136.144.155.250
136.144.155.250:8888
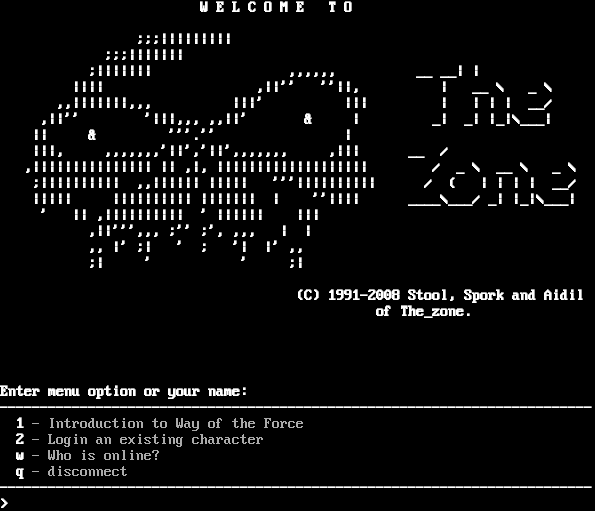
Connection Banner:
Server URLs
- Telnet: telnet://136.144.155.250:8888
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: SGA
Options requested from client: LINEMODE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "67c4982951f1d2c9",
"fingerprint-data": {
"offered-options": [
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"LINEMODE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[2J\r\n\u001b[1;1H\u001b[1m\u001b[1m\u001b[33m\u001b[0m\r\n\u001b[1m W E L C O M E T O\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m ;;;|||||||||\u001b[0m\r\n\u001b[1m ;;;|||||||\u001b[0m\r\n\u001b[1m ;||||||| ,,,,,, __ __| |\u001b[0m\r\n\u001b[1m |||| ,||'' ''||, | __ \\ _ \\\u001b[0m\r\n\u001b[1m ,,|||||||,,, |||' ||| | | | | __/\u001b[0m\r\n\u001b[1m ,||'' '|||,,, ,,||' & | _| _| |_|\\___|\u001b[0m\r\n\u001b[1m || & '''.'' |\u001b[0m\r\n\u001b[1m |||, ,,,,,,,'||','||',,,,,,, ,||| __ /\u001b[0m\r\n\u001b[1m ,||||||||||||||| || ,|, ||||||||||||||||||| / _ \\ __ \\ _ \\ \u001b[0m\r\n\u001b[1m ;|||||||||| ,,|||||| ||||| '''|||||||||| / ( | | | | __/\u001b[0m\r\n\u001b[1m ||||| |||||||||| ||||||| | ''|||| ____\\___/ _| |_|\\___|\u001b[0m\r\n\u001b[1m ' || ,|||||||||| ' |||||| |||\u001b[0m\r\n\u001b[1m ,||''',,, ;'' ;', ,,, | |\u001b[0m\r\n\u001b[1m ,, |' ;| ' ; '| |' ,,\u001b[0m\r\n\u001b[1m ;| ' ' ;|\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m (C) 1991-2008 Stool, Spork and Aidil\u001b[0m\r\n\u001b[1m of The_zone.\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m\u001b[0m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mEnter menu option or your name:\u001b[0m\r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[1m 1\u001b[0m - Introduction to Way of the Force \r\n\u001b[1m 2\u001b[0m - Login an existing character \r\n\u001b[1m w\u001b[0m - Who is online? \r\n\u001b[1m q\u001b[0m - disconnect \r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[0m\u001b[1m> \u001b[0m",
"banner_before_return": "\u001b[2J\r\n\u001b[1;1H\u001b[1;1H\u001b[1mDGD 1.4.1 / WOTF Kernel 0.84\u001b[0m\r\n\r\n\r\n\u001b[2J\r\n\u001b[1;1H\u001b[1m\u001b[1m\u001b[33m\u001b[0m\r\n\u001b[1m W E L C O M E T O\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m ;;;|||||||||\u001b[0m\r\n\u001b[1m ;;;|||||||\u001b[0m\r\n\u001b[1m ;||||||| ,,,,,, __ __| |\u001b[0m\r\n\u001b[1m |||| ,||'' ''||, | __ \\ _ \\\u001b[0m\r\n\u001b[1m ,,|||||||,,, |||' ||| | | | | __/\u001b[0m\r\n\u001b[1m ,||'' '|||,,, ,,||' & | _| _| |_|\\___|\u001b[0m\r\n\u001b[1m || & '''.'' |\u001b[0m\r\n\u001b[1m |||, ,,,,,,,'||','||',,,,,,, ,||| __ /\u001b[0m\r\n\u001b[1m ,||||||||||||||| || ,|, ||||||||||||||||||| / _ \\ __ \\ _ \\ \u001b[0m\r\n\u001b[1m ;|||||||||| ,,|||||| ||||| '''|||||||||| / ( | | | | __/\u001b[0m\r\n\u001b[1m ||||| |||||||||| ||||||| | ''|||| ____\\___/ _| |_|\\___|\u001b[0m\r\n\u001b[1m ' || ,|||||||||| ' |||||| |||\u001b[0m\r\n\u001b[1m ,||''',,, ;'' ;', ,,, | |\u001b[0m\r\n\u001b[1m ,, |' ;| ' ; '| |' ,,\u001b[0m\r\n\u001b[1m ;| ' ' ;|\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m (C) 1991-2008 Stool, Spork and Aidil\u001b[0m\r\n\u001b[1m of The_zone.\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m\u001b[0m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mEnter menu option or your name:\u001b[0m\r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[1m 1\u001b[0m - Introduction to Way of the Force \r\n\u001b[1m 2\u001b[0m - Login an existing character \r\n\u001b[1m w\u001b[0m - Who is online? \r\n\u001b[1m q\u001b[0m - disconnect \r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[0m\u001b[1m> \u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "cp437",
"option_states": {
"server_offered": {
"ECHO": false
