176.9.151.147 (ancientmists.vineyard.haus)
176.9.151.147:1111
Connection Banner:
![\|----------------------------------------------\| \| . . \| \| . _ \|______ _ .--------------------/\\--\| \|_-----------------(_______)----------------.\| \| \| / \\ \| \| \|_ ____ ____ _____ ____ ___ ____\| \| _ \| / /\\ \\\| \| _)/ _ )/ ___) \| ___) \| _ \\ / _ \\ / ___) \|\| \\ \| \| \|__\| \| \| \|_( (/ /\| \| \| \|_____\| \| \| \| \|_\| ( (___\| \|\\\| \| \| \|______\|_\|\\___)____)_\| \|_______) \|\|_/ \\___/ \\____)_\| \|_\| \| . \|_\| REBOOT \\ .------------------------\|--------------------.-------------------------------' \| . .' '. \| Based on InqMUTT(ti-legacy.com) \| ,-----. . \| which was based on DikuMUD, ROM \| . : ' ' ' : \| 2.4b and Merc 2.1. Please check \| : ' ' ' : . \| HELP CREDITS in-game for a full \| . : ' ' ' : \| account of code contributions. \| :--' ' '--: \| \| \|' ' ' ' \| . \| ACCESS CURATION: \| ------. \|' ' ' ' \| \| \| . : ' ' : \|' ' ' ' \| . \| We are a whitelist-only \| \| : ' ' : \|' ' ' ' \| \| \| game. An invitation from \| .-. : ' ' : \|' ' ' ' \| ,---. \| an existing player or \| : ' :---' '--- \|' ' ' ' \| : ' : \| Staff member is required \| .:-'-:.' ' ' \| \|' ' ' ' \| \|--'--\| \| to access Alter Epoch. \| \|' ' \|' ' ' \| \|' ' ' ' \| \|' ' \| \| \| \|' ' \|' ' ' \| \|' ' ' \|--------\| \|' ' \| \| Enter your existing, whitelisted \| \|' ' \|' ' ' \| \|' ' ' \|' ' ' ' \| \|' ' \| \| account name to access character \| \|' ' \|' ' ' \| ;' ' ' \|' ' ' ' \| \|' ' \| \| generation and/or log-in. \| -'----\|--'----\|--\|---'---\|---.------\|--'--- \| What is your account name? [Enter your whitelisted account] Account names are three characters at a minimum. Please try again? >](../_images/banner_d96cfcfd57de.png)
Server URLs
- Telnet: telnet://176.9.151.147:1111
- Website: ti-legacy.com
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: Negotiated
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: ECHO, GMCP, MSDP, MSP, MXP
Options requested from client: CHARSET, MXP, NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c75b6aeeae7b041b",
"fingerprint-data": {
"offered-options": [
"ECHO",
"GMCP",
"MSDP",
"MSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"CHARSET",
"MXP",
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Account names are three characters at a minimum. Please try again?\n\r > ",
"banner_before_return": "\u001b[49;22;36m|----------------------------------------------|\u001b[49;22;37m\n\r\u001b[49;22;36m|\u001b[49;1;36m . .\u001b[49;22;37m \u001b[49;22;36m|\u001b[49;22;37m\n\r\u001b[49;22;36m|\u001b[49;1;36m . \u001b[49;22;37m_ \u001b[49;22;36m|\u001b[49;1;37m______ _\u001b[49;22;37m\n\r\u001b[49;22;31m.--------------------\u001b[49;1;37m/\\\u001b[49;22;31m--\u001b[49;1;37m| |_\u001b[49;22;31m-----------------\u001b[49;1;37m(_______)\u001b[49;22;31m----------------.\u001b[49;1;37m| |\u001b[49;22;37m\n\r\u001b[49;22;31m| \u001b[49;1;37m/ \\ | | |_ ____ ____ _____ ____ ___ ____| | _\n\r\u001b[49;22;31m| \u001b[49;1;37m/ /\\ \\| | _)/ _ )/ ___) | ___) | _ \\ / _ \\ / ___) || \\ \n\r\u001b[49;22;31m| \u001b[49;1;37m| |__| | | |_( (/ /| | | |_____| | | | |_| ( (___| |\u001b[49;22;31m\\\u001b[49;22;37m| |\n\r\u001b[49;22;31m| \u001b[49;1;37m|______|_|\\___)____)_| |_______) ||_/ \\___/ \\____)_| |_|\n\r\u001b[49;22;31m|\u001b[49;22;37m . \u001b[49;1;37m|_|\u001b[49;1;31m REBOOT \u001b[49;22;31m\\\u001b[0;37m\n\r\u001b[49;22;31m.------------------------\u001b[49;22;37m|\u001b[49;22;31m--------------------.-------------------------------'\u001b[49;22;37m\n\r\u001b[49;22;36m| \u001b[49;1;36m.\u001b[49;22;37m .' '. \u001b[49;22;36m|\u001b[49;22;37m Based on InqMUTT(\u001b[49;22;36mti-legacy.com\u001b[49;22;37m)\n\r\u001b[49;22;36m|\u001b[49;22;37m ,-----. \u001b[49;1;36m. \u001b[49;22;36m|\u001b[49;22;37m which was based on DikuMUD, ROM\n\r\u001b[49;22;36m| \u001b[49;1;36m.\u001b[49;22;37m : \u001b[49;1;37m' \u001b[49;22;37m' \u001b[49;1;30m'\u001b[49;22;37m : \u001b[49;22;36m|\u001b[49;22;37m 2.4b and Merc 2.1. Please check\n\r\u001b[49;22;36m|\u001b[49;22;37m : ' \u001b[49;1;37m' \u001b[49;22;37m' : \u001b[49;1;36m. \u001b[49;22;36m|\u001b[49;22;37m \u001b[49;22;36mHELP CREDITS\u001b[49;22;37m in-game for a full\n\r\u001b[49;22;36m| \u001b[49;1;36m.\u001b[49;22;37m : \u001b[49;1;30m' \u001b[49;22;37m' \u001b[49;1;37m'\u001b[49;22;37m : \u001b[49;22;36m|\u001b[49;22;37m account of code contributions.\n\r\u001b[49;22;36m|\u001b[49;22;37m :--' \u001b[49;1;30m' \u001b[49;22;37m'--: \u001b[49;22;36m|\u001b[49;22;37m\n\r\u001b[49;22;36m|\u001b[49;22;37m |' ' ' \u001b[49;1;30m'\u001b[49;22;37m |\u001b[49;1;36m . \u001b[49;22;36m|\u001b[49;1;37m ACCESS CURATION:\u001b[0;37m\n\r\u001b[49;22;36m|\u001b[49;22;37m ------. |' \u001b[49;1;30m'\u001b[49;22;37m ' ' |\u001b[49;22;36m |\u001b[0;37m \n\r\u001b[49;22;36m| \u001b[49;1;37m.\u001b[49;22;37m : ' \u001b[49;1;30m'\u001b[49;22;37m : |' \u001b[49;1;30m' \u001b[49;22;37m' ' | \u001b[49;1;37m. \u001b[49;22;36m|\u001b[0;37m We are a \u001b[49;1;37mwhitelist\u001b[0;37m-only\n\r\u001b[49;22;36m|\u001b[0;37m | : \u001b[49;1;30m'\u001b[0;37m ' : |' ' ' \u001b[49;1;30m'\u001b[0;37m | \u001b[49;22;36m| |\u001b[0;37m game. An invitation from\n\r\u001b[49;22;36m|\u001b[0;37m .-. : ' ' : |\u001b[49;1;30m' \u001b[0;37m' ' ' | ,---. \u001b[49;22;36m|\u001b[0;37m an existing player or\n\r\u001b[49;22;36m|\u001b[0;37m : ' :---' '--- |' \u001b[49;1;30m' \u001b[0;37m' ' | : ' : \u001b[49;22;36m|\u001b[0;37m Staff member is required\n\r\u001b[49;22;36m|\u001b[0;37m .:-'-:.' ' \u001b[49;1;30m' \u001b[0;37m| |' ' \u001b[49;1;30m'\u001b[0;37m ' | |--'--| \u001b[49;22;36m|\u001b[0;37m to access Alter Epoch.\n\r\u001b[49;22;36m|\u001b[0;37m |' ' |' ' ' | |' ' ' ' | |' ' | \u001b[49;22;36m|\u001b[0;37m \n\r\u001b[49;22;36m|\u001b[0;37m |' ' |' ' ' | |' ' ' |--------| |' ' | \u001b[49;22;36m|\u001b[0;37m Enter your existing, whitelisted\n\r\u001b[49;22;36m|\u001b[0;37m |' ' |' ' ' | |' ' ' |' ' ' ' | |' ' | \u001b[49;22;36m|\u001b[0;37m account name to access character\n\r\u001b[49;22;36m|\u001b[0;37m |' ' |' ' ' | ;' ' ' |' ' ' ' | |' ' | \u001b[49;22;36m|\u001b[0;37m generation and/or log-in.\n\r\u001b[49;22;36m| -\u001b[49;22;32m'\u001b[49;22;36m----\u001b[49;22;37m|\u001b[49;22;36m--\u001b[49;22;32m'\u001b[49;22;36m----\u001b[49;22;37m|\u001b[49;22;36m--\u001b[49;22;37m|\u001b[49;22;36m---\u001b[49;22;32m'\u001b[49;22;36m---\u001b[49;22;37m|\u001b[49;22;36m---\u001b[49;22;32m.\u001b[49;22;36m------\u001b[49;22;37m|\u001b[49;22;36m--\u001b[49;22;32m'\u001b[49;22;36m--- |\u001b[49;22;37m \n\r\n\rWhat is your account name? \u001b[49;22;36m[Enter your whitelisted account]\u001b[0;37m\n\r\u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"GMCP": true,
"MSDP": true,
"MSP": true
},
"server_requested": {
"CHARSET": true,
"MXP": true,
"NAWS": true,
"SGA": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5098328590393066,
"total": 5.721675872802734
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:11:23.583835+00:00",
"host": "176.9.151.147",
"ip": "176.9.151.147",
"port": 1111
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 176.9.151.147 1111
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=176.9.151.147 port=1111
ERROR client.py:1318 176.9.151.147:1111: [Errno 111] Connect call failed ('176.9.151.147', 1111)
ancientmists.vineyard.haus:1119
Connection Banner:
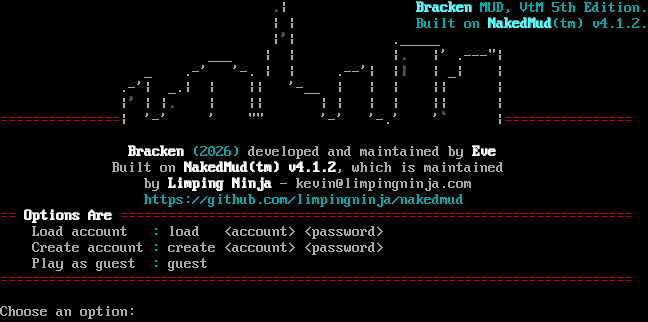
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:1119
- Website: limpingninja.com
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 13 other servers.
Options offered by server: MCCP2
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "886e1f8cbdfbe41f",
"fingerprint-data": {
"offered-options": [
"MCCP2"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Choose an option: ",
"banner_before_return": "\r\n\u001b[0;0m\n \u001b[1;30m.\u001b[0;0m| \u001b[1;36mBracken\u001b[0;36m MUD, VtM 5th Edition.\u001b[0;0m\n | | \u001b[0;36mBuilt on \u001b[1;36mNakedMud\u001b[0;36m(tm) v4.1.2.\u001b[0;0m\n |\u001b[1;30m'\u001b[0;0m| ._____\n ___ | | |\u001b[1;30m.\u001b[0;0m |' .---\"|\n _ .-' '-. | | .--'| |\u001b[1;30m|\u001b[0;0m | _| |\n .-'| _.| | || '-__ | | | || |\n |\u001b[1;30m'\u001b[0;0m | |\u001b[1;30m.\u001b[0;0m | || | | | | || |\n\u001b[0;31m===============\u001b[0;0m| '-' ' \"\" '-' '-.' '\u001b[1;30m`\u001b[0;0m |\u001b[0;31m================\u001b[0;0m\n\n \u001b[1;37mBracken\u001b[0;36m (2026)\u001b[0;0m developed and maintained by \u001b[1;37mEve\u001b[0;0m\n Built on \u001b[1;37mNakedMud(tm) v4.1.2\u001b[0;0m, which is maintained\n by \u001b[1;37mLimping Ninja\u001b[0;0m - kevin@limpingninja.com\n \u001b[0;36mhttps://github.com/limpingninja/nakedmud\u001b[0;0m\r\n\u001b[0;31m==\u001b[1;37m Options Are \u001b[0;31m================================================================\u001b[0;0m\r\n Load account \u001b[0;36m:\u001b[0;0m load <account> <password>\r\n Create account \u001b[0;36m:\u001b[0;0m create <account> <password>\r\n Play as guest \u001b[0;36m:\u001b[0;0m guest\r\n\u001b[0;31m===============================================================================\u001b[0;0m\r\n\r\nChoose an option: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5088670253753662,
"total": 11.205580472946167
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:35:52.495716+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1119
},
{
"connected": "2026-04-07T07:21:03.703289+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1119
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 1119
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=1119
INFO client_base.py:190 Connected to <Peer 176.9.151.147 1119>
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG client_base.py:534 negotiation failed after 4.01s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL AARDWOLF, WILL MSP, WILL MCCP2_COMPRESS, WILL ATCP, WILL MXP, WILL
MCCP3_COMPRESS, WILL ZMP, WILL GMCP, WILL MSDP, DO MSSP, DO AARDWOLF, DO MSP, DO ATCP, DO MXP, DO MCCP3_COMPRESS, DO ZMP, DO
GMCP, DO MSDP'
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 886e1f8cbdfbe41f
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 1119>
ancientmists.vineyard.haus:1538
Connection Banner:
![Welcome to the Ancient Mists.... Do you want ANSI color? [Y/N] Ansi disabled! / \\ _ Ancient Mists ) (( )) ( ROM 2.4 (c)1993/96 _ (O) 2002 raxx@comcast.net /\|\\ ))_(( /\|\\ Russ Taylor (O) \|-\|\\ / \| \\ (/\\\|/\\) / \| \\ /\|-\| \| \|-----------------------/--\|-voV---\\\`\|'/--Vov-\|--\\----------------------\| \| \| \| '^\` (o o) '^\` \| \| \|-\| \`\\Y/' \|-\| \| \| BB BB BB BB BBB BB B \| \| \| \| BBB BB BB BBBB BBBB BB BB \| \| \| \| BBB BB BBB BBBB BB \| \| \|-\| B BB BBB BBB BB BBB BBBBB BBBB B B B BB BB BBB BBBB BBB \|-\| \| \| B BB BBBB BBBBB BB BB BB BBBBB BBBB B B B BB BB BB BB BBB BBBB \| \| \| \| BB BB BB B BB BB BB BB B BB B BB B B B BB BB BB BB B B \| \| \|-\| BB BB BB B BB B BB BB BB BB B BB B B B BB BB BBB BB BB \|-\| \| \| BB BB BB B BB BB BBBBB BB B BB B BBB BB BB BBBB BB BBBB \| \| \| \| BBBBBB BB B BB BB BB BB BB B BB B B BB BB BBB BB BB \| \| \| \| B BB BB B BB BB BB BB BB BB B BB B B BB BB B BB BB B B \| \| \|-\| B BB BB B BBBBB BB BB BB BB B BBB B B BB BB BB BB BBB BBBB \|-\| \| \| B BB BB B BBB BB BBB BB B BB B B BB BB BBB BB BBB \| \| \| \|-----------------------------------------------------------------------\| \| \|-\|/ l /\\ / ( ( \\ /\\ l \\\|-\| (O) l / V \\ \\ V \\ l (O) l/ _) )_ \\I \`\\ /' V Based on MERC 2.1 Code by Hatchet, Furey, and Kahn Original DikuMUD by Hans StaerFeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer Type your name to enter:](../_images/banner_ea9cc99c9251.png)
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:1538
- Website: comcast.net
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Ansi disabled!\n\r\r\n / \\ \r\n _ Ancient Mists ) (( )) ( ROM 2.4 (c)1993/96 _ \r\n (O) 2002 raxx@comcast.net /|\\ ))_(( /|\\ Russ Taylor (O)\r\n |-|\\ / | \\ (/\\|/\\) / | \\ /|-|\r\n | |-----------------------/--|-voV---\\`|'/--Vov-|--\\----------------------| |\r\n | | '^` (o o) '^` | |\r\n |-| `\\Y/' |-|\r\n | | BB BB BB BB BBB BB B | |\r\n | | BBB BB BB BBBB BBBB BB BB | |\r\n | | BBB BB BBB BBBB BB | |\r\n |-| B BB BBB BBB BB BBB BBBBB BBBB B B B BB BB BBB BBBB BBB |-|\r\n | | B BB BBBB BBBBB BB BB BB BBBBB BBBB B B B BB BB BB BB BBB BBBB | |\r\n | | BB BB BB B BB BB BB BB B BB B BB B B B BB BB BB BB B B | |\r\n |-| BB BB BB B BB B BB BB BB BB B BB B B B BB BB BBB BB BB |-|\r\n | | BB BB BB B BB BB BBBBB BB B BB B BBB BB BB BBBB BB BBBB | |\r\n | | BBBBBB BB B BB BB BB BB BB B BB B B BB BB BBB BB BB | |\r\n | | B BB BB B BB BB BB BB BB BB B BB B B BB BB B BB BB B B | |\r\n |-| B BB BB B BBBBB BB BB BB BB B BBB B B BB BB BB BB BBB BBBB |-|\r\n | | B BB BB B BBB BB BBB BB B BB B B BB BB BBB BB BBB | |\r\n | |-----------------------------------------------------------------------| |\r\n |-|/ l /\\ / ( ( \\ /\\ l \\|-|\r\n (O) l / V \\ \\ V \\ l (O)\r\n l/ _) )_ \\I \r\n `\\ /' \r\n V \r\n Based on MERC 2.1 Code by Hatchet, Furey, and Kahn \r\n Original DikuMUD by Hans StaerFeldt, Katja Nyboe, \r\n Tom Madsen, Michael Seifert, and Sebastian Hammer \r\n\r\nType your name to enter: \u001b[0;37m",
"banner_before_return": "\n\r\n\rWelcome to the Ancient Mists....\n\r\n\rDo you want ANSI color? [Y/N] ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 11.328644514083862
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:24:14.759276+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1538
},
{
"connected": "2026-04-05T19:08:40.773729+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1538
},
{
"connected": "2026-04-07T06:53:03.814437+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1538
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 1538
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=1538
INFO client_base.py:190 Connected to <Peer 176.9.151.147 1538>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MXP, WILL ATCP, WILL GMCP, WILL MSDP, WILL MSP, WILL ZMP, WILL MCCP3_COMPRESS, WILL
MCCP2_COMPRESS, WILL MSSP, WILL AARDWOLF, DO MXP, DO ATCP, DO GMCP, DO MSDP, DO MSP, DO ZMP, DO MCCP3_COMPRESS, DO
MCCP2_COMPRESS, DO MSSP, DO AARDWOLF'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 1538>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
TOS TrekMUSH (ancientmists.vineyard.haus:1701)
Connection Banner:
![------------------------------------------------------------------------------ TOS TrekMUSH: _\|_\|_ A text RPG based upon ^/ . ..\\^ the Original Paramount ___[=========]___ TV Series, Movies, and ___-==++"'" . /. . . \\ . "'"++==-___ Books. __-+"" __\\ .. . . \| .. . \| . . . /__ ""+-__ /\\__+-"" \`-----=====\\_ <O> _/=====-----' ""-+__/\\ _/_/ ""="" \\_\\_ /_/ \\_\\ // \| \\\\ /") \\ \| / ("\\ \\o\\ \\\*/ /o/ \\_) --\*\*O\*\*-- (_/ /\*\\ / \| \\ \| (StarTrek, and all related works are Copyright Paramount Pictures.) ------------------------------------------------------------------------------ Use \`create <name> <password>\` to create a character. Use \`connect <name> <password>\` to connect to your existing character. Use \`connect guest\` to connect as guest and look around Use QUIT to logout. Use the WHO command to find out who is online currently. -----------------------------------------------------------------------------](../_images/banner_11d6e84411af.png)
Server URLs
Server Info
Codebase: PennMUSH 1.8.8p0
Players online: 0 [1]
Uptime: 8 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "------------------------------------------------------------------------------\r\n TOS TrekMUSH:\r\n _|_|_ A text RPG based upon\r\n ^/ . ..\\^ the Original Paramount\r\n ___[=========]___ TV Series, Movies, and\r\n ___-==++\"'\" . /. . . \\ . \"'\"++==-___ Books.\r\n\r\n __-+\"\" __\\ .. . . | .. . | . . . /__ \"\"+-__\r\n /\\__+-\"\" `-----=====\\_ <O> _/=====-----' \"\"-+__/\\\r\n _/_/ \"\"=\"\" \\_\\_\r\n /_/ \\_\\\r\n // | \\\\\r\n /\") \\ | / (\"\\\r\n \\o\\ \\*/ /o/\r\n \\_) --**O**-- (_/\r\n /*\\\r\n / | \\\r\n |\r\n (StarTrek, and all related works are Copyright Paramount Pictures.)\r\n------------------------------------------------------------------------------\r\nUse `create <name> <password>` to create a character.\r\nUse `connect <name> <password>` to connect to your existing character.\r\nUse `connect guest` to connect as guest and look around\r\nUse QUIT to logout.\r\nUse the WHO command to find out who is online currently.\r\n-----------------------------------------------------------------------------\r\n\r\n\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.8p0",
"FAMILY": "TinyMUD",
"NAME": "TOS TrekMUSH",
"PLAYERS": "0",
"PORT": "1701",
"PUEBLO": "0",
"UPTIME": "1774815471",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.4057600498199463,
"total": 10.917871713638306
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:51:52.965043+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1701
},
{
"connected": "2026-04-07T06:46:49.117312+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 1701
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 1701
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=1701
INFO client_base.py:190 Connected to <Peer 176.9.151.147 1701>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'TOS TrekMUSH', 'PLAYERS': '0', 'UPTIME': '1774815471', 'PORT': '1701', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'TOS TrekMUSH', 'PLAYERS': '0', 'UPTIME': '1774815471', 'PORT': '1701', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, WILL MSSP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint f96aa48abbc42633
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 1701>
ancientmists.vineyard.haus:2024
Connection Banner:
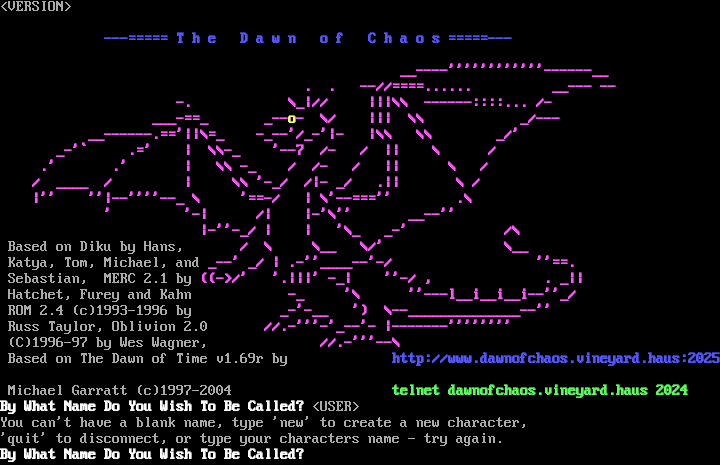
Server URLs
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 5 other servers.
Options offered by server: MCCP2, MSP, MXP
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9e7fd90d3aff78af",
"fingerprint-data": {
"offered-options": [
"MCCP2",
"MSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "You can't have a blank name, type 'new' to create a new character,\r\n'quit' to disconnect, or type your characters name - try again.\r\n\u001b[1;37mBy What Name Do You Wish To Be Called?\u001b[0;37m ",
"banner_before_return": "\u001b[1z<VERSION>\u001b[6z\r\n\r\n\u001b[1;34m ---===== T h e D a w n o f C h a o s =====--- \u001b[0;37m\n\r\u001b[1;35m \u001b[0;37m\n\r\u001b[1;35m __----''''''''''''------__ \u001b[0;37m\n\r\u001b[1;35m . . --//====...... __--- --\u001b[0;37m\n\r\u001b[1;35m -. \\_|// |||\\\\ ------::::... /- \u001b[0;37m\n\r\u001b[1;35m ___-==_ _--\u001b[1;33mo\u001b[1;35m- \\/ ||| \\\\ _/--- \u001b[0;37m\n\r\u001b[1;35m __------.=='||\\=_ -_--'/_-'|- |\\\\ \\\\ _/' \u001b[0;37m\n\r\u001b[1;35m _-'` .=' | \\\\-_ '--7 /- / || \\ / \u001b[0;37m\n\r\u001b[1;35m .' .' | \\\\ -_ / /- / || \\ / \u001b[0;37m\n\r\u001b[1;35m / ____ / | \\\\ '-_/ /|- _/ .|| \\ / \u001b[0;37m\n\r\u001b[1;35m |'' ''|--''''--_ \\ '==-/ | \\'--==='' .\\ \u001b[0;37m\n\r\u001b[1;35m ' '-| /| |-'\\'' __--'' \u001b[0;37m\n\r\u001b[1;35m |-''-_/ | | '\\_ _-' /\\ \u001b[0;37m\n\r Based on Diku by Hans,\u001b[1;35m / \\ \\__ \\/' \\__ \u001b[0;37m\n\r Katya, Tom, Michael, and\u001b[1;35m _--' _/ | .-''____--'-/ ''==. \u001b[0;37m\n\r Sebastian, MERC 2.1 by \u001b[1;35m((->/' '.|||' -_| ''-/ , . _|| \u001b[0;37m\n\r Hatchet, Furey and Kahn \u001b[1;35m -_ '\\ ''---l__i__i__i--''_/ \u001b[0;37m\n\r ROM 2.4 (c)1993-1996 by \u001b[1;35m _-'-__ ') \\--______________--'' \u001b[0;37m\n\r Russ Taylor, Oblivion 2.0\u001b[1;35m //.-'''-'_--'- |-------'''''''' \u001b[0;37m\n\r (C)1996-97 by Wes Wagner,\u001b[1;35m //.-'''--\\ \u001b[0;37m\n\r Based on The Dawn of Time v1.69r by\u001b[1;35m \u001b[1;34mhttp://www.dawnofchaos.vineyard.haus:2025 \u001b[0;37m\n\r Michael Garratt (c)1997-2004\u001b[1;35m \u001b[1;32mtelnet dawnofchaos.vineyard.haus 2024 \u001b[0;37m\n\r\u001b[1;37mBy What Name Do You Wish To Be Called?\u001b[0;37m <USER>",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true,
"MSP": true,
"MXP": true
},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.503730058670044,
"total": 11.378259181976318
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:59:54.724513+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 2024
},
{
"connected": "2026-04-07T07:20:13.005076+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 2024
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 2024
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=2024
INFO client_base.py:190 Connected to <Peer 176.9.151.147 2024>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL MXP, WILL MSP, WILL MCCP3_COMPRESS, WILL ATCP,
WILL MSDP, WILL MSSP, WILL ZMP, WILL GMCP, DO AARDWOLF, DO MCCP3_COMPRESS, DO ATCP, DO MSDP, DO MSSP, DO ZMP, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 9e7fd90d3aff78af
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 2024>
Starholm (ancientmists.vineyard.haus:4106)
Connection Banner:
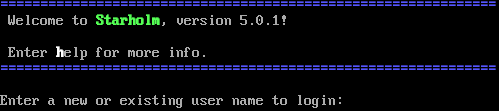
Server URLs
Server Info
Codebase: Evennia
Genre: None
Players online: 1 [2]
Status: Open Beta
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: Yes (MSSP)
MCCP: Yes (MSSP)
MCCP2: Negotiated
MXP: Yes (MSSP)
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 34 other servers.
Options offered by server: ECHO, GMCP, MCCP2, MSDP, MSSP, MXP, SGA
Options requested from client: LINEMODE, MCCP2, MSSP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "4f579dc442743eb8",
"fingerprint-data": {
"offered-options": [
"ECHO",
"GMCP",
"MCCP2",
"MSDP",
"MSSP",
"MXP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"MCCP3",
"MSP",
"STATUS",
"ZMP"
],
"requested-options": [
"LINEMODE",
"MCCP2",
"MSSP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[1m\u001b[34m==============================================================\u001b[0m\r\n Welcome to \u001b[1m\u001b[32mStarholm\u001b[0m, version 5.0.1!\r\n\r\n Enter \u001b[1m\u001b[37mh\u001b[0melp for more info.\r\n\u001b[1m\u001b[34m==============================================================\u001b[0m\r\n\r\nEnter a new or existing user name to login:\u001b[0m\r\n",
"banner_before_return": "\u001b[1m\u001b[34m==============================================================\u001b[0m\r\n Welcome to \u001b[1m\u001b[32mStarholm\u001b[0m, version 5.0.1!\r\n\r\n Enter \u001b[1m\u001b[37mh\u001b[0melp for more info.\r\n\u001b[1m\u001b[34m==============================================================\u001b[0m\r\n\r\nEnter a new or existing user name to login:\u001b[0m\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ADULT MATERIAL": "0",
"ANSI": "1",
"AREAS": "0",
"ATCP": "0",
"CLASSES": "0",
"CODEBASE": "Evennia",
"CONTACT": "",
"CRAWL DELAY": "-1",
"CREATED": "",
"DBSIZE": "0",
"EQUIPMENT SYSTEM": "None",
"EXITS": "0",
"EXTRA DESCRIPTIONS": "0",
"FAMILY": "Evennia",
"GAMEPLAY": "",
"GAMESYSTEM": "Custom",
"GENRE": "None",
"GMCP": "1",
"HELPFILES": "0",
"HIRING BUILDERS": "0",
"HIRING CODERS": "0",
"HOSTNAME": "",
"ICON": "",
"IP": "",
"LANGUAGE": "",
"LEVELS": "0",
"LOCATION": "",
"MCCP": "1",
"MCP": "0",
"MINIMUM AGE": "0",
"MOBILES": "0",
"MSDP": "1",
"MSP": "0",
"MUDPROGS": "0",
"MUDTRIGS": "0",
"MULTICLASSING": "0",
"MULTIPLAYING": "None",
"MXP": "1",
"NAME": "Starholm",
"NEWBIE FRIENDLY": "0",
"OBJECTS": "0",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYER CITIES": "0",
"PLAYER CLANS": "0",
"PLAYER CRAFTING": "0",
"PLAYER GUILDS": "0",
"PLAYERKILLING": "None",
"PLAYERS": "1",
"PORT": "4000",
"PUEBLO": "0",
"QUEST SYSTEM": "None",
"RACES": "0",
"RESETS": "0",
"ROLEPLAYING": "None",
"ROOMS": "0",
"SKILLS": "0",
"SSL": "1",
"STATUS": "Open Beta",
"SUBGENRE": "None",
"TRAINING SYSTEM": "None",
"UPTIME": "1774645499.8232977",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "",
"WORLD ORIGINALITY": "All Original",
"XTERM 256 COLORS": "1",
"XTERM TRUE COLORS": "0",
"ZMP": "0"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": false,
"MSSP": true,
"MXP": true,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"LINEMODE": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.3548102378845215,
"total": 11.049362182617188
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:28:40.636472+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4106
},
{
"connected": "2026-04-07T07:10:22.312827+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4106
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 4106
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=4106
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4106>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO LINEMODE
DEBUG stream_writer.py:1887 handle_do(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = True
DEBUG stream_writer.py:1024 send IAC WILL LINEMODE
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = True
DEBUG stream_writer.py:3384 local_option[LINEMODE] = True
DEBUG stream_writer.py:2816 slc_start: IAC SB LINEMODE SLC [..]
