67.224.119.26 (halcyon.bluecows.com)
halcyon.bluecows.com:4201
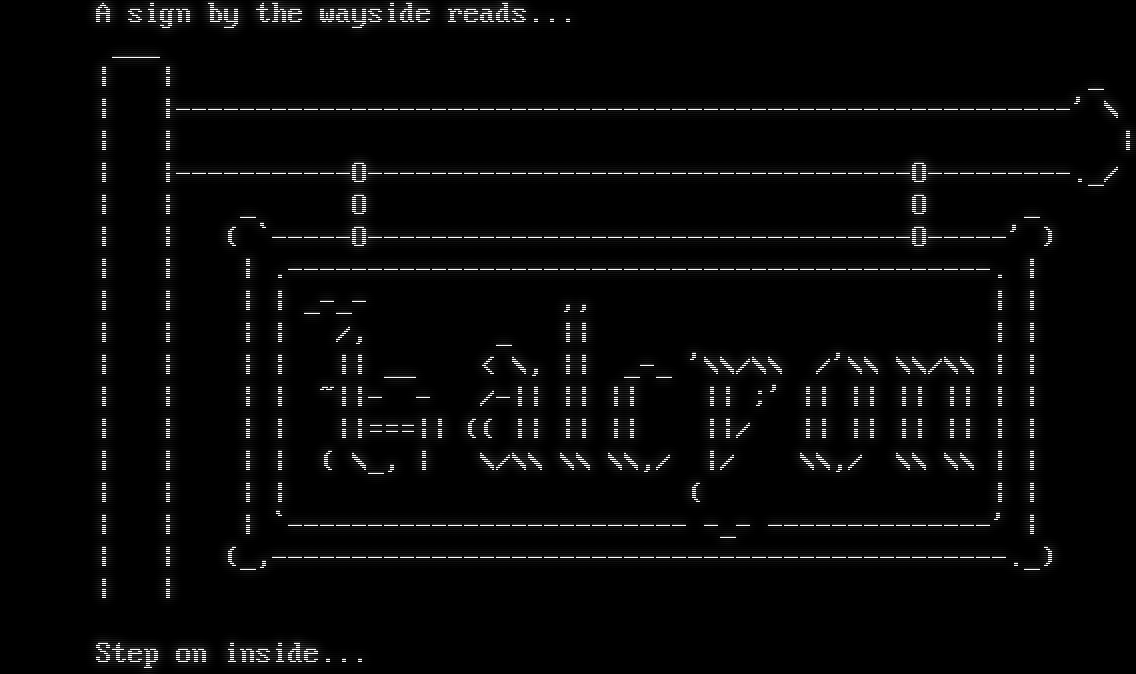
Connection Banner:
Server URLs
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 219 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "a8a260cc4662430c",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " A sign by the wayside reads... \r\n ___\r\n | | _\r\n | |--------------------------------------------------------' \\\r\n | | |\r\n | |-----------O----------------------------------O---------._/\r\n | | _ O O _\r\n | | ( `-----O----------------------------------O-----' )\r\n | | | .--------------------------------------------. |\r\n | | | | _-_- ,, | |\r\n | | | | /, _ || | |\r\n | | | | || __ < \\, || _-_ '\\\\/\\\\ /'\\\\ \\\\/\\\\ | |\r\n | | | | ~||- - /-|| || || || ;' || || || || | |\r\n | | | | ||===|| (( || || || ||/ || || || || | |\r\n | | | | ( \\_, | \\/\\\\ \\\\ \\\\,/ |/ \\\\,/ \\\\ \\\\ | |\r\n | | | | ( | |\r\n | | | `------------------------- -_- --------------' |\r\n | | (_,----------------------------------------------._)\r\n | |\r\n\r\n Step on inside...\r\n\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.505185604095459,
"total": 5.014549970626831
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:33.175063+00:00",
"host": "halcyon.bluecows.com",
"ip": "67.224.119.26",
"port": 4201
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug halcyon.bluecows.com 4201
Show Logfile
DEBUG client.py:965 Fingerprint client: host=halcyon.bluecows.com port=4201
INFO client_base.py:175 Connected to <Peer 67.224.119.26 4201>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
INFO fingerprinting.py:746 connection for server fingerprint a8a260cc4662430c
INFO client_base.py:106 Connection closed to <Peer 67.224.119.26 4201>
holomuck.org:5757
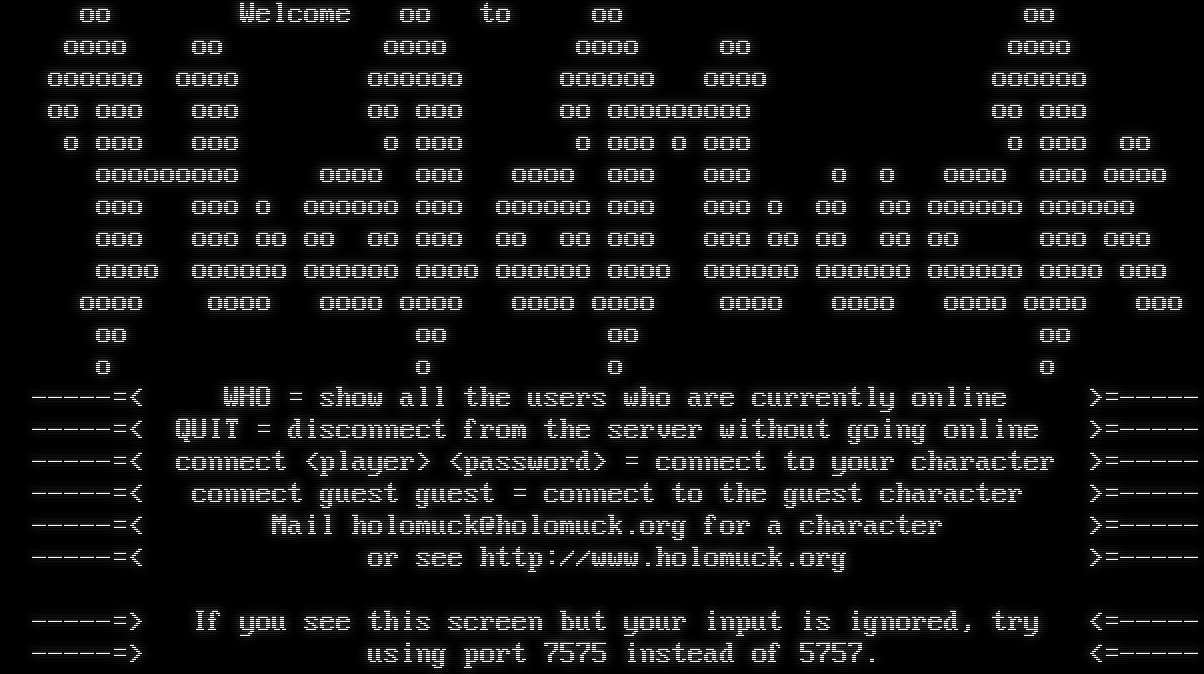
Connection Banner:
Server URLs
- Telnet: telnet://holomuck.org:5757
- Website: holomuck.org
Server Info
Server Location: 🇺🇸 United States (GeoIP)
Telnet Fingerprint
This fingerprint is shared by 219 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and any MSSP metadata.
Show JSON
{
"server-probe": {
"fingerprint": "a8a260cc4662430c",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": " oo Welcome oo to oo oo\r\n oooo oo oooo oooo oo oooo\r\n oooooo oooo oooooo oooooo oooo oooooo\r\n oo ooo ooo oo ooo oo ooooooooo oo ooo\r\n o ooo ooo o ooo o ooo o ooo o ooo oo\r\n ooooooooo oooo ooo oooo ooo ooo o o oooo ooo oooo\r\n ooo ooo o oooooo ooo oooooo ooo ooo o oo oo oooooo oooooo\r\n ooo ooo oo oo oo ooo oo oo ooo ooo oo oo oo oo ooo ooo\r\n oooo oooooo oooooo oooo oooooo oooo oooooo