},
"server_requested": {
"LINEMODE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.503756046295166,
"total": 11.16801643371582
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:20:10.758580+00:00",
"host": "136.144.155.250",
"ip": "136.144.155.250",
"port": 8888
},
{
"connected": "2026-04-05T19:27:55.864139+00:00",
"host": "136.144.155.250",
"ip": "136.144.155.250",
"port": 8888
},
{
"connected": "2026-04-07T06:56:26.959430+00:00",
"host": "136.144.155.250",
"ip": "136.144.155.250",
"port": 8888
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 136.144.155.250 8888
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=136.144.155.250 port=8888
INFO client_base.py:190 Connected to <Peer 136.144.155.250 8888>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x01' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False,
remote:False, local:True> IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL ZMP, WILL AARDWOLF, WILL MSSP, WILL MCCP3_COMPRESS, WILL MSP, WILL MSDP, WILL MXP,
WILL ATCP, WILL GMCP, WILL MCCP2_COMPRESS, DO ZMP, DO AARDWOLF, DO MSSP, DO MCCP3_COMPRESS, DO MSP, DO MSDP, DO MXP, DO ATCP,
DO GMCP, DO MCCP2_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 67c4982951f1d2c9
INFO client_base.py:122 Connection closed to <Peer 136.144.155.250 8888>
lpcdb.themuds.org:4000
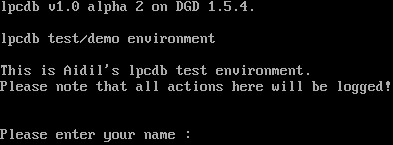
Connection Banner:
Server URLs
- Telnet: telnet://lpcdb.themuds.org:4000
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: SGA
Options requested from client: LINEMODE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "67c4982951f1d2c9",
"fingerprint-data": {
"offered-options": [
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"LINEMODE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\r\nPlease enter your name : ",
"banner_before_return": "lpcdb v1.0 alpha 2 on DGD 1.5.4.\r\n\r\nlpcdb test/demo environment\r\n\r\nThis is Aidil's lpcdb test environment.\r\nPlease note that all actions here will be logged!\r\n\r\n\r\r\nPlease enter your name : ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": false
},
"server_requested": {
"LINEMODE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5050718784332275,
"total": 11.160111427307129
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:02:13.341622+00:00",
"host": "lpcdb.themuds.org",
"ip": "136.144.155.250",
"port": 4000
},
{
"connected": "2026-04-07T07:02:19.187591+00:00",
"host": "lpcdb.themuds.org",
"ip": "136.144.155.250",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug lpcdb.themuds.org 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=lpcdb.themuds.org port=4000
INFO client_base.py:190 Connected to <Peer 136.144.155.250 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x01' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False,
remote:False, local:True> IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL ZMP, WILL ATCP, WILL MSDP, WILL GMCP, WILL MCCP3_COMPRESS, WILL MSP, WILL
MCCP2_COMPRESS, WILL MXP, WILL AARDWOLF, DO MSSP, DO ZMP, DO ATCP, DO MSDP, DO GMCP, DO MCCP3_COMPRESS, DO MSP, DO
MCCP2_COMPRESS, DO MXP, DO AARDWOLF'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 67c4982951f1d2c9
INFO client_base.py:122 Connection closed to <Peer 136.144.155.250 4000>
wotf.org:23
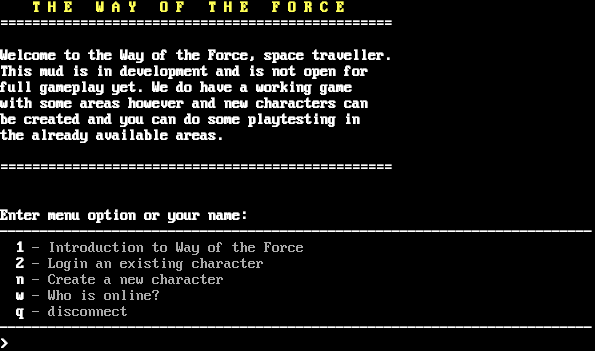
Connection Banner:
Server URLs
- Telnet: telnet://wotf.org
Server Info
Server Location: 🇳🇱 Netherlands (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: SGA
Options requested from client: LINEMODE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "67c4982951f1d2c9",
"fingerprint-data": {
"offered-options": [
