64.182.46.5 (cleftofdimension.com)
cleftofdimension.com:9000
Connection Banner:
![Do you want ANSI color? [Y/n] Do you want ANSI color? [Y/n] Ansi enabled! _______ _ _ _____ ____ _ _____ _____ _______ \|__ __\| \| \| \| \| \| __/ / __ \\ \| \| \| __/ \| __/ \|__ __\| \| \| \| \|__\| \| \| \|__ / / \\/ \| \| \| \|__ \| \|__ \| \| \| \| \| __ \| \| __> ( ( \| \| \| __> \| __> \| \| \| \| \| \| \| \| \| \|__ \\ \\__/\\ \| \|__/\\ \| \|__ \| \| \| \| \\ / \|_\| \|_\| \|____\\ \\____/ \|_____/ \|____\\ \|_\| \\ / V __ V o /\|\\ _____ / \\ _/_ / \| \\ \| __/ ____ \| '\|\\ /_ \\ \|\\ / \\ /\| \| \|__ \\ \\ \\___/ /\\/ O_ //\\ \| \| \| \| \| __> \\__ \\ / \| \\ \| \| \| \| \| \| \\\|_/__/ \\ \|_\|\\\|/ \|/ \\ / \\\| \| \| /// (___/ \\ \| / \\ / \\\\\\ \\\|/ V \\\|>> _____ _ __ __ _____ __ _ ____ _ ____ __ _ \| __ \\ \| \| \| \\ / \| \| __/ \| \\ \| \| / ___\| \| \| / \\ \| \\ \| \| \| \| \\ \| \| \| \| \\/ \| \| \|__ \| \\ \| \| \| \\__ \| \| \| /\\ \| \| \\ \| \| \| \| ( \| \| \| \| \|\\ /\| \| \| __> \| \|\\ \\\| \| \\__ \\ \| \| \| ( ) \| \| \|\\ \\\| \| \| \|__/ \| \| \| \| \| \\/ \| \| \| \|__ \| \| \\ \| ___\\ \| \| \| \| \\/ \| \| \| \\ \| \|_____/ \|_\| \|_\| \|_\| \|____\\ \|_\| \\__\| \|____/ \|_\| \\____/ \|_\| \\__\| ROM Version 2.4 beta Original DikuMUD by Hans Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer Based on MERC 2.1 code by Hatchet, Furey, and Kahn ROM 2.4 copyright (c) 1993-1998 Russ Taylor There came a day upon which the Cleft of Dimension itself folded, leaving only the End of Time in its wake... Please redirect to port 4000 for the newest and improved version of this MUD that has been in development since early 2001! Take note that this MUD is no longer actively supported or supervised, but remains up for archival and nostalgia purposes. What do they call you?](../_images/banner_b077d2a2c19c.png)
Server URLs
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Do you want ANSI color? [Y/n] \u001b[0;35mAnsi enabled!\u001b[0m\n\r\n\r \n\r\u001b[0;36m _______ _ _ _____ \u001b[0;35m ____ _ _____ _____ _______\n\r\u001b[0;36m |__ __| | | | | | __/ \u001b[0;35m / __ \\ | | | __/ | __/ |__ __|\n\r\u001b[0;36m | | | |__| | | |__ \u001b[0;35m / / \\/ | | | |__ | |__ | |\n\r\u001b[0;36m | | | __ | | __> \u001b[0;35m ( ( | | | __> | __> | |\n\r\u001b[0;36m | | | | | | | |__ \u001b[0;35m \\ \\__/\\ | |__/\\ | |__ | | | |\n\r\u001b[0;36m \\ / |_| |_| |____\\ \u001b[0;35m \\____/ |_____/ |____\\ |_| \\ /\n\r\u001b[0;36m V \u001b[1;33m __ \u001b[0;35m V\n\r\u001b[0m \u001b[1;33mo \u001b[1;32m /|\\ \u001b[0;33m _____ \u001b[1;33m / \\\n\r\u001b[0m \u001b[1;37m _\u001b[0;33m/\u001b[1;37m_ \u001b[1;32m / | \\ \u001b[0;33m | __/ \u001b[1;33m ____ | \u001b[1;37m'\u001b[0;33m|\\\n\r\u001b[0m \u001b[1;37m /_ \\ \u001b[1;32m |\\ / \\\u001b[0;32m /|\u001b[0;33m | |__ \u001b[1;33m \\ \\ \\___/ /\u001b[0;33m\\/\n\r\u001b[0m \u001b[1;35m O\u001b[1;37m_ /\u001b[1;31m/\\ \u001b[1;32m | | |\u001b[0;32m | \u001b[0;33m | __> \u001b[1;33m \\__ \\\n\r\u001b[0m \u001b[1;37m / | \u001b[1;31m \\ \u001b[1;32m | | |\u001b[0;32m | \u001b[0;33m | | \u001b[1;33m \\|_/__/\n\r\u001b[0m \u001b[1;37m \\ |_|\u001b[1;31m\\\u001b[0;31m|\u001b[1;31m/ \u001b[1;32m |/ \\ / \u001b[0;32m\\\u001b[1;30m|\u001b[0;33m | | \u001b[0;33m ///\n\r\u001b[0m \u001b[1;37m (___/ \u001b[1;32m \\ |\u001b[1;30m / \u001b[0;33m\\ / \u001b[0;33m \\\\\\\n\r\u001b[0m \u001b[1;32m \u001b[0;32m\\|\u001b[1;30m/ \u001b[0;33m V \u001b[0;33m \\\u001b[0;37m|>>\n\r\u001b[1;30m _____ _ \u001b[0;37m __ __ _____\u001b[1;37m __ _ \u001b[0;37m ____ _ \u001b[1;30m ____ __ _\n\r\u001b[1;30m | __ \\ | |\u001b[0;37m | \\ / | | __/\u001b[1;37m | \\ | |\u001b[0;37m / ___| | |\u001b[1;30m / \\ | \\ | |\n\r\u001b[1;30m | | \\ | | |\u001b[0;37m | \\/ | | |__ \u001b[1;37m | \\ | |\u001b[0;37m | \\__ | |\u001b[1;30m | /\\ | | \\ | |\n\r\u001b[1;30m | | ( | | |\u001b[0;37m | |\\ /| | | __>\u001b[1;37m | |\\ \\| |\u001b[0;37m \\__ \\ | |\u001b[1;30m | ( ) | | |\\ \\| |\n\r\u001b[1;30m | |__/ | | |\u001b[0;37m | | \\/ | | | |__ \u001b[1;37m | | \\ |\u001b[0;37m ___\\ | | |\u001b[1;30m | \\/ | | | \\ |\n\r\u001b[1;30m |_____/ |_|\u001b[0;37m |_| |_| |____\\\u001b[1;37m |_| \\__|\u001b[0;37m |____/ |_|\u001b[1;30m \\____/ |_| \\__|\n\r \n\r\u001b[0;37m ROM Version 2.4 beta\n\r\u001b[0;37m Original DikuMUD by Hans Staerfeldt, Katja Nyboe,\n\r\u001b[0;37m Tom Madsen, Michael Seifert, and Sebastian Hammer\n\r\u001b[0;37m Based on MERC 2.1 code by Hatchet, Furey, and Kahn\n\r\u001b[0;37m ROM 2.4 copyright (c) 1993-1998 Russ Taylor\n\r \n\rThere came a day upon which the Cleft of Dimension itself folded, leaving\n\ronly the End of Time in its wake...\n\r \n\r\u001b[1;31mPlease redirect to port 4000 for the newest and improved version of this\n\rMUD that has been in development since early 2001!\u001b[0;37m\n\r \n\rTake note that this MUD is no longer actively supported or supervised, but\n\rremains up for archival and nostalgia purposes.\n\r \n\r\u001b[0;31mWhat do they call you?\u001b[0;37m \n\r",
"banner_before_return": "\n\r\n\rDo you want ANSI color? [Y/n] ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 16.171255588531494
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:04:14.938218+00:00",
"host": "cleftofdimension.com",
"ip": "64.182.46.5",
"port": 9000
},
{
"connected": "2026-04-07T06:56:02.804475+00:00",
"host": "cleftofdimension.com",
"ip": "64.182.46.5",
"port": 9000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug cleftofdimension.com 9000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=cleftofdimension.com port=9000
INFO client_base.py:190 Connected to <Peer 64.182.46.5 9000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL AARDWOLF, WILL MSSP, WILL MCCP3_COMPRESS, WILL ZMP, WILL MCCP2_COMPRESS,
WILL ATCP, WILL MSDP, WILL GMCP, WILL MXP, DO MSP, DO AARDWOLF, DO MSSP, DO MCCP3_COMPRESS, DO ZMP, DO MCCP2_COMPRESS, DO
ATCP, DO MSDP, DO GMCP, DO MXP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 64.182.46.5 9000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
End of Time (eotmud.com:4000)
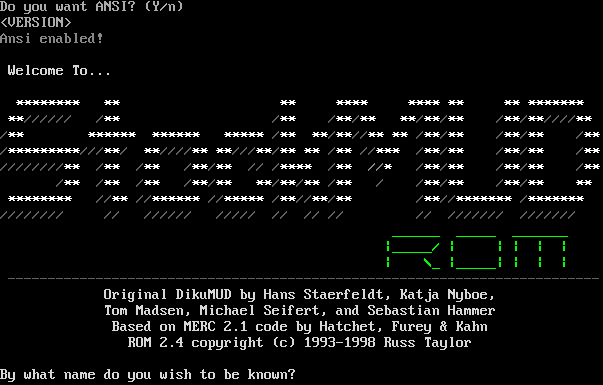
Connection Banner:
Server URLs
- Telnet: telnet://eotmud.com:4000
- Website: http://www.eotmud.com
Server Info
Codebase: Rom (EoT Custom)
Genre: Fantasy
Gameplay: Hack and Slash
Players online: 0 [1]
Uptime: 129 days
Created: 2005
Status: Live
Server Location: 🇺🇸 United States of America (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: Yes (MSSP)
MCCP: No
MCCP2: No
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options offered by server: ECHO, GMCP, MSDP, MSP, MSSP, MXP
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2bd893fec88bd438",
"fingerprint-data": {
"offered-options": [
"ECHO",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"MCCP2",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "End of Time"
}
],
"banner_after_return": "\u001b[38;5;051mFULL MODE enabled!\u001b[0;00m\u001b[1z<VERSION>\u001b[7z\r\n",
