5.39.80.203 (ageofdragons.com)
Age of Dragons MUD (ageofdragons.com:3333)
Connection Banner:
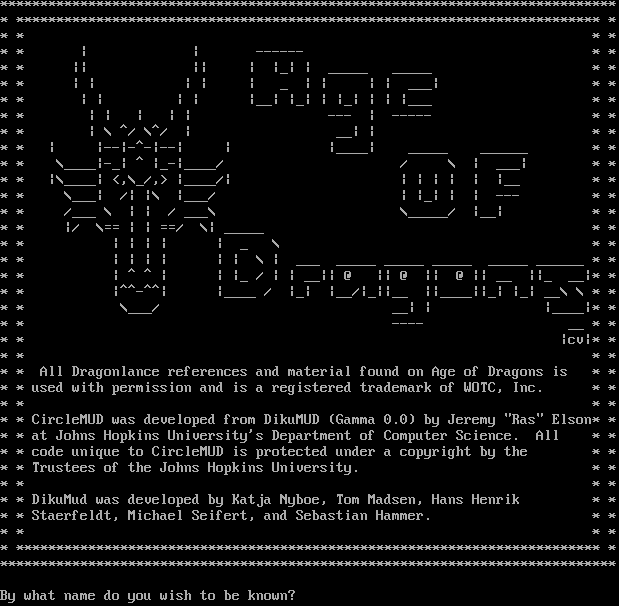
Server URLs
- Telnet: telnet://ageofdragons.com:3333
Server Info
Players online: 0 [1]
Uptime: 166 days
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Age of Dragons MUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\n\r\n\r\n*****************************************************************************\r\n* ************************************************************************* *\r\n* * * *\r\n* * | | ------ * *\r\n* * || || | |_| | _____ _____ * *\r\n* * | | | | | _ | | | | ___| * *\r\n* * | | | | |__| |_| | |_| | | |___ * *\r\n* * | | | | | --- | ----- * *\r\n* * | \\ ^/ \\^/ | __| | * *\r\n* * | |--|-^-|--| | |____| _____ ______ * *\r\n* * \\____|-_| ^ |_-|____/ / \\ | ___| * *\r\n* * |\\____| <,\\_/,> |____/| | | | | | |__ * *\r\n* * \\___| /| |\\ |___/ | |_| | | --- * *\r\n* * /___ \\ | | / ___\\ \\_____/ |__| * *\r\n* * |/ \\== | | ==/ \\| _____ * *\r\n* * | | | | | _ \\ * *\r\n* * | | | | | | \\ | ___ _____ _____ _____ _____ ______ * *\r\n* * | ^ ^ | | |_ / | | __|| @ || @ || @ || __ ||_ __|* *\r\n* * |^^-^^| |____ / |_| |__/|_||__ ||____||_| |_| __\\ \\ * *\r\n* * \\___/ __| | |____|* *\r\n* * ---- __ * *\r\n* * |cv|* *\r\n* * * *\r\n* * All Dragonlance references and material found on Age of Dragons is * *\r\n* * used with permission and is a registered trademark of WOTC, Inc. * *\r\n* * * *\r\n* * CircleMUD was developed from DikuMUD (Gamma 0.0) by Jeremy \"Ras\" Elson* *\r\n* * at Johns Hopkins University's Department of Computer Science. All * *\r\n* * code unique to CircleMUD is protected under a copyright by the * *\r\n* * Trustees of the Johns Hopkins University. * *\r\n* * * *\r\n* * DikuMud was developed by Katja Nyboe, Tom Madsen, Hans Henrik * *\r\n* * Staerfeldt, Michael Seifert, and Sebastian Hammer. * *\r\n* * * *\r\n* ************************************************************************* *\r\n*****************************************************************************\r\n\r\nBy what name do you wish to be known? \u001b[7z\u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "Age of Dragons MUD",
"PLAYERS": "0",
"UPTIME": "1761145278"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.745788335800171
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:55.377676+00:00",
"host": "ageofdragons.com",
"ip": "5.39.80.203",
"port": 3333
},
{
"connected": "2026-04-07T06:51:00.857489+00:00",
"host": "ageofdragons.com",
"ip": "5.39.80.203",
"port": 3333
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ageofdragons.com 3333
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ageofdragons.com port=3333
INFO client_base.py:190 Connected to <Peer 5.39.80.203 3333>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'Age of Dragons MUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'Age of Dragons MUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Age of Dragons MUD', 'PLAYERS': '0', 'UPTIME': '1761145278', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MSDP, WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL MSSP, WILL MSP,