DEBUG stream_writer.py:2852 _slc_add (b'\x00', (^@, default))
DEBUG stream_writer.py:2805 send (slc_end): b'\x00\x03\x00'
DEBUG stream_writer.py:2811 slc_end: [..] IAC SE
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Starholm', 'PLAYERS': '1', 'UPTIME': '1774645499.8232977', 'PORT': '4000', 'CRAWL
DELAY': '-1', 'CODEBASE': 'Evennia', 'FAMILY': 'Evennia', 'ANSI': '1', 'GMCP': '1', 'ATCP': '0', 'MCCP': '1', 'MCP': '0',
'MSDP': '1', 'MSP': '0', 'MXP': '1', 'PUEBLO': '0', 'SSL': '1', 'UTF-8': '1', 'ZMP': '0', 'VT100': '0', 'XTERM 256 COLORS':
'1', 'HOSTNAME': '', 'CONTACT': '', 'CREATED': '', 'ICON': '', 'IP': '', 'LANGUAGE': '', 'LOCATION': '', 'MINIMUM AGE': '0',
'WEBSITE': '', 'GENRE': 'None', 'GAMEPLAY': '', 'STATUS': 'Open Beta', 'GAMESYSTEM': 'Custom', 'SUBGENRE': 'None', 'AREAS':
'0', 'HELPFILES': '0', 'MOBILES': '0', 'OBJECTS': '0', 'ROOMS': '0', 'CLASSES': '0', 'LEVELS': '0', 'RACES': '0', 'SKILLS':
'0', 'XTERM TRUE COLORS': '0', 'PAY TO PLAY': '0', 'PAY FOR PERKS': '0', 'HIRING BUILDERS': '0', 'HIRING CODERS': '0',
'DBSIZE': '0', 'EXITS': '0', 'EXTRA DESCRIPTIONS': '0', 'MUDPROGS': '0', 'MUDTRIGS': '0', 'RESETS': '0', 'ADULT MATERIAL':
'0', 'MULTICLASSING': '0', 'NEWBIE FRIENDLY': '0', 'PLAYER CITIES': '0', 'PLAYER CLANS': '0', 'PLAYER CRAFTING': '0', 'PLAYER
GUILDS': '0', 'EQUIPMENT SYSTEM': 'None', 'MULTIPLAYING': 'None', 'PLAYERKILLING': 'None', 'QUEST SYSTEM': 'None',
'ROLEPLAYING': 'None', 'TRAINING SYSTEM': 'None', 'WORLD ORIGINALITY': 'All Original'}
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:767 begin sub-negotiation SB LINEMODE
DEBUG stream_writer.py:754 sub-negotiation cmd LINEMODE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + LINEMODE] = False
DEBUG stream_writer.py:2703 recv IAC SB LINEMODE LINEMODE-MODE b'\x03' IAC SE
DEBUG stream_writer.py:1390 set Linemode <b'\x07': lit_echo:False, soft_tab:False, ack:True, trapsig:True, remote:False,
local:True>
DEBUG stream_writer.py:1393 send IAC SB LINEMODE LINEMODE-MODE <b'\x07': lit_echo:False, soft_tab:False, ack:True, trapsig:True,
remote:False, local:True> IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:531 negotiation complete after 0.60s.
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'client_options': {'ENCODING': 'utf-8', 'SCREENREADER': 'False', 'INPUTDEBUG': 'False', 'RAW':
'False', 'NOCOLOR': 'False', 'LOCALECHO': 'False'}}
DEBUG stream_writer.py:767 begin sub-negotiation SB GMCP
DEBUG stream_writer.py:754 sub-negotiation cmd GMCP SE completion byte
DEBUG stream_writer.py:2238 [SB + GMCP] unsolicited
DEBUG client.py:210 GMCP: Core.Supports.Get {'ENCODING': 'utf-8', 'SCREENREADER': False, 'INPUTDEBUG': False, 'RAW': False,
'NOCOLOR': False, 'LOCALECHO': False}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 4f579dc442743eb8
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4106>
ancientmists.vineyard.haus:4200
Connection Banner:
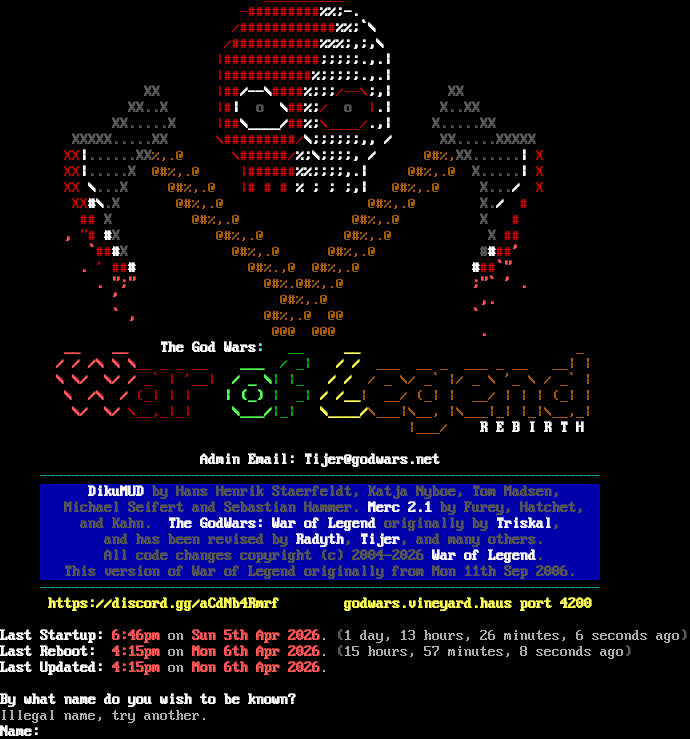
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:4200
- Website: godwars.net
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal name, try another.\n\r\u001b[1;37mName:\u001b[0m \u001b[0m",
"banner_before_return": "\n\r\n\r \n\r\n\r\t\t \u001b[0;31m__________\n\r\t \u001b[0;31m-#########\u001b[1;37m%%;-.\u001b[0m\n\r\t \u001b[0;31m/############\u001b[1;37m%%;`\\\u001b[0m\n\r\t \u001b[0;31m/###########\u001b[1;37m%%%;,;,\\\u001b[0m\n\r\t \u001b[0;31m|############\u001b[1;37m;;;;;.,.|\u001b[0m\n\r\t \u001b[0;31m|###########\u001b[1;37m%;;;;;.,.|\u001b[0m\n\r\t \u001b[1;30mXX\u001b[0m \u001b[0;31m|##\u001b[1;37m/--\\\u001b[0;31m####\u001b[1;37m%;;;\u001b[0;31m/--\\\u001b[1;37m;,|\u001b[0m \u001b[1;30mXX\u001b[0m\n\r\t \u001b[1;30mXX..X\u001b[0m \u001b[0;31m|#\u001b[1;37m| \u001b[1;30mo\u001b[1;37m \\\u001b[0;31m##\u001b[1;37m%;\u001b[0;31m/ \u001b[1;30mo\u001b[0;31m |\u001b[1;37m.|\u001b[0m \u001b[1;30mX..XX\u001b[0m\n\r\t \u001b[1;30mXX.....X\u001b[0m \u001b[0;31m|##\u001b[1;37m\\____/\u001b[0;31m##\u001b[1;37m%;\u001b[0;31m\\____/\u001b[1;37m.,|\u001b[0m \u001b[1;30mX.....XX\u001b[0m\n\r\t \u001b[1;30mXXXXX.....XX\u001b[0m \u001b[0;31m\\#########/\u001b[1;37m\\;;;;;;,, /\u001b[0m \u001b[1;30mXX.....XXXXX\u001b[0m\n\r\t\u001b[0;31mXX\u001b[1;37m|\u001b[1;30m......XX\u001b[0;33m%,.@ \u001b[0;31m\\######/\u001b[1;37m%;\\;;;;, /\u001b[0m \u001b[0;33m@#%,\u001b[1;30mXX......\u001b[1;37m|\u001b[0;31m X\u001b[0m\n\r\t\u001b[0;31mXX\u001b[1;37m|\u001b[1;30m.....X\u001b[0m \u001b[0;33m@#%,.@ \u001b[0;31m|######\u001b[1;37m%%;;;;,.|\u001b[0m \u001b[0;33m@#%,.@\u001b[1;30m X.....\u001b[1;37m|\u001b[0;31m X\u001b[0m\n\r\t\u001b[0;31mXX\u001b[1;37m \\\u001b[1;30m...X\u001b[0m \u001b[0;33m@#%,.@ \u001b[0;31m|# # # \u001b[1;37m% ; ; ;,|\u001b[0m \u001b[0;33m@#%,.@ \u001b[1;30mX...\u001b[1;37m/\u001b[0;31m X\u001b[0m\n\r\t \u001b[0;31mXX\u001b[1;37m#\\\u001b[1;30m.X\u001b[0m \u001b[0;33m@#%,.@ @#%,.@\u001b[0m \u001b[1;30mX.\u001b[1;37m/ \u001b[0;31m#\u001b[0m\n\r\t \u001b[0;31m## \u001b[1;30mX\u001b[0m \u001b[0;33m@#%,.@ @#%,.@\u001b[0m \u001b[1;30mX \u001b[0;31m#\u001b[0m\n\r\t\u001b[1;31m, \u001b[0;31m\"# \u001b[1;37m#\u001b[1;30mX\u001b[0m \u001b[0;33m@#%,.@ @#%,.@\u001b[0m \u001b[1;30mX \u001b[0;31m##\u001b[0m\n\r\t \u001b[1;31m`\u001b[0;31m##\u001b[1;37m#\u001b[1;30mX\u001b[0m \u001b[0;33m@#%,.@ @#%,.@\u001b[0m \u001b[1;30m#\u001b[1;37m#\u001b[0;31m##\u001b[1;31m'\u001b[0m\n\r\t \u001b[1;31m. \u001b[0;31m' ##\u001b[1;37m#\u001b[0m \u001b[0;33m@#%.,@ @#%,.@\u001b[0m \u001b[1;37m#\u001b[0;31m##\u001b[1;31m`\"\u001b[0m\n\r\t \u001b[1;31m. \";\" \u001b[0;33m@#%.@#%,.@\u001b[0m \u001b[1;31m;\"` ' .\u001b[0m\n\r\t \u001b[1;31m' \u001b[0;33m@#%,.@\u001b[0m \u001b[1;31m,.\u001b[0m\n\r\t \u001b[1;31m` , \u001b[0;33m@#%,.@ @@\u001b[0m \u001b[1;31m`\u001b[0m\n\r\t \u001b[0;33m@@@ @@@\u001b[0m \u001b[1;31m.\u001b[0m\n\r \u001b[1;31m __ __ \u001b[0;31m \u001b[1;37mThe God Wars\u001b[1;36m: \u001b[0;32m __ \u001b[1;33m __\u001b[0;33m _\n\r \u001b[1;31m / / /\\ \\ \\\u001b[0;31m__ _ _ __ \u001b[1;32m ___ \u001b[0;32m / _|\u001b[1;33m / /\u001b[0;33m ___ __ _ ___ _ __ __| |\n\r \u001b[1;31m \\ \\/ \\/ /\u001b[0;31m _` | '__|\u001b[1;32m / _ \\\u001b[0;32m| |_ \u001b[1;33m / / \u001b[0;33m / _ \\/ _` |/ _ \\ '_ \\ / _` |\n\r \u001b[1;31m \\ /\\ /\u001b[0;31m (_| | | \u001b[1;32m | (_) \u001b[0;32m| _|\u001b[1;33m / /__\u001b[0;33m| __/ (_| | __/ | | | (_| |\n\r \u001b[1;31m \\/ \\/ \u001b[0;31m\\__,_|_| \u001b[1;32m \\___/\u001b[0;32m|_| \u001b[1;33m \\____/\u001b[0;33m\\___|\\__, |\\___|_| |_|\\__,_|\n\r \u001b[1;31m \u001b[0;31m \u001b[0;32m \u001b[0;32m \u001b[1;33m \u001b[0;33m |___/ \u001b[1;37mR E B I R T H\n\r\n\r\u001b[0m \u001b[1;37m Admin Email: Tijer@godwars.net \u001b[0m\n\r\u001b[0m \u001b[0;36m----------------------------------------------------------------------\u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;37mDikuMUD\u001b[1;30m by Hans Henrik Staerfeldt, Katja Nyboe, Tom Madsen, \u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;30mMichael Seifert and Sebastian Hammer. \u001b[1;37mMerc 2.1\u001b[1;30m by Furey, Hatchet, \u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;30mand Kahn. \u001b[1;37mThe GodWars: War of Legend\u001b[1;30m originally by \u001b[1;37mTriskal\u001b[1;30m, \u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;30mand has been revised by \u001b[1;37mRadyth\u001b[1;30m, \u001b[1;37mTijer\u001b[1;30m, and many others. \u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;30mAll code changes copyright (c) 2004-2026 \u001b[1;37mWar of Legend\u001b[1;30m. \u001b[0m\n\r\u001b[0m \u001b[1;44m \u001b[1;30mThis version of War of Legend originally from Mon 11th Sep 2006. \u001b[0m\n\r\u001b[0m \u001b[0;36m----------------------------------------------------------------------\u001b[0m\n\r\u001b[0m \u001b[1;33mhttps://discord.gg/aCdNb4Rmrf godwars.vineyard.haus port 4200 \u001b[0m\n\r\n\r\u001b[0m\u001b[1;37mLast Startup: \u001b[1;31m6:46pm\u001b[0m on \u001b[1;31mSun 5th Apr 2026\u001b[0m. \u001b[1;30m(\u001b[0m1 day, 13 hours, 26 minutes, 6 seconds ago\u001b[1;30m)\u001b[0m\n\r\u001b[0m\u001b[1;37mLast Reboot: \u001b[1;31m4:15pm\u001b[0m on \u001b[1;31mMon 6th Apr 2026\u001b[0m. \u001b[1;30m(\u001b[0m15 hours, 57 minutes, 8 seconds ago\u001b[1;30m)\u001b[0m\n\r\u001b[0m\u001b[1;37mLast Updated: \u001b[1;31m4:15pm \u001b[0mon \u001b[1;31mMon 6th Apr 2026\u001b[0m.\n\r\n\r\u001b[0m\u001b[1;37mBy what name do you wish to be known?\u001b[0m \u001b[0m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.503807544708252,
"total": 11.310314178466797
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:01:38.822939+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4200
},
{
"connected": "2026-04-07T07:12:57.414141+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4200
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 4200
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=4200
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4200>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MCCP3_COMPRESS, WILL MSSP, WILL MSP, WILL MCCP2_COMPRESS, WILL ZMP,
WILL MSDP, WILL GMCP, WILL MXP, WILL ATCP, DO AARDWOLF, DO MCCP3_COMPRESS, DO MSSP, DO MSP, DO MCCP2_COMPRESS, DO ZMP, DO
MSDP, DO GMCP, DO MXP, DO ATCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4200>
ancientmists.vineyard.haus:4500
Connection Banner:
![^ Welcome To ^ (_) Eternal Darkness (_) /\\ /\\ /\\ /\\ /X\\ V2.0 /X\\ /\\ /\\ /\\ /\\ XX____XX____XX____XX___XXX _________________ XXX___XX____XX____XX____XX XXXXXXXXXXXXXXXXXXXXXXXXXX \|.................\| XXXXXXXXXXXXXXXXXXXXXXXXXX XX XX XX XX XXX \|. .\| XXX XX XX XX XX XX XX XX XX XX/#\|: ___ .\| XXX XX XX XX XX XX XX \|\\_XX __/\|X XX\\#\|:.....I I I......\| XXX X\|\\__ XX_/\| XX XX XX XX \\ _ \\/ _ /X XXX \|. .I_I_I. .\| XXX X\\ _ \\/ _ / XX XX XX XX (I)\\/(I)XX XXX \|. . .\|_XXX XX(I)\\/(I) XX XX XX XX \\/(oo)\\/XX XXX \|...............:(==)XX XX\\/(oo)\\/ XX XX XX XX \|V,,V\| XX XXX \|. . .\| XXX XX \|V,,V\| XX XX XX____XX__/\|A^^A\|\\XX___XXX \|. . .\| XXX___XX/\|A^^A\|\\ XX____XX XXXXXX/ \\/ TTTT \\/\\XXXXX \|.................\| XXXXX/\\/ TTTT \\/ \\XXXXXX XX X/ ( \|\| ) \\ XX/#\|: . .\| XXX / ( \|\| ) \\X XX XX_ X_\\ \\ \|\| / /__XX\\#\|: . .\| XXX__\\ \\ \|\| / /_X _XX XXX/ \\ \\\|\|\|\|/ / \\XX \|.................\| XX/ \\ \\\|\|\|\|/ / \\XXX XX/ oooo_/\|\|\|\|\\_ooo \\X \|_________________\| X/ ooo_/\|\|\|\|\\_oooo \\XX / oooooo \\ / oooooo \\ /_________________________\\ /_________________________\\ \|_________________________\| \|_________________________\| \|___I___I___I___I__I___\| \|___I__I___I___I___I___\| \|_I___I___I___I__I___I_\| \|_I__I___I___I___I___I_\| Original DikuMUD by Hans Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer Based on MERC 2.1 code by Hatchet, Furey, and Kahn ROM 2.4 copyright (c) 1993-1995 Russ Taylor ROT 1.4 copyright (c) 1996-1997 Russ Walsh WDM 2.0 Code by Waterdeep MUD Entertainmant. (c) 2007 Welcome to Fiery Flames ... input your name or choose a new one: +------------------[ Waterdeep Security ]-------------------+ I'm sorry, but that is an illegal name. If you are creating a new character, you will need to pick a name that is not already taken by another player or mobile. If you have always had this character and are recieving this error please contact the staff ASAP. The typical cause of this error is a mobile was created that shares your name. +-----------------------------------------------------------+ Please report this error to the e-mail address below. +------------------[ admin@waterdeep.org ]------------------+](../_images/banner_0a281f38127f.png)
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:4500
- Website: waterdeep.org
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\n\r\n\r\u001b[1;34m+\u001b[0;34m------------------\u001b[1;34m[ \u001b[1;31mWaterdeep Security \u001b[1;34m]\u001b[0;34m-------------------\u001b[1;34m+\u001b[0m\n\r\n\r\n\r \u001b[1;31m I'm sorry, but that is an illegal name.\u001b[0m\n\r\n\r If you are creating a new character, you will need to\n\r pick a name that is not already taken by another player\n\r or mobile.\n\r\n\r If you have always had this character and are recieving\n\r this error please contact the staff ASAP. The typical\n\r cause of this error is a mobile was created that shares\n\r your name.\n\r\n\r\u001b[1;34m+\u001b[0;34m-----------------------------------------------------------\u001b[1;34m+\u001b[0m\n\r \u001b[0;37mPlease report this error to the e-mail address below.\n\r\u001b[1;34m+\u001b[0;34m------------------\u001b[1;34m[ \u001b[1;33madmin@waterdeep.org \u001b[1;34m]\u001b[0;34m------------------\u001b[1;34m+\u001b[0m\n\r",
"banner_before_return": "\n\r\u001b[1;34m \u001b[1;37m ^ \u001b[1;34mWelcome To\u001b[1;37m ^\u001b[0m\n\r\u001b[1;37m \u001b[1;37m(\u001b[1;30m_\u001b[1;37m) \u001b[1;37mEt\u001b[0;37mer\u001b[1;30mnal \u001b[1;37mDa\u001b[0;37mrk\u001b[1;30mne\u001b[0;37mss\u001b[1;37m (\u001b[1;30m_\u001b[1;37m)\u001b[0m\n\r\u001b[1;37m /\\ /\\ /\\ /\\ /\u001b[1;30mX\u001b[1;37m\\ \u001b[1;34mV2.0 \u001b[1;37m /\u001b[1;30mX\u001b[1;37m\\ /\\ /\\ /\\ /\\\u001b[0m\n\r\u001b[1;37m \u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX\u001b[1;37m___\u001b[1;30mXXX \u001b[1;33m_________________ \u001b[1;30mXXX\u001b[1;37m___\u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX____\u001b[1;30mXX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XXXXXXXXXXXXXXXXXXXXXXXXXX \u001b[1;33m|\u001b[0;33m.................\u001b[1;33m| \u001b[1;30mXXXXXXXXXXXXXXXXXXXXXXXXXX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX XX XX XXX \u001b[1;33m|\u001b[0;33m. .\u001b[1;33m|\u001b[1;30m XXX XX XX XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX XX \u001b[1;30mXX XX\u001b[1;33m/\u001b[1;37m#\u001b[1;33m|\u001b[0;33m: \u001b[1;37m___\u001b[0;33m .\u001b[1;33m| \u001b[1;30mXXX XX XX XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30mXX XX\u001b[0;32m |\\_\u001b[1;30mXX \u001b[0;32m__/|\u001b[1;30mX XX\u001b[1;33m\\\u001b[1;37m#\u001b[1;33m|\u001b[0;33m:.....\u001b[1;37mI I I\u001b[0;33m......\u001b[1;33m|\u001b[1;30m XXX X\u001b[0;32m|\\__ \u001b[1;30mXX\u001b[0;32m_/|\u001b[1;30m XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX \u001b[0;32m\\ _ \\/ _ /\u001b[1;30mX XXX \u001b[1;33m|\u001b[0;33m. .\u001b[1;37mI_I_I\u001b[0;33m. .\u001b[1;33m| \u001b[1;30mXXX X\u001b[0;32m\\ _ \\/ _ /\u001b[1;30m XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX \u001b[0;32m (\u001b[1;31mI\u001b[0;32m)\\/(\u001b[1;31mI\u001b[0;32m)\u001b[1;30mXX XXX \u001b[1;33m|\u001b[0;33m. . .\u001b[1;33m|_\u001b[1;30mXXX XX\u001b[0;32m(\u001b[1;31mI\u001b[0;32m)\\/(\u001b[1;31mI\u001b[0;32m) \u001b[1;30m XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX \u001b[0;32m\\/(oo)\\/\u001b[1;30mXX XXX \u001b[1;33m|\u001b[0;33m...............:\u001b[1;33m(==)\u001b[1;30mXX XX\u001b[0;32m\\/(oo)\\/ \u001b[1;30m XX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX XX \u001b[0;32m |V,,V| \u001b[1;30mXX XXX \u001b[1;33m|\u001b[0;33m. . .\u001b[1;33m|\u001b[1;30m XXX XX\u001b[0;32m |V,,V| \u001b[1;30m XX \u001b[1;30mXX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX\u001b[1;37m____\u001b[1;30mXX\u001b[1;37m__\u001b[0;32m/|A^^A|\\\u001b[1;30mXX\u001b[1;37m___\u001b[1;30mXXX \u001b[1;33m|\u001b[0;33m. . .\u001b[1;33m|\u001b[1;30m XXX\u001b[1;37m___\u001b[1;30mXX\u001b[0;32m/|A^^A|\\ \u001b[1;30mXX\u001b[1;37m____\u001b[1;30mXX\u001b[0m\n\r\u001b[1;30m XXXXXX\u001b[0;32m/ \\/ TTTT \\/\\\u001b[1;30mXXXXX \u001b[1;33m|\u001b[0;33m.................\u001b[1;33m| \u001b[1;30mXXXXX\u001b[0;32m/\\/ TTTT \\/ \\\u001b[1;30mXXXXXX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX X\u001b[0;32m/ \u001b[0;32m ( || ) \\ \u001b[1;30mXX\u001b[1;33m/\u001b[1;37m#\u001b[1;33m|\u001b[0;33m: . .\u001b[1;33m| \u001b[1;30mXXX\u001b[0;32m / ( || ) \\\u001b[1;30mX XX\u001b[0m\n\r\u001b[1;30m \u001b[1;30m XX\u001b[1;37m_ \u001b[1;30mX\u001b[1;37m_\u001b[0;32m\\ \\ || / /\u001b[1;37m__\u001b[1;30mXX\u001b[1;33m\\\u001b[1;37m#\u001b[1;33m|\u001b[0;33m: . .\u001b[1;33m|\u001b[1;30m XXX\u001b[1;37m__\u001b[0;32m\\ \\ || / /\u001b[1;37m_\u001b[1;30mX \u001b[1;37m_\u001b[1;30mXX\u001b[0m\n\r\u001b[1;30m XXX\u001b[1;37m/ \u001b[0;32m\\ \\||||/ / \u001b[1;37m \\\u001b[1;30mXX \u001b[1;33m|\u001b[0;33m.................\u001b[1;33m| \u001b[1;30mXX\u001b[1;37m/ \u001b[0;32m \\ \\||||/ / \u001b[1;37m \\\u001b[1;30mXXX\u001b[0m\n\r\u001b[1;30m XX\u001b[1;37m/ \u001b[0;32moooo_/||||\\_ooo \u001b[1;37m \\\u001b[1;30mX \u001b[1;33m|_________________|\u001b[1;30m X\u001b[1;37m/ \u001b[0;32m ooo_/||||\\_oooo \u001b[1;37m \\\u001b[1;30mXX\u001b[0m\n\r\u001b[1;30m \u001b[1;37m/ \u001b[0;32moooooo \u001b[1;37m \\ \u001b[1;37m/ \u001b[0;32m oooooo \u001b[1;37m \\\u001b[0m\n\r\u001b[1;37m \u001b[1;37m /_________________________\\ /_________________________\\\u001b[0m\n\r\u001b[1;37m \u001b[1;37m |_________________________| |_________________________|\u001b[0m\n\r\u001b[1;37m \u001b[1;37m |___I___I___I___I__I___| |___I__I___I___I___I___|\u001b[0m\n\r\u001b[1;37m \u001b[1;37m |_I___I___I___I__I___I_| |_I__I___I___I___I___I_|\u001b[0m\n\r\u001b[0;37m Original DikuMUD by Hans Staerfeldt, Katja Nyboe,\u001b[0m\n\r\u001b[0;37m Tom Madsen, Michael Seifert, and Sebastian Hammer\u001b[0m\n\r\u001b[0;37m Based on MERC 2.1 code by Hatchet, Furey, and Kahn\u001b[0m\n\r\u001b[0;37m ROM 2.4 copyright (c) 1993-1995 Russ Taylor\u001b[0m\n\r\u001b[0;37m ROT 1.4 copyright (c) 1996-1997 Russ Walsh\u001b[0m \n\r\u001b[0;37m WDM 2.0 Code by Waterdeep MUD Entertainmant. (c) 2007\u001b[0m\n\r\u001b[0;36m\n\rWelcome to \u001b[1;31mFier\u001b[0;31my Fl\u001b[1;31mames\u001b[0;36m ... input your name or choose a new one:\u001b[0m\n\r",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.833733558654785
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:00:22.768448+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4500
},
{
"connected": "2026-04-07T06:51:12.054779+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4500
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 4500
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=4500
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4500>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL ATCP, WILL AARDWOLF, WILL ZMP, WILL MSDP, WILL MSSP, WILL MCCP2_COMPRESS,
WILL MCCP3_COMPRESS, WILL GMCP, WILL MXP, DO MSP, DO ATCP, DO AARDWOLF, DO ZMP, DO MSDP, DO MSSP, DO MCCP2_COMPRESS, DO
MCCP3_COMPRESS, DO GMCP, DO MXP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4500>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
RotDR (ancientmists.vineyard.haus:4545)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes ::::::::: :::::::: ::::::::::: ::::::::: :+: :+: :+: :+: :+: :+: :+: +:+ +:+ +:+ +:+ +:+ +:+ +:+ +#++:++#: +#+ +:+ +#+ +#+ +:+ +#+ +#+ +#+ +#+ +#+ +#+ +#+ #+# #+# #+# #+# #+# #+# #+# #+# #+# #+# ### ### ### ######## ### ### ### ######### R e a l m s O F T h e D a m n e d ___________________________ _ The ROTD is kindly hosted \| ==(W{==========- /===- by Vineyard.haus \| \|\| (.--.) /===-_---~~~~~~~~~------____ ____rotd.vineyard.haus_____\| \| \\_,\|\*\*\|,__ \|===-~ ____,-' -==\\\\ \\ ' --' ), //~\\\\ ~~~~---.___.-~~ ______-==\| /\\_. .__/\\ \\ \| \| \\\\ _-~ __--~~~ ,-/-==\\\\ ( \| . \|~~~~\| \| \| \\ ,' _-~ /' \| \\\\ )__/==0==-\\<>/ / / \\ / .' / \| \\\\ /~\\___/~~\\/ /' / \\ /' / ____ / \| \\\\.__/-~~ \\ \|_/' / \\/'_____________ /-'~ ~~~~~---__ \| ~-/~ ( ) /' _--~ \|The ROTD is \| \\_\| / _) \| ; ), __--~~ \|Circle based \| ________________ '~~--_/ _-~/- \|/ \\ '-~ \\ \|which in turn\| \|Administered by:\| {\\__--_/} / \\\\_>-\|)<__\\ \\ \|is Diku based\| \|Johann de Clouet\| /' (_/ _-~ \| \|__>--<__\| \| ------------- \| Rebecca Conroy \|\|\* \*_/) )-~ \| \|__>--<__\| \| \| Jonathan Foo \| / /~ ,_/ / /__>---<__/ \| \|Karti Mahendran \|o-o _// /-~_>---<__-~ / \|& Andrew Rapson \|(^(~ /~_>---<__- _-~ \|with the help of\|,/\| /__>--<__/ _-~ \|the other gods ,//(' \|__>--<__\| / .----_ -------------( ( ')) \|__>--<__\| \| /' _---_~\\ -)) )) ( \|__>--<__\| \| /' / ~\\\\ ,/,'//( ( \\__>--<__\\ \\ /' // \|\| ,( ( ((, )) ~-__>--<_~-_ ~--____---~' _/'/ /' ~/ ) ) ,/\| ~-_~>--<_/-__ __-~ _/ ._-~//( )/ )) ~~-'_/_/ /~~~~~~~__--~ ;'( ')/ ,)( ~~~~~~~~~~ ' ') '( (/ What be thy name. good traveler?](../_images/banner_f11e05d80f00.png)
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:4545
- Website: https://rotdr.vineyard.haus
Server Info
Codebase: tbaMUD
Players online: 1 [3]
Uptime: 0 days
Created: 2000
Server Location: 🇩🇪 US (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "RotDR"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\n\u001b[38;5;028m ::::::::: :::::::: ::::::::::: ::::::::: \r\n\u001b[38;5;142m :+: :+: :+: :+: :+: :+: :+: \r\n\u001b[38;5;142m +:+ +:+ +:+ +:+ +:+ +:+ +:+ \r\n\u001b[38;5;088m +#++:++#: +#+ +:+ +#+ +#+ +:+ \r\n\u001b[38;5;088m +#+ +#+ +#+ +#+ +#+ +#+ +#+ \r\n\u001b[38;5;196m #+# #+# #+# #+# #+# #+# #+# #+# #+# #+# \r\n\u001b[38;5;196m ### ### ### ######## ### ### ### ######### \r\n\u001b[38;5;059m R e a l m s O F T h e D a m n e d\r\n___________________________ \u001b[38;5;142m_\u001b[0;00m\r\n \u001b[38;5;024mThe ROTD\u001b[0;00m is kindly hosted | \u001b[38;5;142m==(W\u001b[38;5;145m{==========-\u001b[0;00m\u001b[38;5;028m /===-\r\n by \u001b[38;5;028mVineyard.haus\u001b[0;00m | \u001b[38;5;059m || (.--.) \u001b[0;00m\u001b[38;5;028m /===-_---~~~~~~~~~------____\r\n\u001b[0;00m____rotd.vineyard.haus_____| \u001b[38;5;059m| \\_,|\u001b[38;5;088m**\u001b[38;5;059m|,__ \u001b[0;00m\u001b[38;5;028m |===-~ ____,-'\r\n -==\\\\ \u001b[38;5;059m\\ ' --' ),\u001b[0;00m\u001b[38;5;028m //~\\\\ ~~~~---.___.-~~\r\n ______-==| \u001b[38;5;059m /\\_. .__/\\ \\\u001b[0;00m\u001b[38;5;028m | | \\\\ _-~\r\n __--~~~ ,-/-==\\\\ ( \u001b[38;5;059m| . |~~~~| |\u001b[0;00m\u001b[38;5;028m | \\ ,'\r\n _-~ /' | \\\\ \u001b[38;5;059m )__/\u001b[38;5;142m==\u001b[38;5;196m0\u001b[38;5;142m==\u001b[38;5;059m-\\<>/\u001b[0;00m\u001b[38;5;028m / / \\ /\r\n .' / | \\\\ \u001b[38;5;059m /~\\___/~~\\/ \u001b[0;00m\u001b[38;5;028m /' / \\ /'\r\n / ____ / | \\\\.__/-~~ \u001b[38;5;059m\\ |_/'\u001b[0;00m\u001b[38;5;028m / \\/'\u001b[0;00m_____________\u001b[38;5;028m\r\n /-'~ ~~~~~---__ | ~-/~ \u001b[38;5;059m( )\u001b[0;00m\u001b[38;5;028m /' _--~ \u001b[0;00m|\u001b[38;5;024mThe ROTD\u001b[0;00m is |\r\n\u001b[38;5;028m \\_| / _) | ; ), __--~~ \u001b[0;00m|Circle based |\r\n\u001b[0;00m ________________ \u001b[38;5;028m '~~--_/ _-~/- |/ \\ '-~ \\ \u001b[0;00m|which in turn|\r\n\u001b[0;00m|Administered by:|\u001b[38;5;028m {\\__--_/} / \\\\_>-|)<__\\ \\ \u001b[0;00m|is Diku based|\r\n\u001b[0;00m|\u001b[38;5;030mJohann de Clouet\u001b[0;00m|\u001b[38;5;028m /' (_/ _-~ | |__>--<__| | \u001b[0;00m -------------\r\n\u001b[0;00m|\u001b[38;5;030m Rebecca Conroy \u001b[0;00m|\u001b[38;5;028m|\u001b[38;5;201m* *\u001b[0;00m\u001b[38;5;028m_/) )-~ | |__>--<__| |\r\n\u001b[0;00m|\u001b[38;5;196m Jonathan Foo\u001b[0;00m |\u001b[38;5;028m / /~ ,_/ / /__>---<__/ |\r\n\u001b[0;00m|\u001b[38;5;030mKarti Mahendran \u001b[0;00m|\u001b[38;5;028mo-o _// /-~_>---<__-~ /\r\n\u001b[0;00m|\u001b[38;5;030m& Andrew Rapson\u001b[0;00m |\u001b[38;5;028m(^(\u001b[38;5;088m~\u001b[38;5;028m /~_>---<__- _-~\r\n\u001b[0;00m|with the help of|\u001b[38;5;088m,/|\u001b[38;5;028m /__>--<__/ _-~\r\n\u001b[0;00m|the other gods \u001b[38;5;088m,//('\u001b[38;5;028m |__>--<__| / .----_\r\n\u001b[0;00m -------------\u001b[38;5;088m( ( '))\u001b[38;5;028m |__>--<__| | /' _---_~\\\r\n \u001b[38;5;088m-)) )) (\u001b[38;5;028m |__>--<__| | /' / ~\\\\\r\n \u001b[38;5;088m,/,'//( (\u001b[38;5;028m \\__>--<__\\ \\ /' // ||\r\n \u001b[38;5;088m,( ( ((, ))\u001b[38;5;028m ~-__>--<_~-_ ~--____---~' _/'/ /'\r\n \u001b[38;5;088m~/ ) ) ,/|\u001b[38;5;028m ~-_~>--<_/-__ __-~ _/\r\n \u001b[38;5;088m._-~//( )/ ))\u001b[38;5;028m ~~-'_/_/ /~~~~~~~__--~\r\n \u001b[38;5;088m ;'( ')/ ,)(\u001b[38;5;028m ~~~~~~~~~~\u001b[0;00m\r\n \u001b[38;5;088m' ') '( (/\u001b[0;00m\r\n\r\n\u001b[38;5;231mWhat be thy name. good traveler?",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CODEBASE": "tbaMUD",
"CONTACT": "mtprower@yahoo.com",
"CRAWL DELAY": "-1",
"CREATED": "2000",
"DBSIZE": "63088",
"HOSTNAME": "rotdr.vineyard.haus",
"LANGUAGE": "English",
"LOCATION": "US",
"MINIMUM AGE": "16",
"MOBILES": "10045",
"NAME": "RotDR",
"OBJECTS": "11791",
"PLAYERS": "1",
"PORT": "4545",
"ROOMS": "41040",
"UPTIME": "1775523978",
"WEBSITE": "https://rotdr.vineyard.haus"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.704183101654053
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:49:12.829072+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4545
},
{
"connected": "2026-04-07T06:59:38.043309+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4545
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 4545
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=4545
