50.214.28.50 (muck.kitsunet.net)
RealityTorn (muck.kitsunet.net:2069)
Connection Banner:
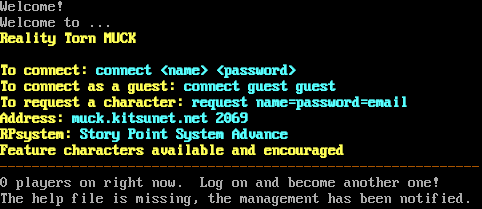
Server URLs
- Telnet: telnet://muck.kitsunet.net:2069
- Website: muck.kitsunet.net
Server Info
Codebase: ProtoMUCK
Players online: 0 [1]
Uptime: 89 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: No
MCCP: Yes (MSSP)
MCCP2: Negotiated
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 5 other servers.
Options offered by server: MCCP2, MSSP
Options requested from client: CHARSET, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "4e3f6280260df409",
"fingerprint-data": {
"offered-options": [
"MCCP2",
"MSSP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "The help file is missing, the management has been notified.\r\n",
"banner_before_return": "\n\r\nWelcome!\r\nWelcome to ...\r\n\u001b[1;33mReality Torn MUCK\u001b[0m\r\n \r\n\u001b[1;33mTo connect: \u001b[1;36mconnect <name> <password>\u001b[0m\r\n\u001b[1;33mTo connect as a guest: \u001b[1;36mconnect guest guest\u001b[0m\r\n\u001b[1;33mTo request a character: \u001b[1;36mrequest name=password=email\u001b[0m\r\n\u001b[1;33mAddress: \u001b[1;36mmuck.kitsunet.net 2069\u001b[0m\r\n\u001b[1;33mRPsystem: \u001b[1;36mStory Point System Advance\u001b[0m\r\n\u001b[1;33mFeature characters available and encouraged \u001b[0m\r\n\u001b[0;33m------------------------------------------------------------\u001b[0m\r\n0 players on right now. Log on and become another one!\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "ProtoMUCK",
"FAMILY": "MUCK",
"MCCP": "1",
"NAME": "RealityTorn",
"PLAYERS": "0",
"UPTIME": "1765096280"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.25592041015625,
"total": 10.892720222473145
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:01:56.233914+00:00",
"host": "muck.kitsunet.net",
"ip": "50.214.28.50",
"port": 2069
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug muck.kitsunet.net 2069
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=muck.kitsunet.net port=2069
ERROR client.py:1318 muck.kitsunet.net:2069: Multiple exceptions: [Errno 111] Connect call failed ('50.214.28.50', 2069), [Errno
101] Network is unreachable
TouhouMUCK (muck.kitsunet.net:22069)
Connection Banner:
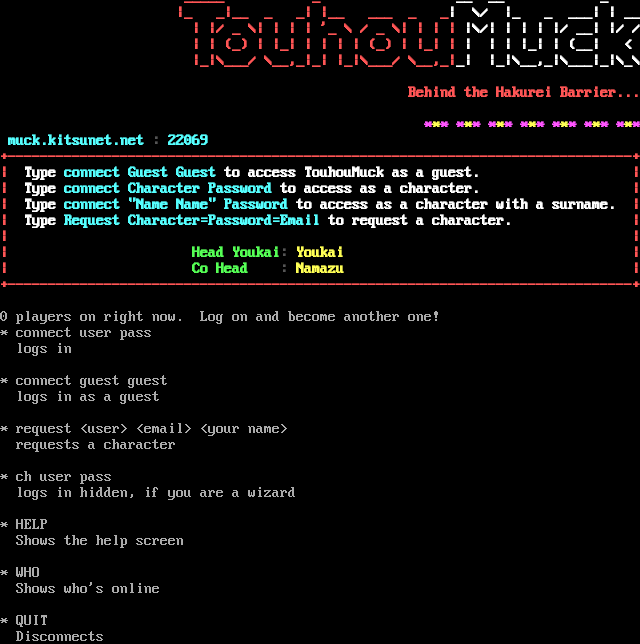
Server URLs
- Telnet: telnet://muck.kitsunet.net:22069
- Website: muck.kitsunet.net
Server Info
Codebase: ProtoMUCK
Players online: 0 [2]
Uptime: 69 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: No
MCCP: Yes (MSSP)
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options offered by server: MSSP
Options requested from client: CHARSET, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "87bf69b65eb785ac",
"fingerprint-data": {
"offered-options": [
