37.59.41.114 (condor.rorscha.ch)
tbaMUD (37.59.41.114:3001)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes ________ ___ \\_____ \\______ __\| _/ _(__ <_ __ \\/ __ \| / \\ \| \\/ /_/ \| telnet://3m.vineyard.haus 3001 /______ /__\| \\____ \| https://3m.vineyard.haus \\/ \\/ ___ ___ /'\\_/\`\\ __ /\\_ \\ /\\_ \\ __ /\\ \\/\\_\\\\//\\ \\ \\//\\ \\ __ ___ ___ /\\_\\ __ __ ___ ___ \\ \\ \\__\\ \\/\\ \\ \\ \\ \\ \\ \\ \\ /'__\`\\/' _ \`\\ /' _ \`\\/\\ \\/\\ \\/\\ \\ /' __\` __\`\\ \\ \\ \\_/\\ \\ \\ \\ \\_\\ \\_ \\_\\ \\_/\\ __//\\ \\/\\ \\/\\ \\/\\ \\ \\ \\ \\ \\_\\ \\/\\ \\/\\ \\/\\ \\ \\ \\_\\\\ \\_\\ \\_\\/\\____\\/\\____\\ \\____\\ \\_\\ \\_\\ \\_\\ \\_\\ \\_\\ \\____/\\ \\_\\ \\_\\ \\_\\ \\/_/ \\/_/\\/_/\\/____/\\/____/\\/____/\\/_/\\/_/\\/_/\\/_/\\/_/\\/___/ \\/_/\\/_/\\/_/ _____ __ __ /____/\\ /_/\| /_/\| ADMINS \| __ \\/\|___ ____ ___ __ _ __\| \|\|__ __ _ __ ___ _\| \|\| ~~~~~~ \| \|__) \|/__/_/__/___/\\ /_ / /__\| \|/_/__/_/__/___/\\/_\| \|\| Opie, Plex \| _ // _ \\ '_ \` _ \\ / _\` / __\| __/ _ \\ '__/ _ \\/ _\` \|\| & Veekster \| \| \\ \\ __/ \| \| \| \| \| (_\| \\__ \\ \|\| __/ \| \| __/ (_\| \|\| \|_\|/ \\_\\___\|_\|/\|_\|/\|_\|\\__,_\|___/\\__\\___\|_\|/ \\___\|\\__,_\|/ Login:](../_images/banner_7fd5fe968cbd.png)
Server URLs
- Telnet: telnet://37.59.41.114:3001
- Website: 3m.vineyard.haus
Server Info
Players online: 0 [1]
Uptime: 35 days
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "tbaMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\n\u001b[38;5;226m\r\n ________ ___\r\n \\_____ \\______ __| _/\r\n _(__ <_ __ \\/ __ |\r\n / \\ | \\/ /_/ | \u001b[0;00mtelnet://3m.vineyard.haus 3001\u001b[38;5;226m\r\n /______ /__| \\____ | \u001b[0;00mhttps://3m.vineyard.haus\u001b[38;5;226m\r\n \\/ \\/\u001b[38;5;021m\r\n ___ ___\r\n /'\\_/`\\ __ /\\_ \\ /\\_ \\ __\r\n /\\ \\/\\_\\\\//\\ \\ \\//\\ \\ __ ___ ___ /\\_\\ __ __ ___ ___\r\n \\ \\ \\__\\ \\/\\ \\ \\ \\ \\ \\ \\ \\ /'__`\\/' _ `\\ /' _ `\\/\\ \\/\\ \\/\\ \\ /' __` __`\\\r\n \\ \\ \\_/\\ \\ \\ \\ \\_\\ \\_ \\_\\ \\_/\\ __//\\ \\/\\ \\/\\ \\/\\ \\ \\ \\ \\ \\_\\ \\/\\ \\/\\ \\/\\ \\\r\n \\ \\_\\\\ \\_\\ \\_\\/\\____\\/\\____\\ \\____\\ \\_\\ \\_\\ \\_\\ \\_\\ \\_\\ \\____/\\ \\_\\ \\_\\ \\_\\\r\n \\/_/ \\/_/\\/_/\\/____/\\/____/\\/____/\\/_/\\/_/\\/_/\\/_/\\/_/\\/___/ \\/_/\\/_/\\/_/\u001b[0;00m\r\n _____ __ __\r\n /____/\\ /_/| /_/|\r\n ADMINS | __ \\/|___ ____ ___ __ _ __| ||__ __ _ __ ___ _| ||\r\n \u001b[38;5;046m~~~~~~\u001b[0;00m | |__) |/__/_/__/___/\\ /_ / /__| |/_/__/_/__/___/\\/_| ||\r\n Opie, Plex | _ // _ \\ '_ ` _ \\ / _` / __| __/ _ \\ '__/ _ \\/ _` ||\r\n & Veekster | | \\ \\ __/ | | | | | (_| \\__ \\ || __/ | | __/ (_| ||\r\n |_|/ \\_\\___|_|/|_|/|_|\\__,_|___/\\__\\___|_|/ \\___|\\__,_|/\r\n\r\n\r\nLogin:",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "tbaMUD",
"PLAYERS": "0",
"UPTIME": "1772477741"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.748571395874023