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4545>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'RotDR'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'RotDR', 'PLAYERS': '1', 'UPTIME': '1775523978', 'CRAWL DELAY': '-1', 'HOSTNAME':
'rotdr.vineyard.haus', 'PORT': '4545', 'CODEBASE': 'tbaMUD', 'CONTACT': 'mtprower@yahoo.com', 'CREATED': '2000', 'LANGUAGE':
'English', 'LOCATION': 'US', 'MINIMUM AGE': '16', 'WEBSITE': 'https://rotdr.vineyard.haus', 'MOBILES': '10045', 'OBJECTS':
'11791', 'ROOMS': '41040', 'DBSIZE': '63088'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'RotDR'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL MCCP3_COMPRESS, WILL MCCP2_COMPRESS, WILL MSDP, WILL MSP, WILL GMCP, WILL
ZMP, WILL AARDWOLF, DO MXP, DO ATCP, DO MCCP3_COMPRESS, DO MCCP2_COMPRESS, DO GMCP, DO ZMP, DO AARDWOLF'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4545>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
PennMUSH (ancientmists.vineyard.haus:4598)
Connection Banner:
Server URLs
Server Info
Codebase: PennMUSH 1.8.8p0
Players online: 0 [4]
Uptime: 9 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "<This is where you announce that they've connected to your MUSH>\r\n<It's a good idea to include the version/patchlevel of MUSH you're running>\r\n<It's a good idea to include an email address for questions about the MUSH>\r\n-----------------------------------------------------------------------------\r\nUse create <name> <password> to create a character.\r\nUse connect <name> <password> to connect to your existing character.\r\nUse 'ch <name> <pass>' to connect hidden, and cd to connect DARK (admin)\r\nUse QUIT to logout.\r\nUse the WHO command to find out who is online currently.\r\n-----------------------------------------------------------------------------\r\nYell at your local god to personalize this file!\r\n\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.8p0",
"FAMILY": "TinyMUD",
"NAME": "PennMUSH",
"PLAYERS": "0",
"PORT": "4598",
"PUEBLO": "0",
"UPTIME": "1774697838",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.35349178314208984,
"total": 10.861495018005371
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:55:04.783645+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4598
},
{
"connected": "2026-04-07T07:08:17.984029+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 4598
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 4598
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=4598
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4598>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'PennMUSH', 'PLAYERS': '0', 'UPTIME': '1774697838', 'PORT': '4598', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'PennMUSH', 'PLAYERS': '0', 'UPTIME': '1774697838', 'PORT': '4598', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.8p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint f96aa48abbc42633
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4598>
ancientmists.vineyard.haus:5000
Connection Banner:
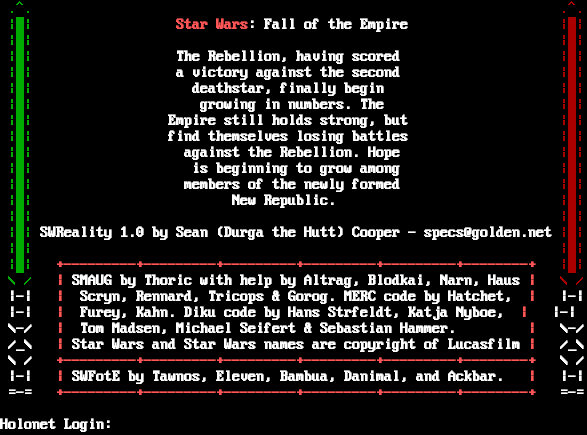
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:5000
- Website: golden.net
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\n\r\u001b[0;37m\u001b[0;32m .^\u001b[40m. \u001b[0;37m\u001b[0;31m .^\u001b[40m.\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m \u001b[0;37m\u001b[1;31mStar Wars\u001b[0;37m\u001b[1;37m: Fall of the Empire \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m The Rebellion, having scored \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m a victory against the second \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m deathstar, finally begin \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m growing in numbers. The \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m Empire still holds strong, but \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m find themselves losing battles \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m against the Rebellion. Hope \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m is beginning to grow among \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m members of the newly formed \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37m New Republic. \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;37mSWReality 1.0 by Sean (Durga the Hutt) Cooper - specs@golden.net \u001b[0;37m\u001b[0;31m|\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m |\u001b[42m \u001b[40m| \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[0;31m |\u001b[41m \u001b[40m|\n\r\u001b[0;37m\u001b[0;32m \\ / \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mSMAUG by Thoric with help by Altrag, Blodkai, Narn, Haus \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[0;31m \\ /\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Scryn, Rennard, Tricops & Gorog. MERC code by Hatchet, \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Furey, Kahn. Diku code by Hans St\udcc3\udca6rfeldt, Katja Nyboe, \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m \\-/ \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Tom Madsen, Michael Seifert & Sebastian Hammer. \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m \\-/\n\r\u001b[0;37m\u001b[1;37m /_\\ \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mStar Wars and Star Wars names are copyright of Lucasfilm \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m /_\\\n\r\u001b[0;37m\u001b[1;37m \\ / \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[1;37m \\ /\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mSWFotE by Tawnos, Eleven, Bambua, Danimal, and Ackbar. \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m =-= \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[1;37m =-=\n\r\n\r\u001b[0;37m\u001b[1;37mHolonet Login: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MCCP2": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.751813173294067
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:45:52.270924+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 5000
},
{
"connected": "2026-04-07T07:09:18.700543+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 5000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 5000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=5000
INFO client_base.py:190 Connected to <Peer 176.9.151.147 5000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MXP, WILL ATCP, WILL MCCP3_COMPRESS, WILL MSSP, WILL GMCP, WILL
AARDWOLF, WILL ZMP, WILL MSDP, WILL MSP, DO MXP, DO ATCP, DO MCCP3_COMPRESS, DO MSSP, DO GMCP, DO AARDWOLF, DO ZMP, DO MSDP,
DO MSP'
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG client_base.py:489 MCCP2 decompression ended (server→client)
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 5000>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
When Worlds Collide (ancientmists.vineyard.haus:6000)
Connection Banner:
![Please wait whilst we attempt to identify your client...<VERSION> Welcome to: : @@ % @@@ : = @@ @@@@ \* -=: . @@@ @@@ @@@@ -:. .. .- = - @@@@@@@@@@ ..- : .. .: -:_____ +. \*. - =_@@@@@___@@@.@ ._ -/ __\\_)_ __ \*.__ _\| \|@@@/ __\\_@_@_ __ \| \|_ __ _ ___ _ _ .. / _\\^\| \| '_ \\=/ _\` \| \|@@/ _\\/ _\` \| '_ \\\| __/ _\` / __\| \| \| \| / /:.:\| \| \|^\| \| (_\| \| \|@/ /@\| (_\| \| \|@\| \| \|\| (_\| \\__ \\ \|_\| \| =:\\/^^^^\|_\|_\|^\|_\|\\__,_\|_\|%\\/@%@\\__,_\|_\|@\|_\|\\__\\__,_\|___/\\__, \| .=:::::.^^^^"""""""""@@@@@@%@%@@%%%@@@@@@@@@@@^"""=""=:::. \|___/ - .-..^^^^:::::=""^^^""":::@@@@@%/\\@@@/\\%@%@@@@@@@@@@"""=:::.:. .= . :. :..^^^::::="":=@@@^@^"""=::%@@@\\ \\@/ /@@%@@@@@@@@""""""=:.^@^^"""-+ =::^^=^::=^@""":""@@@@""@@@@@%%@@\\ V /@%@%%@^^"""""@@@@=:.^@@@^^":.=. \*:. .""":"@@"""":""^@@@@@@@@@@@@@@\\_/@%%@@^^^^^"""@@@@=:::.::""""".-- -\*:...:""@@@@@"""":@@^""^""@@@@@%@@@@%%@@%@^^^^""":====:::::.::: .:= . : += .::@@@@@@@:: W H E N W O R L D S C O L L I D E :=^^=== . :=: -: :.::=@@==::=^^=^===::%%%@@@%%%@@@@@@^@@@@@@@:..^^^^ ======..- :. ..:==YY=======::.@@@@@@@%%%@@@@@@@@@@@@::."^^^""= ====..- .---@------@@@----.@@@==Y==::.::@@@@@@@%@@@%@@%@@@@@@:. . """""= ===... \| To@login@with a \| @@@..::...@@@@@:@@@@@@%@@@@ @@@@@%%@@@ """= ...: \| created@account \|. @@@ @@@@@@@ : @@@@%%@@@ . +@@@@@:........ .:. . \| @ \|@@@%%@@@@@@ + @@@@%%@@ . .+ . ... \| @accountname \|.@@@@ : @@@@ . . .-: '-----------------' :@@%%@@@ .----------------------.--------------@@@-.-@@@------. \| DikuMUD, MERC 2.1, \|StockMUD [ROM] @ \| FFV:WWC \| \| ROM v2.4 Russ Taylor \|Diablos @@\|@by Grief \| '----------------------@------------------@----------' By what name do you go@by?](../_images/banner_0bf21c94ee6f.png)
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:6000
- Website: realms.vineyard.haus
Server Info
Codebase: ROM 2.4
Genre: Fantasy
Gameplay: JRPG/MMO (without the massive)
Players online: 1 [5]
Uptime: 4 days
Created: 2024
Status: Development
Discord: https://discord.gg/94F6TUJkxb
Server Location: 🇩🇪 United States of America (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Yes (MSSP)
MSDP: Yes (MSSP)
MCCP: No
MCCP2: No
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "When Worlds Collide"
}
],
"banner_after_return": "",
"banner_before_return": "\n\rPlease wait whilst we attempt to identify your client...\u001b[0;00m\u001b[7z\u001b[1z<VERSION>\u001b[7z\r\n\n\rWelcome to:\r\n\u001b[0;00m \u001b[38;5;051m: \u001b[38;5;056m @@ \u001b[38;5;102m%\u001b[38;5;056m @@@\n\r\u001b[0;00m \u001b[38;5;051m: \u001b[38;5;030m=\u001b[38;5;056m @@ @@@@ \u001b[38;5;051m* -=:\n\r\u001b[0;00m \u001b[38;5;030m . \u001b[38;5;056m@@@ @@@ @@@@ \u001b[38;5;051m-:. \u001b[38;5;090m.\u001b[38;5;051m.\n\r\u001b[0;00m \u001b[38;5;051m.- \u001b[38;5;030m=\u001b[38;5;051m - \u001b[38;5;056m@@@@@@@@@@ \u001b[38;5;051m..- : \u001b[38;5;030m.\u001b[38;5;051m.\n\r\u001b[0;00m \u001b[38;5;051m.: -:\u001b[38;5;231m_____\u001b[38;5;051m +. *\u001b[38;5;030m. \u001b[38;5;051m- =\u001b[38;5;231m_\u001b[38;5;056m@@@@@\u001b[38;5;231m___\u001b[38;5;056m@@@.@ \u001b[38;5;051m .\u001b[38;5;231m_ \n\r\u001b[0;00m -\u001b[38;5;231m/ __\\_)_ __\u001b[38;5;051m *.\u001b[38;5;231m__ _| |\u001b[38;5;056m@@@\u001b[38;5;231m/ __\\_\u001b[38;5;056m@\u001b[38;5;231m_\u001b[38;5;056m@\u001b[38;5;231m_ __ | |_ __ _ ___ _ _ \n\r\u001b[0;00m\u001b[38;5;051m .. \u001b[38;5;231m/ _\\\u001b[38;5;188m^\u001b[38;5;231m| | '_ \\\u001b[38;5;226m=\u001b[38;5;231m/ _` | |\u001b[38;5;056m@@\u001b[38;5;231m/ _\\/ _` | '_ \\| __/ _` / __| | | |\n\r\u001b[0;00m \u001b[38;5;231m/ /\u001b[38;5;021m:.:\u001b[38;5;231m| | |\u001b[38;5;102m^\u001b[38;5;231m| | (_| | |\u001b[38;5;056m@\u001b[38;5;231m/ /\u001b[38;5;093m@\u001b[38;5;231m| (_| | |\u001b[38;5;056m@\u001b[38;5;231m| | || (_| \\__ \\ |_| |\n\r\u001b[0;00m \u001b[38;5;026m=:\u001b[38;5;231m\\/\u001b[38;5;102m^^^^\u001b[38;5;231m|_|_|\u001b[38;5;102m^\u001b[38;5;231m|_|\\__,_|_|\u001b[38;5;102m%\u001b[38;5;231m\\/\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;093m@\u001b[38;5;231m\\__,_|_|\u001b[38;5;056m@\u001b[38;5;188m|_|\\__\\__,_|___/\\__, |\n\r\u001b[0;00m \u001b[38;5;026m.=\u001b[38;5;021m:::::.\u001b[38;5;102m^\u001b[38;5;100m^\u001b[38;5;102m^^\u001b[38;5;028m\"\"\"\"\"\"\"\"\"\u001b[38;5;056m@@@@@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;093m@@\u001b[38;5;102m%%%\u001b[38;5;056m@@@@\u001b[38;5;093m@\u001b[38;5;056m@@@@@@\u001b[38;5;102m^\u001b[38;5;028m\"\"\"\u001b[38;5;226m=\u001b[38;5;028m\"\"\u001b[38;5;226m=\u001b[38;5;021m:::. \u001b[38;5;231m|___/\n\r\u001b[0;00m\u001b[38;5;051m- \u001b[38;5;026m.-\u001b[38;5;021m..\u001b[38;5;188m^^\u001b[38;5;102m^^\u001b[38;5;021m:::\u001b[38;5;033m::\u001b[38;5;094m=\u001b[38;5;028m\"\"\u001b[38;5;102m^^^\u001b[38;5;028m\"\"\"\u001b[38;5;021m:::\u001b[38;5;056m@@@@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;231m/\\\u001b[38;5;056m@@@\u001b[38;5;231m/\\\u001b[38;5;102m%\u001b[38;5;056m@\u001b[38;5;102m%\u001b[38;5;056m@@@@@@@@@@\u001b[38;5;028m\"\"\"\u001b[38;5;226m=\u001b[38;5;033m:::.:.\u001b[38;5;021m .\u001b[38;5;026m= \u001b[38;5;051m.\n\r\u001b[0;00m\u001b[38;5;051m:\u001b[38;5;030m. \u001b[38;5;026m:\u001b[38;5;021m..\u001b[38;5;188m^\u001b[38;5;102m^^\u001b[38;5;021m::::\u001b[38;5;100m=\u001b[38;5;028m\"\"\u001b[38;5;033m:\u001b[38;5;094m=\u001b[38;5;028m@@@\u001b[38;5;102m^\u001b[38;5;056m@\u001b[38;5;102m^\u001b[38;5;028m\"\"\"=::\u001b[38;5;102m%\u001b[38;5;056m@@@\u001b[38;5;231m\\ \\\u001b[38;5;056m@\u001b[38;5;231m/ /\u001b[38;5;056m@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;056m@@@@@@@@\u001b[38;5;028m\"\"\"\"\"\"\u001b[38;5;226m=\u001b[38;5;033m:.\u001b[38;5;102m^\u001b[38;5;188m@\u001b[38;5;231m^^\u001b[38;5;188m\"\"\"\u001b[38;5;021m-\u001b[38;5;026m+\n\r\u001b[0;00m \u001b[38;5;026m=\u001b[38;5;021m::\u001b[38;5;188m^^\u001b[38;5;231m=\u001b[38;5;188m^\u001b[38;5;021m::\u001b[38;5;100m=\u001b[38;5;102m^\u001b[38;5;028m@\"\"\"\u001b[38;5;033m:\u001b[38;5;028m\"\"\u001b[38;5;056m@@@@\u001b[38;5;028m\"\"\u001b[38;5;056m@@@@\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@@\u001b[38;5;231m\\ V /\u001b[38;5;056m@\u001b[38;5;102m%\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@\u001b[38;5;102m^^\u001b[38;5;028m\"\"\"\"\"\u001b[38;5;076m@@@@\u001b[38;5;226m=\u001b[38;5;033m:.\u001b[38;5;102m^\u001b[38;5;188m@\u001b[38;5;231m@\u001b[38;5;188m@\u001b[38;5;231m^^\u001b[38;5;231m\":\u001b[38;5;021m.=\u001b[38;5;026m.\n\r\u001b[0;00m \u001b[38;5;026m*\u001b[38;5;021m:. .\u001b[38;5;231m\"\"\"\u001b[38;5;021m:\u001b[38;5;028m\"@@\"\"\"\"\u001b[38;5;033m:\u001b[38;5;028m\"\"\u001b[38;5;102m^\u001b[38;5;056m@@@@@@@@@@@@@@\u001b[38;5;231m\\_/\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@@\u001b[38;5;102m^^\u001b[38;5;100m^^^\u001b[38;5;028m\"\"\"\u001b[38;5;076m@@@@\u001b[38;5;226m=\u001b[38;5;021m:::.::\u001b[38;5;188m\"\"\"\u001b[38;5;051m\"\"\u001b[38;5;018m.\u001b[38;5;033m--\n\r\u001b[0;00m \u001b[38;5;026m-*\u001b[38;5;021m:...:\u001b[38;5;028m\"\"\u001b[38;5;028m@\u001b[38;5;076m@@\u001b[38;5;028m@@\"\"\"\"\u001b[38;5;033m:\u001b[38;5;056m@@\u001b[38;5;102m^\u001b[38;5;028m\"\"\u001b[38;5;102m^\u001b[38;5;028m\"\"\u001b[38;5;056m@@@@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;056m@@@@\u001b[38;5;102m%%\u001b[38;5;056m@@\u001b[38;5;102m%\u001b[38;5;102m@\u001b[38;5;102m^^\u001b[38;5;100m^\u001b[38;5;102m^\u001b[38;5;028m\"\"\"\u001b[38;5;021m:\u001b[38;5;226m====\u001b[38;5;021m:::::\u001b[38;5;033m.:::\u001b[38;5;021m .:\u001b[38;5;026m= \u001b[38;5;051m. :\n\r\u001b[0;00m \u001b[38;5;026m+=\u001b[38;5;021m .::\u001b[38;5;028m@\u001b[38;5;076m@@@\u001b[38;5;028m@@@\u001b[38;5;021m::\u001b[38;5;051m W H E N W O R L D S C O L L I D E \u001b[38;5;021m:\u001b[38;5;226m=\u001b[38;5;102m^^\u001b[38;5;226m===\u001b[38;5;021m . :=\u001b[38;5;026m:\n\r\u001b[0;00m \u001b[38;5;026m-: :.::\u001b[38;5;094m=\u001b[38;5;028m@@\u001b[38;5;094m==\u001b[38;5;021m::\u001b[38;5;100m=\u001b[38;5;102m^^\u001b[38;5;226m=\u001b[38;5;102m^\u001b[38;5;226m===\u001b[38;5;021m::\u001b[38;5;102m%%%\u001b[38;5;093m@\u001b[38;5;056m@@\u001b[38;5;102m%%%\u001b[38;5;056m@@@@@@\u001b[38;5;102m^\u001b[38;5;056m@@@@@@@\u001b[38;5;021m:..\u001b[38;5;102m^^\u001b[38;5;100m^\u001b[38;5;102m^ \u001b[38;5;226m======\u001b[38;5;021m..\u001b[38;5;026m-\n\r\u001b[0;00m \u001b[38;5;026m:. ..:\u001b[38;5;094m==\u001b[38;5;100mYY\u001b[38;5;094m===\u001b[38;5;100m====\u001b[38;5;021m::.\u001b[38;5;056m@@@@@@\u001b[38;5;093m@\u001b[38;5;102m%%%\u001b[38;5;093m@@\u001b[38;5;056m@@@@@@@@@@\u001b[38;5;021m::.\u001b[38;5;028m\"\u001b[38;5;100m^^^\u001b[38;5;028m\"\"\u001b[38;5;094m= ====\u001b[38;5;021m..\u001b[38;5;026m-\n\r\u001b[38;5;033m.---\u001b[38;5;056m@\u001b[38;5;033m------\u001b[38;5;056m@@@\u001b[38;5;033m----.\u001b[38;5;056m@@@\u001b[38;5;094m==\u001b[38;5;100mY\u001b[38;5;094m==\u001b[38;5;021m::.::\u001b[38;5;056m@@@@@@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;056m@@@\u001b[38;5;102m%\u001b[38;5;056m@@\u001b[38;5;102m%\u001b[38;5;056m@@@@@@\u001b[38;5;021m:. . \u001b[38;5;028m\"\"\"\"\"\u001b[38;5;094m= ===\u001b[38;5;021m..\u001b[38;5;026m.\n\r\u001b[38;5;033m| \u001b[38;5;188mTo\u001b[38;5;056m@\u001b[38;5;188mlogin\u001b[38;5;056m@\u001b[38;5;188mwith a \u001b[38;5;033m| \u001b[38;5;056m@@@\u001b[38;5;021m..::...\u001b[38;5;056m@@@@@:@@@@@\u001b[38;5;093m@\u001b[38;5;102m%\u001b[38;5;093m@\u001b[38;5;056m@@@ @@@\u001b[38;5;093m@@\u001b[38;5;102m%%\u001b[38;5;093m@\u001b[38;5;056m@@ \u001b[38;5;028m\"\"\"\u001b[38;5;094m= \u001b[38;5;021m...\u001b[38;5;026m:\n\r\u001b[38;5;033m| \u001b[38;5;188mcreated\u001b[38;5;056m@\u001b[38;5;188maccount \u001b[38;5;033m|\u001b[38;5;051m. \u001b[38;5;056m@@@ @@@@@@@ \u001b[38;5;051m: \u001b[38;5;056m@@@\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@\u001b[38;5;056m@@\u001b[38;5;051m . +\u001b[38;5;056m@@@@@\u001b[38;5;102m:\u001b[38;5;021m........ .:\u001b[38;5;026m. \u001b[38;5;051m .\n\r\u001b[38;5;033m| \u001b[38;5;056m @\u001b[38;5;188m \u001b[38;5;033m|\u001b[38;5;056m@@\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@\u001b[38;5;056m@@@@@ \u001b[38;5;051m+ \u001b[38;5;056m@@@\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@@\u001b[38;5;051m . .+ \u001b[38;5;026m. ... \n\r\u001b[38;5;033m| \u001b[38;5;231m@accountname \u001b[38;5;033m|\u001b[38;5;018m.\u001b[38;5;056m@@@@ \u001b[38;5;051m: \u001b[38;5;056m@@@@ \u001b[38;5;090m. . \u001b[38;5;090m.-\u001b[38;5;051m:\n\r\u001b[38;5;033m'-----------------' \u001b[38;5;051m:\u001b[38;5;056m@\u001b[38;5;093m@\u001b[38;5;102m%%\u001b[38;5;093m@\u001b[38;5;056m@@ \n\r\u001b[38;5;033m.----------------------.--------------\u001b[38;5;056m@@@\u001b[38;5;033m-.-\u001b[38;5;056m@@@\u001b[38;5;033m------.\n\r\u001b[38;5;033m| \u001b[38;5;102mDikuMUD, MERC 2.1, \u001b[38;5;033m|\u001b[38;5;102mStockMUD [ROM] \u001b[38;5;056m@ \u001b[38;5;033m|\u001b[38;5;188m FFV:WWC \u001b[38;5;033m|\n\r\u001b[38;5;033m| \u001b[38;5;102mROM v2.4 Russ Taylor \u001b[38;5;033m|\u001b[38;5;102mDiablos \u001b[38;5;056m@@\u001b[38;5;033m|\u001b[38;5;056m@\u001b[38;5;188mby Grief \u001b[38;5;033m|\n\r\u001b[38;5;033m'----------------------\u001b[38;5;056m@\u001b[38;5;033m------------------\u001b[38;5;056m@\u001b[38;5;033m----------'\n\r\u001b[0;00mBy what name do you go\u001b[38;5;056m@\u001b[0;00mby?\n\r",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ABILITIES": "47",
"ANSI": "1",
"AREAS": "9",
"CODEBASE": "ROM 2.4",
"CRAWL DELAY": "-1",
"CREATED": "2024",
"DISCORD": "https://discord.gg/94F6TUJkxb",
"FAMILY": "Rom",
"GAMEPLAY": "JRPG/MMO (without the massive)",
"GAMESYSTEM": "None",
"GENRE": "Fantasy",
"GMCP": "1",
"HELPFILES": "276",
"HIRING BUILDERS": "Yes",
"HIRING CODERS": "No",
"HOSTNAME": "realms.vineyard.haus",
"INTERMUD": "",
"IP": "66.221.0.71",
"JOBS": "6",
"LANGUAGE": "English",
"LEVELS": "100",
"LOCATION": "United States of America",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "0",
"MOBILES": "3",
"MSDP": "1",
"MSP": "1",
"MXP": "1",
"NAME": "When Worlds Collide",
"OBJECTS": "27",
"PAY FOR PERKS": "No",
"PAY TO PLAY": "No",
"PLAYERS": "1",
"PORT": "6000",
"PUEBLO": "0",
"RACES": "4",
"ROOMS": "101",
"STATUS": "Development",
"SUBGENRE": "Final Fantasy",
"UPTIME": "1775192438",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "realms.vineyard.haus",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.784963607788086
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:43:05.787171+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6000
},
{
"connected": "2026-04-07T07:19:47.711414+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 6000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=6000
INFO client_base.py:190 Connected to <Peer 176.9.151.147 6000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'When Worlds Collide'
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'When Worlds Collide'}
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'When Worlds Collide', 'PLAYERS': '1', 'UPTIME': '1775192438', 'CRAWL DELAY': '-1',
'HOSTNAME': 'realms.vineyard.haus', 'PORT': '6000', 'CODEBASE': 'ROM 2.4', 'DISCORD': 'https://discord.gg/94F6TUJkxb',
'CREATED': '2024', 'IP': '66.221.0.71', 'LANGUAGE': 'English', 'LOCATION': 'United States of America', 'MINIMUM AGE': '0',
'WEBSITE': 'realms.vineyard.haus', 'FAMILY': 'Rom', 'GENRE': 'Fantasy', 'GAMEPLAY': 'JRPG/MMO (without the massive)',
'STATUS': 'Development', 'GAMESYSTEM': 'None', 'INTERMUD': '', 'SUBGENRE': 'Final Fantasy', 'AREAS': '9', 'HELPFILES': '276',
'MOBILES': '3', 'OBJECTS': '27', 'ROOMS': '101', 'JOBS': '6', 'LEVELS': '100', 'RACES': '4', 'ABILITIES': '47', 'ANSI': '1',
'GMCP': '1', 'MCCP': '0', 'MCP': '0', 'MSDP': '1', 'MSP': '1', 'MXP': '1', 'PUEBLO': '0', 'UTF-8': '1', 'VT100': '0', 'XTERM
256 COLORS': '1', 'PAY TO PLAY': 'No', 'PAY FOR PERKS': 'No', 'HIRING BUILDERS': 'Yes', 'HIRING CODERS': 'No'}
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL GMCP, DO MCCP2_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 6000>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
ancientmists.vineyard.haus:6100
Connection Banner:
![Do you see Color? Would you like to play using ANSI colors? [Y]es or [N]o Ansi enabled! /============================================================================\\ \|\| _______ _ _ _ \|\| \|\| \|__ __\| \| \| \| \| \| \|\| \|\| \| \| \| \|__ ___ \| \| ___ __ _ ___ _ __ __\| \|___ \|\| \|\| \| \| \| '_ \\ / _ \\ \| \| / _ \\/ _\` \|/ _ \\ '_ \\ / _\` / __\| \|\| \|\| \| \| \| \| \| \| __/ \| \|___\| __/ (_\| \| __/ \| \| \| (_\| \\__ \\ \|\| \|\| \|_\| \|_\| \|_\|\\___\| _ _\|______\\___\|\\__, \|\\___\|_\| \|_\|\\__,_\|___/ \|\| \|\| / _\| \| \|/ / __/ \| \|\| \|\| ___ \| \|_ \| ' / _ __ _ _ \|___/ _ __ \|\| \|\| / _ \\\| _\| \| < \| '__\| \| \| \| '_ \\\| '_ \\ \|\| \|\| \| (_) \| \| \| . \\\| \| \| \|_\| \| \| \| \| \| \| \| \|\| \|\| \\___/\|_\| \|_\|\\_\\_\| \\__, \|_\| \|_\|_\| \|_\| \|\| \|\| __/ \| \|\| \|\| \|___/ \|\| \\============================================================================/ http://legendsofkrynn.vineyard.haus Created in 2026 by: Kolf Admin Email: admin@legendsofkrynn.vineyard.haus Original DikuMUD by Hans Staerfeldt Katja Nyboe, Tom Madsen Michael Seifert, and Sebastian Hammer (based on Merc 2.1 by Hatchet, Furey and Khan) (based on Rom2.4 copyright 1993 - 1994 Russ Taylor) (based on Lok1.1 - by Craig Walters) Brought to you by: The Friendly Immortal Team of LoK State thy Name Adventurer:](../_images/banner_7d3ee9be6af1.png)
Server URLs
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Would you like to play using ANSI colors? [Y]es or [N]o \u001b[1;31mAnsi enabled!\u001b[0m\n\r/============================================================================\\\n\r || _______ _ _ _ ||\n\r || |__ __| | | | | | ||\n\r || | | | |__ ___ | | ___ __ _ ___ _ __ __| |___ ||\n\r || | | | '_ \\ / _ \\ | | / _ \\/ _` |/ _ \\ '_ \\ / _` / __| ||\n\r || | | | | | | __/ | |___| __/ (_| | __/ | | | (_| \\__ \\ ||\n\r || |_| |_| |_|\\___| _ _|______\\___|\\__, |\\___|_| |_|\\__,_|___/ ||\n\r || / _| | |/ / __/ | ||\n\r || ___ | |_ | ' / _ __ _ _ |___/ _ __ ||\n\r || / _ \\| _| | < | '__| | | | '_ \\| '_ \\ ||\n\r || | (_) | | | . \\| | | |_| | | | | | | | ||\n\r || \\___/|_| |_|\\_\\_| \\__, |_| |_|_| |_| ||\n\r || __/ | ||\n\r || |___/ ||\n\r \\============================================================================/\n\r \n\r\u001b[0m http://legendsofkrynn.vineyard.haus\n\r\n\r Created in 2026 by: Kolf\n\r\u001b[0m Admin Email: admin@legendsofkrynn.vineyard.haus\n\r\n\r Original DikuMUD by Hans Staerfeldt Katja Nyboe,\n\r Tom Madsen Michael Seifert, and Sebastian Hammer\n\r (based on Merc 2.1 by Hatchet, Furey and Khan)\n\r (based on Rom2.4 copyright 1993 - 1994 Russ Taylor)\n\r (based on Lok1.1 - by Craig Walters)\n\r\n\r\u001b[0m Brought to you by: The Friendly Immortal Team of LoK\n\r\n\r State thy Name Adventurer: ",
"banner_before_return": "\u001b[1;37mDo you see\u001b[0m \u001b[1;35mC\u001b[1;34mo\u001b[1;32ml\u001b[1;33mo\u001b[1;36mr\u001b[0m? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.559117317199707,
"total": 16.56112504005432
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:07:10.647505+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6100
},
{
"connected": "2026-04-07T06:53:18.963348+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6100
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 6100
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=6100
INFO client_base.py:190 Connected to <Peer 176.9.151.147 6100>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MSSP, WILL MCCP3_COMPRESS, WILL AARDWOLF, WILL MSDP, WILL MXP,
WILL ATCP, WILL GMCP, WILL MSP, WILL ZMP, DO MCCP2_COMPRESS, DO MSSP, DO MCCP3_COMPRESS, DO AARDWOLF, DO MSDP, DO MXP, DO
ATCP, DO GMCP, DO MSP, DO ZMP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 6100>
ancientmists.vineyard.haus:6666
Connection Banner:
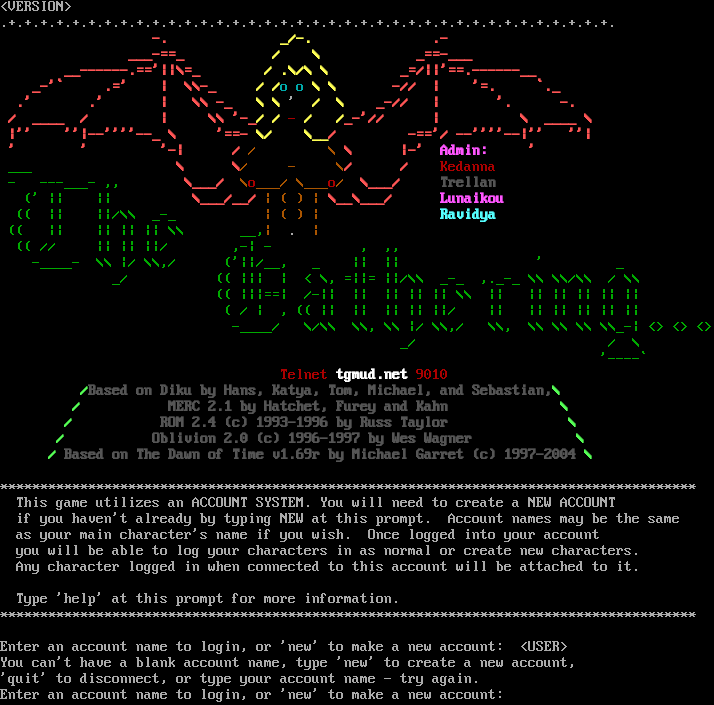
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:6666
- Website: tgmud.net
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 5 other servers.
