44.235.126.228
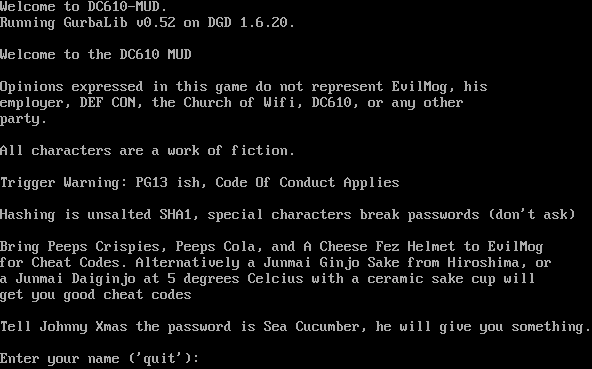
Connection Banner:
Server URLs
- Telnet: telnet://44.235.126.228:4000
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: GMCP, MXP
Options requested from client: LINEMODE, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "0532bfc07a52c110",
"fingerprint-data": {
"offered-options": [
"GMCP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"MSDP",
"MSP",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"LINEMODE",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\r\nPlease enter your name : ",
"banner_before_return": "Welcome to DC610-MUD.\r\nRunning GurbaLib v0.52 on DGD 1.6.20.\r\n\u001b[7z\r\nWelcome to the DC610 MUD\r\n\r\nOpinions expressed in this game do not represent EvilMog, his\r\nemployer, DEF CON, the Church of Wifi, DC610, or any other\r\nparty.\r\n\r\nAll characters are a work of fiction. \r\n\r\nTrigger Warning: PG13 ish, Code Of Conduct Applies\r\n\r\nHashing is unsalted SHA1, special characters break passwords (don't ask)\r\n\r\nBring Peeps Crispies, Peeps Cola, and A Cheese Fez Helmet to EvilMog\r\nfor Cheat Codes. Alternatively a Junmai Ginjo Sake from Hiroshima, or\r\na Junmai Daiginjo at 5 degrees Celcius with a ceramic sake cup will\r\nget you good cheat codes\r\n\r\nTell Johnny Xmas the password is Sea Cucumber, he will give you something.\r\n\r\nEnter your name ('quit'): \u001b[6z<!-- Elements to support the Automapper --><!ELEMENT RName FLAG=\"RoomName\"><!ELEMENT RDesc FLAG='RoomDesc'><!ELEMENT RExits FLAG='RoomExit'><!-- The next element is used to define a room exit link that sends the exit direction to the MUD if the user clicks on it --><!ELEMENT Ex '<SEND>'><!ELEMENT Announce '<FONT COLOR=Cyan>' OPEN><!ELEMENT Gossip '<FONT COLOR=Green>' OPEN><!-- the next elements deal with the MUD prompt --><!ELEMENT Prompt FLAG=\"Prompt\"><!ELEMENT Hp FLAG=\"Set hp\"><!ELEMENT MaxHp FLAG=\"Set maxhp\"><!ELEMENT Mana FLAG=\"Set mana\"><!ELEMENT MaxMana FLAG=\"Set maxmana\"><!ELEMENT End FLAG=\"Set end\"><!ELEMENT MaxEnd FLAG=\"Set maxend\"><!ELEMENT RoomX FLAG=\"Set room_x\"><!ELEMENT RoomY FLAG=\"Set room_y\"><!ELEMENT RoomZ FLAG=\"Set room_Z\"><!EL Itm '<send \"look &text;|drop &text;|wear &text;|wield &text;|drink &text;|unwield &text;|remove &text;\">'><!EL Click '<send \"&text;\">'><!EL ClickP '<send \"&text;\" PROMPT>'>\u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"ECHO": false,
"GMCP": true,
"MXP": true
},
"server_requested": {
"LINEMODE": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5164134502410889,
"total": 5.168087482452393
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:10:18.041346+00:00",
"host": "44.235.126.228",
"ip": "44.235.126.228",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 44.235.126.228 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=44.235.126.228 port=4000
ERROR client.py:1318 44.235.126.228:4000: TCP connection to 44.235.126.228:4000 timed out after 30.0s