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:54.467014+00:00",
"host": "37.59.41.114",
"ip": "37.59.41.114",
"port": 3001
},
{
"connected": "2026-04-07T07:02:03.983368+00:00",
"host": "37.59.41.114",
"ip": "37.59.41.114",
"port": 3001
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 37.59.41.114 3001
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=37.59.41.114 port=3001
INFO client_base.py:190 Connected to <Peer 37.59.41.114 3001>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'tbaMUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'tbaMUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'tbaMUD', 'PLAYERS': '0', 'UPTIME': '1772477741', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, WILL MSDP, WILL ZMP, WILL GMCP,
WILL MSP, WILL MSSP, DO AARDWOLF, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO ZMP, DO ATCP, DO GMCP, DO MXP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 3001>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
adventmud.vineyard.haus:8310
Connection Banner:
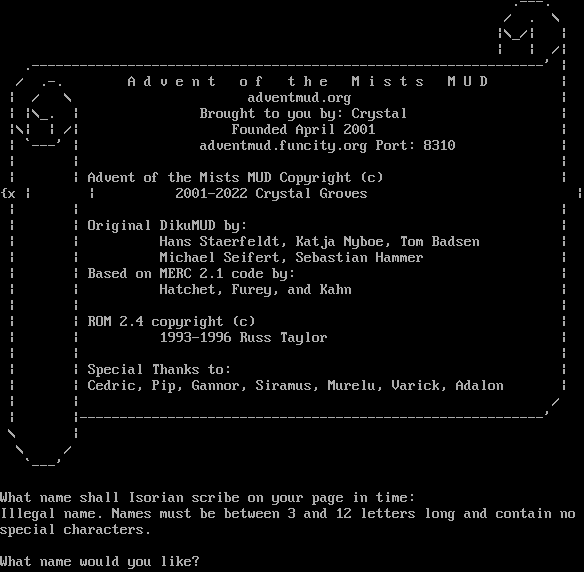
Server URLs
- Telnet: telnet://adventmud.vineyard.haus:8310
- Website: adventmud.org
Server Info
Server Location: 🇫🇷 France (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\n\rIllegal name. Names must be between 3 and 12 letters long and contain no\n\rspecial characters.\n\r\n\rWhat name would you like? ",
"banner_before_return": "\n\r\n\r .---.\n\r / . \\\n\r |\\_/| |\n\r | | /|\n\r .----------------------------------------------------------------' |\n\r / .-. A d v e n t o f t h e M i s t s M U D |\n\r | / \\ adventmud.org |\n\r | |\\_. | Brought to you by: Crystal |\n\r |\\| | /| Founded April 2001 |\n\r | `---' | adventmud.funcity.org Port: 8310 |\n\r | | | \n\r | | Advent of the Mists MUD Copyright (c) | \n\r{x | | 2001-2022 Crystal Groves | \n\r | | |\n\r | | Original DikuMUD by: | \n\r | | Hans Staerfeldt, Katja Nyboe, Tom Badsen | \n\r | | Michael Seifert, Sebastian Hammer | \n\r | | Based on MERC 2.1 code by: | \n\r | | Hatchet, Furey, and Kahn | \n\r | | | \n\r | | ROM 2.4 copyright (c) | \n\r | | 1993-1996 Russ Taylor | \n\r | | | \n\r | | Special Thanks to: | \n\r | | Cedric, Pip, Gannor, Siramus, Murelu, Varick, Adalon | \n\r | | /\n\r | |----------------------------------------------------------'\n\r \\ |\n\r \\ /\n\r `---'\n\r\n\rWhat name shall Isorian scribe on your page in time: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5047621726989746,
"total": 11.390268564224243
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:03.860693+00:00",
"host": "adventmud.vineyard.haus",
"ip": "37.59.41.114",
"port": 8310
},
{
"connected": "2026-04-07T07:13:17.143444+00:00",
"host": "adventmud.vineyard.haus",
"ip": "37.59.41.114",
"port": 8310
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug adventmud.vineyard.haus 8310
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=adventmud.vineyard.haus port=8310