Options offered by server: MCCP2, MSP, MXP
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9e7fd90d3aff78af",
"fingerprint-data": {
"offered-options": [
"MCCP2",
"MSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "You can't have a blank account name, type 'new' to create a new account,\r\n'quit' to disconnect, or type your account name - try again.\r\nEnter an account name to login, or 'new' to make a new account: ",
"banner_before_return": "\r\n\u001b[1z<VERSION>\u001b[6z\r\n.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.+.\n\r\u001b[1;31m -. \u001b[1;33m _/-. \u001b[1;31m .- \n\r\u001b[1;31m ___-==_ \u001b[1;33m / \\ \u001b[1;31m _==-___ \n\r\u001b[1;31m __------.=='||\\=_ \u001b[1;33m/ .\\/\\ \\ \u001b[1;31m _=/||'==.------__\n\r\u001b[1;31m _-'` .=' | \\\\-_ \u001b[1;33m/ /\u001b[0;36mo o \u001b[1;33m\\ \\ \u001b[1;31m -// | '=. `._\n\r\u001b[1;31m .' .' | \\\\ -_ \u001b[1;33m\\ \\ \u001b[0;37m' \u001b[1;33m/ \\\u001b[1;31m _-// | '. -.\n\r\u001b[1;31m / ____ / | \\\\ '-_\u001b[1;33m/ / \u001b[0;31m- \u001b[1;33m/ /\u001b[1;31m_-'// | \\ ____ \\\n\r\u001b[1;31m |'' ''|--''''--_ \\ '==- \u001b[1;33m\\/ \u001b[1;33m\\__\u001b[1;31m/ -=='/ --''''--|'' ''|\n\r\u001b[1;31m ' ' '-| / \u001b[0;33m/ \\\u001b[1;31m \\ |-' \u001b[1;35mAdmin:\u001b[1;31m '\n\r\u001b[0;32m ___ \u001b[1;31m \\ \\\u001b[0;33m/ - \\\u001b[1;31m/ / \u001b[0;33m\u001b[0;31mKedanna\u001b[0;32m\n\r\u001b[0;32m - ---___- ,,\u001b[1;31m \\___/ \u001b[0;33m\\\u001b[0;35m\u001b[0;31mo\u001b[0;33m___/ \\___\u001b[0;35m\u001b[0;31mo\u001b[0;33m/\u001b[1;31m \\___/ \u001b[1;30mTrellan\n\r\u001b[0;32m (' || || \u001b[1;31m\\___/__/\u001b[0;33m | ( ) |\u001b[1;31m \\__\\___/ \u001b[1;35mLunaikou\n\r\u001b[0;32m (( || ||/\\\\ _-_ \u001b[0;33m| ( ) | \u001b[1;36mRavidya\n\r\u001b[0;32m (( || || || || \\\\ __,\u001b[0;33m| \u001b[0;37m. \u001b[0;33m|\n\r\u001b[0;32m (( // || || ||/ ,-| - , ,,\n\r\u001b[0;32m -____- \\\\ |/ \\\\,/ ('||/__, _ || || ' _\n\r\u001b[0;32m _/ (( ||| | < \\, =||= ||/\\\\ _-_ ,._-_ \\\\ \\\\/\\\\ / \\\\\n\r\u001b[0;32m (( |||==| /-|| || || || || \\\\ || || || || || ||\n\r\u001b[0;32m ( / | , (( || || || || ||/ || || || || || ||\n\r\u001b[0;32m -____/ \\/\\\\ \\\\, \\\\ |/ \\\\,/ \\\\, \\\\ \\\\ \\\\ \\\\_-| <> <> <>\n\r\u001b[0;32m _/ / \\\n\r\u001b[0;32m '----`\n\r\u001b[0;31m \u001b[0;31mTelnet \u001b[1;37mtgmud.net \u001b[0;31m9010\n\r\u001b[1;32m /\u001b[1;30mBased on Diku by Hans, Katya, Tom, Michael, and Sebastian,\u001b[1;32m\\\n\r\u001b[1;32m /\u001b[1;30m MERC 2.1 by Hatchet, Furey and Kahn \u001b[1;32m\\\n\r\u001b[1;32m /\u001b[1;30m ROM 2.4 (c) 1993-1996 by Russ Taylor \u001b[1;32m\\\n\r\u001b[1;32m /\u001b[1;30m Oblivion 2.0 (c) 1996-1997 by Wes Wagner \u001b[1;32m\\\n\r\u001b[1;32m /\u001b[1;30m Based on The Dawn of Time v1.69r by Michael Garret (c) 1997-2004 \u001b[1;32m\\\u001b[0;37m\n\r\r\n***************************************************************************************\r\n This game utilizes an ACCOUNT SYSTEM. You will need to create a NEW ACCOUNT\r\n if you haven't already by typing NEW at this prompt. Account names may be the same\r\n as your main character's name if you wish. Once logged into your account\r\n you will be able to log your characters in as normal or create new characters.\r\n Any character logged in when connected to this account will be attached to it.\r\n\r\n Type 'help' at this prompt for more information.\r\n***************************************************************************************\r\n\r\nEnter an account name to login, or 'new' to make a new account: <USER>",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true,
"MSP": true,
"MXP": true
},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5036864280700684,
"total": 11.213984251022339
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:07:49.543541+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6666
},
{
"connected": "2026-04-07T07:21:18.950000+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6666
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 6666
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=6666
INFO client_base.py:190 Connected to <Peer 176.9.151.147 6666>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL MSSP, WILL MCCP2_COMPRESS, WILL ATCP, WILL MSDP, WILL ZMP, WILL
MCCP3_COMPRESS, WILL GMCP, WILL MXP, WILL AARDWOLF, DO MSSP, DO ATCP, DO MSDP, DO ZMP, DO MCCP3_COMPRESS, DO GMCP, DO
AARDWOLF'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 9e7fd90d3aff78af
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 6666>
Kingdoms of Kahara (ancientmists.vineyard.haus:6998)
Connection Banner:
![____ __.__ .___ \| \|/ _\|__\| ____ ____ __\| _/____ _____ ______ \| < \| \|/ \\ / ___\\ / __ \|/ _ \\ / \\ / ___/ \| \| \\\| \| \| \\/ /_/ > /_/ ( <_> ) Y Y \\\\___ \\ \|____\|__ \\__\|___\| /\\___ /\\____ \|\\____/\|__\|_\| /____ > \\/ \\//_____/ \\/ \\/ \\/ _____ _____/ ____\\ / _ \\ __\\ ( <_> ) \| \\____/\|__\| ____ __. .__ \| \|/ _\|____ \| \|__ _____ ____________ \| < \\__ \\ \| \| \\\\__ \\\\_ __ \\__ \\ \| \| \\ / __ \\\| Y \\/ __ \\\| \| \\// __ \\_ \|____\|__ (____ /___\| (____ /__\| (____ / \\/ \\/ \\/ \\/ \\/ o _---\| _ _ _ _ _ o ---\| o ]-I-I-I-[ _ _ _ _ _ _ _---\| \| _---\| \\ \` ' / ]-I-I-I-I-[ ---\| \| ---\| \|. \| \\ \` '_/ \| / \\ \| \| /^\\\| [\*] __\| ^ / ^ \\ ^ \| \|\*\|\| \|__ ,\| / \\ / \`\\ / \\ \| ===\| ___\| ___ ,\|__ / /=_=_=_=\\ \\ \|, _\| I_I__I_I__I_I (====(_________)___\|_\|____\|____ \\-\\--\|-\|--/-/ \| I [ ]__I I_I__\|____I_I_\| \|[] '\| \| [] \|\`__ . [ \\-\\--\|-\|--/-/ \|. \| \|' \|___\|_____I___\|___I___\|---------\| / \\\| [] .\|_\|-\|_\|-\|-\|_\|-\|_\|-\|_\|-\| [] [] \| <===> \| .\|-=-=-=-=-=-=-=-=-=-=-\| \| / \\ ] []\|\` [] \|\|.\|.\|.\|.\|.\|.\|.\|.\|.\|.\|\|- <===> ] []\| \` \| \|/////////\\\\\\\\\\\\\\\\\\\\.\|\|__. \| \|[] [ <===> ' \|\|\|\|\| \| \| \| \|\|\|\|.\|\| [] <===> \\T/ \| \|-- \|\|\|\|\| \| O \| O \| \|\|\|\|.\|\| . \|' \\T/ \| . _\|\|\|\|\| \| \| \| \|\|\|\|.\|\| \| \| \| ../\|' v . \| .\|\|\|\|\|/____\|____\\\|\|\|\| /\|. . \| . ./ .\|//\\............/...........\\........../../\\\\\\ ----------------------------------------------------------------------------- Use create <name> <password> to create a character. Use connect <name> <password> to connect to your existing character. Use QUIT to logout. Use the WHO command to find out who is online currently. -----------------------------------------------------------------------------](../_images/banner_2032bf40614e.png)
Server URLs
Server Info
Codebase: PennMUSH 1.8.6p2
Players online: 1 [6]
Uptime: 10 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " ____ __.__ .___ \r\n| |/ _|__| ____ ____ __| _/____ _____ ______\r\n| < | |/ \\ / ___\\ / __ |/ _ \\ / \\ / ___/\r\n| | \\| | | \\/ /_/ > /_/ ( <_> ) Y Y \\\\___ \\ \r\n|____|__ \\__|___| /\\___ /\\____ |\\____/|__|_| /____ >\r\n \\/ \\//_____/ \\/ \\/ \\/ \r\n _____ \r\n _____/ ____\\\r\n / _ \\ __\\ \r\n ( <_> ) | \r\n \\____/|__| \r\n ____ __. .__ \r\n | |/ _|____ | |__ _____ ____________ \r\n | < \\__ \\ | | \\\\__ \\\\_ __ \\__ \\ \r\n | | \\ / __ \\| Y \\/ __ \\| | \\// __ \\_\r\n |____|__ (____ /___| (____ /__| (____ /\r\n \\/ \\/ \\/ \\/ \\/ \r\n \r\n o \r\n _---| _ _ _ _ _ \r\n o ---| o ]-I-I-I-[ \r\n _ _ _ _ _ _ _---| | _---| \\ ` ' / \r\n ]-I-I-I-I-[ ---| | ---| |. | \r\n \\ ` '_/ | / \\ | | /^\\| \r\n [*] __| ^ / ^ \\ ^ | |*|| \r\n |__ ,| / \\ / `\\ / \\ | ===| \r\n ___| ___ ,|__ / /=_=_=_=\\ \\ |, _|\r\n I_I__I_I__I_I (====(_________)___|_|____|____\r\n \\-\\--|-|--/-/ | I [ ]__I I_I__|____I_I_| \r\n |[] '| | [] |`__ . [ \\-\\--|-|--/-/ \r\n |. | |' |___|_____I___|___I___|---------| \r\n / \\| [] .|_|-|_|-|-|_|-|_|-|_|-| [] [] | \r\n <===> | .|-=-=-=-=-=-=-=-=-=-=-| | / \\ \r\n ] []|` [] ||.|.|.|.|.|.|.|.|.|.||- <===> \r\n ] []| ` | |/////////\\\\\\\\\\\\\\\\\\\\.||__. | |[] [ \r\n <===> ' ||||| | | | ||||.|| [] <===>\r\n \\T/ | |-- ||||| | O | O | ||||.|| . |' \\T/ \r\n | . _||||| | | | ||||.|| | | |\r\n../|' v . | .|||||/____|____\\|||| /|. . | . ./\r\n.|//\\............/...........\\........../../\\\\\\\r\n\r\n-----------------------------------------------------------------------------\r\nUse create <name> <password> to create a character.\r\nUse connect <name> <password> to connect to your existing character.\r\nUse QUIT to logout.\r\nUse the WHO command to find out who is online currently.\r\n-----------------------------------------------------------------------------\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.6p2",
"FAMILY": "TinyMUD",
"NAME": "Kingdoms of Kahara",
"PLAYERS": "1",
"PORT": "6998",
"PUEBLO": "0",
"SSL": "443",
"UPTIME": "1774633916",
"WEBSITE": "http://kingdomsofkahara.vineyard.haus",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.4041023254394531,
"total": 10.918651819229126
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:09:58.757715+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6998
},
{
"connected": "2026-04-07T06:56:53.642167+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 6998
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 6998
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=6998
INFO client_base.py:190 Connected to <Peer 176.9.151.147 6998>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Kingdoms of Kahara', 'PLAYERS': '1', 'UPTIME': '1774633916', 'PORT': '6998', 'SSL':
'443', 'PUEBLO': '0', 'CODEBASE': 'PennMUSH 1.8.6p2', 'FAMILY': 'TinyMUD', 'WEBSITE': 'http://kingdomsofkahara.vineyard.haus',
'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Kingdoms of Kahara', 'PLAYERS': '1', 'UPTIME': '1774633916', 'PORT': '6998', 'SSL':
'443', 'PUEBLO': '0', 'CODEBASE': 'PennMUSH 1.8.6p2', 'FAMILY': 'TinyMUD', 'WEBSITE': 'http://kingdomsofkahara.vineyard.haus',
'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint f96aa48abbc42633
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 6998>
Fixing the Volatile (ancientmists.vineyard.haus:7000)
Connection Banner:
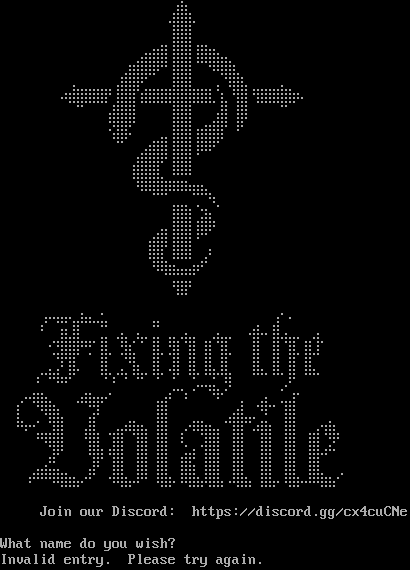
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:7000
- Website: https://discord.gg/cx4cuCNe
Server Info
Players online: 3 [7]
Uptime: 0 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: Negotiated
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: Negotiated
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 2 other servers.
Options requested from client: GMCP, MCCP2, MSDP, MSP, MSSP, NAWS, NEW_ENVIRON, TTYPE, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "195bae7111647e9e",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"GMCP",
"MCCP2",
"MSDP",
"MSP",
"MSSP",
"NAWS",
"NEW_ENVIRON",
"TTYPE",
"ZMP"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\nInvalid entry. Please try again.\r\n",
"banner_before_return": "\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u28e0\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u28f0\u28ff\u28f7\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800 \u2800\u2800\u2800\u2800\u28c0\u28e4\u28f6\u28b8\u28ff\u28ff\u28b0\u28f6\u28e4\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u28e4\u28fe\u28ff\u28ff\u283f\u28b8\u28ff\u28ff\u2818\u281b\u28bf\u28ff\u28f7\u2844\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800 \u2800\u2800 \u2840\u2800\u2800 \u2800\u2880\u28fe\u28ff\u287f\u280b\u2801\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u2848\u28bb\u28ff\u28c6\u2800\u2800\u2800\u2800\u2840\u2800\u2800\u2800\u2800\u2800\r\n\u2800 \u2800 \u2820\u28b6\u28ff\u28ff\u28ff\u28ff\u285f\u28b8\u28ff\u28ff\u28b1\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28c7\u28b1\u2840\u28bb\u28ff\u2818\u28ff\u28ff\u28ff\u28ff\u28f7\u2826\u2800\u2800\u2800\r\n\u2800\u2800 \u2800\u2800 \u2808\u2801\u2800\u2800\u28a0\u28ff\u28ff\u28ff\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u28fc\u2847\u28b8\u28ff\u2800\u2800\u2800\u2800\u2809\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800 \u2800\u2800\u2800 \u2800\u2828\u28fb\u28ff\u284b\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u28a0\u28f4\u28fe\u28ff\u2803\u2838\u2803\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u2819\u280b\u2800\u2800\u28e0\u28f6\u28ff\u28b8\u28ff\u28ff\u28b8\u28ff\u287f\u280b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2800\u2880\u28fe\u28ff\u28ff\u281f\u28b8\u28ff\u28ff\u2808\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2838\u28ff\u28ff\u28ff\u28c4\u28d8\u28db\u285b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2819\u281b\u283f\u283f\u281b\u281b\u281b\u283f\u2837\u28c4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u28b0\u28f6\u28e6\u2810\u28a4\u2848\u2802\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u28c0\u28b8\u28ff\u28ff\u28b0\u28ff\u2877\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u28a0\u28fe\u28ff\u28b8\u28ff\u28ff\u2818\u2809\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2838\u28ff\u28c7\u2838\u283f\u283f\u2800\u28e0\u2803\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2819\u283b\u283f\u2836\u2836\u281f\u2801\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2818\u28ff\u285f\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\r\n\u2800\u2800\u2800\u2800\u2800\u2870\u2812\u2836\u2816\u28e4\u2837\u2826\u28ac\u2844\u2800\u2800\u2800\u2800\u2800\u28e4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2840\u2800\u28f0\u2801\u2802\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2801\u2880\u28f8\u28e7\u28ff\u28c0\u28c0\u28a0\u2844\u2820\u28e6\u2880\u28a6\u2804\u28e4\u2800\u28e4\u2860\u28e6\u2844\u2880\u2860\u28e6\u2864\u2800\u2800\u28ba\u2857\u2802\u28ff\u28b4\u28e4\u2804\u28c0\u28b4\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2821\u28fd\u28ff\u287f\u2809\u2805\u28b8\u2867\u2800\u28bd\u28e7 \u2800\u28ff\u2804\u28bd\u2847\u28b8\u2847\u28b8\u2847\u28b8\u2867\u2800\u2800\u28b8\u2847\u2800\u28ff\u2800\u28ff\u2804\u28ff\u283c\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u28c0\u28c4\u285c\u28b8\u2867\u2800\u2800\u28b8\u28c7\u2880\u28c4\u28b9\u28c6\u2840\u28ff\u2840\u28bc\u2847\u28b8\u28c7\u28b8\u28e7\u28f8\u28c7\u2800\u2800\u28b8\u28e7\u2840\u28ff\u2840\u28ff\u2800\u28ff\u28c4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2818\u2800\u2809\u281b\u280b\u2800\u2800\u2800\u2800\u2801\u2803\u2808\u2800\u2809\u2800\u2808\u2800\u2888\u28c0\u2800\u2861\u2824\u28ec\u2840\u287b\u2800\u2800\u2800 \u2860\u280b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2860\u2812\u28bf\u28f7\u28c4\u2800 \u2820\u283e\u28f7\u2876\u280a\u2800\u2800\u2800\u2800\u2800\u28a0\u28f4\u2803\u2800\u2803 \u2808\u280b\u2800\u2800\u2844\u2800\u28e0\u28c6\u2840\u28a4\u28fc\u2801\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u28c7\u2800\u2880\u2819\u28ff\u28e7\u2800\u2800\u2800\u28f4\u2803\u2800\u2800\u2800\u28c0\u2800\u2800\u28b8\u28ff\u2800\u2800\u2800\u28c0\u2840\u2800\u2800\u28e0\u28fe\u28e7\u2864\u2888\u2843\u2800\u28b8\u28ff\u2800\u2800\u2800\u2800\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2809\u280b\u28a1\u28e4\u28fc\u28ff\u2800 \u28b0\u28ff\u2844\u2820\u28f4\u285e\u283b\u28ff\u2846\u28b8\u28ff\u2800\u28a0\u280a\u281b\u28bf\u28f7\u2846\u2800\u28ff\u2847\u2810\u28bb\u28ff\u2800\u28b8\u28ff\u2800\u28a0\u28f4\u2839\u28ff\u2844\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2808\u28bb\u287f \u2800\u28ff\u28e7\u28a0\u28ff\u2847\u2800\u28ff\u2847\u28b8\u28ff \u2808\u28c2\u2844\u28ba\u28ff\u2847\u2800\u28ff\u2847\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u28e0\u282e\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2880\u28e0\u28db\u2840 \u2800\u28f8\u280f\u2800\u28ff\u2847\u2800\u28ff\u2847\u28b8\u28ff\u2800\u28b8\u28ff\u2845\u28b8\u28ff\u2847\u2800\u28ff\u2847\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2830\u281b\u281b\u283b\u28bf\u28f7\u28e6\u2814\u280b\u2800\u2810\u283f\u28f7\u2864\u281f\u2803\u2838\u28ff\u2866\u2838\u28bf\u28f7\u287c\u28ff\u28e7\u2820\u28bf\u28f7\u2844\u28b8\u28ff\u2864\u2838\u28ff\u2866\u283c\u283f\u28f7\u28e6\u280a\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \r\n\r\n Join our Discord: https://discord.gg/cx4cuCNe\r\n\r\nWhat name do you wish? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"NAME": "Fixing the Volatile",
"PLAYERS": "3",
"UPTIME": "1775668554"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": false,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true,
"ZMP": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.667469501495361
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:19:22.211786+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
},
{
"connected": "2026-04-07T07:06:15.585955+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
},
{
"connected": "2026-04-09T00:07:20.026816+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 7000
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=ancientmists.vineyard.haus port=7000
INFO client_base.py:188 Connected to <Peer 176.9.151.147 7000>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO ZMP
DEBUG stream_writer.py:1887 handle_do(ZMP)
DEBUG stream_writer.py:998 skip WILL ZMP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO MSDP
DEBUG stream_writer.py:1887 handle_do(MSDP)
DEBUG stream_writer.py:998 skip WILL MSDP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO MSP
DEBUG stream_writer.py:1887 handle_do(MSP)
DEBUG stream_writer.py:998 skip WILL MSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Fixing the Volatile', 'PLAYERS': '3', 'UPTIME': '1775668554'}
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:462 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG client_base.py:510 negotiation complete after 0.34s.
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:90 EOF from server, closing.
INFO client_base.py:120 Connection closed to <Peer 176.9.151.147 7000>
DEBUG fingerprinting.py:850 connection for server fingerprint 195bae7111647e9e
Elessar Mush (ancientmists.vineyard.haus:7778)
Connection Banner:
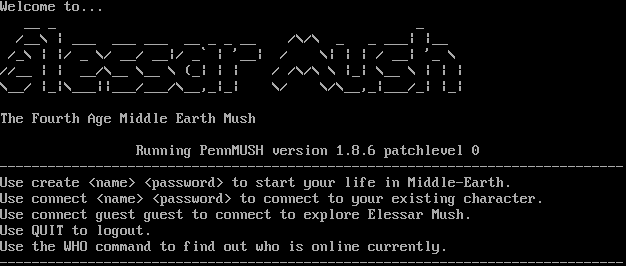
Server URLs
Server Info
Codebase: PennMUSH 1.8.6p0
Players online: 0 [8]
Uptime: 10 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: No
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 30 other servers.
