Battle Fantasia
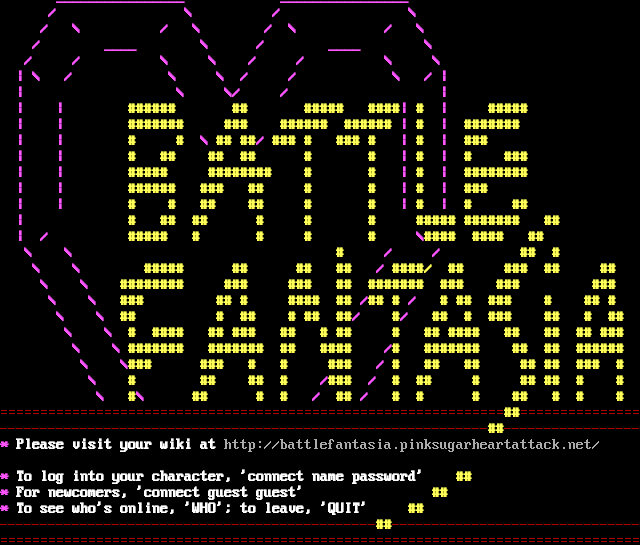
Connection Banner:
Server URLs
Server Info
Codebase: PennMUSH 1.8.5p5
Players online: 5 [1]
Uptime: 32 days
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options offered by server: SGA
Options requested from client: SGA
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "669fa8b4daf4d932",
"fingerprint-data": {
"offered-options": [
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"SGA"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\u001b[1;35m ________________ ________________ \u001b[0m\r\n \u001b[1;35m/ \\ / \\ \u001b[0m\r\n\u001b[1;35m / \\ / \\ / \\ / \\ \u001b[0m\r\n\u001b[1;35m / ____ \\ / ____ \\ \u001b[0m\r\n\u001b[1;35m / / \\ \\ / / \\ \\ \u001b[0m\r\n\u001b[1;35m | \\ / \\ \\ / / \\ / | \u001b[0m\r\n\u001b[1;35m | \\ \\/ / | \u001b[0m\r\n\u001b[1;35m | | \u001b[33m###### ## ##### ####\u001b[35m|\u001b[0m \u001b[1;33m#\u001b[0m \u001b[1;35m|\u001b[0m \u001b[1;33m#####\u001b[0m \r\n\u001b[1;35m | | \u001b[33m####### ### ###### ######\u001b[0m \u001b[1;35m|\u001b[0m \u001b[1;33m#\u001b[0m \u001b[1;35m|\u001b[0m \u001b[1;33m#######\u001b[0m \r\n\u001b[1;35m | | \u001b[33m# # \u001b[35m\\ \u001b[33m## ##\u001b[35m/\u001b[33m ### # ### # \u001b[35m|\u001b[33m # \u001b[35m|\u001b[33m ###\u001b[0m \r\n\u001b[1;35m | | \u001b[33m# ## ## ## # # \u001b[35m | \u001b[33m# \u001b[35m | \u001b[33m# ### \u001b[0m \r\n\u001b[1;35m | | \u001b[33m##### ######## # # \u001b[35m | \u001b[33m# \u001b[35m | \u001b[33m######## \u001b[0m \r\n\u001b[1;35m | | \u001b[33m###### ### ## # # \u001b[35m | \u001b[33m# \u001b[35m | \u001b[33m### \u001b[0m \r\n\u001b[1;35m | | \u001b[33m# # ## ## # # \u001b[35m | \u001b[33m# \u001b[35m | \u001b[33m# ## \u001b[0m \r\n\u001b[1;35m | \u001b[33m# ## ## # # # ##### ####### ##\u001b[0m \r\n\u001b[1;35m | / \u001b[33m##### # # # # \u001b[35m \\\u001b[33m#### #### ## \u001b[0m \r\n\u001b[1;35m \\ \\ \u001b[33m# \u001b[35m/ /\u001b[33m ## #\u001b[0m \r\n\u001b[1;35m \\ \\ \u001b[33m##### ## ## ##\u001b[35m / \u001b[33m####/ ## ### ## ## \u001b[0m\r\n\u001b[1;35m \\ \\ \u001b[33m######## ### ### ## ####### ### ### ### \u001b[0m\r\n\u001b[1;35m \\ \\ \u001b[33m### ## # #### ##\u001b[35m /\u001b[33m## # \u001b[35m/ \u001b[33m # ## ### # ## # \u001b[0m\r\n\u001b[1;35m \\ \\ \u001b[33m## # ## # ## ##\u001b[35m/\u001b[33m #\u001b[35m/\u001b[33m ## # ### ## # ## \u001b[0m\r\n\u001b[1;35m \\ \\ \u001b[33m# #### ## ### ## # ## # ## #### ## ## ## ###\u001b[0m \r\n\u001b[1;35m \\ \\ \u001b[33m####### ####### ## #### \u001b[35m/\u001b[33m# ####### ## ## ###### \u001b[0m\r\n\u001b[1;35m \\ \\\u001b[33m### ### # # ### \u001b[35m/\u001b[33m # ## ## ## ## ### # \u001b[0m\r\n\u001b[1;35m \\ \u001b[33m# ## ## # \u001b[35m/\u001b[33m### \u001b[35m/\u001b[33m # ## # ## ## # # \u001b[0m\r\n\u001b[1;35m \\ \u001b[33m#\u001b[35m\\ \u001b[33m ## # # \u001b[35m/\u001b[33m ##\u001b[35m /\u001b[33m # # # ## # # # \u001b[0m\r\n\u001b[31m===============================================================\u001b[1;33m##\u001b[0m\u001b[31m===============\u001b[0m\r\n\u001b[31m-------------------------------------------------------------\u001b[1;33m##\u001b[0m\u001b[31m-----------------\u001b[0m\r\n\u001b[1;35m*\u001b[0m \u001b[1;37mPlease visit your wiki at \u001b[0mhttp://battlefantasia.pinksugarheartattack.net/ \r\n\u001b[1;35m*\u001b[0m \u001b[1;37mTo log into your character, 'connect name password' \u001b[0m \u001b[1;33m##\u001b[0m \r\n\u001b[1;35m*\u001b[0m \u001b[1;37mFor newcomers, 'connect guest guest' \u001b[0m \u001b[1;33m## \u001b[0m \r\n\u001b[1;35m*\u001b[0m \u001b[1;37mTo see who's online, 'WHO'; to leave, 'QUIT' \u001b[33m## \u001b[0m \r\n\u001b[31m-----------------------------------------------\u001b[1;33m##\u001b[0m\u001b[31m-------------------------------\u001b[0m\r\n\u001b[31m================================================================================\u001b[0m\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ANSI_X3.4-1968",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.5p5",
"FAMILY": "TinyMUD",
"NAME": "Battle Fantasia",
"PLAYERS": "5",
"PORT": "2873",
"PUEBLO": "0",
"UPTIME": "1772764954"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5052413940429688,
"total": 11.017976999282837
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:05.484133+00:00",
"host": "pinksugarheartattack.net",
"ip": "167.172.15.81",
"port": 2873
},
{
"connected": "2026-04-07T06:48:18.027482+00:00",
"host": "pinksugarheartattack.net",
"ip": "167.172.15.81",
"port": 2873
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug pinksugarheartattack.net 2873
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=pinksugarheartattack.net port=2873
INFO client_base.py:190 Connected to <Peer 167.172.15.81 2873>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Battle Fantasia', 'PLAYERS': '5', 'UPTIME': '1772764954', 'PORT': '2873', 'PUEBLO':
'0', 'CODEBASE': 'PennMUSH 1.8.5p5', 'FAMILY': 'TinyMUD', 'ANSI': '1'}
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'DO MSSP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: ANSI_X3.4-1968
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED ANSI_X3.4-1968 IAC SE
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 669fa8b4daf4d932
INFO client_base.py:122 Connection closed to <Peer 167.172.15.81 2873>