INFO client_base.py:190 Connected to <Peer 37.59.41.114 8310>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSDP, WILL MCCP2_COMPRESS, WILL ATCP, WILL AARDWOLF, WILL MCCP3_COMPRESS, WILL MSP,
WILL MSSP, WILL MXP, WILL ZMP, WILL GMCP, DO MSDP, DO MCCP2_COMPRESS, DO ATCP, DO AARDWOLF, DO MCCP3_COMPRESS, DO MSP, DO
MSSP, DO MXP, DO ZMP, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 8310>
PhoenixMud (condor.rorscha.ch:4001)
Connection Banner:
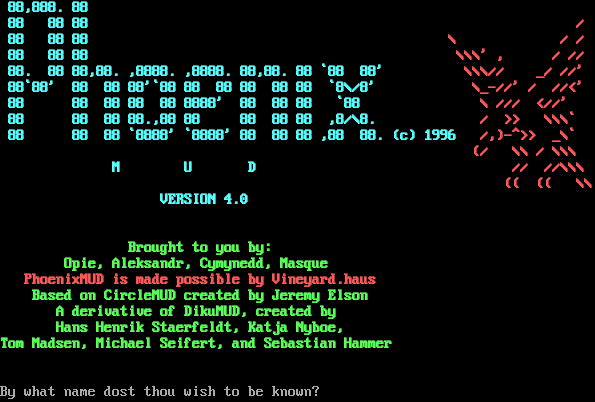
Server URLs
- Telnet: telnet://condor.rorscha.ch:4001
- Website: https://phoenixmud.net
Server Info
Codebase: PhoenixMUD, CircleMUD, DikuMUD, AberMUD
Genre: Fantasy
Players online: 0 [2]
Uptime: 80 days
Created: 1996
Status: Live
Discord: https://discord.gg/dUE3Nm2rEE
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\n\u001b[1m\r\n\r\n\u001b[36m 88,888. 88 \u001b[31m \r\n\u001b[36m 88 88 88 \u001b[31m /\r\n\u001b[36m 88 88 88 \u001b[31m \\ / /\r\n\u001b[36m 88 88 88 \u001b[31m \\\\\\' , / //\r\n\u001b[36m 88. 88 88,88. ,8888. ,8888. 88,88. 88 `88 88' \u001b[31m \\\\\\// _/ //'\r\n\u001b[36m 88`88' 88 88 88'`88 88 88 88 88 88 `8\\/8' \u001b[31m \\_-//' / //<'\r\n\u001b[36m 88 88 88 88 88 8888' 88 88 88 `88 \u001b[31m \\ /// <//' \r\n\u001b[36m 88 88 88 88.,88 88 88 88 88 ,8/\\8. \u001b[31m / >> \\\\\\` \r\n\u001b[36m 88 88 88 `8888' `8888' 88 88 88 ,88 88. (c) 1996\u001b[31m /,)-^>> _\\` \r\n\u001b[36m \u001b[31m (/ \\\\ / \\\\\\ \r\n\u001b[36m M U D \u001b[31m // //\\\\\\\r\n\u001b[36m \u001b[31m (( (( \\\\ \r\n\u001b[36m\t \t VERSION 4.0\t\t\t \u001b[31m \r\n\u001b[36m\t\t\t\t\t\t \u001b[31m \r\n\r\n\u001b[32m Brought to you by: \r\n\u001b[32m Opie, Aleksandr, Cymynedd, Masque \r\n\u001b[31m PhoenixMUD is made possible by Vineyard.haus \r\n\u001b[32m Based on CircleMUD created by Jeremy Elson \r\n\u001b[32m A derivative of DikuMUD, created by \r\n\u001b[32m Hans Henrik Staerfeldt, Katja Nyboe, \r\n\u001b[32mTom Madsen, Michael Seifert, and Sebastian Hammer \u001b[0m\r\n\r\nPlease wait\u001b[2K\r\nBy what name dost thou wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"AREAS": "276",
"CLASSES": "15",
"CREATED": "1996",
"DISCORD": "https://discord.gg/dUE3Nm2rEE",
"FAMILY": [
"PhoenixMUD",
"CircleMUD",
"DikuMUD",
"AberMUD"
],
"GENRE": "Fantasy",
"HELPFILES": "574",
"HOSTNAME": "phoenixmud.net",
"LEVELS": "410",
"MOBILES": "6217",
"NAME": "PhoenixMud",
"OBJECTS": "8102",
"PLAYERS": "0",
"PORT": "4000",
"RACES": "15",
"ROOMS": "20685",
"SKILLS": "206",
"STATUS": "Live",
"UPTIME": "1768622311",
"WEBSITE": "https://phoenixmud.net"
},
"option_states": {
"server_offered": {
"GMCP": true,
"MSDP": true,
"MSSP": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.741794586181641
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:51:32.880782+00:00",
"host": "condor.rorscha.ch",
"ip": "37.59.41.114",
"port": 4001
},
{
"connected": "2026-04-07T06:46:33.864502+00:00",
"host": "condor.rorscha.ch",
"ip": "37.59.41.114",
"port": 4001