Options offered by server: CHARSET, GMCP, MSSP, SGA
Options requested from client: NAWS, SGA, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "f96aa48abbc42633",
"fingerprint-data": {
"offered-options": [
"CHARSET",
"GMCP",
"MSSP",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"COM_PORT",
"ECHO",
"EOR",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS",
"SGA",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "Welcome to...\r\n __ _ _ \r\n /__\\ | ___ ___ ___ __ _ _ __ /\\/\\ _ _ ___| |__ \r\n /_\\ | |/ _ \\/ __/ __|/ _` | '__| / \\| | | / __| '_ \\ \r\n//__ | | __/\\__ \\__ \\ (_| | | / /\\/\\ \\ |_| \\__ \\ | | |\r\n\\__/ |_|\\___||___/___/\\__,_|_| \\/ \\/\\__,_|___/_| |_|\r\n\r\nThe Fourth Age Middle Earth Mush\r\n \r\n Running PennMUSH version 1.8.6 patchlevel 0\r\n------------------------------------------------------------------------------\r\nUse create <name> <password> to start your life in Middle-Earth.\r\nUse connect <name> <password> to connect to your existing character.\r\nUse connect guest guest to connect to explore Elessar Mush.\r\nUse QUIT to logout.\r\nUse the WHO command to find out who is online currently.\r\n------------------------------------------------------------------------------\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ANSI": "1",
"CODEBASE": "PennMUSH 1.8.6p0",
"FAMILY": "TinyMUD",
"NAME": "Elessar Mush",
"PLAYERS": "0",
"PORT": "7778",
"PUEBLO": "0",
"UPTIME": "1774645696",
"XTERM 256 COLORS": "1"
},
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": true,
"MXP": false,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MXP": false,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.35347938537597656,
"total": 10.859118700027466
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:14:26.991391+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7778
},
{
"connected": "2026-04-07T07:08:40.709043+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7778
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 7778
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=7778
INFO client_base.py:190 Connected to <Peer 176.9.151.147 7778>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Elessar Mush', 'PLAYERS': '0', 'UPTIME': '1774645696', 'PORT': '7778', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.6p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Elessar Mush', 'PLAYERS': '0', 'UPTIME': '1774645696', 'PORT': '7778', 'PUEBLO': '0',
'CODEBASE': 'PennMUSH 1.8.6p0', 'FAMILY': 'TinyMUD', 'ANSI': '1', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:990 skip DO CHARSET; remote_option = True
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:789 WILL MSSP unsolicited
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:789 WILL GMCP unsolicited
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
INFO client.py:343 LookupError: encoding x-penn-def not available
DEBUG client.py:376 encoding negotiated: US-ASCII
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED US-ASCII IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSSP, WILL GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT BINARY
DEBUG stream_writer.py:2199 handle_wont(BINARY)
DEBUG stream_writer.py:3384 remote_option[BINARY] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:998 skip DO SGA; pending_option = True
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC WONT ECHO
DEBUG stream_writer.py:2199 handle_wont(ECHO)
DEBUG stream_writer.py:3384 remote_option[ECHO] = False
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint f96aa48abbc42633
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 7778>
The Illusion of Living (ancientmists.vineyard.haus:7800)
Connection Banner:

Server URLs
Server Info
Players online: 2 [9]
Uptime: 9 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: Negotiated
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 8 other servers.
Options requested from client: GMCP, MCCP2, MSP, MSSP, NAWS, NEW_ENVIRON, TTYPE, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2582d677ba7e36e2",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"GMCP",
"MCCP2",
"MSP",
"MSSP",
"NAWS",
"NEW_ENVIRON",
"TTYPE",
"ZMP"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[38;5;239m\r\nInvalid entry. Please try again.\r\n\u001b[0;37;40m",
"banner_before_return": "\u001b[0;37;40m_________ _ _ _______ _________ _______ _ \r\n\\__ __/( \\ ( \\ |\\ /|( ____ \\\\__ __/( ___ )( ( /| \r\n ) ( | ( | ( | ) ( || ( \\/ ) ( | ( ) || \\ ( | \r\n | | | | | | | | | || (_____ | | | | | || \\ | | \r\n | | | | | | | | | |(_____ ) | | | | | || (\\ \\) | \r\n | | | | | | | | | | ) | | | | | | || | \\ | \r\n___) (___| (____/\\| (____/\\| (___) |/\\____) |___) (___| (___) || ) \\ | \r\n\\_______/(_______/(_______/(_______)\\_______)\\_______/(_______)|/ )_) \r\n \r\n _______ _______ _ _________ _________ _ _______ \r\n( ___ )( ____ \\ ( \\ \\__ __/|\\ /|\\__ __/( ( /|( ____ \\\r\n| ( ) || ( \\/ | ( ) ( | ) ( | ) ( | \\ ( || ( \\/\r\n| | | || (__ | | | | | | | | | | | \\ | || | \r\n| | | || __) | | | | ( ( ) ) | | | (\\ \\) || | ____ \r\n| | | || ( | | | | \\ \\_/ / | | | | \\ || | \\_ )\r\n| (___) || ) | (____/\\___) (___ \\ / ___) (___| ) \\ || (___) |\r\n(_______)|/ (_______/\\_______/ \\_/ \\_______/|/ )_)(_______)\r\n\r\n\r\n==================================================================================================== \r\n\r\nDriver: fluffos 20240131-6bc96f74-9ca961e3-uncommited Mudlib: Sand Man 1.0 (alpha)\r\n\r\n There are presently 1 adventurers on-line.\r\n \u001b[38;5;29m\r\nWhat name do you wish? \u001b[0;37;40m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"NAME": "The Illusion of Living",
"PLAYERS": "2",
"UPTIME": "1774729577"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": true,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": true,
"MSSP": true,
"MXP": false,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true,
"ZMP": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.665936470031738
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:40:27.807737+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7800
},
{
"connected": "2026-04-07T06:47:15.317747+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 7800
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 7800
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=7800
INFO client_base.py:190 Connected to <Peer 176.9.151.147 7800>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO MSP
DEBUG stream_writer.py:1887 handle_do(MSP)
DEBUG stream_writer.py:998 skip WILL MSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO ZMP
DEBUG stream_writer.py:1887 handle_do(ZMP)
DEBUG stream_writer.py:998 skip WILL ZMP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'The Illusion of Living', 'PLAYERS': '2', 'UPTIME': '1774729577'}
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG client_base.py:531 negotiation complete after 0.32s.
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 7800>
DEBUG fingerprinting.py:849 connection for server fingerprint 2582d677ba7e36e2
ancientmists.vineyard.haus:8008
Connection Banner:
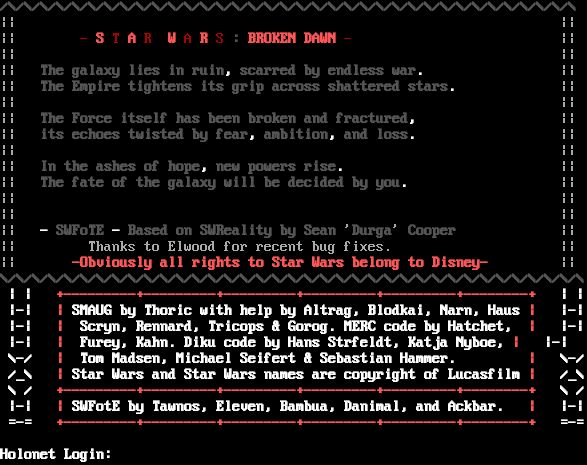
Server URLs
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\n\r\u001b[1;30m/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\\u001b[0;37m\n\r|| ||\n\r|| \u001b[0;31m- \u001b[1;31mS \u001b[0;31mT \u001b[1;31mA \u001b[0;31mR \u001b[1;31mW \u001b[0;31mA \u001b[1;31mR \u001b[0;31mS \u001b[1;30m: \u001b[1;31mBROKEN DAWN \u001b[0;31m- \u001b[0;37m ||\n\r|| ||\n\r|| \u001b[1;30mThe galaxy lies in ruin\u001b[1;37m,\u001b[1;30m scarred by endless war\u001b[1;37m.\u001b[0;37m ||\n\r|| \u001b[1;30mThe Empire tightens its grip across shattered stars\u001b[1;37m.\u001b[0;37m ||\n\r|| ||\n\r|| \u001b[1;30mThe Force itself has been broken and fractured\u001b[1;37m,\u001b[0;37m ||\n\r|| \u001b[1;30mits echoes twisted by fear\u001b[1;37m,\u001b[1;30m ambition\u001b[1;37m,\u001b[1;30m and loss\u001b[1;37m.\u001b[0;37m ||\n\r|| ||\n\r|| \u001b[1;30mIn the ashes of hope\u001b[1;37m,\u001b[1;30m new powers rise\u001b[1;37m.\u001b[0;37m ||\n\r|| \u001b[1;30mThe fate of the galaxy will be decided by you\u001b[1;37m.\u001b[0;37m ||\n\r|| ||\n\r|| ||\n\r|| \u001b[1;37m- \u001b[1;30mSWFoTE \u001b[1;37m- \u001b[1;30mBased on SWReality by Sean \u001b[0;37m'\u001b[1;30mDurga\u001b[0;37m'\u001b[1;30m Cooper \u001b[0;37m ||\n\r|| Thanks to Elwood for recent bug fixes. ||\n\r|| \u001b[1;31m-Obviously all rights to Star Wars belong to Disney-\u001b[0;37m ||\n\r\u001b[1;30m\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\/\\\u001b[0m\n\r\u001b[0;37m\u001b[1;37m | | \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[1;37m | |\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mSMAUG by Thoric with help by Altrag, Blodkai, Narn, Haus \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Scryn, Rennard, Tricops & Gorog. MERC code by Hatchet, \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Furey, Kahn. Diku code by Hans St\udcc3\udca6rfeldt, Katja Nyboe, \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m \\-/ \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m Tom Madsen, Michael Seifert & Sebastian Hammer. \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m \\-/\n\r\u001b[0;37m\u001b[1;37m /_\\ \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mStar Wars and Star Wars names are copyright of Lucasfilm \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m /_\\\n\r\u001b[0;37m\u001b[1;37m \\ / \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[1;37m \\ /\n\r\u001b[0;37m\u001b[1;37m |-| \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37mSWFotE by Tawnos, Eleven, Bambua, Danimal, and Ackbar. \u001b[0;37m\u001b[1;31m| \u001b[0;37m\u001b[1;37m |-|\n\r\u001b[0;37m\u001b[1;37m =-= \u001b[0;37m\u001b[1;31m+---------+---------+---------+---------+---------+--------+ \u001b[0;37m\u001b[1;37m =-=\n\r\n\r\u001b[0;37m\u001b[1;37mHolonet Login: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"MCCP2": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.7694761753082275
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:52:18.326289+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 8008
},
{
"connected": "2026-04-07T06:57:43.860680+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 8008
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 8008
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=8008
INFO client_base.py:190 Connected to <Peer 176.9.151.147 8008>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL GMCP, WILL MSP, WILL MSDP, WILL ATCP, WILL MXP, WILL AARDWOLF,
WILL MSSP, WILL MCCP3_COMPRESS, WILL ZMP, DO GMCP, DO MSP, DO MSDP, DO ATCP, DO MXP, DO AARDWOLF, DO MSSP, DO MCCP3_COMPRESS,
DO ZMP'
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG client_base.py:489 MCCP2 decompression ended (server→client)
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 8008>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
Gundam Wing Universe (ancientmists.vineyard.haus:9876)
Connection Banner:
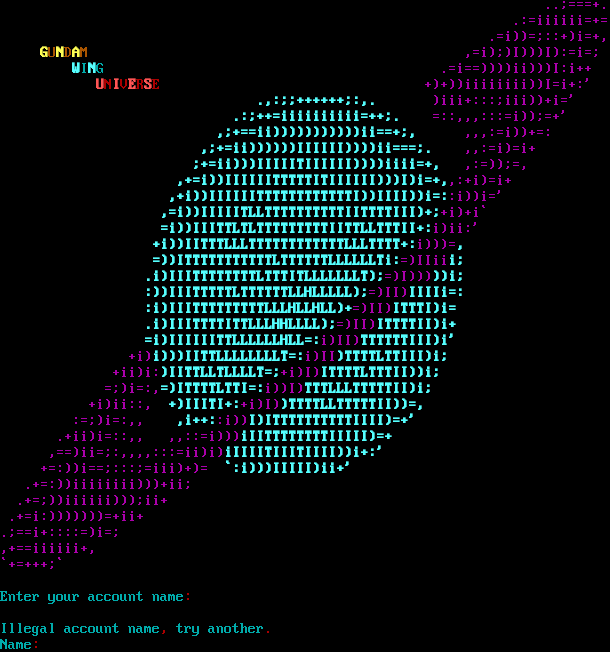
Server URLs
- Telnet: telnet://ancientmists.vineyard.haus:9876
- Website: gundam.vineyard.haus
Server Info
Codebase: GWM 1.02
Genre: Sci-Fi Anime
Gameplay: Casual
Players online: 4 [10]
Uptime: 0 days
Created: 10 Aug 2025
Status: Beta
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Yes (MSSP)
MCCP: Yes (MSSP)
MCCP2: Negotiated
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: ECHO, MCCP2, MSDP, MSP, MSSP, MXP
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "47422ef44d0aacad",
"fingerprint-data": {
"offered-options": [
"ECHO",
"MCCP2",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Gundam Wing Universe"
}
],
"banner_after_return": "\u001b[36m\n\rIllegal account name\u001b[31m,\u001b[36m try another\u001b[31m.\u001b[36m\nName\u001b[31m:\u001b[36m ",
"banner_before_return": "\u001b[35m ..;===+.\n .:=iiiiii=+=\n .=i))=;::+)i=+,\n \u001b[1;33mG\u001b[0;33mU\u001b[1;33mN\u001b[0;33mD\u001b[1;33mA\u001b[0;33mM \u001b[35m ,=i);)I)))I):=i=;\n \u001b[1;36mW\u001b[0;36mI\u001b[1;36mN\u001b[0;36mG \u001b[35m .=i==))))ii)))I:i++\n \u001b[1;31mU\u001b[0;31mN\u001b[1;31mI\u001b[0;31mV\u001b[1;31mE\u001b[0;31mR\u001b[1;31mS\u001b[0;31mE\u001b[35m +)+))iiiiiiii))I=i+:'\n\u001b[1;36m .,:;;++++++;:,.\u001b[0;35m )iii+:::;iii))+i='\n\u001b[1;36m .:;++=iiiiiiiiii=++;.\u001b[0;35m =::,,,:::=i));=+'\n\u001b[1;36m ,;+==ii)))))))))))ii==+;,\u001b[0;35m ,,,:=i))+=:\n\u001b[1;36m ,;+=ii))))))IIIIII))))ii===;.\u001b[0;35m ,,:=i)=i+\n\u001b[1;36m ;+=ii)))IIIIITIIIIII))))iiii=+,\u001b[0;35m ,:=));=,\n\u001b[1;36m ,+=i))IIIIIITTTTTITIIIIII)))I)i=+,\u001b[0;35m,:+i)=i+\n\u001b[1;36m ,+i))IIIIIITTTTTTTTTTTTI))IIII))i=:\u001b[0;35m:i))i='\n\u001b[1;36m ,=i))IIIIITLLTTTTTTTTTTIITTTTIII)+;\u001b[0;35m+i)+i`\n\u001b[1;36m =i))IIITTLTLTTTTTTTTTIITTLLTTTII+:\u001b[0;35mi)ii:'\n\u001b[1;36m +i))IITTTLLLTTTTTTTTTTTTLLLTTTT+:\u001b[0;35mi)))=\u001b[1;36m,\n =))ITTTTTTTTTTTLTTTTTTLLLLLLTi:\u001b[0;35m=)IIii\u001b[1;36mi;\n .i)IIITTTTTTTTLTTTITLLLLLLLT);\u001b[0;35m=)I)))\u001b[1;36m))i;\n :))IIITTTTTLTTTTTTLLHLLLLL);\u001b[0;35m=)II)\u001b[1;36mIIIIi=:\n :i)IIITTTTTTTTTLLLHLLHLL)+\u001b[0;35m=)II)\u001b[1;36mITTTI)i=\n .i)IIITTTTITTLLLHHLLLL);\u001b[0;35m=)II)\u001b[1;36mITTTTII)i+\n =i)IIIIIITTLLLLLLHLL=:\u001b[0;35mi)II)\u001b[1;36mTTTTTTIII)i'\n\u001b[0;35m +i)\u001b[1;36mi)))IITTLLLLLLLLT=:\u001b[0;35mi)II\u001b[1;36m)TTTTLTTIII)i;\n\u001b[0;35m +ii)i:\u001b[1;36m)IITTLLTLLLLT=;\u001b[0;35m+i)I)\u001b[1;36mITTTTLTTTII))i;\n\u001b[0;35m =;)i=:,\u001b[1;36m=)ITTTTLTTI=:\u001b[0;35mi))I)\u001b[1;36mTTTLLLTTTTTII)i;\n\u001b[0;35m +i)ii::, \u001b[1;36m+)IIITI+:\u001b[0;35m+i)I)\u001b[1;36m)TTTTLLTTTTTII))=,\n\u001b[0;35m :=;)i=:,, \u001b[1;36m ,i++:\u001b[0;35m:i))\u001b[1;36mI)ITTTTTTTTTTIIII)=+'\n\u001b[0;35m .+ii)i=::,, ,,::=i)))\u001b[1;36miIITTTTTTTTIIIII)=+\n\u001b[0;35m ,==)ii=;:,,,,:::=ii)i)\u001b[1;36miIIIITIIITIIII))i+:'\n\u001b[0;35m +=:))i==;:::;=iii)+)= \u001b[1;36m `:i)))IIIII)ii+'\n\u001b[0;35m .+=:))iiiiiiii)))+ii;\n .+=;))iiiiii)));ii+\n .+=i:)))))))=+ii+\n.;==i+::::=)i=;\n,+==iiiiii+,\n`+=+++;` \n\n\u001b[36mEnter your account name\u001b[31m:\u001b[37m \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"ANSI": "1",
"CODEBASE": "GWM 1.02",
"CONTACT": "gundamwing@gundam.vineyard.haus",
"CRAWL DELAY": "-1",
"CREATED": "10 Aug 2025",
"GAMEPLAY": "Casual",
"GAMESYSTEM": "Custom",
"GENRE": "Sci-Fi Anime",
"GMCP": "0",
"HOSTNAME": "gundam.vineyard.haus",
"MCCP": "1",
"MCP": "0",
"MSDP": "1",
"MSP": "1",
"MXP": "1",
"NAME": "Gundam Wing Universe",
"PLAYERS": "4",
"PORT": "9876",
"PUEBLO": "0",
"STATUS": "Beta",
"SUBGENRE": "Mobile Suit Gundam",
"UPTIME": "1775536019",
"UTF-8": "1",
"VT100": "0",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5044891834259033,
"total": 11.30936312675476
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:11:20.154153+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 9876
},
{
"connected": "2026-04-07T07:25:23.852131+00:00",
"host": "ancientmists.vineyard.haus",
"ip": "176.9.151.147",
"port": 9876
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ancientmists.vineyard.haus 9876
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=ancientmists.vineyard.haus port=9876
INFO client_base.py:190 Connected to <Peer 176.9.151.147 9876>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'Gundam Wing Universe'
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP2_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Gundam Wing Universe', 'PLAYERS': '4', 'UPTIME': '1775536019', 'CRAWL DELAY': '-1',
'HOSTNAME': 'gundam.vineyard.haus', 'PORT': '9876', 'CODEBASE': 'GWM 1.02', 'CONTACT': 'gundamwing@gundam.vineyard.haus',
'CREATED': '10 Aug 2025', 'GENRE': 'Sci-Fi Anime', 'GAMEPLAY': 'Casual', 'STATUS': 'Beta', 'GAMESYSTEM': 'Custom', 'SUBGENRE':
'Mobile Suit Gundam', 'ANSI': '1', 'GMCP': '0', 'MCCP': '1', 'MCP': '0', 'MSDP': '1', 'MSP': '1', 'MXP': '1', 'PUEBLO': '0',
'UTF-8': '1', 'VT100': '0', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'Gundam Wing Universe'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG client_base.py:531 negotiation complete after 1.12s.
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT b'\xfc'
DEBUG stream_writer.py:2199 handle_wont(WONT)
DEBUG stream_writer.py:3384 remote_option[WONT] = False
DEBUG stream_writer.py:3384 pending_option[DO + WONT] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:998 skip DO ECHO; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:849 connection for server fingerprint 47422ef44d0aacad
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 9876>
Apothica (apothica.kozow.com:6464)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] No ________________ /\\ /\\ / \\____________/ \\ / / \\ \\ / / \\ \\ / / Welcome to \\ \\ /___/ Apothica \\___\\ \\ \\ / / \\ \\ ____________ / / \\ \\ \\##########/ / / ,--, \\ \\ \\########/ / / ,--, )""( \\ \\ \\######/ / / )""( / \\ \\ \\ \\####/ / / /.nn.\\ / \\ \\ \\ \\##/ / / /$$$$$$\\ . . \\ \\ \\/ / / .$$$$$$$$. \|'-....-'\| \\ \\ / / \|"\*$$$$\*"\| \| \| __ \\ \\/_ /_ _ \| \| \| \| / \| ____ ___\\ / /_/ /_ (_)________ _ \| \| \|'-....-'\| / /\| \| / __ \\/ __ \\/ __/ __ \\/ / ___/ __ '/ \|8n....n8\| \| \| / ___ \|/ /_/ / /_/ / /_/ / / / / /__/ /_/ / \|$$$$$$$$\| \| \| /_/ \|_/ .___/\\____/\\__/_/ /_/_/\\___/\\__,_/ \|$$$$$$$$\| '-....-' mh /_/ "\*$$$$\*" By what name do you wish to be known?](../_images/banner_c434228454a1.png)
Server URLs
- Telnet: telnet://apothica.kozow.com:6464
- Website: https://azerethmud.weebly.com/
Server Info
Codebase: tbaMUD
Players online: 0 [11]
Uptime: 6 days
Created: 2009
Server Location: 🇩🇪 US (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mNo\u001b[0;00m\r\n\r\n\r\r\n ________________\r\r\n /\\ /\\\r\r\n / \\____________/ \\\r\r\n / / \\ \\\r\r\n / / \\ \\\r\r\n / / Welcome to \\ \\ \r\r\n /___/ Apothica \\___\\\r\r\n \\ \\ / /\r\r\n \\ \\ ____________ / /\r\r\n \\ \\ \\##########/ / /\r\r\n ,--, \\ \\ \\########/ / / ,--,\r\r\n )\"\"( \\ \\ \\######/ / / )\"\"(\r\r\n / \\ \\ \\ \\####/ / / /.nn.\\\r\r\n / \\ \\ \\ \\##/ / / /$$$$$$\\\r\r\n . . \\ \\ \\/ / / .$$$$$$$$.\r\r\n |'-....-'| \\ \\ / / |\"*$$$$*\"|\r\r\n | | __ \\ \\/_ /_ _ | |\r\r\n | | / | ____ ___\\ / /_/ /_ (_)________ _ | |\r\r\n |'-....-'| / /| | / __ \\/ __ \\/ __/ __ \\/ / ___/ __ '/ |8n....n8|\r\r\n | | / ___ |/ /_/ / /_/ / /_/ / / / / /__/ /_/ / |$$$$$$$$|\r\r\n | | /_/ |_/ .___/\\____/\\__/_/ /_/_/\\___/\\__,_/ |$$$$$$$$|\r\r\n '-....-' mh /_/ \"*$$$$*\" \r\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"CODEBASE": "tbaMUD",
"CONTACT": "colt.adams45@yahoo.com",
"CRAWL DELAY": "-1",
"CREATED": "2009",
"DBSIZE": "52950",
"HOSTNAME": "azereth.vineyard.haus",
"LANGUAGE": "English",
"LOCATION": "US",
"MINIMUM AGE": "16",
"MOBILES": "8790",
"NAME": "Apothica",
"OBJECTS": "10309",
"PLAYERS": "0",
"PORT": "8000",
"ROOMS": "33641",
"UPTIME": "1770566032",
"WEBSITE": "https://azerethmud.weebly.com/"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 3.7223472595214844
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:43.555154+00:00",
"host": "apothica.kozow.com",
"ip": "176.9.151.147",
"port": 6464
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug apothica.kozow.com 6464
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=apothica.kozow.com port=6464
ERROR client.py:1318 apothica.kozow.com:6464: [Errno 111] Connect call failed ('176.9.151.147', 6464)
Azereth (azereth.vineyard.haus:8000)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes /===-_---~~~~~~~------___ ,;'\\ Welcome to: //~\\\\ ~~~~'---.______,-' _.~;';','\\\\ \*\*AZERETH\*\* \| \| \\\\ _-~' __--~ ,-/ /'\\\\ \| \| '\\ ,' _-~ /' \| \\\\ / / \\ / .' / \| \\\\ /' / \\ /' / ____ / \| \\\\ _.~~~\*,,\*~.__/' / \\/' /-'~ ~~~~~---__ \| ~-/~ /' _-~' \\_\| / __--_ ), __--~~ '~~--_/ _-~_>--<_\\ '-~\\ {\\__--_/} / \\\\__>--<_\\ \\ /' (_/ _-~ \| \|__>--<_\| ; __ _____\| _/) )_/ __/_/__ --___\|___ ~_______ __ __ / \\ \|____ / /~ ,_/___\|\| _ \\-\| ____\|\|__ __\|\| \| \| \| / _ \\ /o-o _//\|___ \| \|_\| \|\| \|___ / \| \| \| \|___\| \| / /_\\ \\ / (^(~\| ___\| \| _ /<\| ___\|' \| \| \| ___ \| / ___ \\ / ,/\| \| \|____ \| \|-\\ \\/\| \|__-~ \| \| \| \|; \| \| /__/ \\__\\\|,//('(\\\|\|_______\|\|__\|--\\__\\\|_______\| \|__\| \|__\| _-\|__\|\\ ( ( ')) \|__>--<__\| \| Created Oct. /' /; \|\| '-)) )) ( \\__>--<__\\ \\ 8th, 2000 /' // /' ,/,'//( ( ~-__>--<_~-_ ~--____---~' _/'/ ,( ( ((, )) ~-_~>--<_/-__ __-~ _/ '~/ ) ) ,/\| ~~-'_/_/ /~~~~~~~__--~ ._-~//( )/ )) ~~~~~~~~~~ Type WHO to see who is playing or enter a name to join in the fun.](../_images/banner_bdf6e4866526.png)
Server URLs
- Telnet: telnet://azereth.vineyard.haus:8000
- Website: https://azerethmud.weebly.com/
Server Info
Codebase: tbaMUD
Players online: 0 [12]
Uptime: 9 days
Created: 2009
Server Location: 🇩🇪 US (MSSP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Azereth"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\n /===-_---~~~~~~~------___\r\r\n ,;'\\ Welcome to: //~\\\\ ~~~~'---.______,-'\r\r\n _.~;';','\\\\ **AZERETH** | | \\\\ _-~'\r\r\n __--~ ,-/ /'\\\\ | | '\\ ,'\r\r\n _-~ /' | \\\\ / / \\ /\r\r\n .' / | \\\\ /' / \\ /'\r\r\n / ____ / | \\\\ _.~~~*,,*~.__/' / \\/' \r\r\n /-'~ ~~~~~---__ | ~-/~ /' _-~'\r\r\n \\_| / __--_ ), __--~~ \r\r\n '~~--_/ _-~_>--<_\\ '-~\\\r\r\n {\\__--_/} / \\\\__>--<_\\ \\\r\r\n /' (_/ _-~ | |__>--<_| ;\r\r\n __ _____| _/) )_/ __/_/__ --___|___ ~_______ __ __ \r\r\n / \\ |____ / /~ ,_/___|| _ \\-| ____||__ __|| | | |\r\r\n / _ \\ /o-o _//|___ | |_| || |___ / | | | |___| | \r\r\n / /_\\ \\ / (^(~| ___| | _ /<| ___|' | | | ___ |\r\r\n / ___ \\ / ,/| | |____ | |-\\ \\/| |__-~ | | | |; | |\r\r\n /__/ \\__\\|,//('(\\||_______||__|--\\__\\|_______| |__| |__| _-|__|\\\r\r\n ( ( ')) |__>--<__| | Created Oct. /' /; ||\r\r\n '-)) )) ( \\__>--<__\\ \\ 8th, 2000 /' // /'\r\r\n ,/,'//( ( ~-__>--<_~-_ ~--____---~' _/'/\r\r\n ,( ( ((, )) ~-_~>--<_/-__ __-~ _/\r\r\n '~/ ) ) ,/| ~~-'_/_/ /~~~~~~~__--~\r\r\n ._-~//( )/ )) ~~~~~~~~~~\r\r\nType WHO to see who is playing or enter a name to join in the fun.",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CODEBASE": "tbaMUD",
"CONTACT": "colt.adams45@yahoo.com",
"CRAWL DELAY": "-1",
"CREATED": "2009",
"DBSIZE": "52952",
"HOSTNAME": "azereth.vineyard.haus",
"LANGUAGE": "English",
"LOCATION": "US",
"MINIMUM AGE": "16",
"MOBILES": "8790",
"NAME": "Azereth",
"OBJECTS": "10309",
"PLAYERS": "0",
"PORT": "8000",
"ROOMS": "33641",
"UPTIME": "1774714794",
"WEBSITE": "https://azerethmud.weebly.com/"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.754718542098999
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:04.332559+00:00",
"host": "azereth.vineyard.haus",
"ip": "176.9.151.147",
"port": 8000
},
{
"connected": "2026-04-07T07:07:46.873645+00:00",
"host": "azereth.vineyard.haus",
"ip": "176.9.151.147",
"port": 8000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug azereth.vineyard.haus 8000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=azereth.vineyard.haus port=8000
INFO client_base.py:190 Connected to <Peer 176.9.151.147 8000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'Azereth'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'Azereth'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Azereth', 'PLAYERS': '0', 'UPTIME': '1774714794', 'CRAWL DELAY': '-1', 'HOSTNAME':
'azereth.vineyard.haus', 'PORT': '8000', 'CODEBASE': 'tbaMUD', 'CONTACT': 'colt.adams45@yahoo.com', 'CREATED': '2009',
'LANGUAGE': 'English', 'LOCATION': 'US', 'MINIMUM AGE': '16', 'WEBSITE': 'https://azerethmud.weebly.com/', 'MOBILES': '8790',
'OBJECTS': '10309', 'ROOMS': '33641', 'DBSIZE': '52952'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL ZMP, WILL GMCP, WILL MCCP2_COMPRESS, WILL MSDP, WILL MSSP, WILL
MCCP3_COMPRESS, WILL AARDWOLF, DO ZMP, DO MXP, DO GMCP, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO ATCP, DO AARDWOLF'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 8000>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
colossus.vineyard.haus:10000
Connection Banner:
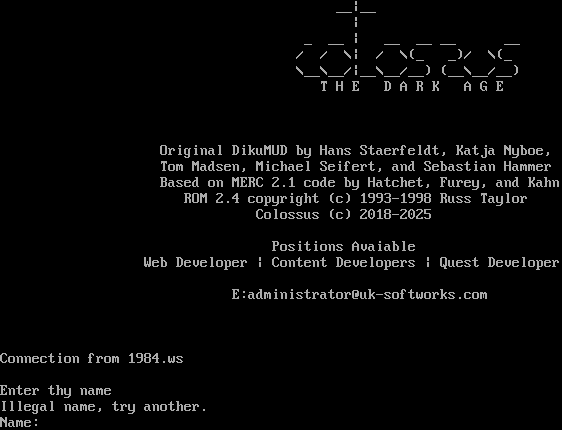
Server URLs
- Telnet: telnet://colossus.vineyard.haus:10000
- Website: uk-softworks.com
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal name, try another.\n\rName: ",
"banner_before_return": "\n\r __|__ \n\r | \n\r _ __ | __ __ __ __ \n\r / / \\| / \\(_ _)/ \\(_ \n\r \\__\\__/|__\\__/__) (__\\__/__)\n\r T H E D A R K A G E\n\r\n\r\n\r\n\r Original DikuMUD by Hans Staerfeldt, Katja Nyboe,\n\r Tom Madsen, Michael Seifert, and Sebastian Hammer\n\r Based on MERC 2.1 code by Hatchet, Furey, and Kahn\n\r ROM 2.4 copyright (c) 1993-1998 Russ Taylor\n\r Colossus (c) 2018-2025\n\r\n\r Positions Avaiable\n\r Web Developer | Content Developers | Quest Developer\n\r\n\r E:administrator@uk-softworks.com\n\r\n\r\n\n\rConnection from 1984.ws\n\n\rEnter thy name ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5050873756408691,
"total": 11.042711019515991
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:32.325035+00:00",
"host": "colossus.vineyard.haus",
"ip": "176.9.151.147",
"port": 10000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug colossus.vineyard.haus 10000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=colossus.vineyard.haus port=10000
ERROR client.py:1318 colossus.vineyard.haus:10000: [Errno 111] Connect call failed ('176.9.151.147', 10000)
Cowboy Bebop: The Galactic Bounty (cowboybebop.vineyard.haus:4020)
Connection Banner:
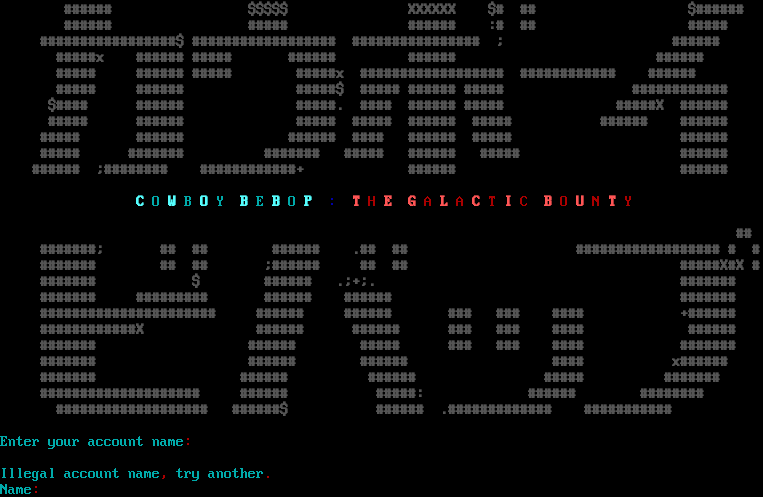
Server URLs
- Telnet: telnet://cowboybebop.vineyard.haus:4020
- Website: cowboybebop.vineyard.haus
Server Info
Codebase: Bebop 1.02
Genre: Sci-Fi Anime
Gameplay: Casual
Players online: 2 [13]
Uptime: 5 days
Created: 10 Aug 2025
Status: Beta
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Yes (MSSP)
MCCP: Yes (MSSP)
MCCP2: Negotiated
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 4 other servers.
