mud.valheru.com
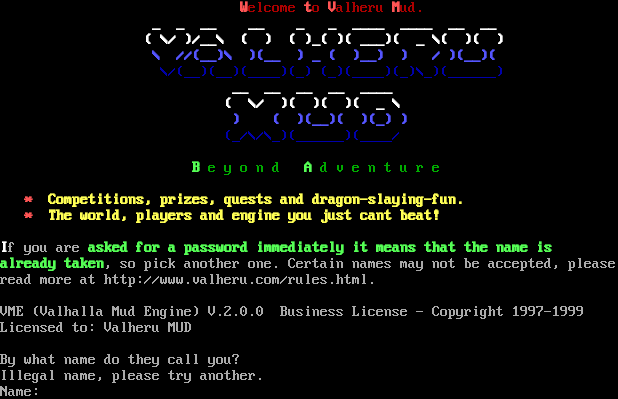
Connection Banner:
Server URLs
- Telnet: telnet://mud.valheru.com:4242
- Website: http://www.valheru.com/rules.html.
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal name, please try another.\n\rName: ",
"banner_before_return": "\n\r\n\r\r\n\r\r \u001b[1;31mW\u001b[0;31m\u001b[40melcome \u001b[1;31mt\u001b[0;31m\u001b[40mo \u001b[1;31mV\u001b[0;31m\u001b[40malheru \u001b[1;31mM\u001b[0;31m\u001b[40mud.\u001b[0;37m\u001b[40m\n\r\r \u001b[1;37m _ _ __ __ _ _ ____ ____ __ __ \n\r\r \u001b[1;37m ( \\/ )/__\\ ( ) ( )_( )( ___)( _ \\( )( ) \n\r\r \u001b[1;34m \\ //(__)\\ )(__ ) _ ( )__) ) / )(__)( \n\r\r \u001b[0;34m\u001b[40m \\/(__)(__)(____)(_) (_)(____)(_)\\_)(______) \n\r\r \u001b[1;37m __ __ __ __ ____ \n\r\r \u001b[1;37m ( \\/ )( )( )( _ \\ \n\r\r \u001b[1;34m ) ( )(__)( )(_) )\n\r\r \u001b[0;34m\u001b[40m (_/\\/\\_)(______)(____/ \n\r\r \n\r\r \u001b[1;32mB\u001b[0;32m\u001b[40m e y o n d \u001b[1;32mA\u001b[0;32m\u001b[40m d v e n t u r e\u001b[0;37m\u001b[40m \n\r\r \n\r\r \u001b[1;31m*\u001b[1;33m Competitions, prizes, quests and dragon-slaying-fun.\n\r\r \u001b[1;31m*\u001b[1;33m The world, players and engine you just cant beat!\n\r\r\n\r\r\u001b[1;37mI\u001b[0;37m\u001b[40mf you are \u001b[1;32masked for a password immediately it means that the name is\n\r\ralready taken\u001b[0;37m\u001b[40m, so pick another one. Certain names may not be accepted, please \n\r\rread more at http://www.valheru.com/rules.html.\n\r\r\nVME (Valhalla Mud Engine) V.2.0.0 Business License - Copyright 1997-1999\n\rLicensed to: Valheru MUD\n\r\n\rBy what name do they call you? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5041828155517578,
"total": 11.37200117111206
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:58.795212+00:00",
"host": "mud.valheru.com",
"ip": "167.71.64.84",
"port": 4242
},
{
"connected": "2026-04-07T07:18:15.270744+00:00",
"host": "mud.valheru.com",
"ip": "167.71.64.84",
"port": 4242
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.valheru.com 4242
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.valheru.com port=4242
INFO client_base.py:190 Connected to <Peer 167.71.64.84 4242>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL MSDP, WILL GMCP, WILL AARDWOLF, WILL ATCP, WILL MCCP2_COMPRESS, WILL MXP,
WILL MSSP, WILL MCCP3_COMPRESS, WILL ZMP, DO MSP, DO MSDP, DO GMCP, DO AARDWOLF, DO ATCP, DO MCCP2_COMPRESS, DO MXP, DO MSSP,
DO MCCP3_COMPRESS, DO ZMP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 167.71.64.84 4242>