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug condor.rorscha.ch 4001
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=condor.rorscha.ch port=4001
INFO client_base.py:190 Connected to <Peer 37.59.41.114 4001>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'PhoenixMud', 'PLAYERS': '0', 'UPTIME': '1768622311', 'CREATED': '1996', 'DISCORD':
'https://discord.gg/dUE3Nm2rEE', 'HOSTNAME': 'phoenixmud.net', 'PORT': '4000', 'WEBSITE': 'https://phoenixmud.net', 'FAMILY':
['PhoenixMUD', 'CircleMUD', 'DikuMUD', 'AberMUD'], 'GENRE': 'Fantasy', 'STATUS': 'Live', 'AREAS': '276', 'HELPFILES': '574',
'MOBILES': '6217', 'OBJECTS': '8102', 'ROOMS': '20685', 'CLASSES': '15', 'LEVELS': '410', 'RACES': '15', 'SKILLS': '206',
'ANSI': '1'}
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MSP, WILL MXP, WILL AARDWOLF, WILL MCCP3_COMPRESS, WILL ATCP,
WILL MSDP, WILL ZMP, WILL MSSP, WILL GMCP, DO MCCP2_COMPRESS, DO MSP, DO MXP, DO AARDWOLF, DO MCCP3_COMPRESS, DO ATCP, DO ZMP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 4001>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
PhoenixMud (condor.rorscha.ch:9000)
Connection Banner:
Server URLs
- Telnet: telnet://condor.rorscha.ch:9000
- Website: https://phoenixmud.net
Server Info
Codebase: PhoenixMUD, CircleMUD, DikuMUD, AberMUD
Genre: Fantasy
Players online: 0 [3]
Uptime: 145 days
Created: 1996
Status: Live
Discord: https://discord.gg/dUE3Nm2rEE
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\n\u001b[1m\r\n\r\n\u001b[36m 88,888. 88 \u001b[31m \r\n\u001b[36m 88 88 88 \u001b[31m /\r\n\u001b[36m 88 88 88 \u001b[31m \\ / /\r\n\u001b[36m 88 88 88 \u001b[31m \\\\\\' , / //\r\n\u001b[36m 88. 88 88,88. ,8888. ,8888. 88,88. 88 `88 88' \u001b[31m \\\\\\// _/ //'\r\n\u001b[36m 88`88' 88 88 88'`88 88 88 88 88 88 `8\\/8' \u001b[31m \\_-//' / //<'\r\n\u001b[36m 88 88 88 88 88 8888' 88 88 88 `88 \u001b[31m \\ /// <//' \r\n\u001b[36m 88 88 88 88.,88 88 88 88 88 ,8/\\8. \u001b[31m / >> \\\\\\` \r\n\u001b[36m 88 88 88 `8888' `8888' 88 88 88 ,88 88. (c) 1996\u001b[31m /,)-^>> _\\` \r\n\u001b[36m \u001b[31m (/ \\\\ / \\\\\\ \r\n\u001b[36m M U D \u001b[31m // //\\\\\\\r\n\u001b[36m \u001b[31m (( (( \\\\ \r\n\u001b[36m\t \t VERSION 4.0\t\t\t \u001b[31m \r\n\u001b[36m\t\t\t\t\t\t \u001b[31m \r\n\r\n\u001b[32m Brought to you by: \r\n\u001b[32m Opie, Aleksandr, Cymynedd, Masque \r\n\u001b[31m PhoenixMUD is made possible by Vineyard.haus \r\n\u001b[32m Based on CircleMUD created by Jeremy Elson \r\n\u001b[32m A derivative of DikuMUD, created by \r\n\u001b[32m Hans Henrik Staerfeldt, Katja Nyboe, \r\n\u001b[32mTom Madsen, Michael Seifert, and Sebastian Hammer \u001b[0m\r\n\r\nPlease wait\u001b[2K\r\nBy what name dost thou wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"AREAS": "400",
"CLASSES": "15",
"CREATED": "1996",
"DISCORD": "https://discord.gg/dUE3Nm2rEE",
"FAMILY": [
"PhoenixMUD",
"CircleMUD",
"DikuMUD",
"AberMUD"
],
"GENRE": "Fantasy",
