mud.nemesis.de
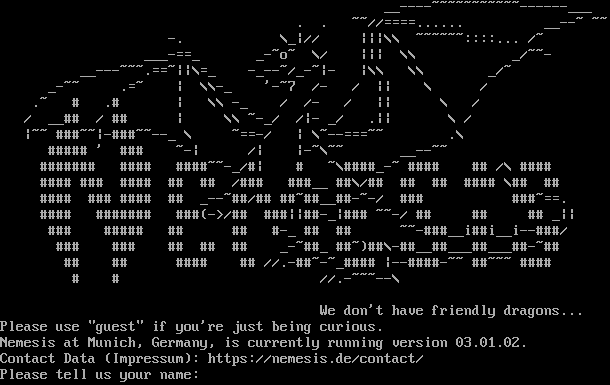
Connection Banner:
Server URLs
- Telnet: telnet://mud.nemesis.de:2000
- Website: https://nemesis.de/contact/
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "6f760814123baeb7",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\n __----~~~~~~~~~~~------___\r\n . . ~~//====...... __--~ ~~\r\n -. \\_|// |||\\\\ ~~~~~~::::... /~\r\n ___-==_ _-~o~ \\/ ||| \\\\ _/~~-\r\n __---~~~.==~||\\=_ -_--~/_-~|- |\\\\ \\\\ _/~\r\n _-~~ .=~ | \\\\-_ '-~7 /- / || \\ /\r\n .~ # .# | \\\\ -_ / /- / || \\ /\r\n / __## / ## | \\\\ ~-_/ /|- _/ .|| \\ /\r\n |~~ ###~~|-###~~--_ \\ ~==-/ | \\~--===~~ .\\\r\n ##### ' ### ~-| /| |-~\\~~ __--~~\r\n ####### #### ####~~-_/#| # ~\\####_-~ #### ## /\\ ####\r\n #### ### #### ## ## /### ###__ ##\\/## ## ## #### \\## ##\r\n #### ### #### ## _--~##/## ##~##__##-~-/ ### ###~==.\r\n #### ####### ###(->/## ###||##-_|### ~~-/ ## ## ## _||\r\n ### ##### ## ## #-_ ## ## ~~-###__i##i__i--###/\r\n ### ### ## ## ## _-~##_ ##~)##\\-##__##___##___##-~##\r\n ## ## #### ## //.-##~-~_#### |--####-~~ ##~~~ ####\r\n # # //.-~~~--\\\r\n\r\n We don't have friendly dragons...\r\nPlease use \"guest\" if you're just being curious.\r\nNemesis at Munich, Germany, is currently running version 03.01.02.\r\nContact Data (Impressum): https://nemesis.de/contact/\r\nPlease tell us your name: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.662405014038086
}
}
},
"sessions": [
{
"connected": "2026-04-08T22:39:41.208735+00:00",
"host": "mud.nemesis.de",
"ip": "81.92.172.208",
"port": 2000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.nemesis.de 2000
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=mud.nemesis.de port=2000
INFO client_base.py:186 Connected to <Peer 81.92.172.208 2000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG client_base.py:499 negotiation failed after 4.00s.
DEBUG client_base.py:505 failed-reply: 'WILL MSP, WILL MSDP, WILL GMCP, WILL MCCP2_COMPRESS, WILL ZMP, WILL MSSP, WILL ATCP, WILL
AARDWOLF, WILL MXP, WILL MCCP3_COMPRESS, DO MSP, DO MSDP, DO GMCP, DO MCCP2_COMPRESS, DO ZMP, DO MSSP, DO ATCP, DO AARDWOLF,
DO MXP, DO MCCP3_COMPRESS, SB TTYPE'
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:89 EOF from server, closing.
INFO client_base.py:118 Connection closed to <Peer 81.92.172.208 2000>
DEBUG fingerprinting.py:849 connection for server fingerprint 6f760814123baeb7