Megaman MUSH
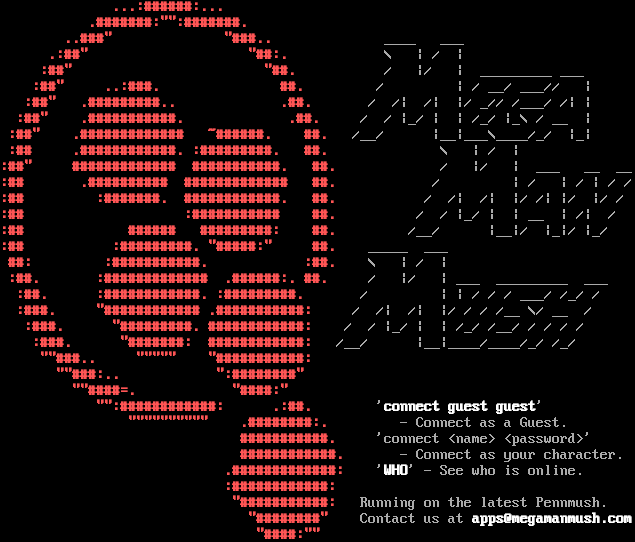
Connection Banner:
Server URLs
- Telnet: telnet://megamanmush.com:1997
- Website: megamanmush.com
Server Info
Codebase: PennMUSH 1.8.8p0
Players online: 11 [1]
Uptime: 16 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " \u001b[1;31m...:######:...\u001b[0m \r\n \u001b[1;31m.#######:\"\":#######.\u001b[0m \r\n \u001b[1;31m..###\" \"###..\u001b[0m ____ ___ \r\n \u001b[1;31m.:##\" \"##:.\u001b[0m \\ | / | \r\n \u001b[1;31m:##\" \"##.\u001b[0m / |/ | _________ ___ \r\n \u001b[1;31m:##\" ..:###. ##.\u001b[0m / | / __/ ___// | \r\n \u001b[1;31m:##\" .#########.. .##.\u001b[0m / /| /| |/ _// /___/ /| | \r\n \u001b[1;31m:##\" .###########. .##.\u001b[0m / / |_/ | | /_/ |_\\ / __ | \r\n \u001b[1;31m:##\" .############# ~######. ##.\u001b[0m /__/ |__|___\\____/_/ |_| \r\n \u001b[1;31m:## .############. :#########. ##.\u001b[0m \\ | / | \r\n\u001b[1;31m:##\" ############# ###########. ##.\u001b[0m / |/ | ___ __ __\r\n\u001b[1;31m:## .########## ############# ##.\u001b[0m / | / | / | / /\r\n\u001b[1;31m:## :#######. ############. ##.\u001b[0m / /| /| |/ /| |/ |/ / \r\n\u001b[1;31m:## :########### ##.\u001b[0m / / |_/ | | __ | /| / \r\n\u001b[1;31m:## ###### #########: ##.\u001b[0m /__/ |__|/ |_|/ |_/ \r\n\u001b[1;31m:## :#########. \"#####:\" ##.\u001b[0m _____ ___ \r\n \u001b[1;31m##: :###########. :##.\u001b[0m \\ | / | \r\n \u001b[1;31m:##. :############# .######:. ##.\u001b[0m / |/ | ___ _________ ___ \r\n \u001b[1;31m:##. :############. :#########.\u001b[0m / | | / / / ___/ /_/ / \r\n \u001b[1;31m:###. \"############ .###########:\u001b[0m / /| /| |/ / / /__ \\/ __ / \r\n \u001b[1;31m:###. \"#########. ############:\u001b[0m / / |_/ | | /_/ /__/ / / / / \r\n \u001b[1;31m:###. \"#######: ############:\u001b[0m /__/ |__|____/____/_/ /_/ \r\n \u001b[1;31m\"\"###.. \"\"\"\"\" \"###########:\u001b[0m \r\n \u001b[1;31m\"\"###:.. \":########\"\u001b[0m \r\n \u001b[1;31m\"\"####=. \"####:\"\u001b[0m \r\n \u001b[1;31m\"\":############: .:##.\u001b[0m '\u001b[1;37mconnect guest guest\u001b[0m' \r\n \u001b[1;31m\"\"\"\"\"\"\"\"\"\" .########:.\u001b[0m - Connect as a Guest. \r\n \u001b[1;31m###########.\u001b[0m 'connect <name> <password>' \r\n \u001b[1;31m############.\u001b[0m - Connect as your character. \r\n \u001b[1;31m.#############:\u001b[0m '\u001b[1;37mWHO\u001b[0m' - See who is online. \r\n \u001b[1;31m:############:\u001b[0m \r\n \u001b[1;31m\"###########:\u001b[0m Running on the latest Pennmush. \r\n \u001b[1;31m\"########\"\u001b[0m Contact us at \u001b[1;37mapps@megamanmush.com\u001b[0m\r\n \u001b[1;31m\"####:\"\"\u001b[0m \r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": [
"1",
"1"
],
"CODEBASE": "PennMUSH 1.8.8p0",
"FAMILY": "TinyMUD",
"NAME": "Megaman MUSH",
"PLAYERS": "11",
"PORT": "1997",
"PUEBLO": "1",
"UPTIME": "1771444066",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.25620555877685547,
"total": 10.765533208847046
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:56.769897+00:00",
"host": "megamanmush.com",
"ip": "50.56.187.128",
"port": 1997
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug megamanmush.com 1997
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=megamanmush.com port=1997
ERROR client.py:1318 megamanmush.com:1997: TCP connection to megamanmush.com:1997 timed out after 30.0s