Options offered by server: ECHO, MCCP2, MSDP, MSP, MSSP, MXP
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "47422ef44d0aacad",
"fingerprint-data": {
"offered-options": [
"ECHO",
"MCCP2",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Cowboy Bebop: The Galactic Bounty"
}
],
"banner_after_return": "\u001b[36m\n\rIllegal account name\u001b[31m,\u001b[36m try another\u001b[31m.\u001b[36m\nName\u001b[31m:\u001b[36m ",
"banner_before_return": "\u001b[1;30m \n ###### $$$$$ XXXXXX $# ## $###### \n ###### ##### ###### :# ## ##### \n #################$ ################## ################ ; ###### \n #####x ###### ##### ###### ###### ###### \n ##### ###### ##### #####x ################## ############ ###### \n ##### ###### #####$ ##### ###### ##### ############ \n $#### ###### #####. #### ###### ##### #####X ###### \n ##### ###### ##### ##### ###### ##### ###### ###### \n ##### ###### ###### #### ###### ##### ###### \n ##### ####### ####### ##### ###### ##### ###### \n ###### ;######## ############+ ###### ###### \n \n \u001b[36mC \u001b[0;36mO \u001b[1;36mW \u001b[0;36mB \u001b[1;36mO \u001b[0;36mY \u001b[1;36mB \u001b[0;36mE \u001b[1;36mB \u001b[0;36mO \u001b[1;36mP \u001b[0;34m: \u001b[1;31mT \u001b[0;31mH \u001b[1;31mE G \u001b[0;31mA \u001b[1;31mL \u001b[0;31mA \u001b[1;31mC \u001b[0;31mT \u001b[1;31mI \u001b[0;31mC \u001b[1;31mB \u001b[0;31mO \u001b[1;31mU \u001b[0;31mN \u001b[1;31mT \u001b[0;31mY \n\u001b[1;30m ## \n #######; ## ## ###### .## ## ################## # # \n ####### ## ## ;###### ## ## #####X#X # \n ####### $ ###### .;+;. ####### \n ####### ######### ###### ###### ####### \n ###################### ###### ###### ### ### #### +###### \n ############X ###### ###### ### ### #### ###### \n ####### ###### ##### ### ### #### ####### \n ####### ###### ###### #### x###### \n ####### ###### ###### ##### ####### \n #################### ###### #####: ###### ######## \n ################### ######$ ###### .############# ########### \n\n\u001b[0;36mEnter your account name\u001b[31m:\u001b[37m \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"ANSI": "1",
"CODEBASE": "Bebop 1.02",
"CONTACT": "bebopmud24@cowboybebop.vineyard.haus",
"CRAWL DELAY": "-1",
"CREATED": "10 Aug 2025",
"GAMEPLAY": "Casual",
"GAMESYSTEM": "Custom",
"GENRE": "Sci-Fi Anime",
"GMCP": "0",
"HOSTNAME": "cowboybebop.vineyard.haus",
"MCCP": "1",
"MCP": "0",
"MSDP": "1",
"MSP": "1",
"MXP": "1",
"NAME": "Cowboy Bebop: The Galactic Bounty",
"PLAYERS": "2",
"PORT": "4020",
"PUEBLO": "0",
"STATUS": "Beta",
"SUBGENRE": "Cowboy Bebop",
"UPTIME": "1772422170",
"UTF-8": "1",
"VT100": "0",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5095696449279785,
"total": 11.293933391571045
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:58:23.994634+00:00",
"host": "cowboybebop.vineyard.haus",
"ip": "176.9.151.147",
"port": 4020
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug cowboybebop.vineyard.haus 4020
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=cowboybebop.vineyard.haus port=4020
ERROR client.py:1318 cowboybebop.vineyard.haus:4020: [Errno 111] Connect call failed ('176.9.151.147', 4020)
darkeningsun.com:5678
Connection Banner:
![<VERSION> \|> Based on: /i\\ Welcome to Diku by Hans, Katya, \\ /#'\`\\ The Darkening Sun Tom, Michael and Sebastian \`\\ /#' \`\\ /\\ Merc 2.1 by Hatchet, \`\\ /#'-. \`\\/ \`\\ \|> Furey and Kahn \`\\ /#'-._ \`\\ \`\\ \| Rom 2.4 1993-1996 by Russ \`\\ /#'-.___ \`\\ \`\\ /'\\ Oblivion 2.0 1996-1997 ___--' '--.._____..--' \`\\/# \`\\ by Wes Wagner ,','\| \|- _ _-=\|_.- /# \`\\ The Dawn of Time v1.69s _-=} \|- {_} _-=\|. /#\`- \`\\ 1997-2010 by Michael Garratt -_=\| \|-________-=\| /#\`-._ \`\\ The Darkening Sun 2000-2022 []=\|_.-._ \\,_._._._./_ /#\`-.___ \`\\ by Marc Garrett -=/\* \`\\ \|-. _-=\| '--.._____..--' + ___ .-(-.._..-)\|- , _-=\| ()\|- ___..---.\| .--.\|__, .-' \`-. MMMMM. ,MMMMM. - \| . \| / / // \\ >'---.,___\\ .-' \`-. ][\`l--Ml][ \`] ,wwwwww// / / {} \\ \| l / \\ ][ ]I,_MI' ][ ] /__...-'\|""""_.- ,-===- ,===. \| / \\ n ][ ][ ][ "i] !_______\| \| \`I[ '\|_[ \| \| \| _ ,----, _ \| ][__][__][__][ ] /^ , /\\ \| ] ___ ] \| ,-' \|\| \|l \| \| ____/,./------/ / ^ ^ ;/ \\/=L ,.=-p q===,__J \|-_\| \*\* __ \*\* \| \| - _ -=##Y /______/ "" \\ \`\\Lt _-=J/ \| \|,,==p' q==,J / [] .- -=#l##_##_ " \| " " \|---\|- ^. _-=\|"-"-!-.-.-Y-' _=\| / - -=#l, ##-##_--.-.-.\|- / \\\\_-=\| .. , .-=\|- /\\=\| .-' _ - _;=#l:. ; . :\|- \|_LI_-=\|.. . . .-=\|- LJ=\|.-' ,.,,, __-=#l:. . : : ::::\|- _-=\| . .__. -=\|- _=\| ===.,,__-=#l:.:: ::: , ::::':\|- _-=\|, ./ \\\\. =\|- _=\| \|\|\|\|'.,_-=#l:: ::: . : ;::,::::\|- __ _-=\| .\| \|I =\|-_, %#\*!-._ \|\|\|\|\|'.,-=#l. ::: :;: ,:::\|- __ ___-=\|. \| -_\|I@,' \`-_ !!!!!{},-=#l:. . ;: , ::#:\|- ., __-=\| @\| "'-,_ . \|\|\|\|\|{},-=#l:.: ' : ##_.-!-_ /!%'\`, \`-,_ \|\|\|\|\|{}.-=#l:. .' : #_.-' %# v @ \`-. \`-,_ What is thy name, Brave Traveller? (Type 'new' to create a new character)<USER> You can't have a blank name, type 'new' to create a new character, 'quit' to disconnect, or type your characters name - try again. What is thy name, Brave Traveller? (Type 'new' to create a new character)](../_images/banner_0576e7410a61.png)
Server URLs
- Telnet: telnet://darkeningsun.com:5678
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 5 other servers.
Options offered by server: MCCP2, MSP, MXP
Options requested from client: TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "9e7fd90d3aff78af",
"fingerprint-data": {
"offered-options": [
"MCCP2",
"MSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSSP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "You can't have a blank name, type 'new' to create a new character,\r\n'quit' to disconnect, or type your characters name - try again.\r\n\u001b[1;37mWhat is thy name, Brave Traveller? \u001b[0;37m(Type '\u001b[1;36mnew\u001b[0;37m' to create a new character)",
"banner_before_return": "\r\n\u001b[1z<VERSION>\u001b[6z\r\n\u001b[0;31m |> \u001b[0;37mBased on:\n\r\u001b[0;31m /\u001b[1;30mi\u001b[0;31m\\ \u001b[1;37mWelcome to \u001b[0;37mDiku by Hans, Katya,\n\r\u001b[0;31m\\ /#'`\\ \u001b[1;37mThe Darkening Sun \u001b[0;37mTom, Michael and Sebastian\n\r\u001b[0;31m`\\ /#' `\\ /\\ \u001b[0;37mMerc 2.1 by Hatchet,\n\r\u001b[0;31m `\\ /#'-. `\\/ `\\ |> \u001b[0;37mFurey and Kahn\n\r\u001b[0;31m `\\ /#'-._ `\\ `\\ \u001b[1;30m| \u001b[0;37mRom 2.4 \udca91993-1996 by Russ\n\r\u001b[0;31m `\\ /#'-.___ `\\ `\\ /\u001b[1;30m'\u001b[0;31m\\ \u001b[0;37mOblivion 2.0 \udca91996-1997\n\r\u001b[0;31m___--' '--.._____..--' `\\/# `\\ \u001b[0;37mby Wes Wagner\n\r,\u001b[1;30m','| \u001b[1;37m|-\u001b[0;37m _ _-\u001b[1;30m=|\u001b[0;31m_.- /# `\\ \u001b[0;37mThe Dawn of Time v1.69s\n\r _-\u001b[1;30m=} \u001b[1;37m|-\u001b[0;37m {_} _-\u001b[1;30m=|. \u001b[0;31m/#`- `\\ \u001b[0;37m\udca91997-2010 by Michael Garratt\n\r -_\u001b[1;30m=| \u001b[1;37m|-\u001b[0;37m________-\u001b[1;30m=| \u001b[0;31m/#`-._ `\\ \u001b[0;37mThe Darkening Sun \udca92000-2022\n\r []\u001b[1;30m=|\u001b[0;35m_.-._ \u001b[1;37m\\,\u001b[0;37m_._.\u001b[1;30m_._./\u001b[0;37m_ \u001b[0;31m/#`-.___ `\\ \u001b[0;37mby Marc Garrett \n\r -\u001b[1;30m=\u001b[0;35m/* `\\\u001b[0;37m \u001b[1;37m|-.\u001b[0;37m _-\u001b[1;30m=| \u001b[0;31m'--.._____..--' \u001b[0;34m+ \u001b[1;33m___ \n\r\u001b[0;37m .-\u001b[0;35m(-.._..-)\u001b[0;37m\u001b[1;37m|- \u001b[0;37m, _-\u001b[1;30m=| ()\u001b[1;37m|\u001b[0;37m- \u001b[0;33m___..---.\u001b[1;30m| \u001b[0;34m.--.|__, \u001b[1;33m.-' `-.\n\r\u001b[0;37mMMMMM. ,MMMMM\u001b[1;30m. - | . \u001b[1;37m| \u001b[0;33m/ / // \\ \u001b[0;34m>'---.,___\\ \u001b[1;33m.-' `-.\n\r\u001b[0;37m ][`l--Ml][ `\u001b[1;30m] \u001b[0;37m,wwwwww\u001b[0;33m// / / \u001b[0;37m{}\u001b[0;33m \\\u001b[0;37m | l \u001b[1;33m/ \\\n\r\u001b[0;37m][ ]I,_MI' ][ \u001b[1;30m] \u001b[0;37m/__...-\u001b[0;33m'\u001b[0;37m|\u001b[0;33m\"\"\"\"\u001b[1;37m_.- \u001b[0;37m,-===- ,===\u001b[1;30m.\u001b[0;37m | \u001b[1;33m/ \\\n\r\u001b[0;37mn ][ ][ ][ \"\u001b[1;30mi] \u001b[0;37m!\u001b[0;36m_______\u001b[0;37m| \u001b[1;37m| `I\u001b[0;37m[ '|_\u001b[1;30m[ |\u001b[0;37m | \u001b[1;33m|\u001b[0;37m _ ,----,\u001b[1;30m _ \u001b[1;33m| \n\r\u001b[0;37m][__][__][__]\u001b[1;30m[ ]\u001b[0;36m /^ , /\\ \u001b[1;37m| ] ___ \u001b[1;30m] \u001b[0;37m| ,-' || |l\u001b[1;30m |\u001b[1;33m |\n\r\u001b[0;37m____/,./----\u001b[1;30m--/ \u001b[0;36m/ ^ ^ ;/ \\\u001b[0;33m/=\u001b[1;37mL ,.\u001b[0;37m=-p q===\u001b[1;30m,__J \u001b[0;37m|\u001b[1;30m-_\u001b[1;37m| *\u001b[0;37m* __ **\u001b[1;30m | \u001b[0;33m|\n\r\u001b[0;37m- _ -=##\u001b[1;30mY \u001b[0;36m/______/ \u001b[1;30m\"\"\u001b[0;36m \\ \u001b[1;37m`\\L\u001b[0;37mt _-\u001b[1;30m=J/\u001b[0;37m | \u001b[1;37m|,,=\u001b[0;37m=p' q==\u001b[1;30m,J \u001b[0;33m/\n\r\u001b[0;37m[] .- -=#\u001b[1;30ml\u001b[1;37m##_##\u001b[0;37m_ \u001b[1;30m\" \u001b[0;37m| \u001b[1;30m\" \"\u001b[0;37m |\u001b[0;33m---\u001b[1;37m|-\u001b[0;37m ^. _-\u001b[1;30m=|\u001b[1;37m\"-\u001b[0;37m\"-!-.-.\u001b[1;30m-\u001b[1;37mY\u001b[0;37m-' _\u001b[1;30m=| \u001b[0;33m/\n\r\u001b[0;37m - -=#\u001b[1;30ml\u001b[1;37m, \u001b[0;37m##-##_--.-.-\u001b[1;30m.\u001b[1;37m|-\u001b[0;37m / \\\\_-\u001b[1;30m=|\u001b[1;37m .\u001b[0;37m. , .-\u001b[1;30m=\u001b[1;37m|\u001b[0;37m- /\\\u001b[1;30m=| \u001b[0;33m.-' \n\r\u001b[0;37m_ - _;=#\u001b[1;30ml\u001b[1;37m:.\u001b[0;37m ; . \u001b[1;30m:\u001b[1;37m|-\u001b[0;37m |_LI_-\u001b[1;30m=|\u001b[1;37m.\u001b[0;37m. . . .-\u001b[1;30m=\u001b[1;37m|\u001b[0;37m- LJ\u001b[1;30m=|\u001b[0;33m.-' \n\r\u001b[0;37m,.,,, __-=#\u001b[1;30ml\u001b[1;37m:. \u001b[0;37m . : : :::\u001b[1;30m:\u001b[1;37m|-\u001b[0;37m _-\u001b[1;30m=| \u001b[0;37m. .__. -\u001b[1;30m=\u001b[1;37m|\u001b[0;37m- _\u001b[1;30m=| \n\r===.,\u001b[0;37m,__-=\u001b[1;30m#l\u001b[1;37m:.:\u001b[0;37m: ::: , ::::'\u001b[1;30m:\u001b[1;37m|-\u001b[0;37m _-\u001b[1;30m=|\u001b[0;37m, ./ \\\\. \u001b[1;30m=\u001b[1;37m|\u001b[0;37m- _\u001b[1;30m=| \n\r\u001b[0;33m||||\u001b[0;37m'\u001b[1;30m.\u001b[0;37m,_-=\u001b[1;30m#l\u001b[1;37m:: :\u001b[0;37m:: . : ;::,::\u001b[1;30m::\u001b[1;37m|-\u001b[0;37m __ _\u001b[1;30m-=|\u001b[0;37m .| |I \u001b[1;30m=|\u001b[0;37m-_, \u001b[0;32m%\u001b[0;36m#\u001b[0;32m*\u001b[1;30m!\u001b[0;32m-._\n\r\u001b[0;33m|||||\u001b[0;37m'\u001b[1;30m.\u001b[0;37m,-=\u001b[1;30m#l\u001b[1;37m. \u001b[0;37m ::: :;: ,:\u001b[1;30m::\u001b[1;37m|-\u001b[0;37m __ _\u001b[1;30m__-=|\u001b[1;37m.\u001b[0;37m | -_|I\u001b[0;32m@,' `-_\n\r\u001b[0;33m!!!!!\u001b[0;37m{}\u001b[1;30m,\u001b[0;37m-=\u001b[1;30m#l\u001b[1;37m:.\u001b[0;37m . ;: , :\u001b[1;30m:\u001b[0;32m#\u001b[1;30m:\u001b[1;37m|-\u001b[0;37m ., \u001b[1;30m__-=| \u001b[0;32m@\u001b[0;37m| \"'\u001b[0;32m-\u001b[0;33m,\u001b[0;32m_ . \n\r\u001b[0;33m|||||\u001b[0;37m{}\u001b[1;30m,\u001b[0;37m-=\u001b[1;30m#l\u001b[1;37m:.\u001b[0;37m: ' : \u001b[0;32m##_.-\u001b[1;37m!-\u001b[0;37m_ /\u001b[1;30m!\u001b[0;32m%'`, `-,_\n\r\u001b[0;33m|||||\u001b[0;37m{}\u001b[1;30m.\u001b[0;37m-=\u001b[1;30m#l\u001b[1;37m:.\u001b[0;37m .' : \u001b[0;32m#_.-' \u001b[0;36m\u001b[0;32m %# v @ `-. `-,_\n\r\u001b[1;37mWhat is thy name, Brave Traveller? \u001b[0;37m(Type '\u001b[1;36mnew\u001b[0;37m' to create a new character)<USER>",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true,
"MSP": true,
"MXP": true
},
"server_requested": {
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5042061805725098,
"total": 11.324104309082031
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:57:28.661394+00:00",
"host": "darkeningsun.com",
"ip": "176.9.151.147",
"port": 5678
},
{
"connected": "2026-04-07T07:13:11.637747+00:00",
"host": "darkeningsun.com",
"ip": "176.9.151.147",
"port": 5678
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug darkeningsun.com 5678
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=darkeningsun.com port=5678
INFO client_base.py:190 Connected to <Peer 176.9.151.147 5678>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSDP, WILL ZMP, WILL MSP, WILL MCCP2_COMPRESS, WILL AARDWOLF, WILL MXP, WILL ATCP,
WILL MCCP3_COMPRESS, WILL MSSP, WILL GMCP, DO MSDP, DO ZMP, DO AARDWOLF, DO ATCP, DO MCCP3_COMPRESS, DO MSSP, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 9e7fd90d3aff78af
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 5678>
dibrovamud.com:9000
Connection Banner:
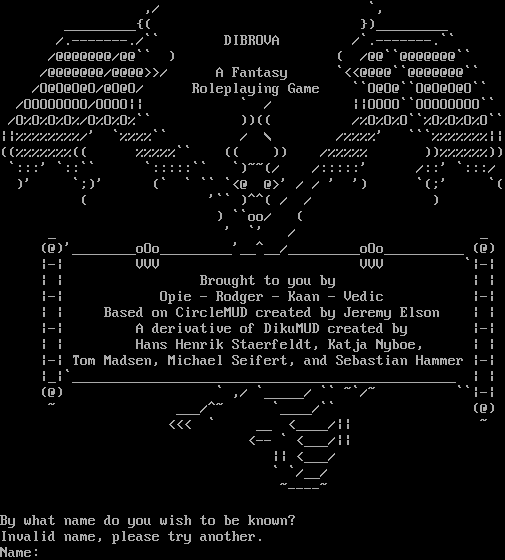
Server URLs
- Telnet: telnet://dibrovamud.com:9000
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Invalid name, please try another.\r\nName: ",
"banner_before_return": "\r\n\r\n ,/ `,\r\n _________{( })_________\r\n /.-------./`` DIBROVA /`.-------.``\r\n /@@@@@@@/@@`` ) ( /@@``@@@@@@@``\r\n /@@@@@@@/@@@@>>/ A Fantasy `<<@@@@``@@@@@@@``\r\n /O@O@O@O/@O@O/ Roleplaying Game ``O@O@``O@O@O@O``\r\n /OOOOOOOO/OOOO|| ` / ||OOOO``OOOOOOOO``\r\n /O%O%O%O%/O%O%O%`` ))(( /%O%O%O``%O%O%O%O``\r\n||%%%%%%%%/' `%%%%`` / \\ /%%%%' ```%%%%%%%||\r\n((%%%%%%%(( %%%%%`` (( )) /%%%%% ))%%%%%%))\r\n `:::' `::`` `:::::`` `)~~(/ /:::::' /::' `:::/\r\n )' `;)' (` ` `` `<@ @>' / / ' ') `(;' `(\r\n ( '`` )^^( / / )\r\n ) ``oo/ (\r\n _ ' `' / _\r\n (@)'________oOo_________'__^__/_________oOo__________ (@)\r\n |-| VVV VVV `|-|\r\n | | Brought to you by | |\r\n |-| Opie - Rodger - Kaan - Vedic |-|\r\n | | Based on CircleMUD created by Jeremy Elson | |\r\n |-| A derivative of DikuMUD created by |-|\r\n | | Hans Henrik Staerfeldt, Katja Nyboe, | |\r\n |-| Tom Madsen, Michael Seifert, and Sebastian Hammer |-|\r\n |_|`________________________________________________ | |\r\n (@) ` ,/ `_____/ `` ~`/~ ``|-|\r\n ~ ___/^~ `____/`` (@)\r\n <<< ` __ <____/|| ~\r\n <-- ` <___/||\r\n || <___/\r\n ` `/__/\r\n ~----~\r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.504197359085083,
"total": 11.261458396911621
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:35.116176+00:00",
"host": "dibrovamud.com",
"ip": "176.9.151.147",
"port": 9000
},
{
"connected": "2026-04-07T07:03:09.889541+00:00",
"host": "dibrovamud.com",
"ip": "176.9.151.147",
"port": 9000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug dibrovamud.com 9000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=dibrovamud.com port=9000
INFO client_base.py:190 Connected to <Peer 176.9.151.147 9000>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSDP, WILL ATCP, WILL MSSP, WILL ZMP, WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL
MCCP3_COMPRESS, WILL MSP, WILL MXP, WILL GMCP, DO MSDP, DO ATCP, DO MSSP, DO ZMP, DO AARDWOLF, DO MCCP2_COMPRESS, DO
MCCP3_COMPRESS, DO MSP, DO MXP, DO GMCP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 9000>
tbaMUD (infiniumgame.com:6060)
Connection Banner:
![__ __ __ ______ __ __ __ __ __ __ __ __ /\\ \\ /\\ "-.\\ \\ /\\ ___\\/\\ \\ /\\ "-.\\ \\ /\\ \\ /\\ \\/\\ \\ /\\ "-./ \\ \\ \\ \\\\ \\ \\-. \\\\ \\ __\\\\ \\ \\\\ \\ \\-. \\\\ \\ \\\\ \\ \\_\\ \\\\ \\ \\-./\\ \\ \\ \\_\\\\ \\_\\\\"\\_\\\\ \\_\\ \\ \\_\\\\ \\_\\\\"\\_\\\\ \\_\\\\ \\_____\\\\ \\_\\ \\ \\_\\ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_____/ \\/_/ \\/_/ A Unique Multi-User Dimension (MUD) Experience Original DikuMUD by Hans Staerfeldt, Katja Nyboe Tom Madsen, Michael Seifert, and Sebastian Hammer (/((((/// ((((((((((((((,\*\*\*//[ ((((((((((/\*,. .....,.,,,,\*,..\* ( ((((((((/,..,.,,,.\*\*\*\*,\*\*\*\*\*\*\*\*,,\*\* \*\* ( ((((/...,,,,,\*,/\*\*\*,/\*\*/\*\*\*//\*,\*\*\*\*\*/ // ((/(/,.,.,,\*,\*,\*\*/\*/,,,/\*\*\*\*\*\*/\*/(/\*\*///// \*\*, ((,...,,,,\*\*\*\*,\*\*\*//\*\*//\*/,((//\*\*/\*((((/\*(/\* ((// ((((...,,\*\*,\*\*,\*,\*/\*\*\*\*////////\*(//(/((((///\* // ////(/ ((((,.,,,,\*\*\*/,\*/\*/\*(//\*/ \*\*\*//\*(\*/( \*/( \*//(/(\*(/ / (\*((/ ((/..,,\*,,\*\*\*\*/\*\*\*\*/\*\*\*\*((/\*\*/((// (((\*\*\*\*/((// /(/ // (/(\*\* ((\*.,,,\*,/\*/\*\*\*(//(/(\*/ (\*(\*( (((((/\*///(\*//(((///((\*/(( (\*\*( / ((\*\*..,,\*\*\*,\*\*\*(/\*\*/,(\*/((/( / ((\*( ((((/ /(/\* ( //(\*(/(((\*/\* \*(/ ((\*.,,\*,/\*\*,//\*\*(\*\*\*/ /\*((((\*( \*/( /\*/\*((/((/ ///\*//\*/(( ((( /(/ \*.% ((,,.,,,/\*\* (\*/(///\*//// \*//(/ ( (/( \*\*/\*(/ \*((\*//(( / (/(\*\* / // (( [Login]](../_images/banner_bc9db79f777d.png)
Server URLs
- Telnet: telnet://infiniumgame.com:6060
Server Info
Players online: 1 [14]
Uptime: 10 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "tbaMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J \u001b[38;5;051m __ __ __ ______ __ __ __ __ __ __ __ __\r\n \u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;051m\"-.\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\ ___\u001b[38;5;033m\\\u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;051m\"-.\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\\u001b[38;5;033m \\\u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;033m\\ \u001b[38;5;024m/\u001b[38;5;033m\\ \u001b[38;5;051m\"-.\u001b[38;5;024m/ \u001b[38;5;033m\\\r\n \u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\-. \\\u001b[38;5;024m\\ \u001b[38;5;033m\\ __\u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\-. \u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\\u001b[38;5;033m \\_\u001b[38;5;033m\\ \u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\ \u001b[38;5;033m\\-./\u001b[38;5;033m\\ \u001b[38;5;033m\\\r\n \u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;033m\\\"\\_\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\ \u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;033m\\\"\u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_____\\\u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\ \u001b[38;5;024m\\ \u001b[38;5;033m\\_\u001b[38;5;033m\\\r\n \u001b[38;5;024m\\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_/ \\/_____/ \\/_/ \\/_/\u001b[0;00m\r\n \r\n \u001b[38;5;231mA Unique Multi-User Dimension (MUD) Experience\u001b[0;00m\r\n \u001b[38;5;059mOriginal DikuMUD by Hans Staerfeldt, Katja Nyboe\r\n Tom Madsen, Michael Seifert, and Sebastian Hammer\u001b[0;00m\r\n \r\n \r\n \r\n \r\n \r\n \r\n \r\n \r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n \u001b[38;5;214m(/((((///\r\n ((((((((((((((\u001b[38;5;088m,***\u001b[38;5;196m//[\r\n \u001b[38;5;214m((((((((((/\u001b[38;5;088m*,. \u001b[38;5;196m....\u001b[38;5;226m.\u001b[38;5;231m,\u001b[38;5;226m.\u001b[38;5;145m,\u001b[38;5;231m,,\u001b[38;5;226m,*,.\u001b[38;5;231m.*\r\n ( \u001b[38;5;214m((((((((\u001b[38;5;088m/,.\u001b[38;5;196m.,.\u001b[38;5;226m,,\u001b[38;5;231m,.\u001b[38;5;226m**\u001b[38;5;231m**,**\u001b[38;5;226m***\u001b[38;5;231m*\u001b[38;5;226m**\u001b[38;5;231m,,*\u001b[38;5;226m* *\u001b[38;5;231m*\r\n ( \u001b[38;5;214m((((/\u001b[38;5;088m.\u001b[38;5;196m..,\u001b[38;5;226m,,\u001b[38;5;231m,\u001b[38;5;226m,*,/***,/*\u001b[38;5;231m*/***//*\u001b[38;5;145m,*\u001b[38;5;226m**\u001b[38;5;231m*\u001b[38;5;226m*/ /\u001b[38;5;231m/\r\n \u001b[38;5;214m((/(/\u001b[38;5;088m,.\u001b[38;5;196m,.,\u001b[38;5;226m,*,\u001b[38;5;231m*,\u001b[38;5;226m**/*/,,\u001b[38;5;145m,/*\u001b[38;5;231m**\u001b[38;5;226m*\u001b[38;5;145m*\u001b[38;5;226m*/*/(/*\u001b[38;5;226m*//\u001b[38;5;231m//\u001b[38;5;145m/ *\u001b[38;5;226m*,\r\n \u001b[38;5;214m((,\u001b[38;5;088m..\u001b[38;5;196m.,,,\u001b[38;5;226m,*\u001b[38;5;231m*\u001b[38;5;226m**,*\u001b[38;5;226m**//*\u001b[38;5;226m*//\u001b[38;5;145m*/,((//**/\u001b[38;5;145m*((\u001b[38;5;226m((/*(\u001b[38;5;226m/\u001b[38;5;145m* (\u001b[38;5;231m(\u001b[38;5;226m//\r\n \u001b[38;5;214m(((\u001b[38;5;088m(..\u001b[38;5;196m.,,*\u001b[38;5;226m*,*\u001b[38;5;231m*,\u001b[38;5;226m*,*/\u001b[38;5;145m**\u001b[38;5;226m**/\u001b[38;5;145m/\u001b[38;5;226m////\u001b[38;5;226m//*(//\u001b[38;5;226m(/\u001b[38;5;231m((\u001b[38;5;145m((\u001b[38;5;226m//\u001b[38;5;226m/* // ///\u001b[38;5;226m/(/\r\n \u001b[38;5;214m((((\u001b[38;5;088m,.,\u001b[38;5;196m,,,*\u001b[38;5;226m*\u001b[38;5;145m*\u001b[38;5;231m/,\u001b[38;5;226m*/\u001b[38;5;231m*\u001b[38;5;145m/*(/\u001b[38;5;231m/*/ \u001b[38;5;145m***//\u001b[38;5;145m*(\u001b[38;5;226m*/( */\u001b[38;5;145m( *//(/(\u001b[38;5;145m*(/ / (*((/\r\n \u001b[38;5;214m((/\u001b[38;5;088m..,\u001b[38;5;196m,*,,*\u001b[38;5;226m**\u001b[38;5;231m*/\u001b[38;5;226m***\u001b[38;5;231m*/*\u001b[38;5;226m**\u001b[38;5;231m*\u001b[38;5;145m((/*\u001b[38;5;231m*/(\u001b[38;5;226m(// (\u001b[38;5;226m((*\u001b[38;5;231m*\u001b[38;5;145m**/(\u001b[38;5;226m(/\u001b[38;5;231m/ /(\u001b[38;5;226m/ \u001b[38;5;231m// (/(\u001b[38;5;226m*\u001b[38;5;231m*\r\n \u001b[38;5;214m((*\u001b[38;5;088m.\u001b[38;5;196m,,,*,/*\u001b[38;5;226m/*\u001b[38;5;231m**\u001b[38;5;226m(//(/(*/\u001b[38;5;145m (*(\u001b[38;5;226m*(\u001b[38;5;231m ((\u001b[38;5;145m(\u001b[38;5;226m((/*/\u001b[38;5;226m//(*//(((\u001b[38;5;226m//\u001b[38;5;231m/\u001b[38;5;145m((*/\u001b[38;5;226m(( (*\u001b[38;5;231m*( /\r\n \u001b[38;5;214m ((**.\u001b[38;5;088m.,,*\u001b[38;5;196m**,\u001b[38;5;226m**\u001b[38;5;231m*(\u001b[38;5;226m/**/,\u001b[38;5;226m(*/\u001b[38;5;145m((/( / \u001b[38;5;145m((*( ((\u001b[38;5;226m((/ /(/* ( //(*(/(((*/* *(/\r\n \u001b[38;5;214m((*\u001b[38;5;088m.,,\u001b[38;5;196m*,/**\u001b[38;5;226m,/\u001b[38;5;231m/*\u001b[38;5;226m*(*\u001b[38;5;145m\u001b[38;5;226m**/ /\u001b[38;5;145m*(\u001b[38;5;231m((\u001b[38;5;226m(*( */(\u001b[38;5;226m /*\u001b[38;5;231m/*((/(\u001b[38;5;226m(/ \u001b[38;5;145m/\u001b[38;5;145m//*/\u001b[38;5;226m/*/\u001b[38;5;145m(( \u001b[38;5;226m((( /(/ *.%\r\n \u001b[38;5;214m((\u001b[38;5;088m,,.\u001b[38;5;196m,,,/\u001b[38;5;226m*\u001b[38;5;145m*\u001b[38;5;231m (*\u001b[38;5;226m/(//\u001b[38;5;226m/*//\u001b[38;5;226m// *//\u001b[38;5;226m(/ ( (/\u001b[38;5;226m( **/\u001b[38;5;226m*(\u001b[38;5;145m/ *((\u001b[38;5;226m*//(( \u001b[38;5;226m/ (/\u001b[38;5;226m(** / /\u001b[38;5;145m/ ((\r\n\u001b[0;00m[Login]",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "tbaMUD",
