME': 'Chronicles of Ivalice: Emberstrand', 'PORT': '1771', 'STATUS': 'Open Beta', 'WEBSITE': 'http://www.coimuck.com/',
'PLAYERS': '0', 'UPTIME': '1768456412', 'ANSI': '1', 'CODEBASE': 'ProtoMUCK', 'FAMILY': 'MUCK', 'MCCP': '1'}
DEBUG stream_writer.py:699 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:686 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2241 recv TTYPE SEND: b''
DEBUG stream_writer.py:2254 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
DEBUG stream_writer.py:707 recv IAC WONT BINARY
DEBUG stream_writer.py:2025 handle_wont(BINARY)
DEBUG stream_writer.py:3174 remote_option[BINARY] = False
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:707 recv IAC WONT SGA
DEBUG stream_writer.py:2025 handle_wont(SGA)
DEBUG stream_writer.py:3174 remote_option[SGA] = False
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = False
DEBUG stream_writer.py:707 recv IAC WONT ECHO
DEBUG stream_writer.py:2025 handle_wont(ECHO)
DEBUG stream_writer.py:3174 remote_option[ECHO] = False
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:707 recv IAC WONT STATUS
DEBUG stream_writer.py:2025 handle_wont(STATUS)
DEBUG stream_writer.py:3174 remote_option[STATUS] = False
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:707 recv IAC WONT CHARSET
DEBUG stream_writer.py:2025 handle_wont(CHARSET)
DEBUG stream_writer.py:3174 remote_option[CHARSET] = False
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:707 recv IAC WONT EOR
DEBUG stream_writer.py:2025 handle_wont(EOR)
DEBUG stream_writer.py:3174 remote_option[EOR] = False
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = False
DEBUG stream_writer.py:707 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2025 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3174 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = False
DEBUG stream_writer.py:707 recv IAC WONT GMCP
DEBUG stream_writer.py:2025 handle_wont(GMCP)
DEBUG stream_writer.py:3174 remote_option[GMCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSDP
DEBUG stream_writer.py:2025 handle_wont(MSDP)
DEBUG stream_writer.py:3174 remote_option[MSDP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSP
DEBUG stream_writer.py:2025 handle_wont(MSP)
DEBUG stream_writer.py:3174 remote_option[MSP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = False
DEBUG stream_writer.py:707 recv IAC WONT MXP
DEBUG stream_writer.py:2025 handle_wont(MXP)
DEBUG stream_writer.py:3174 remote_option[MXP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = False
DEBUG stream_writer.py:707 recv IAC WONT ZMP
DEBUG stream_writer.py:2025 handle_wont(ZMP)
DEBUG stream_writer.py:3174 remote_option[ZMP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:707 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2025 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3174 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:707 recv IAC WONT ATCP
DEBUG stream_writer.py:2025 handle_wont(ATCP)
DEBUG stream_writer.py:3174 remote_option[ATCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = False
INFO fingerprinting.py:737 new server fingerprint 3dc27f894ea465a2
INFO client_base.py:106 Connection closed to <Peer 216.167.189.34 1771>
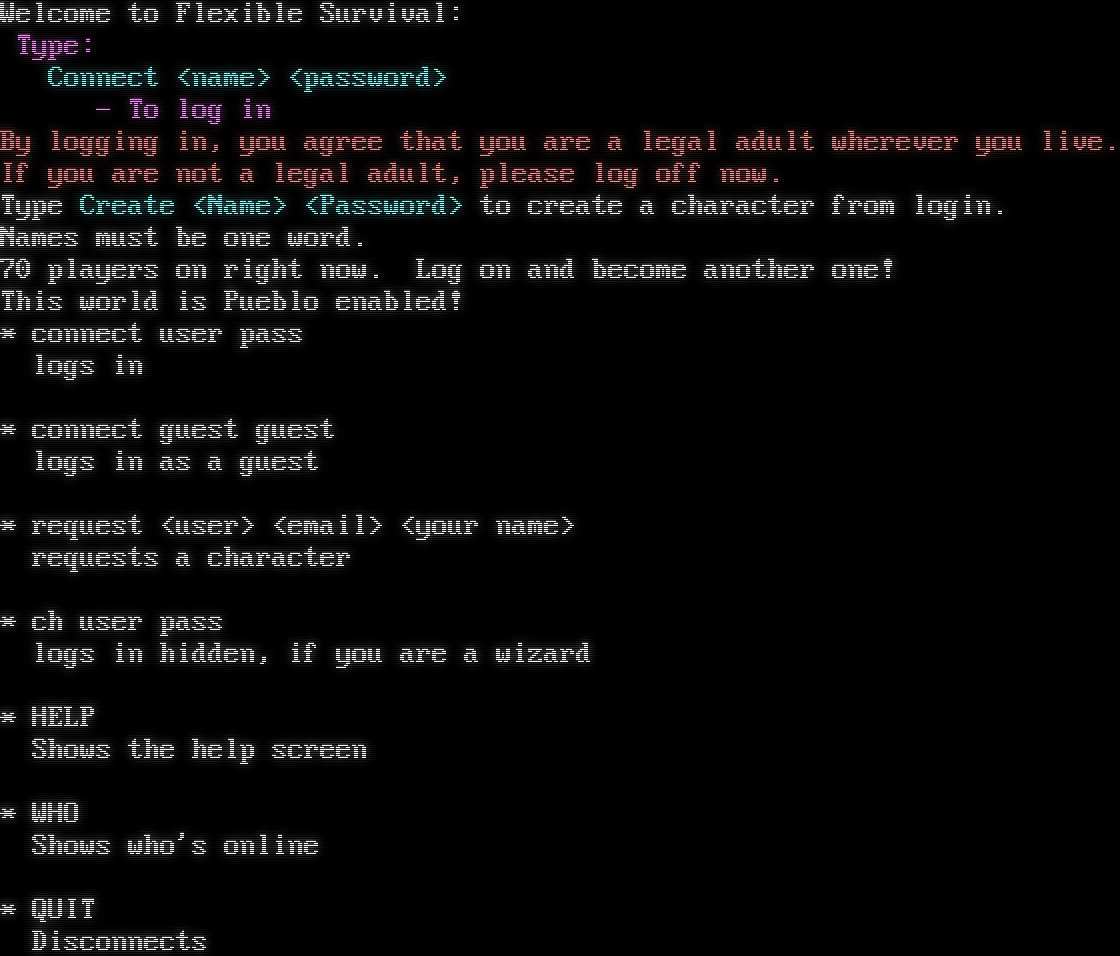
flexiblesurvival.com:2000
Connection Banner:
Server URLs