"HELPFILES": "513",
"HOSTNAME": "phoenixmud.net",
"LEVELS": "410",
"MOBILES": "7080",
"NAME": "PhoenixMud",
"OBJECTS": "9325",
"PLAYERS": "0",
"PORT": "4000",
"RACES": "15",
"ROOMS": "24670",
"SKILLS": "206",
"STATUS": "Live",
"UPTIME": "1763011704",
"WEBSITE": "https://phoenixmud.net"
},
"option_states": {
"server_offered": {
"MSSP": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.744972229003906
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:12:40.889146+00:00",
"host": "condor.rorscha.ch",
"ip": "37.59.41.114",
"port": 9000
},
{
"connected": "2026-04-07T06:56:11.859591+00:00",
"host": "condor.rorscha.ch",
"ip": "37.59.41.114",
"port": 9000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug condor.rorscha.ch 9000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=condor.rorscha.ch port=9000
INFO client_base.py:190 Connected to <Peer 37.59.41.114 9000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'PhoenixMud', 'PLAYERS': '0', 'UPTIME': '1763011704', 'CREATED': '1996', 'DISCORD':
'https://discord.gg/dUE3Nm2rEE', 'HOSTNAME': 'phoenixmud.net', 'PORT': '4000', 'WEBSITE': 'https://phoenixmud.net', 'FAMILY':
['PhoenixMUD', 'CircleMUD', 'DikuMUD', 'AberMUD'], 'GENRE': 'Fantasy', 'STATUS': 'Live', 'AREAS': '400', 'HELPFILES': '513',
'MOBILES': '7080', 'OBJECTS': '9325', 'ROOMS': '24670', 'CLASSES': '15', 'LEVELS': '410', 'RACES': '15', 'SKILLS': '206',
'ANSI': '1'}
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, WILL MSDP, WILL GMCP, WILL AARDWOLF, WILL MXP,
WILL ATCP, WILL ZMP, WILL MSSP, WILL MSP, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO MSDP, DO GMCP, DO AARDWOLF, DO MXP, DO
ATCP, DO ZMP, DO MSP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 9000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
PhoenixMud (phoenixmud.net:4000)
Connection Banner:
Server URLs
- Telnet: telnet://phoenixmud.net:4000
- Play in Browser: LociTerm
- Website: https://phoenixmud.net
Server Info
Codebase: PhoenixMUD, CircleMUD, DikuMUD, AberMUD
Genre: Fantasy
Players online: 0 [4]
Uptime: 9 days
Created: 1996
Status: Live
Discord: https://discord.gg/dUE3Nm2rEE
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\n\u001b[1m\r\n\r\n\u001b[36m 88,888. 88 \u001b[31m \r\n\u001b[36m 88 88 88 \u001b[31m /\r\n\u001b[36m 88 88 88 \u001b[31m \\ / /\r\n\u001b[36m 88 88 88 \u001b[31m \\\\\\' , / //\r\n\u001b[36m 88. 88 88,88. ,8888. ,8888. 88,88. 88 `88 88' \u001b[31m \\\\\\// _/ //'\r\n\u001b[36m 88`88' 88 88 88'`88 88 88 88 88 88 `8\\/8' \u001b[31m \\_-//' / //<'\r\n\u001b[36m 88 88 88 88 88 8888' 88 88 88 `88 \u001b[31m \\ /// <//' \r\n\u001b[36m 88 88 88 88.,88 88 88 88 88 ,8/\\8. \u001b[31m / >> \\\\\\` \r\n\u001b[36m 88 88 88 `8888' `8888' 88 88 88 ,88 88. (c) 1996\u001b[31m /,)-^>> _\\` \r\n\u001b[36m \u001b[31m (/ \\\\ / \\\\\\ \r\n\u001b[36m M U D \u001b[31m // //\\\\\\\r\n\u001b[36m \u001b[31m (( (( \\\\ \r\n\u001b[36m\t \t VERSION 4.0\t\t\t \u001b[31m \r\n\u001b[36m\t\t\t\t\t\t \u001b[31m \r\n\r\n\u001b[32m Brought to you by: \r\n\u001b[32m Opie, Aleksandr, Cymynedd, Masque \r\n\u001b[31m PhoenixMUD is made possible by Vineyard.haus \r\n\u001b[32m Based on CircleMUD created by Jeremy Elson \r\n\u001b[32m A derivative of DikuMUD, created by \r\n\u001b[32m Hans Henrik Staerfeldt, Katja Nyboe, \r\n\u001b[32mTom Madsen, Michael Seifert, and Sebastian Hammer \u001b[0m\r\n\r\nPlease wait\u001b[2K\r\nBy what name dost thou wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"AREAS": "276",
"CLASSES": "15",
"CREATED": "1996",
"DISCORD": "https://discord.gg/dUE3Nm2rEE",
"FAMILY": [
"PhoenixMUD",
"CircleMUD",
"DikuMUD",
"AberMUD"
],
"GENRE": "Fantasy",
"HELPFILES": "574",
"HOSTNAME": "phoenixmud.net",
"LEVELS": "410",
"MOBILES": "6217",
"NAME": "PhoenixMud",
"OBJECTS": "8102",
"PLAYERS": "0",
"PORT": "4000",
"RACES": "15",
"ROOMS": "20685",
"SKILLS": "206",
"STATUS": "Live",
"UPTIME": "1774734796",
"WEBSITE": "https://phoenixmud.net"
},
"option_states": {
"server_offered": {
"GMCP": true,
"MSDP": true,
"MSSP": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.7409210205078125
}
}
},
"sessions": [
{
"connected": "2026-03-07T05:04:28.669011+00:00",
"host": "phoenixmud.net",
"ip": "37.59.41.114",
"port": 4000
},
{
"connected": "2026-04-07T07:14:03.875923+00:00",
"host": "phoenixmud.net",
"ip": "37.59.41.114",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug phoenixmud.net 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=phoenixmud.net port=4000
INFO client_base.py:190 Connected to <Peer 37.59.41.114 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'PhoenixMud', 'PLAYERS': '0', 'UPTIME': '1774734796', 'CREATED': '1996', 'DISCORD':
'https://discord.gg/dUE3Nm2rEE', 'HOSTNAME': 'phoenixmud.net', 'PORT': '4000', 'WEBSITE': 'https://phoenixmud.net', 'FAMILY':
['PhoenixMUD', 'CircleMUD', 'DikuMUD', 'AberMUD'], 'GENRE': 'Fantasy', 'STATUS': 'Live', 'AREAS': '276', 'HELPFILES': '574',
'MOBILES': '6217', 'OBJECTS': '8102', 'ROOMS': '20685', 'CLASSES': '15', 'LEVELS': '410', 'RACES': '15', 'SKILLS': '206',
'ANSI': '1'}
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL ATCP, WILL ZMP, WILL GMCP, WILL MSP, WILL MXP,
WILL MSDP, WILL MSSP, WILL MCCP3_COMPRESS, DO AARDWOLF, DO MCCP2_COMPRESS, DO ATCP, DO ZMP, DO MSP, DO MXP, DO MCCP3_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 4000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
timesmud.com:8500
Connection Banner:
Server URLs
- Telnet: telnet://timesmud.com:8500
Server Info
Server Location: 🇫🇷 France (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\n\u001b[0;40;37mPlease type yes or no followed by enter. ",
"banner_before_return": "Welcome to Medieval Times MUD. If you are using a screen reader\r\nplease type yes, else, enter no.\u001b[0;40;37m ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5035040378570557,
"total": 11.263267278671265
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:44.066916+00:00",
