rplay.net
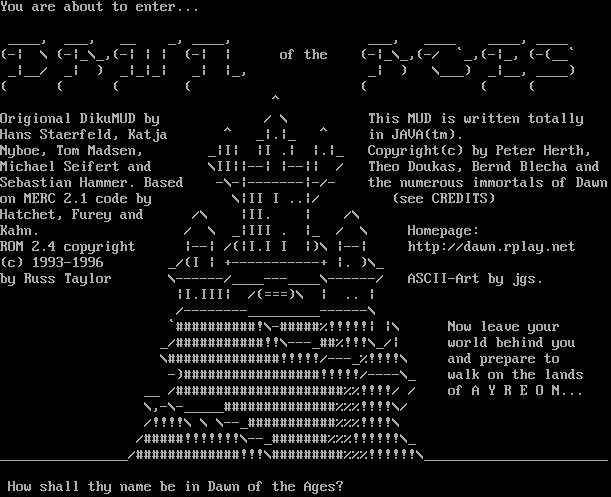
Connection Banner:
Server URLs
- Telnet: telnet://rplay.net:8000
- Website: http://dawn.rplay.net
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": " How shall thy name be in Dawn of the Ages? ",
"banner_before_return": "\n\rYou are about to enter... \n\n ____, ___, __ _, ____, ___, ____ ____, ____ \n(-| \\ (-|_\\_,(-| | | (-| | of the (-|_\\_,(-/ `_,(-|_, (-(__`\n _|__/ _| ) _|_|_| _| |_, _| ) \\___) _|__, ____)\n( ( ( ( ( ( (\n ^\nOrigional DikuMUD by / \\ This MUD is written totally\nHans Staerfeld, Katja ^ _|.|_ ^ in JAVA(tm). \nNyboe, Tom Madsen, _|I| |I .| |.|_ Copyright(c) by Peter Herth,\nMichael Seifert and \\II||--| |--|| / Theo Doukas, Bernd Blecha and\nSebastian Hammer. Based -\\-|-------|-/- the numerous immortals of Dawn\non MERC 2.1 code by \\|II I ..|/ (see CREDITS)\nHatchet, Furey and /\\ |II. | /\\ \nKahn. / \\ _|III . |_ / \\ Homepage:\nROM 2.4 copyright |--| /(|I.I I |)\\ |--| http://dawn.rplay.net\n(c) 1993-1996 _/(I | +-----------+ |. )\\_ \nby Russ Taylor \\------/____---____\\------/ ASCII-Art by jgs.\n |I.III| /(===)\\ | .. |\n /--------_________------\\\n `##########!\\-#####%!!!!!| |\\ Now leave your\n _/###########!!\\---_##%!!!\\_/| world behind you\n \\##############!!!!!/---_%!!!!\\ and prepare to\n -)#################!!!!!/----\\_ walk on the lands\n __ /#####################%%!!!!/ / of A Y R E O N...\n \\,-\\-_____##############%%%!!!!\\/ \n /!!!!\\ \\ \\--_###########%%%!!!!\\ \n /#####!!!!!!!\\--_#######%%%!!!!!!\\_ \n________________/#############!!!\\#########%%%!!!!!!\\_______________________\n\r\n How shall thy name be in Dawn of the Ages? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5044772624969482,
"total": 11.243230104446411
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:59:09.798951+00:00",
"host": "rplay.net",
"ip": "212.132.110.231",
"port": 8000
},
{
"connected": "2026-04-07T07:01:27.624143+00:00",
"host": "rplay.net",
"ip": "212.132.110.231",
"port": 8000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug rplay.net 8000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=rplay.net port=8000
INFO client_base.py:190 Connected to <Peer 212.132.110.231 8000>
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL ATCP, WILL MSP, WILL MSDP, WILL MSSP, WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL GMCP,
WILL MCCP3_COMPRESS, WILL ZMP, WILL MXP, DO ATCP, DO MSP, DO MSDP, DO MSSP, DO AARDWOLF, DO MCCP2_COMPRESS, DO GMCP, DO
MCCP3_COMPRESS, DO ZMP, DO MXP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 212.132.110.231 8000>