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 20 other servers.
Options requested from client: NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "6e6641437dab4b1b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": " \r\n* connect user pass\r\n logs in\r\n \r\n* connect guest guest\r\n logs in as a guest\r\n \r\n* request <user> <email> <your name>\r\n requests a character\r\n \r\n* ch user pass\r\n logs in hidden, if you are a wizard\r\n \r\n* HELP\r\n Shows the help screen\r\n \r\n* WHO\r\n Shows who's online\r\n \r\n* QUIT\r\n Disconnects\r\n \r\n\r\n",
"banner_before_return": "\r\nWelcome to Flexible Survival: \r\n\u001b[1;35m Type: \u001b[0m\r\n\u001b[1;36m Connect <name> <password>\u001b[0m\r\n\u001b[1;35m - To log in \u001b[0m\r\n\u001b[1;31mBy logging in, you agree that you are a legal adult wherever you live.\u001b[0m\r\n\u001b[1;31mIf you are not a legal adult, please log off now.\u001b[0m\r\nType \u001b[1;36mCreate <Name> <Password>\u001b[0m to create a character from login.\u001b[0m\r\nNames must be one word.\r\n70 players on right now. Log on and become another one!\r\nThis world is Pueblo enabled!\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MSSP": false
},
"server_requested": {
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.3597888946533203,
"total": 5.148417949676514
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:26.214871+00:00",
"host": "flexiblesurvival.com",
"ip": "216.167.189.34",
"port": 2000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug flexiblesurvival.com 2000
Show Logfile
DEBUG client.py:965 Fingerprint client: host=flexiblesurvival.com port=2000
INFO client_base.py:175 Connected to <Peer 216.167.189.34 2000>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:707 recv IAC WILL MSSP
DEBUG stream_writer.py:723 WILL MSSP unsolicited
DEBUG stream_writer.py:1900 handle_will(MSSP)
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 remote_option[MSSP] = True
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:707 recv IAC DO TTYPE
DEBUG stream_writer.py:1770 handle_do(TTYPE)
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:950 send IAC WILL TTYPE
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3174 local_option[TTYPE] = True
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:707 recv IAC DO NAWS
DEBUG stream_writer.py:1770 handle_do(NAWS)
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:950 send IAC WILL NAWS
DEBUG stream_writer.py:2346 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3174 local_option[NAWS] = True
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:707 recv IAC WONT MSSP
DEBUG stream_writer.py:2025 handle_wont(MSSP)
DEBUG stream_writer.py:3174 remote_option[MSSP] = False
DEBUG stream_writer.py:699 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:686 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2241 recv TTYPE SEND: b''
DEBUG stream_writer.py:2254 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
DEBUG stream_writer.py:707 recv IAC WONT BINARY
DEBUG stream_writer.py:2025 handle_wont(BINARY)
DEBUG stream_writer.py:3174 remote_option[BINARY] = False
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:707 recv IAC WONT SGA
DEBUG stream_writer.py:2025 handle_wont(SGA)
DEBUG stream_writer.py:3174 remote_option[SGA] = False
