us.muds.net
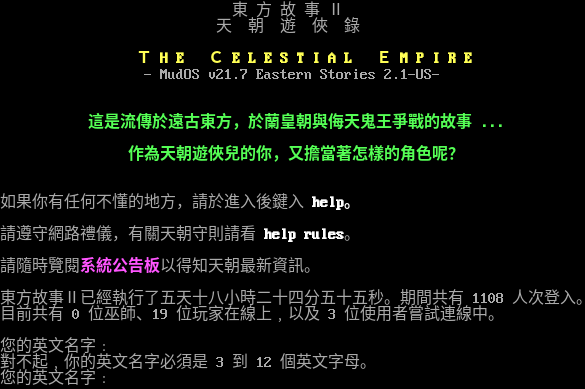
Connection Banner:
Server URLs
- Telnet: telnet://us.muds.net:4000
Server Info
Server Location: 🇸🇬 Singapore (GeoIP)
Encoding: big5
This server uses a legacy encoding:
telnetlib3-client --encoding big5 --force-binary us.muds.net 4000
Telnet Fingerprint
This fingerprint is shared by 23 other servers.
Options requested from client: NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "5fda562c200a52b3",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u5c0d\u4e0d\u8d77\ufe50\u4f60\u7684\u82f1\u6587\u540d\u5b57\u5fc5\u9808\u662f 3 \u5230 12 \u500b\u82f1\u6587\u5b57\u6bcd\u3002\r\n\u60a8\u7684\u82f1\u6587\u540d\u5b57\ufe55",
"banner_before_return": "\r\n\r\n \u6771 \u65b9 \u6545 \u4e8b \u2161\r\n \u5929 \u671d \u904a \u4fe0 \u9304\r\n\r\n \u001b[1;33m\uff34 H E \uff23 E L E S T I A L \uff25 M P I R E\u001b[2;37;0m\r\n - MudOS v21.7 Eastern Stories 2.1-US-\r\n\r\n\r\n \u001b[1;32m\u9019\u662f\u6d41\u50b3\u65bc\u9060\u53e4\u6771\u65b9\uff0c\u65bc\u862d\u7687\u671d\u8207\u4fae\u5929\u9b3c\u738b\u722d\u6230\u7684\u6545\u4e8b ...\r\n\r\n \u4f5c\u70ba\u5929\u671d\u904a\u4fe0\u5152\u7684\u4f60\uff0c\u53c8\u64d4\u7576\u8457\u600e\u6a23\u7684\u89d2\u8272\u5462\uff1f\u001b[2;37;0m\r\n\r\n\r\n\u5982\u679c\u4f60\u6709\u4efb\u4f55\u4e0d\u61c2\u7684\u5730\u65b9\uff0c\u8acb\u65bc\u9032\u5165\u5f8c\u9375\u5165 \u001b[1;37mhelp\u3002\u001b[2;37;0m\r\n\r\n\u8acb\u9075\u5b88\u7db2\u8def\u79ae\u5100\uff0c\u6709\u95dc\u5929\u671d\u5b88\u5247\u8acb\u770b \u001b[1;37mhelp rules\u001b[2;37;0m\u3002\r\n\r\n\u8acb\u96a8\u6642\u89bd\u95b1\u001b[1;35m\u7cfb\u7d71\u516c\u544a\u677f\u001b[2;37;0m\u4ee5\u5f97\u77e5\u5929\u671d\u6700\u65b0\u8cc7\u8a0a\u3002\r\n\r\n\u6771\u65b9\u6545\u4e8b\u2161\u5df2\u7d93\u57f7\u884c\u4e86\u4e94\u5929\u5341\u516b\u5c0f\u6642\u4e8c\u5341\u56db\u5206\u4e94\u5341\u4e94\u79d2\u3002\u671f\u9593\u5171\u6709 1108 \u4eba\u6b21\u767b\u5165\u3002\r\n\u76ee\u524d\u5171\u6709 0 \u4f4d\u5deb\u5e2b\u300119 \u4f4d\u73a9\u5bb6\u5728\u7dda\u4e0a\ufe50\u4ee5\u53ca 3 \u4f4d\u4f7f\u7528\u8005\u5617\u8a66\u9023\u7dda\u4e2d\u3002\r\n\r\n\u60a8\u7684\u82f1\u6587\u540d\u5b57\ufe55",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "big5",
"option_states": {
"server_offered": {},
"server_requested": {
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5038065910339355,
"total": 11.182754278182983
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:16.580774+00:00",
"host": "us.muds.net",
"ip": "139.162.24.232",
"port": 4000
},
{
"connected": "2026-04-07T07:16:23.528590+00:00",
"host": "us.muds.net",
"ip": "139.162.24.232",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug us.muds.net 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=us.muds.net port=4000
INFO client_base.py:190 Connected to <Peer 139.162.24.232 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL ZMP, WILL MCCP2_COMPRESS, WILL AARDWOLF, WILL MCCP3_COMPRESS, WILL ATCP, WILL GMCP,
WILL MSDP, WILL MSP, WILL MXP, WILL MSSP, DO ZMP, DO MCCP2_COMPRESS, DO AARDWOLF, DO MCCP3_COMPRESS, DO ATCP, DO GMCP, DO
MSDP, DO MSP, DO MXP, DO MSSP'
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 5fda562c200a52b3
INFO client_base.py:122 Connection closed to <Peer 139.162.24.232 4000>