"banner_before_return": "\r\nView End of Time in full (Y) or screen reader (N) mode? \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ADULT MATERIAL": "0",
"ANSI": "1",
"AREAS": "183",
"ATCP": "1",
"CLASSES": "36",
"CODEBASE": "Rom (EoT Custom)",
"CRAWL DELAY": "-1",
"CREATED": "2005",
"EQUIPMENT SYSTEM": "Both",
"EXITS": "92890",
"EXTRA DESCRIPTIONS": "949",
"FAMILY": "DikuMUD",
"GAMEPLAY": "Hack and Slash",
"GAMESYSTEM": "None",
"GENRE": "Fantasy",
"GMCP": "1",
"HELPFILES": "1342",
"HIRING BUILDERS": "1",
"HIRING CODERS": "0",
"HOSTNAME": "eotmud.com",
"INTERMUD": "",
"IP": "66.221.0.71",
"LANGUAGE": "English",
"LEVELS": "80",
"LOCATION": "United States of America",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "0",
"MOBILES": "4362",
"MSDP": "1",
"MSP": "1",
"MULTICLASSING": "0",
"MULTIPLAYING": "Yes",
"MXP": "1",
"NAME": "End of Time",
"NEWBIE FRIENDLY": "1",
"OBJECTS": "7474",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYER CITIES": "0",
"PLAYER CLANS": "1",
"PLAYER CRAFTING": "1",
"PLAYER GUILDS": "0",
"PLAYERKILLING": "Restricted",
"PLAYERS": "0",
"PORT": "4000",
"PUEBLO": "0",
"QUEST SYSTEM": "Immortal Run, Integrated",
"RACES": "9",
"RESETS": "8415",
"ROLEPLAYING": "Accepted",
"ROOMS": "16987",
"SKILLS": "224",
"SSL": "0",
"STATUS": "Live",
"SUBGENRE": "Final Fantasy",
"TRAINING SYSTEM": "Both",
"UPTIME": "1764366783",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "http://www.eotmud.com",
"WORLD ORIGINALITY": "All Original",
"XTERM 256 COLORS": "1",
"ZMP": "0"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.503833532333374,
"total": 11.088293552398682
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:08.334672+00:00",
"host": "eotmud.com",
"ip": "64.182.46.5",
"port": 4000
},
{
"connected": "2026-04-07T06:54:46.686363+00:00",
"host": "eotmud.com",
"ip": "64.182.46.5",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug eotmud.com 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=eotmud.com port=4000
INFO client_base.py:190 Connected to <Peer 64.182.46.5 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'End of Time'
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'End of Time'}
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'End of Time', 'PLAYERS': '0', 'UPTIME': '1764366783', 'CRAWL DELAY': '-1', 'HOSTNAME':
'eotmud.com', 'PORT': '4000', 'CODEBASE': 'Rom (EoT Custom)', 'CREATED': '2005', 'IP': '66.221.0.71', 'LANGUAGE': 'English',
'LOCATION': 'United States of America', 'MINIMUM AGE': '0', 'WEBSITE': 'http://www.eotmud.com', 'FAMILY': 'DikuMUD', 'GENRE':
'Fantasy', 'GAMEPLAY': 'Hack and Slash', 'STATUS': 'Live', 'GAMESYSTEM': 'None', 'INTERMUD': '', 'SUBGENRE': 'Final Fantasy',
'AREAS': '183', 'HELPFILES': '1342', 'MOBILES': '4362', 'OBJECTS': '7474', 'ROOMS': '16987', 'CLASSES': '36', 'LEVELS': '80',
'RACES': '9', 'SKILLS': '224', 'ANSI': '1', 'GMCP': '1', 'MCCP': '0', 'MCP': '0', 'MSDP': '1', 'MSP': '1', 'MXP': '1',
'PUEBLO': '0', 'UTF-8': '1', 'VT100': '0', 'XTERM 256 COLORS': '1', 'PAY TO PLAY': '0', 'PAY FOR PERKS': '0', 'HIRING
BUILDERS': '1', 'HIRING CODERS': '0', 'EXITS': '92890', 'EXTRA DESCRIPTIONS': '949', 'RESETS': '8415', 'ADULT MATERIAL': '0',
'MULTICLASSING': '0', 'NEWBIE FRIENDLY': '1', 'PLAYER CITIES': '0', 'PLAYER CLANS': '1', 'PLAYER CRAFTING': '1', 'PLAYER
GUILDS': '0', 'EQUIPMENT SYSTEM': 'Both', 'MULTIPLAYING': 'Yes', 'PLAYERKILLING': 'Restricted', 'QUEST SYSTEM': 'Immortal Run,