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = False
DEBUG stream_writer.py:707 recv IAC WONT ECHO
DEBUG stream_writer.py:2025 handle_wont(ECHO)
DEBUG stream_writer.py:3174 remote_option[ECHO] = False
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:707 recv IAC WONT STATUS
DEBUG stream_writer.py:2025 handle_wont(STATUS)
DEBUG stream_writer.py:3174 remote_option[STATUS] = False
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:707 recv IAC WONT CHARSET
DEBUG stream_writer.py:2025 handle_wont(CHARSET)
DEBUG stream_writer.py:3174 remote_option[CHARSET] = False
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:707 recv IAC WONT EOR
DEBUG stream_writer.py:2025 handle_wont(EOR)
DEBUG stream_writer.py:3174 remote_option[EOR] = False
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = False
DEBUG stream_writer.py:707 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2025 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3174 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = False
DEBUG stream_writer.py:707 recv IAC WONT GMCP
DEBUG stream_writer.py:2025 handle_wont(GMCP)
DEBUG stream_writer.py:3174 remote_option[GMCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSDP
DEBUG stream_writer.py:2025 handle_wont(MSDP)
DEBUG stream_writer.py:3174 remote_option[MSDP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSP
DEBUG stream_writer.py:2025 handle_wont(MSP)
DEBUG stream_writer.py:3174 remote_option[MSP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = False
DEBUG stream_writer.py:707 recv IAC WONT MXP
DEBUG stream_writer.py:2025 handle_wont(MXP)
DEBUG stream_writer.py:3174 remote_option[MXP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = False
DEBUG stream_writer.py:707 recv IAC WONT ZMP
DEBUG stream_writer.py:2025 handle_wont(ZMP)
DEBUG stream_writer.py:3174 remote_option[ZMP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:707 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2025 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3174 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:707 recv IAC WONT ATCP
DEBUG stream_writer.py:2025 handle_wont(ATCP)
DEBUG stream_writer.py:3174 remote_option[ATCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = False
INFO fingerprinting.py:746 connection for server fingerprint 6e6641437dab4b1b
INFO client_base.py:106 Connection closed to <Peer 216.167.189.34 2000>
ginkosoft.com:8898
Connection Banner:
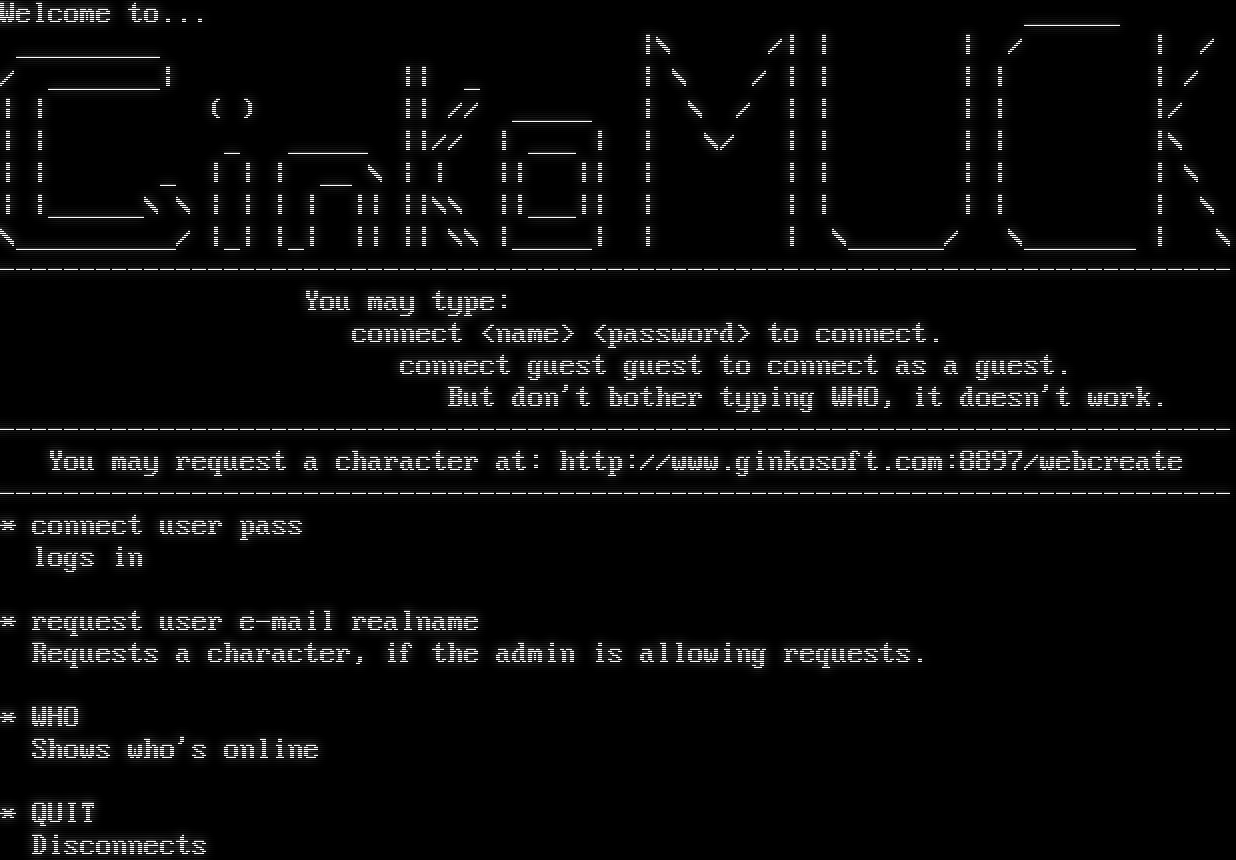
Server URLs
- Telnet: telnet://ginkosoft.com:8898
- Website: http://www.ginkosoft.com:8897/webcreate
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 20 other servers.
Options requested from client: NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "6e6641437dab4b1b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "* connect user pass\r\n logs in\r\n\r\n* request user e-mail realname\r\n Requests a character, if the admin is allowing requests.\r\n\r\n* WHO\r\n Shows who's online\r\n\r\n* QUIT\r\n Disconnects\r\n",
