nomoreheroes.org
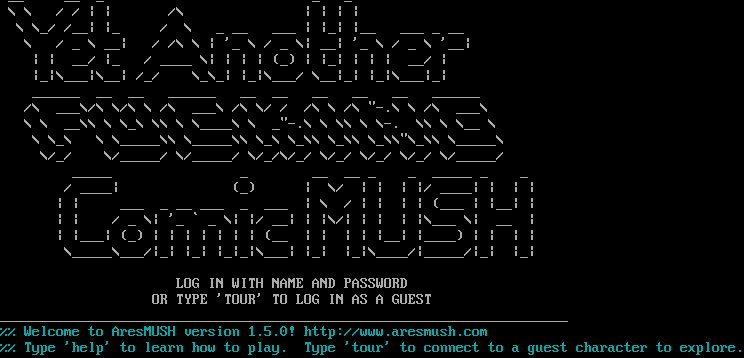
Connection Banner:
Server URLs
- Telnet: telnet://nomoreheroes.org:4201
- Website: http://www.aresmush.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 13 other servers.
Options requested from client: CHARSET, NAWS
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "ba94558ba15cc5eb",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"NAWS"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " __ __ _ _ _ \n \\ \\ / / | | /\\ | | | | \n \\ \\_/ /__| |_ / \\ _ __ ___ | |_| |__ ___ _ __ \n \\ / _ \\ __| / /\\ \\ | '_ \\ / _ \\| __| '_ \\ / _ \\ '__| \n | | __/ |_ / ____ \\| | | | (_) | |_| | | | __/ | \n |_|\\___|\\__| /_/ \\_\\_| |_|\\___/ \\__|_| |_|\\___|_| \n ______ __ __ ______ __ __ __ __ __ ______ \n /\\ ___\\/\\ \\/\\ \\ /\\ ___\\ /\\ \\/ / /\\ \\ /\\ \"-.\\ \\ /\\ ___\\ \n \\ \\ __\\\\ \\ \\_\\ \\\\ \\ \\____\\ \\ _\"-.\\ \\ \\\\ \\ \\-. \\\\ \\ \\__ \\ \n \\ \\_\\ \\ \\_____\\\\ \\_____\\\\ \\_\\ \\_\\\\ \\_\\\\ \\_\\\\\"\\_\\\\ \\_____\\ \n \\/_/ \\/_____/ \\/_____/ \\/_/\\/_/ \\/_/ \\/_/ \\/_/ \\/_____/\n _____ _ __ __ _ _ _____ _ _ \n / ____| (_) | \\/ | | | |/ ____| | | |\n | | ___ _ __ ___ _ ___ | \\ / | | | | (___ | |__| |\n | | / _ \\| '_ ` _ \\| |/ __| | |\\/| | | | |\\___ \\| __ |\n | |___| (_) | | | | | | | (__ | | | | |__| |____) | | | |\n \\_____\\___/|_| |_| |_|_|\\___| |_| |_|\\____/|_____/|_| |_|\n\n LOG IN WITH NAME AND PASSWORD \n OR TYPE 'TOUR' TO LOG IN AS A GUEST\n_______________________________________________________________________\u001b[0m\r\n\u001b[36m%% Welcome to AresMUSH version 1.5.0! http://www.aresmush.com\n%% Type 'help' to learn how to play. Type 'tour' to connect to a guest character to explore.\u001b[0m\u001b[0m\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"option_states": {
"server_offered": {},
"server_requested": {
"CHARSET": true,
"NAWS": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5043158531188965,
"total": 11.014559745788574
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:46.343191+00:00",
"host": "nomoreheroes.org",
"ip": "165.227.192.95",
"port": 4201
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug nomoreheroes.org 4201
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=nomoreheroes.org port=4201
ERROR client.py:1318 nomoreheroes.org:4201: [Errno 111] Connect call failed ('165.227.192.95', 4201)