Integrated', 'ROLEPLAYING': 'Accepted', 'TRAINING SYSTEM': 'Both', 'WORLD ORIGINALITY': 'All Original', 'ATCP': '1', 'SSL':
'0', 'ZMP': '0'}
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, DO MCCP2_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:773 recv IAC WONT b'\xfc'
DEBUG stream_writer.py:2199 handle_wont(WONT)
DEBUG stream_writer.py:3384 remote_option[WONT] = False
DEBUG stream_writer.py:3384 pending_option[DO + WONT] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 2bd893fec88bd438
INFO client_base.py:122 Connection closed to <Peer 64.182.46.5 4000>
StockMUD [ROM] (stockmud.com:5000)
Connection Banner:
Server URLs
- Telnet: telnet://stockmud.com:5000
- Website: http://www.stockmud.com
Server Info
Codebase: ROM 2.4
Genre: Fantasy
Gameplay: Hack and Slash
Players online: 0 [2]
Uptime: 22 days
Created: 2019
Status: Live
Server Location: 🇺🇸 United States of America (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: Yes (MSSP)
MCCP: No
MCCP2: No
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options offered by server: ECHO, GMCP, MSDP, MSP, MSSP, MXP
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2bd893fec88bd438",
"fingerprint-data": {
"offered-options": [
"ECHO",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"MCCP2",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "StockMUD [ROM]"
}
],
"banner_after_return": "\u001b[1z<VERSION>\u001b[7z\r\n\u001b[38;5;102mAnsi enabled!\u001b[0;00m\r\n\u001b[38;5;188m \n\r\u001b[38;5;188m Welcome To...\n\r\u001b[38;5;188m \n\r\u001b[38;5;231m ******** ** ** **** **** ** ** *******\u001b[38;5;188m\n\r\u001b[38;5;231m **\u001b[0;00m\u001b[38;5;241m////// /\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** **\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m////\u001b[38;5;231m**\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** ****** ****** ***** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** **\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m** ** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m*********\u001b[0;00m\u001b[38;5;241m///\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/ \u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m////\u001b[38;5;231m** **\u001b[0;00m\u001b[38;5;241m///\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** ** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m*** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m////////\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m// /\u001b[38;5;231m**** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[38;5;102m//\u001b[38;5;231m* \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m /\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** **\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/ /\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** **\u001b[38;5;188m\n\r\u001b[38;5;231m ******** \u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m****** \u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m***** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m** \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m**\u001b[0;00m\u001b[38;5;241m//\u001b[38;5;231m******* \u001b[0;00m\u001b[38;5;241m/\u001b[38;5;231m*******\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m//////// // ////// ///// // // // // /////// ///////\u001b[38;5;188m\n\r\u001b[38;5;046m ______ _____ _______\u001b[38;5;188m\n\r\u001b[38;5;046m |_____/ | | | | |\u001b[38;5;188m\n\r\u001b[38;5;046m | \\_ |_____| | | |\u001b[38;5;188m\n\r\u001b[0;00m\u001b[38;5;241m --------------------------------------------------------------------------\u001b[38;5;188m\n\r\u001b[38;5;188m Original DikuMUD by Hans Staerfeldt, Katja Nyboe,\n\r\u001b[38;5;188m Tom Madsen, Michael Seifert, and Sebastian Hammer\n\r\u001b[38;5;188m Based on MERC 2.1 code by Hatchet, Furey & Kahn\n\r\u001b[38;5;188m ROM 2.4 copyright (c) 1993-1998 Russ Taylor\n\r\u001b[38;5;188m \n\r\u001b[38;5;188mBy what name do you wish to be known? \n\r",
