Pax Republica: A Star Wars MUSH
Connection Banner:
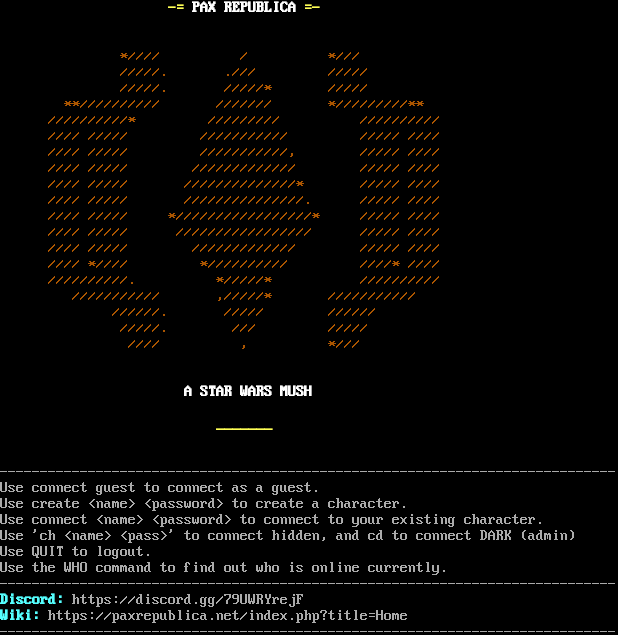
Server URLs
- Telnet: telnet://paxrepublica.net:9999
- Play in Browser: LociTerm
- Website: https://discord.gg/79UWRYrejF
Server Info
Codebase: PennMUSH 1.8.8p0
Players online: 2 [1]
Uptime: 155 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\n\r\n \u001b[33;1m-=\u001b[0m \u001b[1;37mPAX REPUBLICA\u001b[0m \u001b[33;1m=-\u001b[0m\r\n\r\n\r\n \u001b[33m*//// / */// \r\n /////. ./// ///// \r\n /////. /////* ///// \r\n **////////// /////// */////////** \r\n //////////* ///////// ////////// \r\n //// ///// /////////// ///// //// \r\n //// ///// ///////////, ///// //// \r\n //// ///// ///////////// ///// //// \r\n //// ///// //////////////* ///// //// \r\n //// ///// ///////////////. ///// //// \r\n //// ///// */////////////////* ///// //// \r\n //// ///// ///////////////// ///// //// \r\n //// ///// ///////////// ///// //// \r\n //// *//// *////////// ////* //// \r\n //////////. */////* ////////// \r\n /////////// ,/////* /////////// \r\n //////. ///// ////// \r\n /////. /// ///// \r\n //// , *///\u001b[0m \r\n\r\n\r\n \u001b[1;37mA STAR WARS MUSH\u001b[0m\r\n\r\n \u001b[33;1m_______\u001b[0m\r\n\r\n\r\n-----------------------------------------------------------------------------\r\nUse connect guest to connect as a guest.\r\nUse create <name> <password> to create a character.\r\nUse connect <name> <password> to connect to your existing character.\r\nUse 'ch <name> <pass>' to connect hidden, and cd to connect DARK (admin)\r\nUse QUIT to logout.\r\nUse the WHO command to find out who is online currently.\r\n-----------------------------------------------------------------------------\r\n\u001b[36;1mDiscord:\u001b[0m https://discord.gg/79UWRYrejF\r\n\u001b[36;1mWiki:\u001b[0m https://paxrepublica.net/index.php?title=Home\r\n-----------------------------------------------------------------------------\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.8p0",
"FAMILY": "TinyMUD",
"NAME": "Pax Republica: A Star Wars MUSH",
"PLAYERS": "2",
"PORT": "9999",
"PUEBLO": "1",
"SSL": "9998",
"UPTIME": "1762126299",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.1523761749267578,
"total": 10.665528297424316
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:30.049359+00:00",
"host": "paxrepublica.net",
"ip": "74.208.122.190",
"port": 9999
},
{
"connected": "2026-04-07T07:10:36.277930+00:00",
"host": "paxrepublica.net",
"ip": "74.208.122.190",
"port": 9999
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug paxrepublica.net 9999
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=paxrepublica.net port=9999
INFO client_base.py:190 Connected to <Peer 74.208.122.190 9999>
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Pax Republica: A Star Wars MUSH', 'PLAYERS': '2', 'UPTIME': '1762126299', 'PORT':
'9999', 'SSL': '9998', 'PUEBLO': '1', 'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS':
'1'}
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Pax Republica: A Star Wars MUSH', 'PLAYERS': '2', 'UPTIME': '1762126299', 'PORT':
'9999', 'SSL': '9998', 'PUEBLO': '1', 'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS':
'1'}
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint f96aa48abbc42633
INFO client_base.py:122 Connection closed to <Peer 74.208.122.190 9999>