mud.xyllomer.de
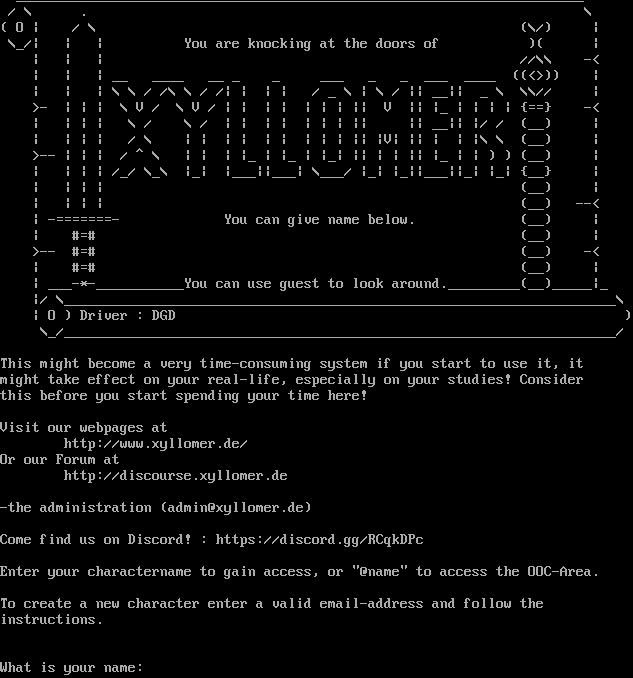
Connection Banner:
Server URLs
- Telnet: telnet://mud.xyllomer.de:3000
- Website: http://www.xyllomer.de/
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " _______________________________________________________________________\n / \\ . \\\n( O | / \\ (\\/) |\n \\_/| | | You are knocking at the doors of )( |\n | | | //\\\\ -<\n | | | __ ____ __ _ _ ___ _ _ ___ ____ ((<>)) |\n | | | \\ \\ / /\\ \\ / /| | | | / _ \\ | \\ / || __|| _ \\ \\\\// |\n >- | | | \\ V / \\ V / | | | | | | | || V || |_ | | | | {==} -<\n | | | | \\ / \\ / | | | | | | | || || __|| |/ / (__) |\n | | | | / \\ | | | | | | | | | || |V| || | | |\\ \\ (__) |\n >-- | | | / ^ \\ | | | |_ | |_ | |_| || | | || |_ | | ) ) (__) |\n | | | | /_/ \\_\\ |_| |___||___| \\___/ |_| |_||___||_| |_| {__} |\n | | | | (__) |\n | | | | (__) --<\n | -=======- You can give name below. (__) |\n | #=# (__) |\n >-- #=# (__) -<\n | #=# (__) |\n | ___-*-___________You can use guest to look around._________(__)_____|_\n |/ \\_____________________________________________________________________\\\n | O ) Driver : DGD )\n \\_/_____________________________________________________________________/\n\nThis might become a very time-consuming system if you start to use it, it \nmight take effect on your real-life, especially on your studies! Consider\nthis before you start spending your time here!\n\nVisit our webpages at \n http://www.xyllomer.de/\nOr our Forum at\n http://discourse.xyllomer.de\n \n-the administration (admin@xyllomer.de)\n\nCome find us on Discord! : https://discord.gg/RCqkDPc\n\nEnter your charactername to gain access, or \"@name\" to access the OOC-Area.\n\nTo create a new character enter a valid email-address and follow the \ninstructions.\n\n\nWhat is your name: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"GMCP": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.646787405014038
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:03.704326+00:00",
"host": "mud.xyllomer.de",
"ip": "51.15.58.92",
"port": 3000
},
{
"connected": "2026-04-07T07:01:47.124594+00:00",
"host": "mud.xyllomer.de",
"ip": "51.15.58.92",
"port": 3000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.xyllomer.de 3000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.xyllomer.de port=3000
INFO client_base.py:190 Connected to <Peer 51.15.58.92 3000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL MSDP, WILL MCCP2_COMPRESS, WILL MXP, WILL MCCP3_COMPRESS, WILL ZMP, WILL
ATCP, WILL GMCP, WILL MSP, WILL AARDWOLF, DO MSSP, DO MSDP, DO MCCP2_COMPRESS, DO MXP, DO MCCP3_COMPRESS, DO ZMP, DO ATCP, DO
MSP, DO AARDWOLF'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 51.15.58.92 3000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41