40.115.76.212
40.115.76.212:4040
Connection Banner:
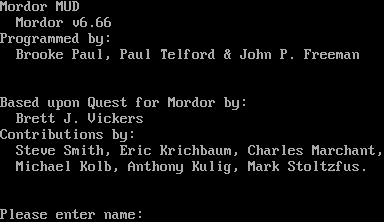
Server URLs
- Telnet: telnet://40.115.76.212:4040
Server Info
Server Location: 🇦🇺 Australia (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Please enter name: ",
"banner_before_return": "\n\rMordor MUD\n\r Mordor v6.66\n\rProgrammed by:\n\r Brooke Paul, Paul Telford & John P. Freeman\n\r\n\r\n\rBased upon Quest for Mordor by:\n\r Brett J. Vickers\n\rContributions by:\n\r Steve Smith, Eric Krichbaum, Charles Marchant,\n\r Michael Kolb, Anthony Kulig, Mark Stoltzfus.\n\r\n\r\n\rPlease enter name: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5040984153747559,
"total": 11.263715744018555
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:58:28.790080+00:00",
"host": "40.115.76.212",
"ip": "40.115.76.212",
"port": 4040
},
{
"connected": "2026-04-07T07:17:31.281142+00:00",
"host": "40.115.76.212",
"ip": "40.115.76.212",
"port": 4040
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 40.115.76.212 4040
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=40.115.76.212 port=4040
INFO client_base.py:190 Connected to <Peer 40.115.76.212 4040>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MXP, WILL MSSP, WILL AARDWOLF, WILL ZMP, WILL GMCP, WILL MSDP,
WILL MCCP2_COMPRESS, WILL MSP, WILL ATCP, DO MCCP3_COMPRESS, DO MXP, DO MSSP, DO AARDWOLF, DO ZMP, DO GMCP, DO MSDP, DO
MCCP2_COMPRESS, DO MSP, DO ATCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 40.115.76.212 4040>
tmux.wonko.info:4042
Connection Banner:
![TerraMUD T E R R A M U D X v6.68 [The Neighbour of the Beast] (TMUX) Originally Programmed by Brooke Paul, Paul Telford & John P. Freeman Hacked, customized and re-themed by wOnKo 2002-2008 ______ CONNECT: telnet:terramud.wonko.info:4042 -w- \|______\| __ __ _ _ __ __\|____@_\|__ \\ \\ / / \| \| \| \| / _\| \\\\\\\\\\\\, " (')') \\ \\ /\\ / /__ _ __\| \| __\| \| ___ \| \|_ _/'') \\\\\\ C _) \\ \\/ \\/ / _ \\\| '__\| \|/ _\` \| / _ \\\| _\| \\ D \\ _\| \\ /\\ / (_) \| \| \| \| (_\| \| \| (_) \| \| \\_ / \\__/ \\/ \\/ \\___/\|_\| \|_\|\\__,_\| \\___/\|_\| <\\ />,_ <___Y> _______ __ __ _ _ _____ __ __ / \\Y/ /\` \\ / \\ /\\\\ \|__ __\| \| \\/ \| \| \| \| __ \\\\ \\ / / \|_\| # \|__\| / \| \\\|\\ \| \| ___ _ __ _ __ __ _\| \\ / \| \| \| \| \| \| \|\\ \\/ / \|\| / \| \| \|___\| \\\|/\\ \| \|/ _ \\ '__\| '__/ _\` \| \|\\/\| \| \| \| \| \| \| \| \| \| \|\| / \| ) \| \| \\\|\\ \\ \| \| __/ \| \| \| \| (_\| \| \| \| \| \|__\| \| \|__\| \|/ /\\ \\ \|\| V \| \| \\ \\ v\| \\ \\_\|_\|\\___\|_\| \|_\| \\__,_\|_\| \|_\|\\____/\|_____//_/ \\_\\ _\|\|=[]=\|_\| \\ \\==[\| \\\\\\ //\| \| /\|\\\\ ///\` \|\| A massively [well, fairly big anyway] multiplayer \| \| \| \| \|\| first-person text-based online role play game. \|_\|___\| \| )) \| \| \| \| \|\| (_( \| \| \|\| Battle in and around the remains of an Inner-City College [ \|_\| [___]] now in ruins. Explore, collect and use your Imagination. _\|_[_] \|____)) (_(___\| The TEXTUAL REALITY "First Person Texter" in glorious TEXT-O-RAMA. NEWBIES GUIDE: http://www.wonko.info/mud/ Please enter your character name [or make up a new one]:](../_images/banner_5ba13f1df66f.png)
