torilmud.org
Connection Banner:
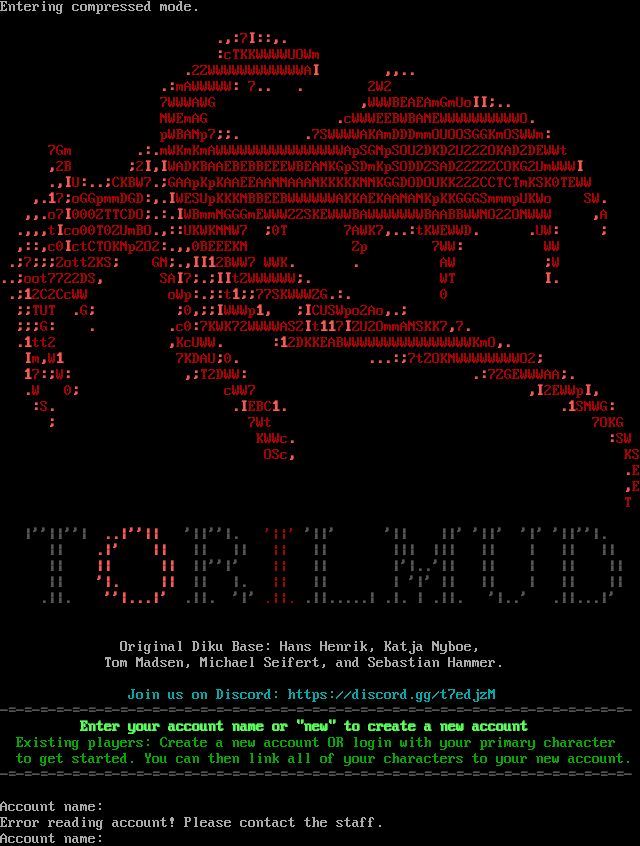
Server URLs
- Telnet: telnet://torilmud.org:9999
- Website: https://discord.gg/t7edjzM
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 1 other server.
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9aa8b85bb2525a87",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Error reading account! Please contact the staff.\u001b[0m\nAccount name: ",
"banner_before_return": "\nEntering compressed mode.\n\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mcTKKWWWWUOWm\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m2ZWWWWWWWWWWWWA\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mmAWWWWW\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m 7\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m 2W2\r\u001b[0m\n\u001b[0m\u001b[31m 7WWWAWG \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mWWWBEAEAmGmUo\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m NWEmAG \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mcWWWEEBWBANEWWWWWWWWWWO\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m pWBANp7\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m7SWWWWAKAmDDDmmOUOOSGGKmOSWWm\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m 7Gm \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mmWKmKmAWWWWWWWWWWWWWWWWApSGNpSOU2DKD2U222OKAD2DEWWt\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m2B \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m2\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mWADKBAAEBEBBEEEWBEANKGpSDmKpSODDZSAD22ZZZCOKG2UmWWW\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mU\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mCKBW7\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mGAApKpKAAEEAANNAAANKKKKKNNKGGDODOUKK222CCTCTmKSK0TEWW\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31moGGpmmDGD\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mWESUpKKKNBBEEBWWWWWWAKKAEKAANANKpKKGGGSmmmpUKWo SW\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mo7\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m000ZTTCDO\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mWBmmNGGGmEWWWZZSKEWWWBAWWWWWWWBAABBWWNO22ONWWW \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mA\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mt\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mco00T0ZUmBO\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mUKWKNNW7 \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m0T 7AWK7\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mtKWEWWD\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mUW\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mc0\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mctCTOKNpZO2\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m0BEEEKN Zp 7WW\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m WW\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mZottZKS\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m GN\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m2BWW7 WWK\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m AW \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mW\r\u001b[0m\n\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31moot7722DS\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m SA\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mtZWWWWWW\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m WT \u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m2C2CcWW oWp\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mt\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m77SKWWWZG\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m 0\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mTUT \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mG\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m0\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mWWWp\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mCUSWpo2Ao\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mG\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mc0\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m7KWK72WWWWASZ\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mt\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mZU2OmmANSKK7\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31mtt2 \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mKcUWW\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m2DKKEABWWWWWWWWWWWWWWWWKmO\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mm\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mW\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m 7KDAU\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m0\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m7tZOKNWWWWWWWWO2\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m7\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mW\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31mT2DWW\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m7ZGEWWWAA\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mW 0\u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m cWW7 \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m2EWWp\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mS\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m\u001b[0m\u001b[1;31mI\u001b[0m\u001b[31m\u001b[0m\u001b[31mEBC\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m\u001b[0m\u001b[1;31m1\u001b[0m\u001b[31mSNWG\u001b[0m\u001b[1;31m:\u001b[0m\u001b[31m\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m;\u001b[0m\u001b[31m 7Wt 7OKG\r\u001b[0m\n\u001b[0m\u001b[31m KWWc\u001b[0m\u001b[1;31m.\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m:\u001b[0m\u001b[31mSW\r\u001b[0m\n\u001b[0m\u001b[31m OSc\u001b[0m\u001b[1;31m,\u001b[0m\u001b[31m KS\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m.\u001b[0m\u001b[31mE\r\u001b[0m\n\u001b[0m\u001b[31m \u001b[0m\u001b[1;31m,\u001b[0m\u001b[31mE\r\u001b[0m\n\u001b[0m\u001b[31m T\r\u001b[0m\n\r\u001b[0m\n\u001b[0m\u001b[1;30m |''||''|\u001b[0m\u001b[1;31m ..|''|| \u001b[0m\u001b[1;30m '||''|. \u001b[0m\u001b[31m '||'\u001b[0m\u001b[1;30m '||' '|| ||' '||' '|' '||''|.\r\u001b[0m\n\u001b[0m\u001b[1;30m || \u001b[0m\u001b[1;31m .|' || \u001b[0m\u001b[1;30m || || \u001b[0m\u001b[31m || \u001b[0m\u001b[1;30m || ||| ||| || | || ||\r\u001b[0m\n\u001b[0m\u001b[1;30m || \u001b[0m\u001b[1;31m || ||\u001b[0m\u001b[1;30m ||''|' \u001b[0m\u001b[31m || \u001b[0m\u001b[1;30m || |'|..'|| || | || ||\r\u001b[0m\n\u001b[0m\u001b[1;30m || \u001b[0m\u001b[1;31m '|. ||\u001b[0m\u001b[1;30m || |. \u001b[0m\u001b[31m || \u001b[0m\u001b[1;30m || | '|' || || | || ||\r\u001b[0m\n\u001b[0m\u001b[1;30m .||. \u001b[0m\u001b[1;31m ''|...|' \u001b[0m\u001b[1;30m .||. '|'\u001b[0m\u001b[31m .||.\u001b[0m\u001b[1;30m .||.....| .|. | .||. '|..' .||...|'\r\u001b[0m\n\r\u001b[0m\n\r\u001b[0m\n \u001b[37mOriginal Diku Base: Hans Henrik, Katja Nyboe,\r\u001b[0m\n \u001b[37mTom Madsen, Michael Seifert, and Sebastian Hammer.\r\u001b[0m\n\r\u001b[0m\n \u001b[36mJoin us on Discord: https://discord.gg/t7edjzM\r\u001b[0m\n\u001b[0m\u001b[1;30m-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-\u001b[0m\n \u001b[0m\u001b[1;32mEnter your account name or \"new\" to create a new account\u001b[0m\n \u001b[0m\u001b[32mExisting players:\u001b[0m\u001b[32m Create a new account OR login with your primary character\u001b[0m\n \u001b[0m\u001b[32mto get started. You can then link all of your characters to your new account.\u001b[0m\n\u001b[0m\u001b[1;30m-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-\u001b[0m\n\u001b[0m\n\u001b[0m\u001b[37mAccount name: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5037720203399658,
"total": 11.33309531211853
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:11.068465+00:00",
"host": "torilmud.org",
"ip": "104.236.2.214",
"port": 9999
},
{
"connected": "2026-04-07T06:58:32.885667+00:00",
"host": "torilmud.org",
"ip": "104.236.2.214",
"port": 9999
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug torilmud.org 9999
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=torilmud.org port=9999
INFO client_base.py:190 Connected to <Peer 104.236.2.214 9999>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL ZMP, WILL MCCP3_COMPRESS, WILL GMCP, WILL ATCP,
WILL MSP, WILL MSSP, WILL MSDP, WILL MXP, DO AARDWOLF, DO MCCP2_COMPRESS, DO ZMP, DO MCCP3_COMPRESS, DO GMCP, DO ATCP, DO MSP,
DO MSSP, DO MSDP, DO MXP, SB TTYPE'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 9aa8b85bb2525a87
INFO client_base.py:122 Connection closed to <Peer 104.236.2.214 9999>