perilousrealms.com
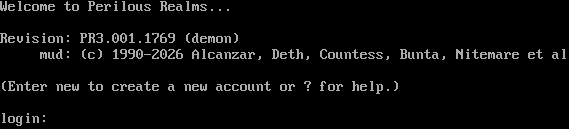
Connection Banner:
Server URLs
- Telnet: telnet://perilousrealms.com
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 6 other servers.
Options requested from client: LINEMODE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "98ef96f171413a1c",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"LINEMODE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\nWelcome to Perilous Realms...\r\n\r\nRevision: PR3.001.1769 (demon)\r\n mud: (c) 1990-2026 Alcanzar, Deth, Countess, Bunta, Nitemare et al\r\n\r\n(Enter new to create a new account or ? for help.)\r\n\r\nlogin: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"LINEMODE": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.654718399047852
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:08.018809+00:00",
"host": "perilousrealms.com",
"ip": "13.57.88.213",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug perilousrealms.com 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=perilousrealms.com port=23
ERROR client.py:1318 perilousrealms.com:23: TCP connection to perilousrealms.com:23 timed out after 30.0s