isharmud.com
Connection Banner:
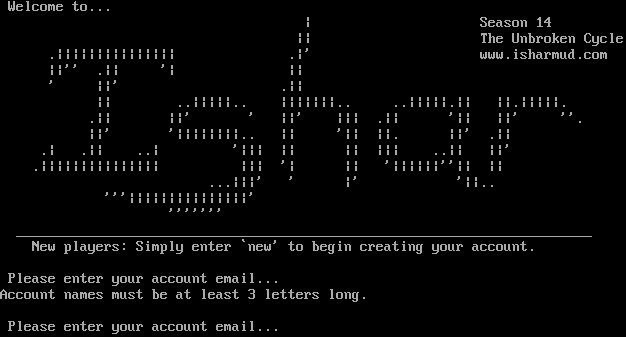
Server URLs
- Telnet: telnet://isharmud.com
- Play in Browser: LociTerm
- Website: www.isharmud.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: BINARY, EOR, GMCP, SGA
Options requested from client: BINARY, LINEMODE, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "d9ddecf161738886",
"fingerprint-data": {
"offered-options": [
"BINARY",
"EOR",
"GMCP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"CHARSET",
"COM_PORT",
"ECHO",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY",
"LINEMODE",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Account names must be at least 3 letters long.\r\n\r\n Please enter your account email... ",
"banner_before_return": "\u001b[H\u001b[J Welcome to...\r\n | Season 14\r\n || The Unbroken Cycle\r\n .||||||||||||||| .|' www.isharmud.com\r\n ||'' .|| '| ||\r\n ' ||' .||\r\n || ..|||||.. |||||||.. ..|||||.|| ||.|||||.\r\n .|| ||' ' ||' ||| .|| '|| ||' ''.\r\n ||' '||||||||.. || '|| ||. ||' .||\r\n .| .|| ..| '||| || || ||| ..|| ||'\r\n .||||||||||||||| ||| '| || '||||||''|| ||\r\n ...|||' ' |' '||..\r\n '''|||||||||||||||'\r\n '''''''\r\n ________________________________________________________________________\r\n New players: Simply enter `new' to begin creating your account.\r\n\r\n Please enter your account email... ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"ECHO": false,
"EOR": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"LINEMODE": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.2027144432067871,
"total": 10.92870545387268
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:06.417233+00:00",
"host": "isharmud.com",
"ip": "52.14.83.8",
"port": 23
},
{
"connected": "2026-04-07T06:44:10.184633+00:00",
"host": "isharmud.com",
"ip": "52.14.83.8",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug isharmud.com 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=isharmud.com port=23
INFO client_base.py:190 Connected to <Peer 52.14.83.8 23>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL EOR
DEBUG stream_writer.py:789 WILL EOR unsolicited
DEBUG stream_writer.py:2045 handle_will(EOR)
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 remote_option[EOR] = True
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:773 recv IAC DO BINARY
DEBUG stream_writer.py:1887 handle_do(BINARY)
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = True
DEBUG stream_writer.py:1024 send IAC WILL BINARY
DEBUG stream_writer.py:3384 local_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB GMCP
DEBUG stream_writer.py:754 sub-negotiation cmd GMCP SE completion byte
DEBUG stream_writer.py:2238 [SB + GMCP] unsolicited
DEBUG client.py:210 GMCP: Core.Hello {'client': 'IsharMud', 'version': '11.1.1'}
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, SB LINEMODE'
DEBUG stream_writer.py:1470 IAC EOR: End of Record (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WILL BINARY
DEBUG stream_writer.py:2045 handle_will(BINARY)
DEBUG stream_writer.py:998 skip DO BINARY; pending_option = True
DEBUG stream_writer.py:3384 remote_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint d9ddecf161738886
INFO client_base.py:122 Connection closed to <Peer 52.14.83.8 23>