WILL ZMP, WILL GMCP, DO MCCP3_COMPRESS, DO ATCP, DO MXP, DO AARDWOLF, DO MCCP2_COMPRESS, DO ZMP, DO GMCP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 5.39.80.203 3333>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
daedal-macabre.org:9000
Connection Banner:
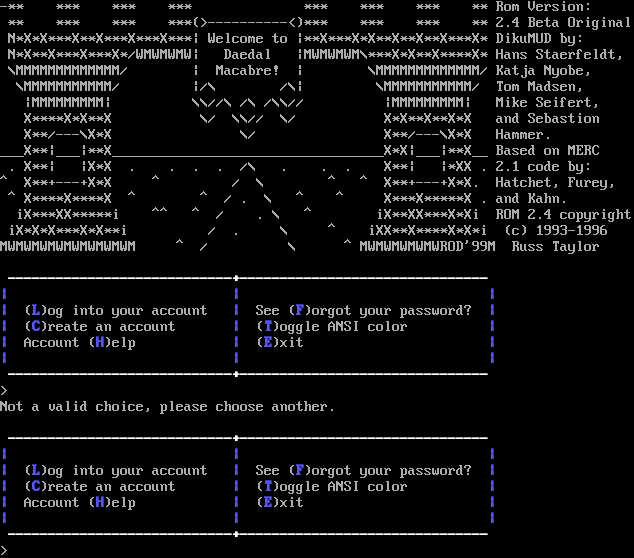
Server URLs
- Telnet: telnet://daedal-macabre.org:9000
Server Info
Server Location: 🇫🇷 France (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Not a valid choice, please choose another.\n\r\n\r\u001b[1;37m ----------------------------+------------------------------- \u001b[0m\n\r\u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m (\u001b[1;34mL\u001b[0m)og into your account \u001b[1;34m|\u001b[0m See (\u001b[1;34mF\u001b[0m)orgot your password? \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m (\u001b[1;34mC\u001b[0m)reate an account \u001b[1;34m|\u001b[0m (\u001b[1;34mT\u001b[0m)oggle ANSI color \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m Account (\u001b[1;34mH\u001b[0m)elp \u001b[1;34m|\u001b[0m (\u001b[1;34mE\u001b[0m)xit \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m\n\r\u001b[1;37m ----------------------------+------------------------------- \u001b[0m\n\r> ",
"banner_before_return": "\n\r-** *** *** *** *** *** *** ** Rom Version:\n\r ** *** *** ***(>----------<)*** *** *** ** 2.4 Beta Original\n\r N*X*X***X**X***X***X***| Welcome to |**X***X*X**X**X**X***X* DikuMUD by:\n\r N*X**X***X***X*/WMWMWMW| Daedal |MWMWMWM\\***X*X**X****X* Hans Staerfeldt,\n\r \\MMMMMMMMMMMMM/ | Macabre! | \\MMMMMMMMMMMMM/ Katja Nyobe,\n\r \\MMMMMMMMMMM/ |/\\ /\\| \\MMMMMMMMMMM/ Tom Madsen,\n\r |MMMMMMMMM| \\\\//\\ /\\ /\\\\// |MMMMMMMMM| Mike Seifert,\n\r X****X*X**X \\/ \\\\// \\/ X*X**X**X*X and Sebastion\n\r X**/---\\X*X \\/ X**/---\\X*X Hammer.\n\r___X**|___|**X__________________________________X*X|___|**X__ Based on MERC\n\r . X**| |X*X . . . . /\\ . . . X**| |*XX . 2.1 code by:\n\r^ X**+---+X*X ^ / \\ ^ ^ X**+---+X*X. Hatchet, Furey,\n\r ^ X****X****X ^ ^ / . \\ ^ ^ X***X*****X . and Kahn.\n\r iX***XX*****i ^^ ^ / . \\ ^ iX**XX***X*Xi ROM 2.4 copyright\n\r iX*X*X***X*X**i / . \\ ^ iXX**X****X*X*i (c) 1993-1996\n\rMWMWMWMWMWMWMWMWM ^ / \\ ^ MWMWMWMWMWROD'99M Russ Taylor\n\r\n\r\u001b[1;37m ----------------------------+------------------------------- \u001b[0m\n\r\u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m (\u001b[1;34mL\u001b[0m)og into your account \u001b[1;34m|\u001b[0m See (\u001b[1;34mF\u001b[0m)orgot your password? \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m (\u001b[1;34mC\u001b[0m)reate an account \u001b[1;34m|\u001b[0m (\u001b[1;34mT\u001b[0m)oggle ANSI color \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m Account (\u001b[1;34mH\u001b[0m)elp \u001b[1;34m|\u001b[0m (\u001b[1;34mE\u001b[0m)xit \u001b[1;34m|\u001b[0m\n\r\u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m \u001b[1;34m|\u001b[0m\n\r\u001b[1;37m ----------------------------+------------------------------- \u001b[0m\n\r> ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5050458908081055,
"total": 11.334874153137207
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:21:12.833455+00:00",
"host": "daedal-macabre.org",
"ip": "5.39.80.203",
"port": 9000
},
{
"connected": "2026-04-05T19:02:00.591208+00:00",