"PLAYERS": "1",
"UPTIME": "1774631753"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.7397496700286865
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:01:59.301618+00:00",
"host": "infiniumgame.com",
"ip": "176.9.151.147",
"port": 6060
},
{
"connected": "2026-04-07T07:09:22.384623+00:00",
"host": "infiniumgame.com",
"ip": "176.9.151.147",
"port": 6060
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug infiniumgame.com 6060
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=infiniumgame.com port=6060
INFO client_base.py:190 Connected to <Peer 176.9.151.147 6060>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'tbaMUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'tbaMUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'tbaMUD', 'PLAYERS': '1', 'UPTIME': '1774631753', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL MCCP2_COMPRESS, WILL MSDP, WILL MSSP, WILL MCCP3_COMPRESS, WILL ZMP, WILL
AARDWOLF, WILL GMCP, DO MXP, DO MCCP2_COMPRESS, DO ATCP, DO MCCP3_COMPRESS, DO ZMP, DO AARDWOLF, DO GMCP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 6060>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
kotl.org:2221
Connection Banner:
![_ _ ( \| / ) \\\|/ /' \|\\ . ,_ ,_ _ / _ ,_ _ ,' (_\| \\_)_/_/ (_(_/_(_/_(_)_/ ( (_/_)_ _ /__________ /\\ (_/ Email the owners at: \|/ _/_ /_ _ Chalgyr Vokel (_)_/\| _/__/ (_(/ Chalgyr@yahoo.com -----\|\\ Gillian Verity _ \\/ Herberkids3@yahoo.com ( \| \| _\|_ \| _ , / _\|____)_/(_)_/_)_/(____ ( ) ____ .'\* \*.' __/_\*_\*(_ / _______ \\ _\\_)/___\\(_/_ /\*_((\\- -/))_\*\\ \\\*\\())(-)(()/\*/ '\*\\(((()))/\*' / '\*\\)).))/\*' \\ / _ \\ - \| - /_ \\ ( ( .;''';. .' ) _\\"__ / )\\ __"/_ \\/ \\ ' / \\/ .' '...' ' ) / / \*\|\* \\ \\ / . \* . \* . \\ / . \* . \* \\ / \* / \* \| \* \\ \* \\ .' \* / \* b \* '. '. _.-' \* / \* Bb \* '-. '-._ _.-' \* \| \* BBb \* '-. '-. (________mrf\\____.dBBBb.________)____) _,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,_ Kingdoms of the Lost is based on: Original DikuMUD by Hans Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer Based on MERC 2.1 code by Hatchet, Furey, and Kahn ROM 2.4 copyright (c) 1993-1996 Russ Taylor _,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,__,.-'-'-.,_ [Press Return to continue] ________________---===) Kingdoms of the Lost (===---________________ [1] Logon to KoTL [5] Disconnect [2] Who is Online [6] Create a Character [3] Change player password [7] Announcements [4] Read the story of KoTL [8] Toggle color on/off _________________---===) Game Status: Open (===---_________________ ________________---===) Kingdoms of the Lost (===---________________ [1] Logon to KoTL [5] Disconnect [2] Who is Online [6] Create a Character [3] Change player password [7] Announcements [4] Read the story of KoTL [8] Toggle color on/off _________________---===) Game Status: Open (===---________________\_](../_images/banner_6d0219106f52.png)
Server URLs
- Telnet: telnet://kotl.org:2221
- Website: yahoo.com
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[2J\n\r\n\r \u001b[1;30m________________---\u001b[0;37m===\u001b[1;36m) \u001b[1;37mKingdoms of the Lost \u001b[1;36m(\u001b[0;37m===\u001b[1;30m---________________\u001b[0;37m\u001b[0;37m\n\r\n\r \u001b[0;37m[\u001b[1;36m1\u001b[0;37m] \u001b[0;36m\u001b[0;36mLogon to KoTL \u001b[0;37m[\u001b[1;36m5\u001b[0;37m] \u001b[0;36m\u001b[0;36mDisconnect \n\r\n\r \u001b[0;37m[\u001b[1;36m2\u001b[0;37m] \u001b[0;36m\u001b[0;36mWho is Online \u001b[0;37m[\u001b[1;36m6\u001b[0;37m] \u001b[0;36m\u001b[0;36mCreate a Character \n\r\n\r \u001b[0;37m[\u001b[1;36m3\u001b[0;37m] \u001b[0;36m\u001b[0;36mChange player password \u001b[0;37m[\u001b[1;36m7\u001b[0;37m] \u001b[0;36m\u001b[0;36mAnnouncements \n\r\n\r \u001b[0;37m[\u001b[1;36m4\u001b[0;37m] \u001b[0;36m\u001b[0;36mRead the story of KoTL \u001b[0;37m[\u001b[1;36m8\u001b[0;37m] \u001b[0;36m\u001b[0;36mToggle color on/off \n\r\n\r\n\r \u001b[1;30m_________________---\u001b[0;37m===\u001b[1;36m) \u001b[1;37mGame Status: Open \u001b[1;36m(\u001b[0;37m===\u001b[1;30m---_________________\u001b[0;37m\u001b[0;37m\n\r\n\r\u001b[2J\n\r\n\r \u001b[1;30m________________---\u001b[0;37m===\u001b[1;36m) \u001b[1;37mKingdoms of the Lost \u001b[1;36m(\u001b[0;37m===\u001b[1;30m---________________\u001b[0;37m\u001b[0;37m\n\r\n\r \u001b[0;37m[\u001b[1;36m1\u001b[0;37m] \u001b[0;36m\u001b[0;36mLogon to KoTL \u001b[0;37m[\u001b[1;36m5\u001b[0;37m] \u001b[0;36m\u001b[0;36mDisconnect \n\r\n\r \u001b[0;37m[\u001b[1;36m2\u001b[0;37m] \u001b[0;36m\u001b[0;36mWho is Online \u001b[0;37m[\u001b[1;36m6\u001b[0;37m] \u001b[0;36m\u001b[0;36mCreate a Character \n\r\n\r \u001b[0;37m[\u001b[1;36m3\u001b[0;37m] \u001b[0;36m\u001b[0;36mChange player password \u001b[0;37m[\u001b[1;36m7\u001b[0;37m] \u001b[0;36m\u001b[0;36mAnnouncements \n\r\n\r \u001b[0;37m[\u001b[1;36m4\u001b[0;37m] \u001b[0;36m\u001b[0;36mRead the story of KoTL \u001b[0;37m[\u001b[1;36m8\u001b[0;37m] \u001b[0;36m\u001b[0;36mToggle color on/off \n\r\n\r\n\r \u001b[1;30m_________________---\u001b[0;37m===\u001b[1;36m) \u001b[1;37mGame Status: Open \u001b[1;36m(\u001b[0;37m===\u001b[1;30m---_________________\u001b[0;37m\u001b[0;37m\n\r\n\r",
"banner_before_return": "\n\r\u001b[1;35m _ _\n\r\u001b[1;35m ( | / )\n\r\u001b[1;35m \\|/ /'\n\r\u001b[1;35m |\\ . ,_ ,_ _ / _ ,_ _ ,'\n\r\u001b[1;35m (_| \\_)_/_/ (_(_/_(_/_(_)_/ ( (_/_)_\n\r\u001b[1;35m _ /__________\n\r\u001b[1;30m /\\\u001b[1;35m (_/ \u001b[1;30mEmail the owners at:\n\r\u001b[1;30m |/ _/_ /_ _ \u001b[1;31mChalgyr Vokel\u001b[1;30m\n\r\u001b[1;30m (_)_/| _/__/ (_(/ \u001b[0;36mChalgyr@yahoo.com \u001b[1;30m\n\r\u001b[1;30m -----|\\ \u001b[1;32mGillian Verity\u001b[1;30m\n\r\u001b[1;35m _ \u001b[1;30m \\/ \u001b[0;36mHerberkids3@yahoo.com \u001b[1;30m\n\r\u001b[1;35m ( | \n\r\u001b[1;35m | _|_ \n\r\u001b[1;35m \u001b[1;35m| _ , /\n\r\u001b[1;35m \u001b[1;35m _|____)_/(_)_/_)_/(____\n\r\u001b[1;35m \u001b[1;35m( )\n\r\u001b[0;35m ____\n\r\u001b[0;35m .'\u001b[1;33m* *\u001b[0;35m.'\n\r\u001b[0;35m __/_\u001b[1;33m*\u001b[0;35m_\u001b[1;33m*\u001b[0;35m(_\n\r\u001b[0;35m / _______ \\\n\r\u001b[0;35m _\\_)\u001b[0;37m/___\\\u001b[0;35m(_/_\n\r\u001b[0;35m /\u001b[1;33m*\u001b[0;35m_\u001b[0;37m((\\\u001b[1;34m- -\u001b[0;37m/))\u001b[0;35m_\u001b[1;33m*\u001b[0;35m\\\n\r\u001b[0;35m \\\u001b[1;33m*\u001b[0;35m\\\u001b[0;37m())(\u001b[1;31m-\u001b[0;37m)(()\u001b[0;35m/\u001b[1;33m*\u001b[0;35m/\n\r\u001b[0;35m '\u001b[1;33m*\u001b[0;35m\\\u001b[0;37m(((()))\u001b[0;35m/\u001b[1;33m*\u001b[0;35m'\n\r\u001b[0;35m / '\u001b[1;33m*\u001b[0;35m\\\u001b[0;37m)).))\u001b[0;35m/\u001b[1;33m*\u001b[0;35m' \\\n\r\u001b[0;35m / _ \u001b[1;36m\\\u001b[0;35m - \u001b[1;36m|\u001b[0;35m -\u001b[1;36m /\u001b[0;35m_ \\\n\r\u001b[0;35m ( ( \u001b[1;36m.;''';.\u001b[0;35m .' )\n\r\u001b[1;36m _\u001b[0;35m\\\"\u001b[1;36m__ / \u001b[1;37m)\u001b[1;36m\\ __\u001b[0;35m\"/\u001b[1;36m_\n\r\u001b[0;35m \\/ \u001b[1;36m\\ \u001b[1;37m' \u001b[1;36m/\u001b[0;35m \\/\n\r\u001b[0;35m .' \u001b[1;36m'...'\u001b[0;35m ' )\n\r\u001b[0;35m / \u001b[1;36m/ \u001b[1;33m*\u001b[1;36m|\u001b[1;33m*\u001b[1;36m \\\u001b[0;35m \\\n\r\u001b[0;35m / \u001b[0;36m. \u001b[1;33m* \u001b[0;36m.\u001b[1;33m *\u001b[0;36m .\u001b[0;35m \\\n\r\u001b[0;35m / \u001b[0;36m.\u001b[1;33m * \u001b[0;36m. \u001b[1;33m*\u001b[0;35m \\\n\r\u001b[0;35m / \u001b[1;33m*\u001b[0;35m / \u001b[1;33m* \u001b[0;35m| \u001b[1;33m* \u001b[0;35m\\ \u001b[1;33m*\u001b[0;35m \\\n\r\u001b[0;35m .' \u001b[1;33m* \u001b[0;35m/ \u001b[1;33m* \u001b[1;35mb\u001b[1;33m *\u001b[0;35m '. '.\n\r\u001b[0;35m _.-' \u001b[1;33m*\u001b[0;35m / \u001b[1;33m* \u001b[1;35mBb\u001b[1;33m *\u001b[0;35m '-. '-._\n\r\u001b[0;35m _.-' \u001b[1;33m*\u001b[0;35m | \u001b[1;33m* \u001b[1;35mBBb\u001b[1;33m *\u001b[0;35m '-. '-.\n\r\u001b[0;35m (________\u001b[1;35mmrf\u001b[0;35m\\____\u001b[1;35m.dBBBb.\u001b[0;35m________)____)\n\r\u001b[0;35m _,.-'-'-.,_\u001b[1;35m_,.-'-'-.,_\u001b[1;37m_,.-'-'-.,__,.-'-'-.,_\u001b[1;35m_,.-'-'-.,_\u001b[0;35m_,.-'-'-.,_\n\r\u001b[1;35m Kingdoms \u001b[1;30mof the \u001b[1;35mLost \u001b[1;30mis based on:\n\r\u001b[0;37m\n\r Original DikuMUD by Hans Staerfeldt, Katja Nyboe,\n\r Tom Madsen, Michael Seifert, and Sebastian Hammer\n\r Based on MERC 2.1 code by Hatchet, Furey, and Kahn\n\r ROM 2.4 copyright (c) 1993-1996 Russ Taylor\n\r\u001b[1;37m _,.-'-'-.,_\u001b[1;35m_,.-'-'-.,_\u001b[0;35m_,.-'-'-.,__,.-'-'-.,_\u001b[1;35m_,.-'-'-.,_\u001b[1;37m_,.-'-'-.,_\u001b[0;37m\n\r \n\r\u001b[1;30m[\u001b[0;36mPress \u001b[1;36mReturn\u001b[0;36m to continue\u001b[1;30m]\u001b[0;37m\n\r \n\r",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5049893856048584,
"total": 16.532015562057495
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:55:26.504336+00:00",
"host": "kotl.org",
"ip": "176.9.151.147",
"port": 2221
},
{
"connected": "2026-04-07T06:52:58.063567+00:00",
"host": "kotl.org",
"ip": "176.9.151.147",
"port": 2221
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug kotl.org 2221
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=kotl.org port=2221
INFO client_base.py:190 Connected to <Peer 176.9.151.147 2221>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MCCP2_COMPRESS, WILL ZMP, WILL AARDWOLF, WILL MSSP, WILL MXP,
WILL GMCP, WILL MSDP, WILL ATCP, WILL MSP, DO MCCP3_COMPRESS, DO MCCP2_COMPRESS, DO ZMP, DO AARDWOLF, DO MSSP, DO MXP, DO
GMCP, DO MSDP, DO ATCP, DO MSP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 2221>
mud.darkrisings.org:1313
Connection Banner:
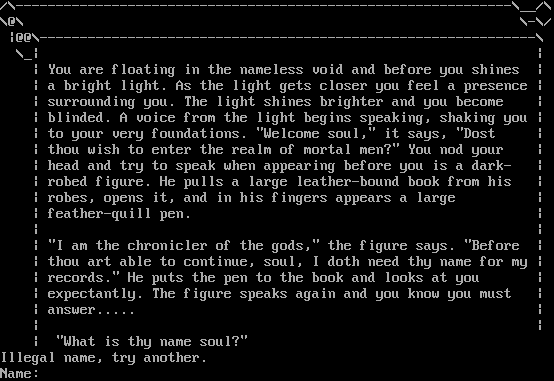
Server URLs
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 320 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Illegal name, try another.\n\rName: ",
"banner_before_return": "\n\r/\\--------------------------------------------------------------\\__/\\\n\r\\@\\ \\-\\/\n\r |@@\\--------------------------------------------------------------\\\n\r \\_| |\n\r | You are floating in the nameless void and before you shines |\n\r | a bright light. As the light gets closer you feel a presence |\n\r | surrounding you. The light shines brighter and you become |\n\r | blinded. A voice from the light begins speaking, shaking you |\n\r | to your very foundations. \"Welcome soul,\" it says, \"Dost |\n\r | thou wish to enter the realm of mortal men?\" You nod your |\n\r | head and try to speak when appearing before you is a dark- |\n\r | robed figure. He pulls a large leather-bound book from his |\n\r | robes, opens it, and in his fingers appears a large |\n\r | feather-quill pen. |\n\r | |\n\r | \"I am the chronicler of the gods,\" the figure says. \"Before |\n\r | thou art able to continue, soul, I doth need thy name for my |\n\r | records.\" He puts the pen to the book and looks at you |\n\r | expectantly. The figure speaks again and you know you must |\n\r | answer..... |\n\r | |\n\r | \"What is thy name soul?\" ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5039417743682861,
"total": 11.234923124313354
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:01.268081+00:00",
"host": "mud.darkrisings.org",
"ip": "176.9.151.147",
"port": 1313
},
{
"connected": "2026-04-07T07:14:50.764398+00:00",
"host": "mud.darkrisings.org",
"ip": "176.9.151.147",
"port": 1313
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.darkrisings.org 1313
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.darkrisings.org port=1313
INFO client_base.py:190 Connected to <Peer 176.9.151.147 1313>
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MSP, WILL ZMP, WILL ATCP, WILL AARDWOLF, WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS,
WILL MXP, WILL MSSP, WILL GMCP, WILL MSDP, DO MSP, DO ZMP, DO ATCP, DO AARDWOLF, DO MCCP2_COMPRESS, DO MCCP3_COMPRESS, DO MXP,
DO MSSP, DO GMCP, DO MSDP'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint e89ffa4fe5c32389
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 1313>
reaux.vineyard.haus:1119
Connection Banner:
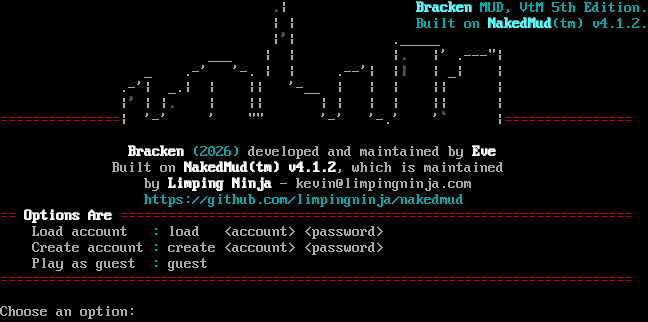
Server URLs
- Telnet: telnet://reaux.vineyard.haus:1119
- Website: limpingninja.com
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: No
GMCP: No
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: No
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 13 other servers.
Options offered by server: MCCP2
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "886e1f8cbdfbe41f",
"fingerprint-data": {
"offered-options": [
"MCCP2"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Choose an option: ",
"banner_before_return": "\r\n\u001b[0;0m\n \u001b[1;30m.\u001b[0;0m| \u001b[1;36mBracken\u001b[0;36m MUD, VtM 5th Edition.\u001b[0;0m\n | | \u001b[0;36mBuilt on \u001b[1;36mNakedMud\u001b[0;36m(tm) v4.1.2.\u001b[0;0m\n |\u001b[1;30m'\u001b[0;0m| ._____\n ___ | | |\u001b[1;30m.\u001b[0;0m |' .---\"|\n _ .-' '-. | | .--'| |\u001b[1;30m|\u001b[0;0m | _| |\n .-'| _.| | || '-__ | | | || |\n |\u001b[1;30m'\u001b[0;0m | |\u001b[1;30m.\u001b[0;0m | || | | | | || |\n\u001b[0;31m===============\u001b[0;0m| '-' ' \"\" '-' '-.' '\u001b[1;30m`\u001b[0;0m |\u001b[0;31m================\u001b[0;0m\n\n \u001b[1;37mBracken\u001b[0;36m (2026)\u001b[0;0m developed and maintained by \u001b[1;37mEve\u001b[0;0m\n Built on \u001b[1;37mNakedMud(tm) v4.1.2\u001b[0;0m, which is maintained\n by \u001b[1;37mLimping Ninja\u001b[0;0m - kevin@limpingninja.com\n \u001b[0;36mhttps://github.com/limpingninja/nakedmud\u001b[0;0m\r\n\u001b[0;31m==\u001b[1;37m Options Are \u001b[0;31m================================================================\u001b[0;0m\r\n Load account \u001b[0;36m:\u001b[0;0m load <account> <password>\r\n Create account \u001b[0;36m:\u001b[0;0m create <account> <password>\r\n Play as guest \u001b[0;36m:\u001b[0;0m guest\r\n\u001b[0;31m===============================================================================\u001b[0;0m\r\n\r\nChoose an option: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"0x55": false,
"MCCP2": true
},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5037841796875,
"total": 11.23629355430603
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:25:33.681273+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 1119
},
{
"connected": "2026-04-07T07:02:26.178950+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 1119
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug reaux.vineyard.haus 1119
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=reaux.vineyard.haus port=1119
INFO client_base.py:190 Connected to <Peer 176.9.151.147 1119>
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP_COMPRESS] = False
DEBUG stream_writer.py:1024 send IAC DONT MCCP_COMPRESS
DEBUG stream_writer.py:2182 Unhandled: WILL MCCP_COMPRESS.
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL AARDWOLF, WILL MSDP, WILL GMCP, WILL MSSP, WILL ZMP, WILL MXP, WILL MCCP3_COMPRESS,
WILL MCCP2_COMPRESS, WILL ATCP, WILL MSP, DO AARDWOLF, DO MSDP, DO GMCP, DO MSSP, DO ZMP, DO MXP, DO MCCP3_COMPRESS, DO ATCP,
DO MSP'
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:849 connection for server fingerprint 886e1f8cbdfbe41f
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 1119>
reaux.vineyard.haus:3033
Connection Banner:
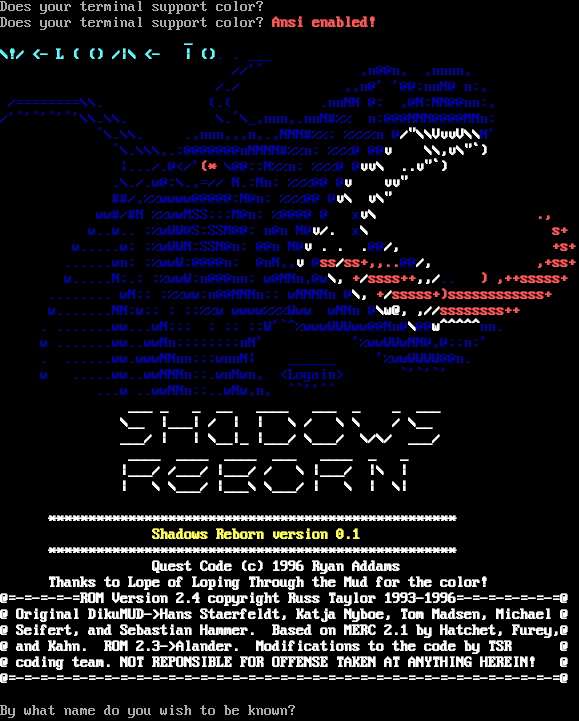
Server URLs
- Telnet: telnet://reaux.vineyard.haus:3033
- Website: ww.www
Server Info
Server Location: 🇩🇪 Germany (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 111 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Does your terminal support color? \u001b[1;31mAnsi enabled!\u001b[0m\n\r\u001b[1;36m _\n\r\u001b[1;36m\\!/ <- L ( () /|\\ <- | ()\u001b[0;34m. . ___\n\r\u001b[0;34m //'` ,n@@n, ,nnnn,\n\r\u001b[0;34m /./ ,,n@' '@@;nnN@ n:,\n\r\u001b[0;34m /========\\\\. (.( .nnNN @; ,@N;NN@@nn:,\n\r\u001b[0;34m/'`'`'`'`'\\\\.\\\\. \\.`\\_,nnn,.nnN#%% n;@@@NNN@@@@MNn:\n\r\u001b[0;34m `\\.\\\\. .,nnn,,,n,.,NNN#%%; %%%%n @\u001b[1;37m/\"\\\\VvvV\\\\\u001b[0;34mN'\n\r\u001b[0;34m `\\.\\\\\\,.;@@@@@@@nNNNN#%%n; %%%@ @@\u001b[1;37mv \\\\,v\\\"`)\n\r\u001b[0;34m |.../.@</'\u001b[1;31m(*\u001b[0;34m \\@@;;N%%n; %%%@ @\u001b[1;37mvv\\ ..v\"`)\n\r\u001b[0;34m .\\./.w@;\\.,=// N.;Nn; %%%@@ @\u001b[1;37mv vv\"\n\r\u001b[0;34m ##/,%%wwww@@@@@;N@n; %%%@@ @\u001b[1;37mv\\ v\\\"\n\r\u001b[0;34m ww#/#N %%wwMSS;;;M@n; %@@@@ @ \u001b[0;34mx\u001b[1;37mv\\ \u001b[1;31m .,\n\r\u001b[0;34m w..w.. ;%wWW@S;SSM@@; n@n N@\u001b[1;37mv/. \u001b[0;34mx\u001b[1;37m\\ \u001b[1;31m s+\n\r\u001b[0;34m w.....w; ;%wWWN;SSN@n; @@n N@\u001b[1;37mv . . .\u001b[0;34m@@\u001b[1;37m/,\u001b[1;31m +s+\n\r\u001b[0;34m ......wn; ;%wwW;@@@@n; @nN,,\u001b[1;37mv \u001b[0;34m@\u001b[1;31mss\u001b[1;37m/\u001b[1;31mss+,,..\u001b[0;34m@@\u001b[1;37m/,\u001b[1;31m ,+ss+\n\r\u001b[0;34m w.....N;.; ;%wwW;n@@@nn; w@NNn,@w\u001b[1;37m\\, \u001b[1;31m+\u001b[1;37m/\u001b[1;31mssss++\u001b[1;37m,,/\u001b[0;34m.. \u001b[1;31m) ,++sssss+\n\r\u001b[0;34m ........ wN;; ;%%ww;n@@NNNn;; wNNNNn @\u001b[1;37m\\,\u001b[1;31m +\u001b[1;37m/\u001b[1;31msssss+)ssssssssssss+\n\r\u001b[0;34m w.......NN;w;; ; ;;%%w wwww%%%Www wNNn @\u001b[1;37m\\w@, ,//\u001b[1;31mssssssss++\n\r\u001b[0;34m . .......ww...wN;;; ; ;; ;;W'`^%wwwWWWww@@Nn@\u001b[1;37m\\\u001b[0;34m@@\u001b[1;37mw^^^^^\u001b[0;34mnn.\n\r\u001b[0;34m w .......ww..wwNn;;;;;;;;nN' '%wwWWwNN@,@;;n;'\n\r\u001b[0;34m . ......ww.wwwNNnn;;;wnnN| ______ '%wwWWWW@@n.\n\r\u001b[0;34m w .....ww..wwNNNn::.wnNwn, <Logain> `'`'`'\n\r\u001b[0;34m ...w ..wwNNn::..wNw,n, ``''``\n\r\u001b[1;37m ___ _ _ __ ____ ___ _ _ ___\n\r \\__ |___| / | | \\ / \\ \\ / \\__\n\r ___/ | | \\__|_ |___/ \\___/ \\/\\/ ___/\n\r ____ ____ ____ ___ ____ _ _\n\r |___/ /___/ |___/ / \\ |___/ |\\ |\n\r | \\ \\___/ |___\\ \\___/ | \\ | \\|\n\r\n\r \u001b[1;37m ***************************************************\n\r \u001b[1;33m Shadows Reborn version 0.1\n\r \u001b[1;37m ***************************************************\n\r Quest Code (c) 1996 Ryan Addams\n\r Thanks to Lope of Loping Through the Mud for the color!\n\r@=-=-=-=-=ROM Version 2.4 copyright Russ Taylor 1993-1996=-=-=-=-=-=-=@\n\r@ Original DikuMUD->Hans Staerfeldt, Katja Nyboe, Tom Madsen, Michael @\n\r@ Seifert, and Sebastian Hammer. Based on MERC 2.1 by Hatchet, Furey,@\n\r@ and Kahn. ROM 2.3->Alander. Modifications to the code by TSR @\n\r@ coding team. NOT REPONSIBLE FOR OFFENSE TAKEN AT ANYTHING HEREIN! @\n\r@=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=@\n\r\u001b[0m\n\rBy what name do you wish to be known? \n\r",
"banner_before_return": "\n\rDoes your terminal support color? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 16.368242502212524
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:23:40.275557+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 3033
},
{
"connected": "2026-04-05T18:57:15.381986+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 3033
},
{
"connected": "2026-04-07T07:24:02.957103+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 3033
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug reaux.vineyard.haus 3033
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=reaux.vineyard.haus port=3033
INFO client_base.py:190 Connected to <Peer 176.9.151.147 3033>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP3_COMPRESS, WILL MCCP2_COMPRESS, WILL MSP, WILL MSSP, WILL MXP, WILL ZMP, WILL
AARDWOLF, WILL ATCP, WILL MSDP, WILL GMCP, DO MCCP3_COMPRESS, DO MCCP2_COMPRESS, DO MSP, DO MSSP, DO MXP, DO ZMP, DO AARDWOLF,
DO ATCP, DO MSDP, DO GMCP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 3033>
DEBUG fingerprinting.py:849 connection for server fingerprint c2dd7d4e76383b41
Fixing the Volatile (reaux.vineyard.haus:7000)
Connection Banner:
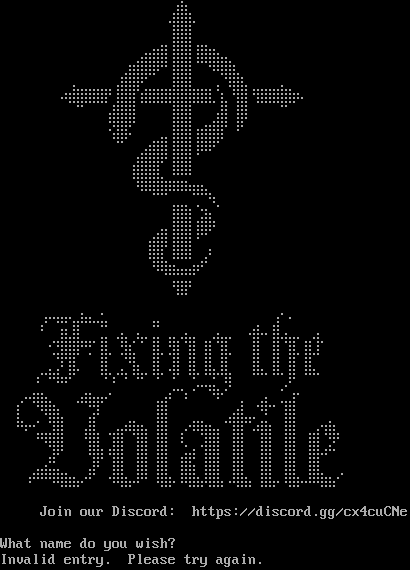
Server URLs
- Telnet: telnet://reaux.vineyard.haus:7000
- Website: https://discord.gg/cx4cuCNe
Server Info
Players online: 3 [15]
Uptime: 0 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: Negotiated
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: Negotiated
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 2 other servers.