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"LINEMODE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[2J\r\n\u001b[1;1H\u001b[1m\u001b[1m\u001b[33m T H E W A Y O F T H E F O R C E\u001b[0m\r\n\u001b[1m=================================================\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mWelcome to the Way of the Force, space traveller.\u001b[0m\r\n\u001b[1mThis mud is in development and is not open for\u001b[0m\r\n\u001b[1mfull gameplay yet. We do have a working game \u001b[0m\r\n\u001b[1mwith some areas however and new characters can \u001b[0m\r\n\u001b[1mbe created and you can do some playtesting in \u001b[0m\r\n\u001b[1mthe already available areas. \u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m=================================================\u001b[0m\r\n\u001b[1m\u001b[0m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mEnter menu option or your name:\u001b[0m\r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[1m 1\u001b[0m - Introduction to Way of the Force \r\n\u001b[1m 2\u001b[0m - Login an existing character \r\n\u001b[1m n\u001b[0m - Create a new character \r\n\u001b[1m w\u001b[0m - Who is online? \r\n\u001b[1m q\u001b[0m - disconnect \r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[0m\u001b[1m> \u001b[0m",
"banner_before_return": "\u001b[2J\r\n\u001b[1;1H\u001b[1;1H\u001b[1mDGD 1.2.157-WOTF-NET / WOTF Kernel 0.84\u001b[0m\r\n\r\n\r\n\u001b[2J\r\n\u001b[1;1H\u001b[1m\u001b[1m\u001b[33m T H E W A Y O F T H E F O R C E\u001b[0m\r\n\u001b[1m=================================================\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mWelcome to the Way of the Force, space traveller.\u001b[0m\r\n\u001b[1mThis mud is in development and is not open for\u001b[0m\r\n\u001b[1mfull gameplay yet. We do have a working game \u001b[0m\r\n\u001b[1mwith some areas however and new characters can \u001b[0m\r\n\u001b[1mbe created and you can do some playtesting in \u001b[0m\r\n\u001b[1mthe already available areas. \u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1m=================================================\u001b[0m\r\n\u001b[1m\u001b[0m\u001b[0m\r\n\u001b[1m\u001b[0m\r\n\u001b[1mEnter menu option or your name:\u001b[0m\r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[1m 1\u001b[0m - Introduction to Way of the Force \r\n\u001b[1m 2\u001b[0m - Login an existing character \r\n\u001b[1m n\u001b[0m - Create a new character \r\n\u001b[1m w\u001b[0m - Who is online? \r\n\u001b[1m q\u001b[0m - disconnect \r\n\u001b[1m--------------------------------------------------------------------------\u001b[0m\r\n\u001b[0m\u001b[1m> \u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": false
},
"server_requested": {
"LINEMODE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5048668384552002,
"total": 11.17320203781128
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:37.261467+00:00",
"host": "wotf.org",
"ip": "136.144.155.250",
"port": 23
},
{
"connected": "2026-04-07T07:24:12.739126+00:00",
"host": "wotf.org",
"ip": "136.144.155.250",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug wotf.org 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=wotf.org port=23
INFO client_base.py:190 Connected to <Peer 136.144.155.250 23>
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x01' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x05': lit_echo:False, soft_tab:False, ack:True, trapsig:False,
remote:False, local:True> IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL ATCP, WILL MSP, WILL MXP, WILL MSDP, WILL MSSP, WILL MCCP3_COMPRESS, WILL ZMP, WILL
AARDWOLF, WILL MCCP2_COMPRESS, WILL GMCP, DO ATCP, DO MSP, DO MXP, DO MSDP, DO MSSP, DO MCCP3_COMPRESS, DO ZMP, DO AARDWOLF,
DO MCCP2_COMPRESS, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 67c4982951f1d2c9
INFO client_base.py:122 Connection closed to <Peer 136.144.155.250 23>