"banner_before_return": "Welcome to... ______\r\n _________ |\\ /| | | / | /\r\n/ _______| || _ | \\ / | | | | | /\r\n| | ( ) || // _____ | \\ / | | | | |/\r\n| | _ _____ ||// | ___ | | \\/ | | | | |\\\r\n| | _ | | | __ \\ | | || || | | | | | | \\\r\n| |______\\ \\ | | | | || ||\\\\ ||___|| | | | | | | \\\r\n\\__________/ |_| |_| || || \\\\ |_____| | | \\______/ \\_______ | \\\r\n-----------------------------------------------------------------------------\r\n You may type:\r\n connect <name> <password> to connect.\r\n connect guest guest to connect as a guest.\r\n But don't bother typing WHO, it doesn't work.\r\n-----------------------------------------------------------------------------\r\n You may request a character at: http://www.ginkosoft.com:8897/webcreate\r\n-----------------------------------------------------------------------------\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MSSP": false
},
"server_requested": {
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.25862669944763184,
"total": 5.037543535232544
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:09:55.798661+00:00",
"host": "ginkosoft.com",
"ip": "216.167.189.34",
"port": 8898
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ginkosoft.com 8898
Show Logfile
DEBUG client.py:965 Fingerprint client: host=ginkosoft.com port=8898
INFO client_base.py:175 Connected to <Peer 216.167.189.34 8898>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:707 recv IAC WILL MSSP
DEBUG stream_writer.py:723 WILL MSSP unsolicited
DEBUG stream_writer.py:1900 handle_will(MSSP)
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 remote_option[MSSP] = True
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:707 recv IAC DO TTYPE
DEBUG stream_writer.py:1770 handle_do(TTYPE)
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:950 send IAC WILL TTYPE
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3174 local_option[TTYPE] = True
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:707 recv IAC DO NAWS
DEBUG stream_writer.py:1770 handle_do(NAWS)
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:950 send IAC WILL NAWS
DEBUG stream_writer.py:2346 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3174 local_option[NAWS] = True
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:707 recv IAC WONT MSSP
DEBUG stream_writer.py:2025 handle_wont(MSSP)
DEBUG stream_writer.py:3174 remote_option[MSSP] = False
DEBUG stream_writer.py:699 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:686 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2241 recv TTYPE SEND: b''
DEBUG stream_writer.py:2254 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
DEBUG stream_writer.py:707 recv IAC WONT BINARY
DEBUG stream_writer.py:2025 handle_wont(BINARY)
DEBUG stream_writer.py:3174 remote_option[BINARY] = False
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:707 recv IAC WONT SGA
DEBUG stream_writer.py:2025 handle_wont(SGA)
DEBUG stream_writer.py:3174 remote_option[SGA] = False
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = False
DEBUG stream_writer.py:707 recv IAC WONT ECHO
DEBUG stream_writer.py:2025 handle_wont(ECHO)
DEBUG stream_writer.py:3174 remote_option[ECHO] = False
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:707 recv IAC WONT STATUS
DEBUG stream_writer.py:2025 handle_wont(STATUS)
DEBUG stream_writer.py:3174 remote_option[STATUS] = False
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:707 recv IAC WONT CHARSET
DEBUG stream_writer.py:2025 handle_wont(CHARSET)
DEBUG stream_writer.py:3174 remote_option[CHARSET] = False