Options requested from client: GMCP, MCCP2, MSDP, MSP, MSSP, NAWS, NEW_ENVIRON, TTYPE, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "195bae7111647e9e",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"GMCP",
"MCCP2",
"MSDP",
"MSP",
"MSSP",
"NAWS",
"NEW_ENVIRON",
"TTYPE",
"ZMP"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\nInvalid entry. Please try again.\r\n",
"banner_before_return": "\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u28e0\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u28f0\u28ff\u28f7\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800 \u2800\u2800\u2800\u2800\u28c0\u28e4\u28f6\u28b8\u28ff\u28ff\u28b0\u28f6\u28e4\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u28e4\u28fe\u28ff\u28ff\u283f\u28b8\u28ff\u28ff\u2818\u281b\u28bf\u28ff\u28f7\u2844\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800 \u2800\u2800 \u2840\u2800\u2800 \u2800\u2880\u28fe\u28ff\u287f\u280b\u2801\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u2848\u28bb\u28ff\u28c6\u2800\u2800\u2800\u2800\u2840\u2800\u2800\u2800\u2800\u2800\r\n\u2800 \u2800 \u2820\u28b6\u28ff\u28ff\u28ff\u28ff\u285f\u28b8\u28ff\u28ff\u28b1\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28ff\u28c7\u28b1\u2840\u28bb\u28ff\u2818\u28ff\u28ff\u28ff\u28ff\u28f7\u2826\u2800\u2800\u2800\r\n\u2800\u2800 \u2800\u2800 \u2808\u2801\u2800\u2800\u28a0\u28ff\u28ff\u28ff\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u2800\u2800\u2800\u28fc\u2847\u28b8\u28ff\u2800\u2800\u2800\u2800\u2809\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800 \u2800\u2800\u2800 \u2800\u2828\u28fb\u28ff\u284b\u2800\u2800\u2800\u2800\u28b8\u28ff\u28ff\u28a0\u28f4\u28fe\u28ff\u2803\u2838\u2803\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u2819\u280b\u2800\u2800\u28e0\u28f6\u28ff\u28b8\u28ff\u28ff\u28b8\u28ff\u287f\u280b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2800\u2880\u28fe\u28ff\u28ff\u281f\u28b8\u28ff\u28ff\u2808\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2838\u28ff\u28ff\u28ff\u28c4\u28d8\u28db\u285b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2819\u281b\u283f\u283f\u281b\u281b\u281b\u283f\u2837\u28c4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u28b0\u28f6\u28e6\u2810\u28a4\u2848\u2802\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2800\u2800\u28c0\u28b8\u28ff\u28ff\u28b0\u28ff\u2877\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u28a0\u28fe\u28ff\u28b8\u28ff\u28ff\u2818\u2809\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2838\u28ff\u28c7\u2838\u283f\u283f\u2800\u28e0\u2803\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800\u2819\u283b\u283f\u2836\u2836\u281f\u2801\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \u2800\u2818\u28ff\u285f\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\r\n\u2800\u2800\u2800\u2800\u2800\u2870\u2812\u2836\u2816\u28e4\u2837\u2826\u28ac\u2844\u2800\u2800\u2800\u2800\u2800\u28e4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2840\u2800\u28f0\u2801\u2802\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2801\u2880\u28f8\u28e7\u28ff\u28c0\u28c0\u28a0\u2844\u2820\u28e6\u2880\u28a6\u2804\u28e4\u2800\u28e4\u2860\u28e6\u2844\u2880\u2860\u28e6\u2864\u2800\u2800\u28ba\u2857\u2802\u28ff\u28b4\u28e4\u2804\u28c0\u28b4\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2800\u2821\u28fd\u28ff\u287f\u2809\u2805\u28b8\u2867\u2800\u28bd\u28e7 \u2800\u28ff\u2804\u28bd\u2847\u28b8\u2847\u28b8\u2847\u28b8\u2867\u2800\u2800\u28b8\u2847\u2800\u28ff\u2800\u28ff\u2804\u28ff\u283c\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u28c0\u28c4\u285c\u28b8\u2867\u2800\u2800\u28b8\u28c7\u2880\u28c4\u28b9\u28c6\u2840\u28ff\u2840\u28bc\u2847\u28b8\u28c7\u28b8\u28e7\u28f8\u28c7\u2800\u2800\u28b8\u28e7\u2840\u28ff\u2840\u28ff\u2800\u28ff\u28c4\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2818\u2800\u2809\u281b\u280b\u2800\u2800\u2800\u2800\u2801\u2803\u2808\u2800\u2809\u2800\u2808\u2800\u2888\u28c0\u2800\u2861\u2824\u28ec\u2840\u287b\u2800\u2800\u2800 \u2860\u280b\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2860\u2812\u28bf\u28f7\u28c4\u2800 \u2820\u283e\u28f7\u2876\u280a\u2800\u2800\u2800\u2800\u2800\u28a0\u28f4\u2803\u2800\u2803 \u2808\u280b\u2800\u2800\u2844\u2800\u28e0\u28c6\u2840\u28a4\u28fc\u2801\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u28c7\u2800\u2880\u2819\u28ff\u28e7\u2800\u2800\u2800\u28f4\u2803\u2800\u2800\u2800\u28c0\u2800\u2800\u28b8\u28ff\u2800\u2800\u2800\u28c0\u2840\u2800\u2800\u28e0\u28fe\u28e7\u2864\u2888\u2843\u2800\u28b8\u28ff\u2800\u2800\u2800\u2800\u2840\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2809\u280b\u28a1\u28e4\u28fc\u28ff\u2800 \u28b0\u28ff\u2844\u2820\u28f4\u285e\u283b\u28ff\u2846\u28b8\u28ff\u2800\u28a0\u280a\u281b\u28bf\u28f7\u2846\u2800\u28ff\u2847\u2810\u28bb\u28ff\u2800\u28b8\u28ff\u2800\u28a0\u28f4\u2839\u28ff\u2844\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2800\u2808\u28bb\u287f \u2800\u28ff\u28e7\u28a0\u28ff\u2847\u2800\u28ff\u2847\u28b8\u28ff \u2808\u28c2\u2844\u28ba\u28ff\u2847\u2800\u28ff\u2847\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u28e0\u282e\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2800\u2880\u28e0\u28db\u2840 \u2800\u28f8\u280f\u2800\u28ff\u2847\u2800\u28ff\u2847\u28b8\u28ff\u2800\u28b8\u28ff\u2845\u28b8\u28ff\u2847\u2800\u28ff\u2847\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u28b8\u28ff\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\r\n\u2800\u2800\u2800\u2830\u281b\u281b\u283b\u28bf\u28f7\u28e6\u2814\u280b\u2800\u2810\u283f\u28f7\u2864\u281f\u2803\u2838\u28ff\u2866\u2838\u28bf\u28f7\u287c\u28ff\u28e7\u2820\u28bf\u28f7\u2844\u28b8\u28ff\u2864\u2838\u28ff\u2866\u283c\u283f\u28f7\u28e6\u280a\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800\u2800 \u2800 \r\n\r\n Join our Discord: https://discord.gg/cx4cuCNe\r\n\r\nWhat name do you wish? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "utf-8",
"mssp": {
"NAME": "Fixing the Volatile",
"PLAYERS": "3",
"UPTIME": "1775668554"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": false,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true,
"ZMP": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.662196397781372
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:05:10.167314+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
},
{
"connected": "2026-04-07T06:47:49.951193+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
},
{
"connected": "2026-04-09T00:08:38.364212+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 7000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug reaux.vineyard.haus 7000
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=reaux.vineyard.haus port=7000
INFO client_base.py:188 Connected to <Peer 176.9.151.147 7000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO ZMP
DEBUG stream_writer.py:1887 handle_do(ZMP)
DEBUG stream_writer.py:998 skip WILL ZMP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DO MSP
DEBUG stream_writer.py:1887 handle_do(MSP)
DEBUG stream_writer.py:998 skip WILL MSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO MSDP
DEBUG stream_writer.py:1887 handle_do(MSDP)
DEBUG stream_writer.py:998 skip WILL MSDP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:462 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Fixing the Volatile', 'PLAYERS': '3', 'UPTIME': '1775668554'}
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:510 negotiation complete after 0.32s.
DEBUG client_base.py:90 EOF from server, closing.
INFO client_base.py:120 Connection closed to <Peer 176.9.151.147 7000>
DEBUG fingerprinting.py:850 connection for server fingerprint 195bae7111647e9e
The Illusion of Living (reaux.vineyard.haus:7800)
Connection Banner:

Server URLs
Server Info
Players online: 2 [16]
Uptime: 9 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: Negotiated
MSDP: No
MCCP: No
MCCP2: Negotiated
MXP: No
MSP: Negotiated
MCP: No
ZMP: Negotiated
Telnet Fingerprint
This fingerprint is shared by 8 other servers.
Options requested from client: GMCP, MCCP2, MSP, MSSP, NAWS, NEW_ENVIRON, TTYPE, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2582d677ba7e36e2",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"GMCP",
"MCCP2",
"MSP",
"MSSP",
"NAWS",
"NEW_ENVIRON",
"TTYPE",
"ZMP"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[38;5;239m\r\nInvalid entry. Please try again.\r\n\u001b[0;37;40m",
"banner_before_return": "\u001b[0;37;40m_________ _ _ _______ _________ _______ _ \r\n\\__ __/( \\ ( \\ |\\ /|( ____ \\\\__ __/( ___ )( ( /| \r\n ) ( | ( | ( | ) ( || ( \\/ ) ( | ( ) || \\ ( | \r\n | | | | | | | | | || (_____ | | | | | || \\ | | \r\n | | | | | | | | | |(_____ ) | | | | | || (\\ \\) | \r\n | | | | | | | | | | ) | | | | | | || | \\ | \r\n___) (___| (____/\\| (____/\\| (___) |/\\____) |___) (___| (___) || ) \\ | \r\n\\_______/(_______/(_______/(_______)\\_______)\\_______/(_______)|/ )_) \r\n \r\n _______ _______ _ _________ _________ _ _______ \r\n( ___ )( ____ \\ ( \\ \\__ __/|\\ /|\\__ __/( ( /|( ____ \\\r\n| ( ) || ( \\/ | ( ) ( | ) ( | ) ( | \\ ( || ( \\/\r\n| | | || (__ | | | | | | | | | | | \\ | || | \r\n| | | || __) | | | | ( ( ) ) | | | (\\ \\) || | ____ \r\n| | | || ( | | | | \\ \\_/ / | | | | \\ || | \\_ )\r\n| (___) || ) | (____/\\___) (___ \\ / ___) (___| ) \\ || (___) |\r\n(_______)|/ (_______/\\_______/ \\_/ \\_______/|/ )_)(_______)\r\n\r\n\r\n==================================================================================================== \r\n\r\nDriver: fluffos 20240131-6bc96f74-9ca961e3-uncommited Mudlib: Sand Man 1.0 (alpha)\r\n\r\n There are presently 1 adventurers on-line.\r\n \u001b[38;5;29m\r\nWhat name do you wish? \u001b[0;37;40m",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"NAME": "The Illusion of Living",
"PLAYERS": "2",
"UPTIME": "1774729577"
},
"option_states": {
"environ_requested": [
{
"name": "*",
"type": "VAR"
},
{
"name": "*",
"type": "USERVAR"
}
],
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"CHARSET": true,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": true,
"MSSP": true,
"MXP": false,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": true,
"MCCP2": true,
"MCCP3": false,
"MSDP": false,
"MSP": true,
"MSSP": true,
"MXP": false,
"NAWS": true,
"NEW_ENVIRON": true,
"TTYPE": true,
"ZMP": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.664872646331787
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:58:32.971172+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 7800
},
{
"connected": "2026-04-07T06:52:32.409450+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 7800
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug reaux.vineyard.haus 7800
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=reaux.vineyard.haus port=7800
INFO client_base.py:190 Connected to <Peer 176.9.151.147 7800>
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO NEW_ENVIRON
DEBUG stream_writer.py:1887 handle_do(NEW_ENVIRON)
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = True
DEBUG stream_writer.py:1024 send IAC WILL NEW_ENVIRON
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 local_option[NEW_ENVIRON] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NEW_ENVIRON] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WILL CHARSET
DEBUG stream_writer.py:791 WILL CHARSET (bi-directional capability exchange)
DEBUG stream_writer.py:2045 handle_will(CHARSET)
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 remote_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DO ZMP
DEBUG stream_writer.py:1887 handle_do(ZMP)
DEBUG stream_writer.py:998 skip WILL ZMP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:773 recv IAC DO MSSP
DEBUG stream_writer.py:1887 handle_do(MSSP)
DEBUG stream_writer.py:998 skip WILL MSSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO MSP
DEBUG stream_writer.py:1887 handle_do(MSP)
DEBUG stream_writer.py:998 skip WILL MSP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1887 handle_do(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip WILL MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DO GMCP
DEBUG stream_writer.py:1887 handle_do(GMCP)
DEBUG stream_writer.py:998 skip WILL GMCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[GMCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL ZMP
DEBUG stream_writer.py:2045 handle_will(ZMP)
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[ZMP] = True
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'The Illusion of Living', 'PLAYERS': '2', 'UPTIME': '1774729577'}
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL GMCP
DEBUG stream_writer.py:2045 handle_will(GMCP)
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[GMCP] = True
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Hello IAC SE
DEBUG stream_writer.py:1072 send IAC SB GMCP Core.Supports.Set IAC SE
INFO client.py:201 GMCP handshake: Core.Hello + Core.Supports.Set ['Char 1', 'Char.Vitals 1', 'Char.Items 1', 'Room 1', 'Room.Info
1', 'Comm 1', 'Comm.Channel 1', 'Group 1']
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB NEW_ENVIRON
DEBUG stream_writer.py:754 sub-negotiation cmd NEW_ENVIRON SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + NEW_ENVIRON] = False
DEBUG stream_writer.py:2449 recv NEW_ENVIRON SEND (all)
DEBUG stream_writer.py:2473 env send: LANG='C', TERM='xterm-256color', LINES=25, COLUMNS=80, COLORTERM=''
DEBUG client_base.py:531 negotiation complete after 0.32s.
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 7800>
DEBUG fingerprinting.py:849 connection for server fingerprint 2582d677ba7e36e2
Gundam Wing Universe (reaux.vineyard.haus:9876)
Connection Banner:
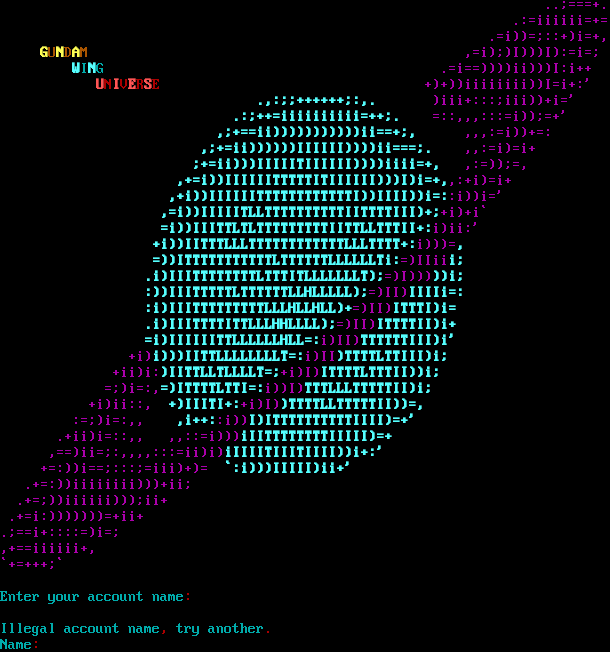
Server URLs
- Telnet: telnet://reaux.vineyard.haus:9876
- Website: gundam.vineyard.haus
Server Info
Codebase: GWM 1.02
Genre: Sci-Fi Anime
Gameplay: Casual
Players online: 4 [17]
Uptime: 0 days
Created: 10 Aug 2025
Status: Beta
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Yes (MSSP)
MCCP: Yes (MSSP)
MCCP2: Negotiated
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is unique to this server.
Options offered by server: MCCP2, MSDP, MSP, MSSP, MXP
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "21391570273c5f22",
"fingerprint-data": {
"offered-options": [
"MCCP2",
"MSDP",
"MSP",
"MSSP",
"MXP"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP3",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "Gundam Wing Universe"
}
],
"banner_after_return": "\u001b[36m\n\rIllegal account name\u001b[31m,\u001b[36m try another\u001b[31m.\u001b[36m\nName\u001b[31m:\u001b[36m ",
"banner_before_return": "\u001b[35m ..;===+.\n .:=iiiiii=+=\n .=i))=;::+)i=+,\n \u001b[1;33mG\u001b[0;33mU\u001b[1;33mN\u001b[0;33mD\u001b[1;33mA\u001b[0;33mM \u001b[35m ,=i);)I)))I):=i=;\n \u001b[1;36mW\u001b[0;36mI\u001b[1;36mN\u001b[0;36mG \u001b[35m .=i==))))ii)))I:i++\n \u001b[1;31mU\u001b[0;31mN\u001b[1;31mI\u001b[0;31mV\u001b[1;31mE\u001b[0;31mR\u001b[1;31mS\u001b[0;31mE\u001b[35m +)+))iiiiiiii))I=i+:'\n\u001b[1;36m .,:;;++++++;:,.\u001b[0;35m )iii+:::;iii))+i='\n\u001b[1;36m .:;++=iiiiiiiiii=++;.\u001b[0;35m =::,,,:::=i));=+'\n\u001b[1;36m ,;+==ii)))))))))))ii==+;,\u001b[0;35m ,,,:=i))+=:\n\u001b[1;36m ,;+=ii))))))IIIIII))))ii===;.\u001b[0;35m ,,:=i)=i+\n\u001b[1;36m ;+=ii)))IIIIITIIIIII))))iiii=+,\u001b[0;35m ,:=));=,\n\u001b[1;36m ,+=i))IIIIIITTTTTITIIIIII)))I)i=+,\u001b[0;35m,:+i)=i+\n\u001b[1;36m ,+i))IIIIIITTTTTTTTTTTTI))IIII))i=:\u001b[0;35m:i))i='\n\u001b[1;36m ,=i))IIIIITLLTTTTTTTTTTIITTTTIII)+;\u001b[0;35m+i)+i`\n\u001b[1;36m =i))IIITTLTLTTTTTTTTTIITTLLTTTII+:\u001b[0;35mi)ii:'\n\u001b[1;36m +i))IITTTLLLTTTTTTTTTTTTLLLTTTT+:\u001b[0;35mi)))=\u001b[1;36m,\n =))ITTTTTTTTTTTLTTTTTTLLLLLLTi:\u001b[0;35m=)IIii\u001b[1;36mi;\n .i)IIITTTTTTTTLTTTITLLLLLLLT);\u001b[0;35m=)I)))\u001b[1;36m))i;\n :))IIITTTTTLTTTTTTLLHLLLLL);\u001b[0;35m=)II)\u001b[1;36mIIIIi=:\n :i)IIITTTTTTTTTLLLHLLHLL)+\u001b[0;35m=)II)\u001b[1;36mITTTI)i=\n .i)IIITTTTITTLLLHHLLLL);\u001b[0;35m=)II)\u001b[1;36mITTTTII)i+\n =i)IIIIIITTLLLLLLHLL=:\u001b[0;35mi)II)\u001b[1;36mTTTTTTIII)i'\n\u001b[0;35m +i)\u001b[1;36mi)))IITTLLLLLLLLT=:\u001b[0;35mi)II\u001b[1;36m)TTTTLTTIII)i;\n\u001b[0;35m +ii)i:\u001b[1;36m)IITTLLTLLLLT=;\u001b[0;35m+i)I)\u001b[1;36mITTTTLTTTII))i;\n\u001b[0;35m =;)i=:,\u001b[1;36m=)ITTTTLTTI=:\u001b[0;35mi))I)\u001b[1;36mTTTLLLTTTTTII)i;\n\u001b[0;35m +i)ii::, \u001b[1;36m+)IIITI+:\u001b[0;35m+i)I)\u001b[1;36m)TTTTLLTTTTTII))=,\n\u001b[0;35m :=;)i=:,, \u001b[1;36m ,i++:\u001b[0;35m:i))\u001b[1;36mI)ITTTTTTTTTTIIII)=+'\n\u001b[0;35m .+ii)i=::,, ,,::=i)))\u001b[1;36miIITTTTTTTTIIIII)=+\n\u001b[0;35m ,==)ii=;:,,,,:::=ii)i)\u001b[1;36miIIIITIIITIIII))i+:'\n\u001b[0;35m +=:))i==;:::;=iii)+)= \u001b[1;36m `:i)))IIIII)ii+'\n\u001b[0;35m .+=:))iiiiiiii)))+ii;\n .+=;))iiiiii)));ii+\n .+=i:)))))))=+ii+\n.;==i+::::=)i=;\n,+==iiiiii+,\n`+=+++;` \n\n\u001b[36mEnter your account name\u001b[31m:\u001b[37m \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "UTF-8",
"mssp": {
"ANSI": "1",
"CODEBASE": "GWM 1.02",
"CONTACT": "gundamwing@gundam.vineyard.haus",
"CRAWL DELAY": "-1",
"CREATED": "10 Aug 2025",
"GAMEPLAY": "Casual",
"GAMESYSTEM": "Custom",
"GENRE": "Sci-Fi Anime",
"GMCP": "0",
"HOSTNAME": "gundam.vineyard.haus",
"MCCP": "1",
"MCP": "0",
"MSDP": "1",
"MSP": "1",
"MXP": "1",
"NAME": "Gundam Wing Universe",
"PLAYERS": "4",
"PORT": "9876",
"PUEBLO": "0",
"STATUS": "Beta",
"SUBGENRE": "Mobile Suit Gundam",
"UPTIME": "1775536019",
"UTF-8": "1",
"VT100": "0",
"XTERM 256 COLORS": "1"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": true,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5042977333068848,
"total": 11.259008646011353
}
}
},
"sessions": [
{
"connected": "2026-04-07T06:46:17.038956+00:00",
"host": "reaux.vineyard.haus",
"ip": "176.9.151.147",
"port": 9876
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug reaux.vineyard.haus 9876
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=reaux.vineyard.haus port=9876
INFO client_base.py:190 Connected to <Peer 176.9.151.147 9876>
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:767 begin sub-negotiation SB MCCP2_COMPRESS
DEBUG stream_writer.py:754 sub-negotiation cmd MCCP2_COMPRESS SE completion byte
DEBUG stream_writer.py:2238 [SB + MCCP2_COMPRESS] unsolicited
DEBUG stream_writer.py:3232 MCCP2 activated
DEBUG client_base.py:483 MCCP2 decompression started (server→client)
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = True
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'Gundam Wing Universe'
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'Gundam Wing Universe'}
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'Gundam Wing Universe', 'PLAYERS': '4', 'UPTIME': '1775536019', 'CRAWL DELAY': '-1',
'HOSTNAME': 'gundam.vineyard.haus', 'PORT': '9876', 'CODEBASE': 'GWM 1.02', 'CONTACT': 'gundamwing@gundam.vineyard.haus',
'CREATED': '10 Aug 2025', 'GENRE': 'Sci-Fi Anime', 'GAMEPLAY': 'Casual', 'STATUS': 'Beta', 'GAMESYSTEM': 'Custom', 'SUBGENRE':
'Mobile Suit Gundam', 'ANSI': '1', 'GMCP': '0', 'MCCP': '1', 'MCP': '0', 'MSDP': '1', 'MSP': '1', 'MXP': '1', 'PUEBLO': '0',
'UTF-8': '1', 'VT100': '0', 'XTERM 256 COLORS': '1'}
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:789 WILL MCCP2_COMPRESS unsolicited
DEBUG stream_writer.py:2045 handle_will(MCCP2_COMPRESS)
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG client_base.py:531 negotiation complete after 1.03s.
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG fingerprinting.py:849 connection for server fingerprint 21391570273c5f22
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 9876>
tbaMUD (tbamud.com:9091)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes WELCOME TO THE: \*\*\*\* \* \* \* \* \* \* \* \*\*\*\* \* \* \* \* \*\*\* \*\* \* \*\* \* \* \* \* \* \* \* \* \* \*\* \*\* \* \* \* \* \* \* \* \* \*\* \* \*\*\*\* \*\*\* \* \* \*\*\*\* \*\*\* \* \* \* \* \* \* \* \* \*\*\* \*\*\* \*\*\* \*\* \* \* \* \* \*\*\*\*\* \* \* \* \* \* \* \*\* \*\* \*\* \* \* \* \* \* \* \* \* \* \*\* \* \* \* \* \* \* \* \*\*\* \*\*\*\* \*\*\*\* \*\*\* \* \* \* \*\*\* \* \*\* Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer email: rumble@tbamud.com By what name do you wish to be known?](../_images/banner_e49bd3d9a073.png)
Server URLs
- Telnet: telnet://tbamud.com:9091
- Website: tbamud.com
Server Info
Players online: 0 [18]
Uptime: 10 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "tbaMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\nWELCOME TO THE:\r\n \r\n **** * * *\r\n * * * *\r\n **** * * * * *** ** * **\r\n * * * * * * * * * ** ** \r\n * * * * * * * * ** * \r\n **** *** * * **** *** *\r\n\r\n * * \r\n * * *\r\n * * *** *** *** ** * * * *\r\n ***** * * * * * * ** ** ** * *\r\n * * * * * * * ** * * * * *\r\n * * *** **** **** *** * * * ***\r\n *\r\n **\r\n Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt,\r\n Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer\r\n email: rumble@tbamud.com \r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "tbaMUD",
"PLAYERS": "0",
"UPTIME": "1774605683"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.757449150085449
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:00:25.500347+00:00",
"host": "tbamud.com",
"ip": "176.9.151.147",
"port": 9091
},
{
"connected": "2026-04-07T07:25:02.708884+00:00",
"host": "tbamud.com",
"ip": "176.9.151.147",
"port": 9091
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug tbamud.com 9091
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=tbamud.com port=9091
INFO client_base.py:190 Connected to <Peer 176.9.151.147 9091>
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'tbaMUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'tbaMUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'tbaMUD', 'PLAYERS': '0', 'UPTIME': '1774605683', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL ZMP, WILL MCCP3_COMPRESS, WILL MSDP, WILL MSSP, WILL AARDWOLF, WILL GMCP, WILL
MCCP2_COMPRESS, WILL MSP, DO ATCP, DO ZMP, DO MXP, DO MCCP3_COMPRESS, DO AARDWOLF, DO GMCP, DO MCCP2_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 9091>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
tbaMUD (timeslost.duckdns.org:4000)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes T B A M U D 2 0 2 5 Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer By what name do you wish to be known?](../_images/banner_2ed57e39c115.png)
This banner is more than 99% similar to 2 other servers:
🇨🇦 mud.theghostbox.com:4001 (100% match)
🇺🇸 173.230.135.147:4000 (99% match)
Server URLs
Server Info
Players online: 1 [19]
Uptime: 10 days
Server Location: 🇩🇪 Germany (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "tbaMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\n T B A M U D\r\n 2 0 2 5 \r\n\r\n Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt,\r\n Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer\r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "tbaMUD",
"PLAYERS": "1",
"UPTIME": "1774605976"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.757110595703125
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:32.998197+00:00",
"host": "timeslost.duckdns.org",
"ip": "176.9.151.147",
"port": 4000
},
{
"connected": "2026-04-07T06:58:57.545913+00:00",
"host": "timeslost.duckdns.org",
"ip": "176.9.151.147",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug timeslost.duckdns.org 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=timeslost.duckdns.org port=4000
INFO client_base.py:190 Connected to <Peer 176.9.151.147 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'tbaMUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'tbaMUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'tbaMUD', 'PLAYERS': '1', 'UPTIME': '1774605976', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL MSDP, WILL ZMP, WILL GMCP, WILL AARDWOLF, WILL MSSP, WILL
MCCP3_COMPRESS, WILL MSP, DO MCCP2_COMPRESS, DO ZMP, DO GMCP, DO ATCP, DO AARDWOLF, DO MCCP3_COMPRESS, DO MXP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 176.9.151.147 4000>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b