51.161.5.210 (mud.theghostbox.com)
The Ghost EmpireMUD (mud.theghostbox.com:4000)
Connection Banner:
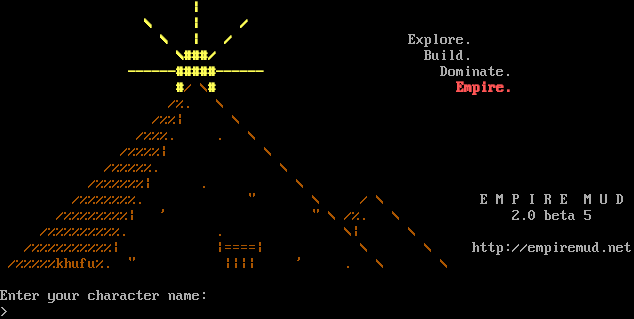
Server URLs
- Telnet: telnet://mud.theghostbox.com:4000
- Website: http://empiremud.net
Server Info
Codebase: EmpireMUD 2.0 beta 5.200
Genre: Fantasy
Gameplay: Adventure, Hack and Slash, Player versus Player, Player versus Environment, Roleplaying, Simulation
Players online: 2 [1]
Uptime: 3 days
Created: 2015
Status: Live
Server Location: 🇨🇦 Canada (GeoIP)
Language: English
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Yes (MSSP)
MCCP: No
MCCP2: No
MXP: Yes (MSSP)
MSP: Yes (MSSP)
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "The Ghost EmpireMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\n \u001b[1;33m|\r\n \\ | /\r\n \\ | / \u001b[0mExplore.\r\n \u001b[1;33m\\###/ \u001b[0mBuild.\r\n \u001b[1;33m------#####------ \u001b[0mDominate.\r\n \u001b[1;33m#\u001b[0;33m/ \\\u001b[1;33m# \u001b[1;31mEmpire.\r\n \u001b[0;33m/%. \\\r\n /%%| \\\r\n /%%%. . \\\r\n /%%%%| \\\r\n /%%%%%. \\\r\n /%%%%%%| . \\\r\n /%%%%%%%. \" \\ / \\ \u001b[0m E M P I R E M U D\r\n \u001b[0;33m/%%%%%%%%| ' \" \\ /%. \\ \u001b[0m 2.0 beta 5\r\n \u001b[0;33m/%%%%%%%%%. . \\| \\\r\n /%%%%%%%%%%| |====| \\ \\ \u001b[0mhttp://empiremud.net\r\n \u001b[0;33m/%%%%%khufu%. \" |||| ' . \\ \\\u001b[0m\r\n \r\nEnter your character name:\r\n> \u001b[7z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"ADULT MATERIAL": "0",
"ANSI": "1",
"AREAS": "111",
"ATCP": "1",
"CLASSES": "1",
"CODEBASE": "EmpireMUD 2.0 beta 5.200",
"CONTACT": "",
"CRAWL DELAY": "-1",
"CREATED": "2015",
"DBSIZE": "10783",
"EQUIPMENT SYSTEM": "Level and Skill",
"EXTRA DESCRIPTIONS": "5343",
"FAMILY": "DikuMUD",
"GAMEPLAY": "Adventure, Hack and Slash, Player versus Player, Player versus Environment, Roleplaying, Simulation",
"GAMESYSTEM": "Custom",
"GENRE": "Fantasy",
"GMCP": "0",
"HELPFILES": "1940",
"HIRING BUILDERS": "0",
"HIRING CODERS": "0",
"HOSTNAME": "",
"ICON": "",
"INTERMUD": "",
"IP": "",
"LANGUAGE": "English",
"LEVELS": "400",
"LOCATION": "",
"MCCP": "0",
"MCP": "0",
"MINIMUM AGE": "",
"MOBILES": "1361",
"MSDP": "1",
"MSP": "1",
"MUDPROGS": "0",
"MUDTRIGS": "1613",
"MULTICLASSING": "1",
"MULTIPLAYING": "No",
"MXP": "1",
"NAME": "The Ghost EmpireMUD",
"NEWBIE FRIENDLY": "1",
"OBJECTS": "3015",
"PAY FOR PERKS": "0",
"PAY TO PLAY": "0",
"PLAYER CITIES": "1",
"PLAYER CLANS": "1",
"PLAYER CRAFTING": "1",
"PLAYER GUILDS": "1",
"PLAYERKILLING": "Restricted",
"PLAYERS": "2",
"PORT": "4000",
"PUEBLO": "0",
"QUEST SYSTEM": "Integrated",
"RACES": "0",
"RESETS": "0",
"ROLEPLAYING": "Encouraged",
"ROOMS": "7465",
"SKILLS": "309",
"SSL": "0",
"STATUS": "Live",
"SUBGENRE": "Medieval Fantasy",
"TRAINING SYSTEM": "Skill",
"UPTIME": "1775263906",
"UTF-8": "1",
"VT100": "0",
"WEBSITE": "",
"WORLD ORIGINALITY": "All Original",
"XTERM 256 COLORS": "1",
"ZMP": "0"
},
"mxp": [
"activated"
],
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP3": false,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": true,
"CHARSET": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": true,
"NAWS": true,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.647745132446289
}
}
},
"sessions": [
{
"connected": "2026-03-07T03:56:23.131118+00:00",
"host": "mud.theghostbox.com",
"ip": "51.161.5.210",
"port": 4000
},
{
"connected": "2026-04-07T07:25:07.175349+00:00",
"host": "mud.theghostbox.com",
"ip": "51.161.5.210",
"port": 4000
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.theghostbox.com 4000
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.theghostbox.com port=4000
INFO client_base.py:190 Connected to <Peer 51.161.5.210 4000>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:1451 IAC GA: Go-Ahead (unhandled).
