风云再现2025
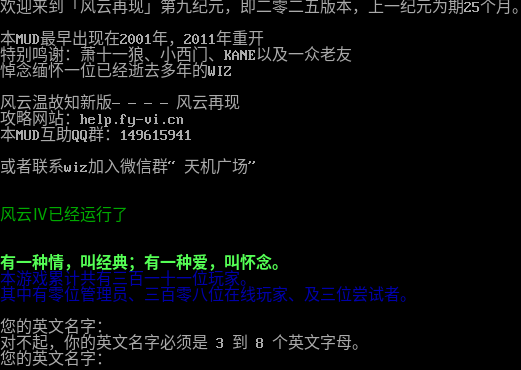
Connection Banner:
Server URLs
- Telnet: telnet://mud.fy-vi.cn:6666
- Website: help.fy-vi.cn
Server Info
Players online: 311 [1]
Uptime: 51 days
Server Location: 🇨🇳 China (GeoIP)
Encoding: gbk
This server uses a legacy encoding:
telnetlib3-client --encoding gbk --force-binary mud.fy-vi.cn 6666
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: Negotiated
MSP: No
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 14 other servers.
Options offered by server: ECHO, GMCP, MCCP2, MSSP, SGA, ZMP
Options requested from client: GMCP, LINEMODE, MCCP2, MSSP, MXP, NAWS, NEW_ENVIRON, SGA, TTYPE, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "b853cfd2acfc218d",
"fingerprint-data": {
"offered-options": [
"ECHO",
"GMCP",
"MCCP2",
"MSSP",
"SGA",
"ZMP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS"
],
"requested-options": [
"GMCP",
"LINEMODE",
"MCCP2",
"MSSP",
"MXP",
"NAWS",
"NEW_ENVIRON",
"SGA",
"TTYPE",
"ZMP"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u5bf9\u4e0d\u8d77\uff0c\u4f60\u7684\u82f1\u6587\u540d\u5b57\u5fc5\u987b\u662f 3 \u5230 8 \u4e2a\u82f1\u6587\u5b57\u6bcd\u3002\r\n\u60a8\u7684\u82f1\u6587\u540d\u5b57\uff1a\r\n",
"banner_before_return": "\u6b22\u8fce\u6765\u5230\u300c\u98ce\u4e91\u518d\u73b0\u300d\u7b2c\u4e5d\u7eaa\u5143\uff0c\u5373\u4e8c\u96f6\u4e8c\u4e94\u7248\u672c\uff0c\u4e0a\u4e00\u7eaa\u5143\u4e3a\u671f25\u4e2a\u6708\u3002\r\n\r\n\u672cMUD\u6700\u65e9\u51fa\u73b0\u57282001\u5e74\uff0c2011\u5e74\u91cd\u5f00\r\n\u7279\u522b\u9e23\u8c22\uff1a\u8427\u5341\u4e00\u72fc\u3001\u5c0f\u897f\u95e8\u3001KANE\u4ee5\u53ca\u4e00\u4f17\u8001\u53cb\r\n\u60bc\u5ff5\u7f05\u6000\u4e00\u4f4d\u5df2\u7ecf\u901d\u53bb\u591a\u5e74\u7684WIZ\r\n\r\n\u98ce\u4e91\u6e29\u6545\u77e5\u65b0\u7248\u2014\u2014\u2014\u2014\u98ce\u4e91\u518d\u73b0\r\n\u653b\u7565\u7f51\u7ad9\uff1ahelp.fy-vi.cn\r\n\u672cMUD\u4e92\u52a9QQ\u7fa4\uff1a149615941\r\n\r\n\u6216\u8005\u8054\u7cfbwiz\u52a0\u5165\u5fae\u4fe1\u7fa4\u201c\u5929\u673a\u5e7f\u573a\u201d\r\n\r\n\r\n\u001b[32m\u98ce\u4e91\u2163\u5df2\u7ecf\u8fd0\u884c\u4e86\u001b[5m\u001b[1;33m\u4e94\u5341\u4e00\u5929\u4e94\u5c0f\u65f6\u5341\u516d\u5206\u5341\u4e8c\u79d2\u3002\r\n\r\n\u001b[2;37;0m\u001b[1;32m\r\n\u6709\u4e00\u79cd\u60c5\uff0c\u53eb\u7ecf\u5178\uff1b\u6709\u4e00\u79cd\u7231\uff0c\u53eb\u6000\u5ff5\u3002\r\n\u001b[2;37;0m\u001b[34m\u672c\u6e38\u620f\u7d2f\u8ba1\u5171\u6709\u4e09\u767e\u4e00\u5341\u4e00\u4f4d\u73a9\u5bb6\u3002\r\n\u5176\u4e2d\u6709\u96f6\u4f4d\u7ba1\u7406\u5458\u3001\u4e09\u767e\u96f6\u516b\u4f4d\u5728\u7ebf\u73a9\u5bb6\u3001\u53ca\u4e09\u4f4d\u5c1d\u8bd5\u8005\u3002\r\n\r\n\u001b[2;37;0m\u60a8\u7684\u82f1\u6587\u540d\u5b57\uff1a\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "gbk",
"mssp": {
"NAME": "\u98ce\u4e91\u518d\u73b02025",
"PLAYERS": "311",
"UPTIME": "1771119474"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"LINEMODE": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": true,
"NAWS": true,
"NEW_ENVIRON": true,
"SGA": true,
"TTYPE": true,
"ZMP": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.25209712982177734,
"total": 11.057539463043213
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:01:05.012951+00:00",
"host": "mud.fy-vi.cn",
"ip": "112.124.15.134",
"port": 6666
},
{
"connected": "2026-04-07T06:54:18.134879+00:00",
"host": "mud.fy-vi.cn",
"ip": "112.124.15.134",
"port": 6666
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.fy-vi.cn 6666
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.fy-vi.cn port=6666
INFO client_base.py:190 Connected to <Peer 112.124.15.134 6666>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x03' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x07': lit_echo:False, soft_tab:False, ack:True, trapsig:True, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x07': lit_echo:False, soft_tab:False, ack:True, trapsig:True,
remote:False, local:True> IAC SE
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO ZMP
DEBUG stream_writer.py:1887 handle_do(ZMP)
DEBUG stream_writer.py:998 skip WILL ZMP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': '风云再现2025', 'PLAYERS': '311', 'UPTIME': '1771119474'}
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG client_base.py:531 negotiation complete after 0.67s.
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint b853cfd2acfc218d
INFO client_base.py:122 Connection closed to <Peer 112.124.15.134 6666>