trollattack.com
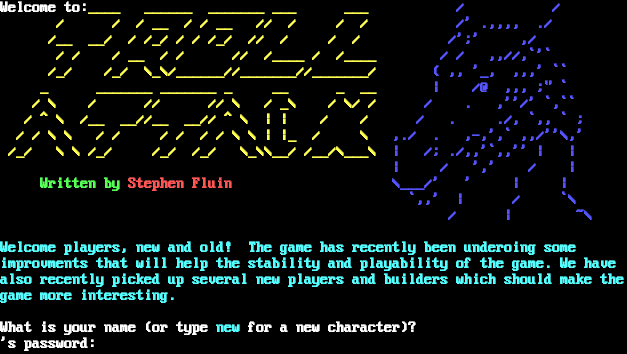
Connection Banner:
Server URLs
- Telnet: telnet://trollattack.com:4000
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "a8a260cc4662430c",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "'s password:\n\r",
"banner_before_return": "\u001b[1;37mWelcome to:\u001b[1;33m____ ______ _______ ___ ___ \u001b[1;34m / / \n\r\u001b[1;33m / / / __ / / __ // / / / \u001b[1;34m /' .,,,, ./ \n\r\u001b[1;33m /__ __/ / /_/ / / /_/ // / / / \u001b[1;34m /';' ,/ \n\r\u001b[1;33m / / / __ / / // /____ / /____ \u001b[1;34m / / ,,//,`'` \n\r\u001b[1;33m /_/ /_/ \\_\\/______//_______//_______/ \u001b[1;34m ( ,, '_, ,,,' `` \n\r\u001b[1;33m _ _______ _______ _ __ _ __ \u001b[1;34m | /@ ,,, ;\" ` \n\r\u001b[1;33m / \\ / // // \\ / _\\ / \\/ / \u001b[1;34m / . ,''/' `,`` \n\r\u001b[1;33m / ^ \\ /__ __//__ __// ^ \\ | | / / \u001b[1;34m / . ./, `,, ` ; \n\r\u001b[1;33m / / \\ \\ / / / / / / \\ \\ | |_ / \\ \u001b[1;34m,./ . ,-,',` ,,/''\\,' \n\r\u001b[1;33m /_/ \\ \\ /_/ /_/ /_/ \\_\\\\__/ /__/\\___\\ \u001b[1;34m| /; ./,,'`,,'' | | \n\r\u001b[1;33m \u001b[1;34m| / ',' / | \n\r\u001b[1;32m Written by \u001b[1;31mStephen Fluin\u001b[1;33m \u001b[1;34m\\___/' ' | | \n\r\u001b[1;33m \u001b[1;34m `,,' | / `\\ \n\r\u001b[1;33m \u001b[1;34m / | ~\\ \n\r\n\r\u001b[1;36mWelcome players, new and old! The game has recently been underoing some \n\rimprovments that will help the stability and playability of the game. We have\n\ralso recently picked up several new players and builders which should make the\n\rgame more interesting.\n\r\n\r\u001b[1;37mWhat is your name (or type \u001b[1;36mnew\u001b[1;37m for a new character)?\n\r",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5165135860443115,
"total": 5.257735013961792
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:09:44.783440+00:00",
"host": "trollattack.com",
"ip": "34.106.100.140",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug trollattack.com 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=trollattack.com port=4000
ERROR client.py:1318 trollattack.com:4000: TCP connection to trollattack.com:4000 timed out after 30.0s