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'The Ghost EmpireMUD'
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'The Ghost EmpireMUD', 'PLAYERS': '2', 'UPTIME': '1775263906', 'CRAWL DELAY': '-1',
'HOSTNAME': '', 'PORT': '4000', 'CODEBASE': 'EmpireMUD 2.0 beta 5.200', 'CONTACT': '', 'CREATED': '2015', 'ICON': '', 'IP':
'', 'LANGUAGE': 'English', 'LOCATION': '', 'MINIMUM AGE': '', 'WEBSITE': '', 'FAMILY': 'DikuMUD', 'GENRE': 'Fantasy',
'GAMEPLAY': 'Adventure, Hack and Slash, Player versus Player, Player versus Environment, Roleplaying, Simulation', 'STATUS':
'Live', 'GAMESYSTEM': 'Custom', 'INTERMUD': '', 'SUBGENRE': 'Medieval Fantasy', 'AREAS': '111', 'HELPFILES': '1940',
'MOBILES': '1361', 'OBJECTS': '3015', 'ROOMS': '7465', 'CLASSES': '1', 'LEVELS': '400', 'RACES': '0', 'SKILLS': '309', 'ANSI':
'1', 'GMCP': '0', 'MCCP': '0', 'MCP': '0', 'MSDP': '1', 'MSP': '1', 'MXP': '1', 'PUEBLO': '0', 'UTF-8': '1', 'VT100': '0',
'XTERM 256 COLORS': '1', 'PAY TO PLAY': '0', 'PAY FOR PERKS': '0', 'HIRING BUILDERS': '0', 'HIRING CODERS': '0', 'DBSIZE':
'10783', 'EXTRA DESCRIPTIONS': '5343', 'MUDPROGS': '0', 'MUDTRIGS': '1613', 'RESETS': '0', 'ADULT MATERIAL': '0',
'MULTICLASSING': '1', 'NEWBIE FRIENDLY': '1', 'PLAYER CITIES': '1', 'PLAYER CLANS': '1', 'PLAYER CRAFTING': '1', 'PLAYER
GUILDS': '1', 'EQUIPMENT SYSTEM': 'Level and Skill', 'MULTIPLAYING': 'No', 'PLAYERKILLING': 'Restricted', 'QUEST SYSTEM':
'Integrated', 'ROLEPLAYING': 'Encouraged', 'TRAINING SYSTEM': 'Skill', 'WORLD ORIGINALITY': 'All Original', 'ATCP': '1',
'SSL': '0', 'ZMP': '0'}
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'The Ghost EmpireMUD'}
DEBUG stream_writer.py:773 recv IAC WILL MXP
DEBUG stream_writer.py:2045 handle_will(MXP)
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.01s.
DEBUG client_base.py:540 failed-reply: 'DO MCCP2_COMPRESS'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 51.161.5.210 4000>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b
tbaMUD (mud.theghostbox.com:4001)
Connection Banner:
![Attempting to Detect Client, Please Wait... [Client] xterm-256color \| [Colors] 256 \| [MXP] Yes \| [MSDP] Yes \| [ATCP] Yes T B A M U D 2 0 2 1 Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt, Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer By what name do you wish to be known?](../_images/banner_df4023bc5efb.png)
This banner is more than 99% similar to 2 other servers:
🇩🇪 timeslost.duckdns.org:4000 (100% match)
🇺🇸 173.230.135.147:4000 (99% match)
Server URLs
Server Info
Players online: 0 [2]
Uptime: 13 days
Server Location: 🇨🇦 Canada (GeoIP)
Protocol Support
MUD-specific protocols detected via MSSP flags or Telnet negotiation.
MSSP: Yes (MSSP)
GMCP: No
MSDP: Negotiated
MCCP: No
MCCP2: No
MXP: Negotiated
MSP: Negotiated
MCP: No
ZMP: No
Telnet Fingerprint
This fingerprint is shared by 57 other servers.