"host": "daedal-macabre.org",
"ip": "5.39.80.203",
"port": 9000
},
{
"connected": "2026-04-07T07:24:18.076761+00:00",
"host": "daedal-macabre.org",
"ip": "5.39.80.203",
"port": 9000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug daedal-macabre.org 9000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=daedal-macabre.org port=9000
INFO client_base.py:190 Connected to <Peer 5.39.80.203 9000>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL AARDWOLF, WILL MSSP, WILL MCCP2_COMPRESS, WILL ZMP, WILL ATCP, WILL GMCP,
WILL MSP, WILL MCCP3_COMPRESS, WILL MSDP, DO MXP, DO AARDWOLF, DO MSSP, DO MCCP2_COMPRESS, DO ZMP, DO ATCP, DO GMCP, DO MSP,
DO MCCP3_COMPRESS, DO MSDP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 5.39.80.203 9000>
zombiemud.net:2150
Connection Banner:
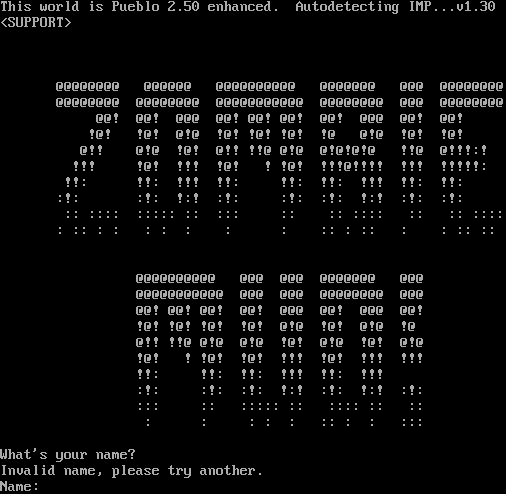
Server URLs
- Telnet: telnet://zombiemud.net:2150
Server Info
Server Location: 🇫🇷 France (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 2 other servers.
Options offered by server: MXP
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "5784853734154710",
"fingerprint-data": {
"offered-options": [
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Invalid name, please try another.\r\nName: ",
"banner_before_return": "\r\nThis world is Pueblo 2.50 enhanced. Autodetecting IMP...v1.30\n\u001b[1z<SUPPORT>\u001b[0z\n\r\n\r\n\r\n @@@@@@@@ @@@@@@ @@@@@@@@@@ @@@@@@@ @@@ @@@@@@@@\r\n @@@@@@@@ @@@@@@@@ @@@@@@@@@@@ @@@@@@@@ @@@ @@@@@@@@\r\n @@! @@! @@@ @@! @@! @@! @@! @@@ @@! @@!\r\n !@! !@! @!@ !@! !@! !@! !@ @!@ !@! !@!\r\n @!! @!@ !@! @!! !!@ @!@ @!@!@!@ !!@ @!!!:!\r\n !!! !@! !!! !@! ! !@! !!!@!!!! !!! !!!!!:\r\n !!: !!: !!! !!: !!: !!: !!! !!: !!:\r\n :!: :!: !:! :!: :!: :!: !:! :!: :!:\r\n :: :::: ::::: :: ::: :: :: :::: :: :: ::::\r\n : :: : : : : : : : :: : :: : : :: ::\r\n\r\n\r\n @@@@@@@@@@ @@@ @@@ @@@@@@@ @@@\r\n @@@@@@@@@@@ @@@ @@@ @@@@@@@@ @@@\r\n @@! @@! @@! @@! @@@ @@! @@@ @@!\r\n !@! !@! !@! !@! @!@ !@! @!@ !@\r\n @!! !!@ @!@ @!@ !@! @!@ !@! @!@\r\n !@! ! !@! !@! !!! !@! !!! !!!\r\n !!: !!: !!: !!! !!: !!!\r\n :!: :!: :!: !:! :!: !:! :!:\r\n ::: :: ::::: :: :::: :: ::\r\n : : : : : :: : : :::\r\n\r\nWhat's your name? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MXP": true
},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5036399364471436,
"total": 11.253936767578125
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:48.841058+00:00",
"host": "zombiemud.net",
"ip": "5.39.80.203",
"port": 2150
},
{
"connected": "2026-04-07T07:05:35.188763+00:00",
"host": "zombiemud.net",
"ip": "5.39.80.203",
"port": 2150
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug zombiemud.net 2150
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=zombiemud.net port=2150
INFO client_base.py:190 Connected to <Peer 5.39.80.203 2150>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL MCCP3_COMPRESS, WILL ZMP, WILL ATCP, WILL AARDWOLF, WILL MSSP, WILL MSP,
WILL MSDP, WILL MCCP2_COMPRESS, WILL GMCP, DO MCCP3_COMPRESS, DO ZMP, DO ATCP, DO AARDWOLF, DO MSSP, DO MSP, DO MSDP, DO
MCCP2_COMPRESS, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 5784853734154710
INFO client_base.py:122 Connection closed to <Peer 5.39.80.203 2150>