blackfire.online
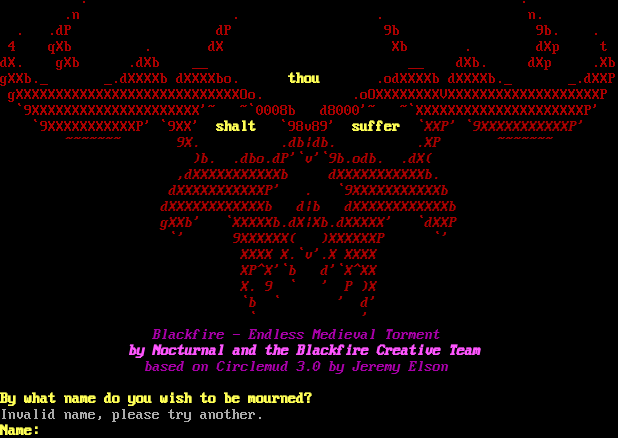
Connection Banner:
Server URLs
- Telnet: telnet://blackfire.online:4000
- Website: 9b.odb
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Invalid name, please try another.\r\n\u001b[1;33mName:\u001b[0;0m \u001b[0m",
"banner_before_return": "\r\n\r\n\u001b[36m\r\n\r\n\u001b[2J\u001b[H\u001b[0m\u001b[37m \u001b[31m .\u001b[37m \u001b[31m.\r\n\u001b[37m \u001b[31m.n\u001b[37m \u001b[31m.\u001b[37m \u001b[31m.\u001b[37m \u001b[31mn.\r\n\u001b[37m \u001b[31m.\u001b[37m \u001b[31m.dP\u001b[37m \u001b[31mdP\u001b[37m \u001b[31m9b\u001b[37m \u001b[31m9b.\u001b[37m \u001b[31m.\r\n\u001b[37m \u001b[31m4\u001b[37m \u001b[31mqXb\u001b[37m \u001b[31m.\u001b[37m \u001b[31mdX\u001b[37m \u001b[31mXb\u001b[37m \u001b[31m.\u001b[37m \u001b[31mdXp\u001b[37m \u001b[31mt\r\ndX.\u001b[37m \u001b[31mgXb\u001b[37m \u001b[31m.dXb\u001b[37m \u001b[31m__\u001b[37m \u001b[31m__\u001b[37m \u001b[31mdXb.\u001b[37m \u001b[31mdXp\u001b[37m \u001b[31m.Xb\r\ngXXb._\u001b[37m \u001b[31m_.dXXXXb\u001b[37m \u001b[31mdXXXXbo.\u001b[37m \u001b[1;33m thou\u001b[0;37;0m \u001b[31m.odXXXXb\u001b[37m \u001b[31mdXXXXb._\u001b[37m \u001b[31m_.dXXP\r\n\u001b[37m \u001b[31mgXXXXXXXXXXXXXXXXXXXXXXXXXXXXOo.\u001b[37m \u001b[31m.oOXXXXXXXXVXXXXXXXXXXXXXXXXXXXP\r\n\u001b[37m \u001b[31m`9XXXXXXXXXXXXXXXXXXXXX'~\u001b[37m \u001b[31m~`0008b\u001b[37m \u001b[31md8000'~\u001b[37m \u001b[31m~`XXXXXXXXXXXXXXXXXXXXXP'\r\n\u001b[37m \u001b[31m`9XXXXXXXXXXXP'\u001b[37m \u001b[31m`9XX'\u001b[37m \u001b[1;33mshalt\u001b[0;37;0m \u001b[31m`98v89'\u001b[37m \u001b[1;33msuffer\u001b[0;31;3m `XXP'\u001b[37m \u001b[31m`9XXXXXXXXXXXP'\r\n\u001b[37m \u001b[31m~~~~~~~\u001b[37m \u001b[31m9X.\u001b[37m \u001b[31m.db|db.\u001b[37m \u001b[31m.XP\u001b[37m \u001b[31m~~~~~~~\r\n\u001b[37m \u001b[31m)b.\u001b[37m \u001b[31m.dbo.dP'`v'`9b.odb.\u001b[37m \u001b[31m.dX(\r\n\u001b[37m \u001b[31m,dXXXXXXXXXXXb\u001b[37m \u001b[31mdXXXXXXXXXXXb.\r\n\u001b[37m \u001b[31mdXXXXXXXXXXXP'\u001b[37m \u001b[31m.\u001b[37m \u001b[31m`9XXXXXXXXXXXb\r\n\u001b[37m \u001b[31mdXXXXXXXXXXXXb\u001b[37m \u001b[31md|b\u001b[37m \u001b[31mdXXXXXXXXXXXXb\r\n\u001b[37m \u001b[31mgXXb'\u001b[37m \u001b[31m`XXXXXb.dX|Xb.dXXXXX'\u001b[37m \u001b[31m`dXXP\r\n\u001b[37m \u001b[31m`'\u001b[37m \u001b[31m9XXXXXX(\u001b[37m \u001b[31m)XXXXXXP\u001b[37m \u001b[31m`'\r\n\u001b[37m \u001b[31mXXXX\u001b[37m \u001b[31mX.`v'.X\u001b[37m \u001b[31mXXXX\r\n\u001b[37m \u001b[31mXP^X'`b\u001b[37m \u001b[31md'`X^XX\r\n\u001b[37m \u001b[31mX.\u001b[37m \u001b[31m9\u001b[37m \u001b[31m`\u001b[37m \u001b[31m'\u001b[37m \u001b[31mP\u001b[37m \u001b[31m)X\r\n\u001b[37m \u001b[31m`b\u001b[37m \u001b[31m`\u001b[37m \u001b[31m'\u001b[37m \u001b[31md'\r\n\u001b[37m \u001b[31m`\u001b[37m \u001b[31m'\r\n\u001b[35m Blackfire - Endless Medieval Torment\r\n\u001b[1m by Nocturnal and the Blackfire Creative Team\r\n\u001b[0;35;3m based on Circlemud 3.0 by Jeremy Elson\u001b[1m\r\n\r\n\u001b[0m\u001b[1;33mBy what name do you wish to be mourned?\u001b[0;0m \u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5054996013641357,
"total": 11.24847149848938
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:17.266765+00:00",
"host": "blackfire.online",
"ip": "31.220.4.180",
"port": 4000
},
{
"connected": "2026-04-07T07:25:18.760546+00:00",
"host": "blackfire.online",
"ip": "31.220.4.180",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug blackfire.online 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=blackfire.online port=4000
INFO client_base.py:190 Connected to <Peer 31.220.4.180 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MXP, WILL MSSP, WILL MSP, WILL GMCP, WILL ZMP, WILL AARDWOLF,
WILL ATCP, WILL MSDP, WILL MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO MXP, DO MSSP, DO MSP, DO GMCP, DO ZMP, DO AARDWOLF, DO ATCP,
DO MSDP, DO MCCP2_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 31.220.4.180 4000>