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:707 recv IAC WONT EOR
DEBUG stream_writer.py:2025 handle_wont(EOR)
DEBUG stream_writer.py:3174 remote_option[EOR] = False
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = False
DEBUG stream_writer.py:707 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2025 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3174 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = False
DEBUG stream_writer.py:707 recv IAC WONT GMCP
DEBUG stream_writer.py:2025 handle_wont(GMCP)
DEBUG stream_writer.py:3174 remote_option[GMCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSDP
DEBUG stream_writer.py:2025 handle_wont(MSDP)
DEBUG stream_writer.py:3174 remote_option[MSDP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSP
DEBUG stream_writer.py:2025 handle_wont(MSP)
DEBUG stream_writer.py:3174 remote_option[MSP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = False
DEBUG stream_writer.py:707 recv IAC WONT MXP
DEBUG stream_writer.py:2025 handle_wont(MXP)
DEBUG stream_writer.py:3174 remote_option[MXP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = False
DEBUG stream_writer.py:707 recv IAC WONT ZMP
DEBUG stream_writer.py:2025 handle_wont(ZMP)
DEBUG stream_writer.py:3174 remote_option[ZMP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:707 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2025 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3174 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:707 recv IAC WONT ATCP
DEBUG stream_writer.py:2025 handle_wont(ATCP)
DEBUG stream_writer.py:3174 remote_option[ATCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = False
INFO fingerprinting.py:746 connection for server fingerprint 6e6641437dab4b1b
INFO client_base.py:106 Connection closed to <Peer 216.167.189.34 8898>
rustedpromises.com:9630
Connection Banner:
![/\\ /::\\ \| :: \| \| :: \| ______ _ _ \| :: \| \| ___ \\ \| \| \| \| \| :: \| \| \|_/ / _ ___\| \|_ ___ __\| \| \| :: \| \| / \| \| / __\| __/ _ \\/ _\` \| \| :: \| \| \|\\ \\ \|_\| \\__ \\ \|\| __/ (_\| \| \| :: \| \\_\| \\_\\__,_\|___/\\__\\___\|\\__,_\| \| :: \| \| :: \| ______ _ \| :: \| \| ___ \\ (_) \| :: \| \| \|_/ / __ ___ _ __ ___ _ ___ ___ ___ \| :: \| \| __/ '__/ _ \\\| '_ \` _ \\\| / __\|/ _ \\/ __\| \| :: \| \| \| \| \| \| (_) \| \| \| \| \| \| \\__ \\ __/\\__ \\ \| :: \| \\_\| \|_\| \\___/\|_\| \|_\| \|_\|_\|___/\\___\|\|___/ \| :: \| 1 \| :: \| 1 8b \| :: \| d8 Welcome to Rusted Promises: 88b ,%\| :: \|%, d88 888b%%%%\| :: \|%%%%d888 Type: "Y88888[[[]]]88888Y" connect <name> <password> [[[]]] - To log in [[[]]] Type create <name> <password> to make a character. [[[]]] Names must be one word. [[[]]] [[[]]] [[[]]] \|\|\|\|\|\| Play on the web! - http://rustedpromises.com/ {{{{}}}} For more info - http://wiki.rustedpromises.com/ {{{{{}}}}} {{{{}}}} (rustedpromises.com port 23) (__) 0 players on right now. Log on and become another one! This world is Pueblo enabled! \* connect user pass logs in \* connect guest guest logs in as a guest \* request <user> <email> <your name> requests a character \* ch user pass logs in hidden, if you are a wizard \* HELP Shows the help screen \* WHO Shows who's online \* QUIT Disconnects](../_images/banner_277bd799d07d.png)
Server URLs
- Telnet: telnet://rustedpromises.com:9630
- Website: http://rustedpromises.com/