"banner_before_return": "Do you want ANSI? (Y/n) \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"AREAS": "49",
"CLASSES": "4",
"CODEBASE": "ROM 2.4",
"CRAWL DELAY": "-1",
"CREATED": "2019",
"FAMILY": "DikuMUD",
"GAMEPLAY": "Hack and Slash",
"GAMESYSTEM": "None",
"GENRE": "Fantasy",
"GMCP": "1",
"HELPFILES": "274",
"HIRING BUILDERS": "0",
"HIRING CODERS": "0",
"HOSTNAME": "stockmud.com",
"INTERMUD": "",
"IP": "66.221.0.71",
"LANGUAGE": "English",
"LEVELS": "51",
"LOCATION": "United States of America",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "0",
"MOBILES": "986",
"MSDP": "1",
"MSP": "1",
"MXP": "1",
"NAME": "StockMUD [ROM]",
"OBJECTS": "1268",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYERS": "0",
"PORT": "5000",
"PUEBLO": "0",
"RACES": "4",
"ROOMS": "3130",
"SKILLS": "134",
"STATUS": "Live",
"SUBGENRE": "",
"UPTIME": "1773628610",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "http://www.stockmud.com",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5046494007110596,
"total": 16.35804510116577
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:50.241748+00:00",
"host": "stockmud.com",
"ip": "64.182.46.5",
"port": 5000
},
{
"connected": "2026-04-07T07:20:59.241577+00:00",
"host": "stockmud.com",
"ip": "64.182.46.5",
"port": 5000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug stockmud.com 5000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=stockmud.com port=5000
INFO client_base.py:190 Connected to <Peer 64.182.46.5 5000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'StockMUD [ROM]'
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'StockMUD [ROM]'}
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'StockMUD [ROM]', 'PLAYERS': '0', 'UPTIME': '1773628610', 'CRAWL DELAY': '-1',
'HOSTNAME': 'stockmud.com', 'PORT': '5000', 'CODEBASE': 'ROM 2.4', 'CREATED': '2019', 'IP': '66.221.0.71', 'LANGUAGE':
'English', 'LOCATION': 'United States of America', 'MINIMUM AGE': '0', 'WEBSITE': 'http://www.stockmud.com', 'FAMILY':
'DikuMUD', 'GENRE': 'Fantasy', 'GAMEPLAY': 'Hack and Slash', 'STATUS': 'Live', 'GAMESYSTEM': 'None', 'INTERMUD': '',
'SUBGENRE': '', 'AREAS': '49', 'HELPFILES': '274', 'MOBILES': '986', 'OBJECTS': '1268', 'ROOMS': '3130', 'CLASSES': '4',
'LEVELS': '51', 'RACES': '4', 'SKILLS': '134', 'ANSI': '1', 'GMCP': '1', 'MCCP': '0', 'MCP': '0', 'MSDP': '1', 'MSP': '1',
'MXP': '1', 'PUEBLO': '0', 'UTF-8': '1', 'VT100': '0', 'XTERM 256 COLORS': '1', 'PAY TO PLAY': '0', 'PAY FOR PERKS': '0',
'HIRING BUILDERS': '0', 'HIRING CODERS': '0'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, DO MCCP2_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:773 recv IAC WONT b'\xfc'
DEBUG stream_writer.py:2199 handle_wont(WONT)
DEBUG stream_writer.py:3384 remote_option[WONT] = False
DEBUG stream_writer.py:3384 pending_option[DO + WONT] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 2bd893fec88bd438
INFO client_base.py:122 Connection closed to <Peer 64.182.46.5 5000>