jorm.kurowski.xyz
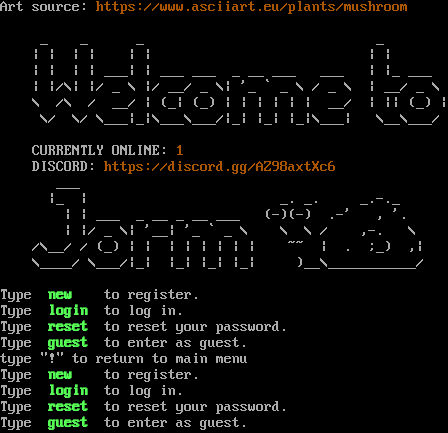
Connection Banner:
Server URLs
- Telnet: telnet://jorm.kurowski.xyz:4001
- Play in Browser: LociTerm
- Website: https://www.asciiart.eu/plants/mushroom
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Negotiated
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options offered by server: GMCP, MSSP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f9092aef0ae576de",
"fingerprint-data": {
"offered-options": [
"GMCP",
"MSSP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "type \"!\" to return to main menu\nType \u001b[1;32m new \u001b[0m to register.\nType \u001b[1;32m login \u001b[0m to log in.\nType \u001b[1;32m reset \u001b[0m to reset your password.\nType \u001b[1;32m guest \u001b[0m to enter as guest.\n",
"banner_before_return": "\u001b[0mArt source: \u001b[0;33mhttps://www.asciiart.eu/plants/mushroom\n\u001b[0m\n _ _ _ _ \n | | | | | | | | \n | | | | ___| | ___ ___ _ __ ___ ___ | |_ ___ \n | |/\\| |/ _ \\ |/ __/ _ \\| '_ ` _ \\ / _ \\ | __/ _ \\ \n \\ /\\ / __/ | (_| (_) | | | | | | __/ | || (_) | \n \\/ \\/ \\___|_|\\___\\___/|_| |_| |_|\\___| \\__\\___/ \n \n CURRENTLY ONLINE: \u001b[0;33m1\u001b[0m \n DISCORD: \u001b[0;33mhttps://discord.gg/AZ98axtXc6\u001b[0m \n ___ \n |_ | _. _. _.-._ \n | | ___ _ __ _ __ ___ (-)(-) .-' , '. \n | |/ _ \\| '__| '_ ` _ \\ \\ \\ / ,-. \\ \n /\\__/ / (_) | | | | | | | | ~~ | . ;_) ,| \n \\____/ \\___/|_| |_| |_| |_| )__\\___________/ \n\u001b[0m\nType \u001b[1;32m new \u001b[0m to register.\nType \u001b[1;32m login \u001b[0m to log in.\nType \u001b[1;32m reset \u001b[0m to reset your password.\nType \u001b[1;32m guest \u001b[0m to enter as guest.\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"GMCP": true,
"MSSP": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5050814151763916,
"total": 11.184318780899048
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:20.232479+00:00",
"host": "jorm.kurowski.xyz",
"ip": "139.162.165.60",
"port": 4001
},
{
"connected": "2026-04-07T07:19:47.194678+00:00",
"host": "jorm.kurowski.xyz",
"ip": "139.162.165.60",
"port": 4001
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug jorm.kurowski.xyz 4001
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=jorm.kurowski.xyz port=4001
INFO client_base.py:190 Connected to <Peer 139.162.165.60 4001>
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, WILL AARDWOLF, WILL MSDP, WILL MSSP, WILL MXP, WILL ZMP, WILL ATCP, WILL
MCCP2_COMPRESS, WILL MSP, WILL MCCP3_COMPRESS, DO AARDWOLF, DO MSDP, DO MXP, DO ZMP, DO ATCP, DO MCCP2_COMPRESS, DO MSP, DO
MCCP3_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint f9092aef0ae576de
INFO client_base.py:122 Connection closed to <Peer 139.162.165.60 4001>