"MSSP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": " \r\n* connect user pass\r\n logs in\r\n \r\n* connect guest guest\r\n logs in as a guest\r\n \r\n* request <user> <email> <your name>\r\n requests a character\r\n \r\n* ch user pass\r\n logs in hidden, if you are a wizard\r\n \r\n* HELP\r\n Shows the help screen\r\n \r\n* WHO\r\n Shows who's online\r\n \r\n* QUIT\r\n Disconnects\r\n \r\n\r\n",
"banner_before_return": "\n \u001b[1;31m _____ _ \u001b[1;37m __ __ _\u001b[0m\r\n \u001b[1;31m |_ _|__ _ _| |__ ___ _ _\u001b[1;37m| \\/ |_ _ ___| | __\u001b[0m\r\n \u001b[1;31m | |/ _ \\| | | | '_ \\ / _ \\| | | | \u001b[1;37m|\\/| | | | |/ __| |/ /\u001b[0m\r\n \u001b[1;31m| | (_) | |_| | | | | (_) | |_| | \u001b[1;37m| | | |_| | (__| <\u001b[0m\r\n \u001b[1;31m|_|\\___/ \\__,_|_| |_|\\___/ \\__,_|\u001b[1;37m_| |_|\\__,_|\\___|_|\\_\\\u001b[0m\r\n \r\n \u001b[1;31mBehind the Hakurei Barrier...\u001b[0m\r\n \r\n \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m* \u001b[1;35m*\u001b[1;33m*\u001b[1;35m*\u001b[0m\r\n\u001b[1;36m muck.kitsunet.net \u001b[1;30m: \u001b[1;36m22069\u001b[0m\r\n\u001b[1;31m+------------------------------------------------------------------------------+\u001b[0m\r\n\u001b[1;31m| \u001b[1;37mType \u001b[1;36mconnect Guest Guest \u001b[1;37mto access TouhouMuck as a guest. \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;37mType \u001b[1;36mconnect Character Password \u001b[1;37mto access as a character. \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;37mType \u001b[1;36mconnect \"Name Name\" Password \u001b[1;37mto access as a character with a surname. \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;37mType \u001b[1;36mRequest Character=Password=Email \u001b[1;37mto request a character. \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;32mHead Youkai\u001b[1;30m: \u001b[1;33mYoukai \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m| \u001b[1;32mCo Head \u001b[1;30m: \u001b[1;33mNamazu \u001b[1;31m|\u001b[0m\r\n\u001b[1;31m+------------------------------------------------------------------------------+\u001b[0m\r\n \r\n0 players on right now. Log on and become another one!\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "ProtoMUCK",
"FAMILY": "MUCK",
"MCCP": "1",
"NAME": "TouhouMUCK",
"PLAYERS": "0",
"UPTIME": "1765096285"
},
"option_states": {
"server_offered": {
"0x56": false,
"MSSP": true
},
"server_requested": {
"CHARSET": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.4080033302307129,
"total": 5.2124340534210205
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:48.774464+00:00",
"host": "muck.kitsunet.net",
"ip": "50.214.28.50",
"port": 22069
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug muck.kitsunet.net 22069
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=muck.kitsunet.net port=22069
ERROR client.py:1318 muck.kitsunet.net:22069: Multiple exceptions: [Errno 111] Connect call failed ('50.214.28.50', 22069), [Errno
101] Network is unreachable