mud.valinor.com.br
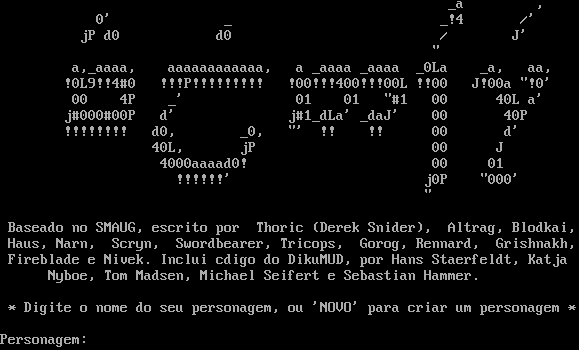
Connection Banner:
Server URLs
- Telnet: telnet://mud.valinor.com.br:4000
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "6f760814123baeb7",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\n\r\n\r _a ,\n\r 0' _ _!4 /'\n\r jP d0 d0 / J'\n\r \"\n\r a,_aaaa, aaaaaaaaaaaa, a _aaaa _aaaa _0La _a, aa,\n\r !0L9!!4#0 !!!P!!!!!!!!! !00!!!400!!!00L !!00 J!00a \"!0'\n\r 00 4P _' 01 01 \"#1 00 40L a'\n\r j#000#00P d' j#1_dLa' _daJ' 00 40P\n\r !!!!!!!! d0, _0, \"' !! !! 00 d'\n\r 40L, jP 00 J\n\r 4000aaaad0! 00 01\n\r !!!!!!' j0P \"000'\n\r \"\n\r\n\r Baseado no SMAUG, escrito por Thoric (Derek Snider), Altrag, Blodkai,\n\r Haus, Narn, Scryn, Swordbearer, Tricops, Gorog, Rennard, Grishnakh,\n\r Fireblade e Nivek. Inclui c\udcf3digo do DikuMUD, por Hans Staerfeldt, Katja\n\r Nyboe, Tom Madsen, Michael Seifert e Sebastian Hammer.\n\r\n\r * Digite o nome do seu personagem, ou 'NOVO' para criar um personagem *\n\r\n\rPersonagem: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.8182079792022705
}
}
},
"sessions": [
{
"connected": "2026-04-08T22:39:41.195960+00:00",
"host": "mud.valinor.com.br",
"ip": "199.101.100.114",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.valinor.com.br 4000
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=mud.valinor.com.br port=4000
INFO client_base.py:186 Connected to <Peer 199.101.100.114 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:499 negotiation failed after 4.00s.
DEBUG client_base.py:505 failed-reply: 'WILL MXP, WILL ZMP, WILL MSDP, WILL ATCP, WILL MCCP2_COMPRESS, WILL AARDWOLF, WILL
MCCP3_COMPRESS, WILL GMCP, WILL MSSP, WILL MSP, DO MXP, DO ZMP, DO MSDP, DO ATCP, DO MCCP2_COMPRESS, DO AARDWOLF, DO
MCCP3_COMPRESS, DO GMCP, DO MSSP, DO MSP'
DEBUG client_base.py:89 EOF from server, closing.
INFO client_base.py:118 Connection closed to <Peer 199.101.100.114 4000>
DEBUG fingerprinting.py:849 connection for server fingerprint 6f760814123baeb7