bc.kelotz.net
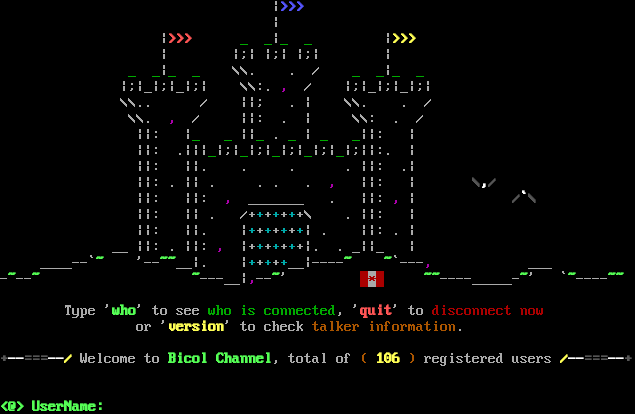
Connection Banner:
Server URLs
- Telnet: telnet://bc.kelotz.net:2018
Server Info
Server Location: 🇨🇦 Canada (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[0m\n\r\u001b[1m\u001b[32m<@> UserName: \u001b[0m",
"banner_before_return": "\n\r |\u001b[1m\u001b[34m>>>\u001b[0m\u001b[0m\n\r |\u001b[0m\n\r |\u001b[1m\u001b[31m>>>\u001b[0m \u001b[32m_ _\u001b[0m|\u001b[32m_ _\u001b[0m |\u001b[1m\u001b[33m>>>\u001b[0m\u001b[0m\n\r | |;| |;| |;| |\u001b[0m\n\r \u001b[32m_ _\u001b[0m|\u001b[32m_ _\u001b[0m \\\\. . / \u001b[32m_ _\u001b[0m|\u001b[32m_ _\u001b[0m\u001b[0m\n\r |;|_|;|_|;| \\\\:. \u001b[35m,\u001b[0m / |;|_|;|_|;|\u001b[0m\n\r \\\\.. / ||; . | \\\\. . /\u001b[0m\n\r \\\\. \u001b[35m,\u001b[0m / ||: . | \\\\: . /\u001b[0m\n\r ||: |\u001b[32m_ _\u001b[0m ||\u001b[32m_\u001b[0m .\u001b[32m _ \u001b[0m| \u001b[32m_ _\u001b[0m||: |\u001b[0m\n\r ||: .|||\u001b[32m_\u001b[0m|;|\u001b[32m_\u001b[0m|;|\u001b[32m_\u001b[0m|;|\u001b[32m_\u001b[0m|;|\u001b[32m_\u001b[0m|;||:. |\u001b[0m\n\r ||: ||. . . . ||: .|\u001b[0m\n\r ||: . || . . . . \u001b[35m,\u001b[0m ||: | \u001b[1m\u001b[30m\\\u001b[37m,\u001b[30m/\u001b[0m\u001b[0m\n\r ||: ||: \u001b[35m,\u001b[0m _______ . ||: \u001b[35m,\u001b[0m | \u001b[1m\u001b[30m/\u001b[37m`\u001b[30m\\\u001b[0m\u001b[0m\n\r ||: || . /+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\\ . ||: |\u001b[0m\n\r ||: ||. |\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m| . ||: . |\u001b[0m\n\r __ ||: . ||: \u001b[35m,\u001b[0m |+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+|. . _||_ |\u001b[0m\n\r ____--`\u001b[1m\u001b[32m~\u001b[0m '--\u001b[1m\u001b[32m~~\u001b[0m__|. |\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m+\u001b[36m+\u001b[0m__|----\u001b[1m\u001b[32m~ ~\u001b[0m`---\u001b[35m,\u001b[0m ___\u001b[0m\n\r-\u001b[1m\u001b[32m~\u001b[0m--\u001b[1m\u001b[32m~\u001b[0m \u001b[1m\u001b[32m~\u001b[0m---__|\u001b[35m,\u001b[0m--\u001b[1m\u001b[32m~\u001b[0m' \u001b[41m \u001b[47m\u001b[31m*\u001b[41m \u001b[0m \u001b[1m\u001b[32m~~\u001b[0m----_____-\u001b[1m\u001b[32m~\u001b[0m' `\u001b[1m\u001b[32m~\u001b[0m----\u001b[1m\u001b[32m~~\u001b[0m\u001b[0m\n\r\u001b[0m\n\r Type '\u001b[1m\u001b[32mwho\u001b[0m' to see \u001b[32mwho is connected\u001b[0m, '\u001b[1m\u001b[31mquit\u001b[0m' to \u001b[31mdisconnect now\u001b[0m \u001b[0m\n\r or '\u001b[1m\u001b[33mversion\u001b[0m' to check \u001b[33mtalker information\u001b[0m.\u001b[0m\n\r\u001b[0m\n\r\u001b[0m\u001b[1m\u001b[30m+\u001b[37m--\u001b[30m===\u001b[37m--\u001b[33m/ \u001b[0mWelcome to \u001b[1m\u001b[32mBicol Channel\u001b[0m, total of \u001b[33m(\u001b[1m 106\u001b[0m\u001b[33m ) \u001b[0mregistered users \u001b[1m\u001b[33m/\u001b[37m--\u001b[30m===\u001b[37m--\u001b[30m+\u001b[0m\u001b[0m\n\r\u001b[0m\n\r\u001b[0m\n\r\u001b[0m\u001b[0m\u001b[1m\u001b[32m<@> UserName: \u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": false
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5038516521453857,
"total": 11.16400694847107
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:55.564519+00:00",
"host": "bc.kelotz.net",
"ip": "207.47.192.67",
"port": 2018
},
{
"connected": "2026-04-07T07:09:18.024767+00:00",
"host": "bc.kelotz.net",
"ip": "207.47.192.67",
"port": 2018
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug bc.kelotz.net 2018
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=bc.kelotz.net port=2018
INFO client_base.py:190 Connected to <Peer 207.47.192.67 2018>
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL MSP, WILL MCCP2_COMPRESS, WILL GMCP, WILL ATCP, WILL MSDP, WILL AARDWOLF,
WILL MXP, WILL MCCP3_COMPRESS, WILL ZMP, DO MSSP, DO MSP, DO MCCP2_COMPRESS, DO GMCP, DO ATCP, DO MSDP, DO AARDWOLF, DO MXP,
DO MCCP3_COMPRESS, DO ZMP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 207.47.192.67 2018>