muck.sprmuck.org
Connection Banner:
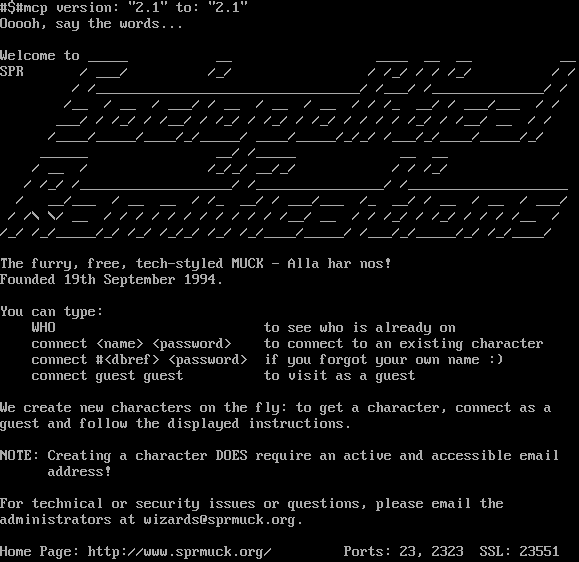
Server URLs
- Telnet: telnet://muck.sprmuck.org
- Website: sprmuck.org
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "#$#mcp version: \"2.1\" to: \"2.1\"\r\nOoooh, say the words... \r\n\r\nWelcome to _____ __ ____ __ __ __\r\nSPR / ___/ /_/ / /_/ / / /_/ / /\r\n / /_________________________________/ /___/ /______________/ /\r\n /__ / __ / ___/ / __ / __ / __ / / /_ __/ / ___/___ / /\r\n ___/ / /_/ / /__/ / /_/ / /_/ / /_/ / / / / /_/ / /__/ __ / /\r\n /____/_____/____/_/_____/ ____/_____/_/_/ /___/_/____/_____/_/\r\n ______ __/ /_____ __ __\r\n / __ / /_/_/ __/_/ / / /_/\r\n / /_/ /___________________/ /________________/ /____________________\r\n / __/___ / __ __ / /_ __/ / ___/___ /_ __/ / __ / __ / ___/\r\n / /\\ \\/ __ / / / / / / / / / / / /__/ __ / / /_/ / /_/ / / / /__ /\r\n/_/ /_/_____/_/ /_/ /_/_/ /_/ /_/____/_____/ /___/_/_____/_/ /_/____/\r\n\r\nThe furry, free, tech-styled MUCK - Alla har nos!\r\nFounded 19th September 1994.\r\n\r\nYou can type:\r\n WHO to see who is already on\r\n connect <name> <password> to connect to an existing character\r\n connect #<dbref> <password> if you forgot your own name :)\r\n connect guest guest to visit as a guest \r\n\r\nWe create new characters on the fly: to get a character, connect as a\r\nguest and follow the displayed instructions.\r\n\r\nNOTE: Creating a character DOES require an active and accessible email\r\n address! \r\n\r\nFor technical or security issues or questions, please email the\r\nadministrators at wizards@sprmuck.org.\r\n\r\nHome Page: http://www.sprmuck.org/ Ports: 23, 2323 SSL: 23551\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5049083232879639,
"total": 11.015814542770386
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:00.759442+00:00",
"host": "muck.sprmuck.org",
"ip": "173.255.235.187",
"port": 23
},
{
"connected": "2026-04-07T07:19:38.597827+00:00",
"host": "muck.sprmuck.org",
"ip": "173.255.235.187",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug muck.sprmuck.org 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=muck.sprmuck.org port=23
INFO client_base.py:190 Connected to <Peer 173.255.235.187 23>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG client_base.py:531 negotiation complete after 0.14s.
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT b'\xfc'
DEBUG stream_writer.py:2199 handle_wont(WONT)
DEBUG stream_writer.py:3384 remote_option[WONT] = False
DEBUG stream_writer.py:3384 pending_option[DO + WONT] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 173.255.235.187 23>