Sanity’s Edge
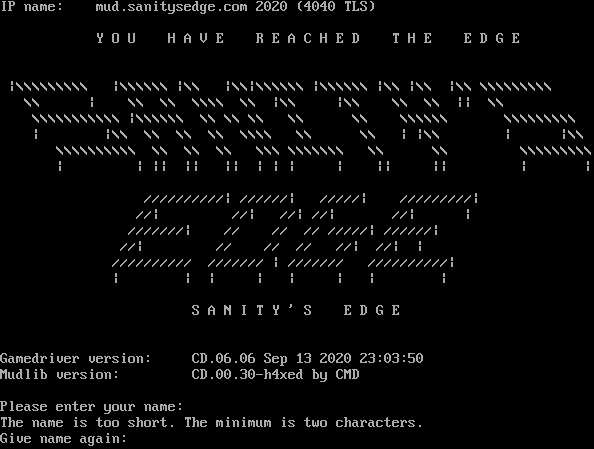
Connection Banner:
Server URLs
- Telnet: telnet://sanitysedge.com:2020
- Play in Browser: LociTerm
- Website: sanitysedge.com
Server Info
Codebase: CD
Genre: Science Fiction
Gameplay: Hack and Slash
Players online: 6 [1]
Uptime: 4 days
Created: 1995
Server Location: 🇺🇸 United States of America (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options offered by server: CHARSET, ECHO, GMCP, MSSP, SGA
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "fc3ff80640fda031",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"ECHO",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "The name is too short. The minimum is two characters.\r\nGive name again: ",
"banner_before_return": "IP name: mud.sanitysedge.com 2020 (4040 TLS)\r\n\r\n\t Y O U H A V E R E A C H E D T H E E D G E \r\n\r\n \r\n |\\\\\\\\\\\\\\\\\\ |\\\\\\\\\\\\ |\\\\ |\\\\|\\\\\\\\\\\\ |\\\\\\\\\\\\ |\\\\ |\\\\ |\\\\ \\\\\\\\\\\\\\\\\\\r\n \\\\ | \\\\ \\\\ \\\\\\\\ \\\\ |\\\\ |\\\\ \\\\ \\\\ || \\\\\r\n \\\\\\\\\\\\\\\\\\\\\\ |\\\\\\\\\\\\ \\\\ \\\\ \\\\ \\\\ \\\\ \\\\\\\\\\\\ \\\\\\\\\\\\\\\\\\\r\n | |\\\\ \\\\ \\\\ \\\\ \\\\\\\\ \\\\ \\\\ | |\\\\ | |\\\\\r\n \\\\\\\\\\\\\\\\\\\\ \\\\ \\\\ \\\\ \\\\\\ \\\\\\\\\\\\\\ \\\\ \\\\ \\\\\\\\\\\\\\\\\\\r\n | | || || || | | | | || || | |\r\n\r\n //////////| //////| /////| /////////|\r\n //| //| //| //| //| |\r\n ///////| // // // /////| //////| \r\n //| // // // //| //| |\r\n ////////// /////// | /////// //////////|\r\n | | | | | | | |\r\n\r\n\t\t\tS A N I T Y ' S E D G E\r\n\r\n\r\nGamedriver version:\tCD.06.06 Sep 13 2020 23:03:50\r\nMudlib version:\t\tCD.00.30-h4xed by CMD\r\n\r\nPlease enter your name: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CLASSES": "0",
"CODEBASE": "CD",
"CRAWL DELAY": "-1",
"CREATED": "1995",
"FAMILY": "LPMud",
"GAMEPLAY": "Hack and Slash",
"GAMESYSTEM": "None",
"GENRE": "Science Fiction",
"GMCP": "1",
"HIRING BUILDERS": "0",
"HIRING CODERS": "0",
"HOSTNAME": "sanitysedge.com",
"LANGUAGE": "English",
"LEVELS": "0",
"LOCATION": "United States of America",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "18",
"MSDP": "0",
"MSP": "0",
"MXP": "0",
"NAME": "Sanity's Edge",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYERS": "6",
"PORT": "2020",
"PUEBLO": "0",
"RACES": "1",
"SKILLS": "34",
"SUBGENRE": "Cyberpunk",
"UPTIME": "1775118128",
"UTF-8": "0",
"XTERM 256 COLORS": "1",
"XTERM TRUE COLORS": "0"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.10142898559570312,
"total": 10.672399997711182
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:33.564574+00:00",
"host": "sanitysedge.com",
"ip": "35.171.219.224",
"port": 2020
},
{
"connected": "2026-04-07T07:00:21.545958+00:00",
"host": "sanitysedge.com",
"ip": "35.171.219.224",
"port": 2020
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug sanitysedge.com 2020
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=sanitysedge.com port=2020
INFO client_base.py:190 Connected to <Peer 35.171.219.224 2020>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'CODEBASE': 'CD', 'UTF-8': '0', 'MSDP': '0', 'ANSI': '1', 'GMCP': '1', 'LEVELS': '0',
'GAMESYSTEM': 'None', 'GAMEPLAY': 'Hack and Slash', 'CREATED': '1995', 'PAY FOR PERKS': '0', 'MSP': '0', 'XTERM 256 COLORS':
'1', 'SUBGENRE': 'Cyberpunk', 'MCCP': '0', 'FAMILY': 'LPMud', 'LANGUAGE': 'English', 'UPTIME': '1775118128', 'RACES': '1',
'GENRE': 'Science Fiction', 'PLAYERS': '6', 'HIRING BUILDERS': '0', 'PAY TO PLAY': '0', 'MCP': '0', 'NAME': "Sanity's Edge",
'CRAWL DELAY': '-1', 'PUEBLO': '0', 'MXP': '0', 'SKILLS': '34', 'CLASSES': '0', 'MINIMUM AGE': '18', 'HIRING CODERS': '0',
'XTERM TRUE COLORS': '0', 'LOCATION': 'United States of America', 'HOSTNAME': 'sanitysedge.com', 'PORT': '2020'}
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG client_base.py:531 negotiation complete after 0.14s.
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG _base.py:78 Invalid telnet byte: Illegal option follows IAC SB CHARSET: b';'.
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint fc3ff80640fda031
INFO client_base.py:122 Connection closed to <Peer 35.171.219.224 2020>