Server URLs
- Telnet: telnet://tmux.wonko.info:4042
- Website: terramud.wonko.info
Server Info
Server Location: 🇦🇺 Australia (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Please enter your character name [or make up a new one]: ",
"banner_before_return": "\n\rTerraMUD\n\rT E R R A M U D X v6.68 [The Neighbour of the Beast] (TMUX)\n\r Originally Programmed by Brooke Paul, Paul Telford & John P. Freeman\n\r Hacked, customized and re-themed by wOnKo 2002-2008\n\r ______ CONNECT: telnet:terramud.wonko.info:4042 -w-\n\r |______| __ __ _ _ __ \n\r__|____@_|__ \\ \\ / / | | | | / _| \\\\\\\\\\\\, \n\r \" (')') \\ \\ /\\ / /__ _ __| | __| | ___ | |_ _/'') \\\\\\\n\r C _) \\ \\/ \\/ / _ \\| '__| |/ _` | / _ \\| _| \\ D\n\r \\ _| \\ /\\ / (_) | | | | (_| | | (_) | | \\_ / \n\r \\__/ \\/ \\/ \\___/|_| |_|\\__,_| \\___/|_| <\\ />,_\n\r <___Y> _______ __ __ _ _ _____ __ __ / \\Y/ /` \\\n\r / \\ /\\\\ |__ __| | \\/ | | | | __ \\\\ \\ / / |_| # |__|\n\r / | \\|\\ | | ___ _ __ _ __ __ _| \\ / | | | | | | |\\ \\/ / || / | |\n\r |___| \\|/\\ | |/ _ \\ '__| '__/ _` | |\\/| | | | | | | | | | || / | )\n\r | | \\|\\ \\ | | __/ | | | | (_| | | | | |__| | |__| |/ /\\ \\ || V | |\n\r \\ \\ v| \\ \\_|_|\\___|_| |_| \\__,_|_| |_|\\____/|_____//_/ \\_\\ _||=[]=|_|\n\r \\ \\==[| \\\\\\ //| | /|\\\\\n\r ///` || A massively [well, fairly big anyway] multiplayer | | | \n\r | || first-person text-based online role play game. |_|___|\n\r | )) | | |\n\r | || (_( |\n\r | || Battle in and around the remains of an Inner-City College [ |_|\n\r [___]] now in ruins. Explore, collect and use your Imagination. _|_[_]\n\r |____)) (_(___|\n\r The TEXTUAL REALITY \"First Person Texter\" in glorious TEXT-O-RAMA.\n\r NEWBIES GUIDE: http://www.wonko.info/mud/\n\r\n\rPlease enter your character name [or make up a new one]: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5137763023376465,
"total": 11.248708248138428
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:04:42.445212+00:00",
"host": "tmux.wonko.info",
"ip": "40.115.76.212",
"port": 4042
},
{
"connected": "2026-04-07T06:45:05.711191+00:00",
"host": "tmux.wonko.info",
"ip": "40.115.76.212",
"port": 4042
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug tmux.wonko.info 4042
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=tmux.wonko.info port=4042
INFO client_base.py:190 Connected to <Peer 40.115.76.212 4042>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, WILL MSSP, WILL AARDWOLF, WILL MSDP, WILL ZMP,
WILL MXP, WILL ATCP, WILL GMCP, WILL MSP, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO MSSP, DO AARDWOLF, DO MSDP, DO ZMP, DO MXP,
DO ATCP, DO GMCP, DO MSP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 40.115.76.212 4042>