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 20 other servers.
Options requested from client: NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "6e6641437dab4b1b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": " \r\n* connect user pass\r\n logs in\r\n \r\n* connect guest guest\r\n logs in as a guest\r\n \r\n* request <user> <email> <your name>\r\n requests a character\r\n \r\n* ch user pass\r\n logs in hidden, if you are a wizard\r\n \r\n* HELP\r\n Shows the help screen\r\n \r\n* WHO\r\n Shows who's online\r\n \r\n* QUIT\r\n Disconnects\r\n \r\n\r\n",
"banner_before_return": "\r\n /\\ \r\n /::\\\r\n | :: |\r\n | :: | ______ _ _ \r\n | :: | | ___ \\ | | | | \r\n | :: | | |_/ / _ ___| |_ ___ __| | \r\n | :: | | / | | / __| __/ _ \\/ _` | \r\n | :: | | |\\ \\ |_| \\__ \\ || __/ (_| | \r\n | :: | \\_| \\_\\__,_|___/\\__\\___|\\__,_| \r\n | :: | \r\n | :: | ______ _ \r\n | :: | | ___ \\ (_) \r\n | :: | | |_/ / __ ___ _ __ ___ _ ___ ___ ___ \r\n | :: | | __/ '__/ _ \\| '_ ` _ \\| / __|/ _ \\/ __|\r\n | :: | | | | | | (_) | | | | | | \\__ \\ __/\\__ \\\r\n | :: | \\_| |_| \\___/|_| |_| |_|_|___/\\___||___/\r\n | :: | \r\n 1 | :: | 1 \r\n 8b | :: | d8 Welcome to \u001b[1;33mRusted Promises\u001b[0m:\u001b[0m\r\n 88b ,%| :: |%, d88 \r\n 888b%%%%| :: |%%%%d888 Type: \r\n \"Y88888[[[]]]88888Y\" \u001b[1;36mconnect <name> <password>\u001b[0m \u001b[0m\r\n [[[]]] \u001b[1;35m - To log in \u001b[0m \u001b[0m\r\n [[[]]] Type \u001b[1;36mcreate <name> <password>\u001b[0m to make a character.\u001b[0m\r\n [[[]]] Names must be one word. \r\n [[[]]] \r\n [[[]]] \r\n [[[]]] \r\n |||||| Play on the web! - http://rustedpromises.com/ \r\n {{{{}}}} For more info - http://wiki.rustedpromises.com/ \r\n {{{{{}}}}} \r\n {{{{}}}} (rustedpromises.com port 23)\r\n (__) \r\n \r\n0 players on right now. Log on and become another one!\r\nThis world is Pueblo enabled!\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MSSP": false
},
"server_requested": {
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.25508952140808105,
"total": 5.0411412715911865
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:09:57.589647+00:00",
"host": "rustedpromises.com",
"ip": "216.167.189.34",
"port": 9630
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug rustedpromises.com 9630
Show Logfile
DEBUG client.py:965 Fingerprint client: host=rustedpromises.com port=9630
INFO client_base.py:175 Connected to <Peer 216.167.189.34 9630>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:707 recv IAC WILL MSSP
DEBUG stream_writer.py:723 WILL MSSP unsolicited
DEBUG stream_writer.py:1900 handle_will(MSSP)
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 remote_option[MSSP] = True
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:707 recv IAC DO TTYPE
DEBUG stream_writer.py:1770 handle_do(TTYPE)
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:950 send IAC WILL TTYPE
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3174 local_option[TTYPE] = True
DEBUG stream_writer.py:3174 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:707 recv IAC DO NAWS
DEBUG stream_writer.py:1770 handle_do(NAWS)
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:950 send IAC WILL NAWS
DEBUG stream_writer.py:2346 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3174 local_option[NAWS] = True