Options requested from client: ATCP, CHARSET, MXP, NAWS, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "2d1d3bcf28abae7b",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"ATCP",
"CHARSET",
"MXP",
"NAWS",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"atcp": [
{
"package": "MSDP.SERVER_ID",
"value": "tbaMUD"
}
],
"banner_after_return": "",
"banner_before_return": "\r\nAttempting to Detect Client, Please Wait...\r\n\u001b[7z\u001b[7z\r\n\u001b[H\u001b[J\u001b[38;5;214m[\u001b[38;5;208mClient\u001b[38;5;214m] \u001b[38;5;145mxterm-256color\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mColors\u001b[38;5;214m] \u001b[38;5;145m256\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMXP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mMSDP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m | \u001b[38;5;214m[\u001b[38;5;208mATCP\u001b[38;5;214m] \u001b[38;5;145mYes\u001b[0;00m\r\n\r\n T B A M U D\r\n 2 0 2 1 \r\n\r\n Based on CircleMUD by Jeremy Elson and DikuMUD by Hans-Henrik Staerfeldt,\r\n Katja Nyboe, Tom Madsen, Michael Seifert, and Sebastian Hammer\r\n\r\nBy what name do you wish to be known? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"mssp": {
"CRAWL DELAY": "-1",
"NAME": "tbaMUD",
"PLAYERS": "0",
"UPTIME": "1774418972"
},
"mxp": [
"activated",
"activated"
],
"option_states": {
"server_offered": {
"MSDP": true,
"MSP": true,
"MSSP": true
},
"server_requested": {
"ATCP": true,
"CHARSET": true,
"MXP": true,
"NAWS": true,
"TTYPE": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.660692453384399
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:03:57.675292+00:00",
"host": "mud.theghostbox.com",
"ip": "51.161.5.210",
"port": 4001
},
{
"connected": "2026-04-07T07:03:18.178356+00:00",
"host": "mud.theghostbox.com",
"ip": "51.161.5.210",
"port": 4001
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug mud.theghostbox.com 4001
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=mud.theghostbox.com port=4001
INFO client_base.py:190 Connected to <Peer 51.161.5.210 4001>
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB ATCP
DEBUG stream_writer.py:754 sub-negotiation cmd ATCP SE completion byte
DEBUG stream_writer.py:2238 [SB + ATCP] unsolicited
DEBUG stream_writer.py:1820 ATCP: MSDP.SERVER_ID 'tbaMUD'
DEBUG stream_writer.py:767 begin sub-negotiation SB MXP
DEBUG stream_writer.py:754 sub-negotiation cmd MXP SE completion byte
DEBUG stream_writer.py:2238 [SB + MXP] unsolicited
DEBUG stream_writer.py:1805 MXP: b''
DEBUG stream_writer.py:767 begin sub-negotiation SB MSSP
DEBUG stream_writer.py:754 sub-negotiation cmd MSSP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSSP] unsolicited
DEBUG stream_writer.py:1796 MSSP: {'NAME': 'tbaMUD', 'PLAYERS': '0', 'UPTIME': '1774418972', 'CRAWL DELAY': '-1'}
DEBUG stream_writer.py:767 begin sub-negotiation SB MSDP
DEBUG stream_writer.py:754 sub-negotiation cmd MSDP SE completion byte
DEBUG stream_writer.py:2238 [SB + MSDP] unsolicited
DEBUG stream_writer.py:1792 MSDP: {'SERVER_ID': 'tbaMUD'}
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO CHARSET
DEBUG stream_writer.py:1887 handle_do(CHARSET)
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC WILL CHARSET
DEBUG stream_writer.py:3384 local_option[CHARSET] = True
DEBUG stream_writer.py:3384 pending_option[WILL + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WILL MSDP
DEBUG stream_writer.py:2045 handle_will(MSDP)
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSDP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSSP
DEBUG stream_writer.py:2045 handle_will(MSSP)
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC DO ATCP
DEBUG stream_writer.py:1887 handle_do(ATCP)
DEBUG stream_writer.py:998 skip WILL ATCP; pending_option = True
DEBUG stream_writer.py:3384 local_option[ATCP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WILL MSP
DEBUG stream_writer.py:2045 handle_will(MSP)
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:3384 remote_option[MSP] = True
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC DO MXP
DEBUG stream_writer.py:1887 handle_do(MXP)
DEBUG stream_writer.py:998 skip WILL MXP; pending_option = True
DEBUG stream_writer.py:3384 local_option[MXP] = True
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:2238 [SB + TTYPE] unsolicited
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG stream_writer.py:767 begin sub-negotiation SB CHARSET
DEBUG stream_writer.py:754 sub-negotiation cmd CHARSET SE completion byte
DEBUG stream_writer.py:2238 [SB + CHARSET] unsolicited
DEBUG client.py:376 encoding negotiated: UTF-8
DEBUG stream_writer.py:2321 send IAC SB CHARSET ACCEPTED UTF-8 IAC SE
DEBUG client_base.py:534 negotiation failed after 4.00s.
DEBUG client_base.py:540 failed-reply: 'WILL MCCP2_COMPRESS, WILL ZMP, WILL MSP, WILL AARDWOLF, WILL MCCP3_COMPRESS, WILL GMCP,
WILL MSSP, WILL MSDP, DO MCCP2_COMPRESS, DO ZMP, DO AARDWOLF, DO MXP, DO MCCP3_COMPRESS, DO GMCP, DO ATCP'
DEBUG client_base.py:93 EOF from server, closing.
INFO client_base.py:122 Connection closed to <Peer 51.161.5.210 4001>
DEBUG fingerprinting.py:849 connection for server fingerprint 2d1d3bcf28abae7b