"host": "timesmud.com",
"ip": "37.59.41.114",
"port": 8500
},
{
"connected": "2026-04-07T06:56:16.167493+00:00",
"host": "timesmud.com",
"ip": "37.59.41.114",
"port": 8500
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug timesmud.com 8500
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=timesmud.com port=8500
INFO client_base.py:190 Connected to <Peer 37.59.41.114 8500>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSDP, WILL MCCP3_COMPRESS, WILL MCCP2_COMPRESS, WILL MXP, WILL AARDWOLF, WILL MSP,
WILL ZMP, WILL MSSP, WILL ATCP, WILL GMCP, DO MSDP, DO MCCP3_COMPRESS, DO MCCP2_COMPRESS, DO MXP, DO AARDWOLF, DO MSP, DO ZMP,
DO MSSP, DO ATCP, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 8500>
wotl.vineyard.haus:3000
Connection Banner:
Server URLs
- Telnet: telnet://wotl.vineyard.haus:3000
- Website: 3m.funcity.org
Server Info
Server Location: 🇫🇷 France (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "That is not a proper response.\r\nDo you support the ANSI color standard (Yn)? Color is on.\r\n\u001b[2J\r\n\u001b[1;33m\r\n________ .___\r\n\\_____ \\______ __| _/\r\n _(__ <_ __ \\/ __ | \r\n / \\ | \\/ /_/ | \r\n/______ /__| \\____ | \r\n \\/ \\/ \u001b[0m\r\n\u001b[1;34m ___ ___ \r\n /'\\_/`\\ __ /\\_ \\ /\\_ \\ __ \r\n/\\ \\/\\_\\\\//\\ \\ \\//\\ \\ __ ___ ___ /\\_\\ __ __ ___ ___ \r\n\\ \\ \\__\\ \\/\\ \\ \\ \\ \\ \\ \\ \\ /'__`\\/' _ `\\ /' _ `\\/\\ \\/\\ \\/\\ \\ /' __` __`\\ \r\n \\ \\ \\_/\\ \\ \\ \\ \\_\\ \\_ \\_\\ \\_/\\ __//\\ \\/\\ \\/\\ \\/\\ \\ \\ \\ \\ \\_\\ \\/\\ \\/\\ \\/\\ \\ \r\n \\ \\_\\\\ \\_\\ \\_\\/\\____\\/\\____\\ \\____\\ \\_\\ \\_\\ \\_\\ \\_\\ \\_\\ \\____/\\ \\_\\ \\_\\ \\_\\\r\n \\/_/ \\/_/\\/_/\\/____/\\/____/\\/____/\\/_/\\/_/\\/_/\\/_/\\/_/\\/___/ \\/_/\\/_/\\/_/\r\n\u001b[0m \r\n telnet://3m.funcity.org:3000\r\n \r\n https://3m.funcity.org\r\n\r\n ADMINS: Opie - Veekster - Plex\r\n\r\n\r\nLogin: ",
"banner_before_return": "Do you support the ANSI color standard (Yn)? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 16.14717936515808
}
}
},
"sessions": [
{
"connected": "2026-03-07T05:04:39.574551+00:00",
"host": "wotl.vineyard.haus",
"ip": "37.59.41.114",
"port": 3000
},
{
"connected": "2026-04-07T07:15:42.341996+00:00",
"host": "wotl.vineyard.haus",
"ip": "37.59.41.114",
"port": 3000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug wotl.vineyard.haus 3000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=wotl.vineyard.haus port=3000
INFO client_base.py:190 Connected to <Peer 37.59.41.114 3000>
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, WILL MCCP2_COMPRESS, WILL MSSP, WILL ATCP, WILL MSP, WILL AARDWOLF, WILL MXP,
WILL MCCP3_COMPRESS, WILL MSDP, WILL ZMP, DO GMCP, DO MCCP2_COMPRESS, DO MSSP, DO ATCP, DO MSP, DO AARDWOLF, DO MXP, DO
MCCP3_COMPRESS, DO MSDP, DO ZMP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 37.59.41.114 3000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41