DEBUG stream_writer.py:3174 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:707 recv IAC WONT MSSP
DEBUG stream_writer.py:2025 handle_wont(MSSP)
DEBUG stream_writer.py:3174 remote_option[MSSP] = False
DEBUG stream_writer.py:699 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:686 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3174 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2241 recv TTYPE SEND: b''
DEBUG stream_writer.py:2254 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
DEBUG stream_writer.py:707 recv IAC WONT BINARY
DEBUG stream_writer.py:2025 handle_wont(BINARY)
DEBUG stream_writer.py:3174 remote_option[BINARY] = False
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:707 recv IAC WONT SGA
DEBUG stream_writer.py:2025 handle_wont(SGA)
DEBUG stream_writer.py:3174 remote_option[SGA] = False
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = False
DEBUG stream_writer.py:707 recv IAC WONT ECHO
DEBUG stream_writer.py:2025 handle_wont(ECHO)
DEBUG stream_writer.py:3174 remote_option[ECHO] = False
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:707 recv IAC WONT STATUS
DEBUG stream_writer.py:2025 handle_wont(STATUS)
DEBUG stream_writer.py:3174 remote_option[STATUS] = False
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:707 recv IAC WONT CHARSET
DEBUG stream_writer.py:2025 handle_wont(CHARSET)
DEBUG stream_writer.py:3174 remote_option[CHARSET] = False
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:707 recv IAC WONT EOR
DEBUG stream_writer.py:2025 handle_wont(EOR)
DEBUG stream_writer.py:3174 remote_option[EOR] = False
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = False
DEBUG stream_writer.py:707 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2025 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3174 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = False
DEBUG stream_writer.py:707 recv IAC WONT GMCP
DEBUG stream_writer.py:2025 handle_wont(GMCP)
DEBUG stream_writer.py:3174 remote_option[GMCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSDP
DEBUG stream_writer.py:2025 handle_wont(MSDP)
DEBUG stream_writer.py:3174 remote_option[MSDP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:707 recv IAC WONT MSP
DEBUG stream_writer.py:2025 handle_wont(MSP)
DEBUG stream_writer.py:3174 remote_option[MSP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = False
DEBUG stream_writer.py:707 recv IAC WONT MXP
DEBUG stream_writer.py:2025 handle_wont(MXP)
DEBUG stream_writer.py:3174 remote_option[MXP] = False
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = False
DEBUG stream_writer.py:707 recv IAC WONT ZMP
DEBUG stream_writer.py:2025 handle_wont(ZMP)
DEBUG stream_writer.py:3174 remote_option[ZMP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:707 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2025 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3174 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:707 recv IAC WONT ATCP
DEBUG stream_writer.py:2025 handle_wont(ATCP)
DEBUG stream_writer.py:3174 remote_option[ATCP] = False
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = False
INFO fingerprinting.py:746 connection for server fingerprint 6e6641437dab4b1b
INFO client_base.py:106 Connection closed to <Peer 216.167.189.34 9630>