oooooo oooooo oooo ooo\r\n oooo oooo oooo oooo oooo oooo oooo oooo oooo oooo ooo\r\n oo oo oo oo\r\n o o o o\r\n -----=< WHO = show all the users who are currently online >=----- \r\n -----=< QUIT = disconnect from the server without going online >=-----\r\n -----=< connect <player> <password> = connect to your character >=-----\r\n -----=< connect guest guest = connect to the guest character >=-----\r\n -----=< Mail holomuck@holomuck.org for a character >=-----\r\n -----=< or see http://www.holomuck.org >=-----\r\n\r\n -----=> If you see this screen but your input is ignored, try <=-----\r\n -----=> using port 7575 instead of 5757. <=-----\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5180416107177734,
"total": 5.029497385025024
}
}
},
"sessions": [
{
"connected": "2026-02-14T17:12:36.406921+00:00",
"host": "holomuck.org",
"ip": "67.224.119.26",
"port": 5757
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug holomuck.org 5757
Show Logfile
DEBUG client.py:965 Fingerprint client: host=holomuck.org port=5757
INFO client_base.py:175 Connected to <Peer 67.224.119.26 5757>
DEBUG client_base.py:492 negotiation complete after 0.00s.
DEBUG stream_writer.py:3174 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:950 send IAC DO BINARY
DEBUG stream_writer.py:3174 pending_option[DO + SGA] = True
DEBUG stream_writer.py:950 send IAC DO SGA
DEBUG stream_writer.py:3174 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:950 send IAC DO ECHO
DEBUG stream_writer.py:3174 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:950 send IAC DO STATUS
DEBUG stream_writer.py:3174 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:950 send IAC DO CHARSET
DEBUG stream_writer.py:3174 pending_option[DO + EOR] = True
DEBUG stream_writer.py:950 send IAC DO EOR
DEBUG stream_writer.py:3174 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:950 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:3174 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:950 send IAC DO GMCP
DEBUG stream_writer.py:3174 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:950 send IAC DO MSDP
DEBUG stream_writer.py:3174 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:950 send IAC DO MSSP
DEBUG stream_writer.py:3174 pending_option[DO + MSP] = True
DEBUG stream_writer.py:950 send IAC DO MSP
DEBUG stream_writer.py:3174 pending_option[DO + MXP] = True
DEBUG stream_writer.py:950 send IAC DO MXP
DEBUG stream_writer.py:3174 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:950 send IAC DO ZMP
DEBUG stream_writer.py:3174 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:950 send IAC DO AARDWOLF
DEBUG stream_writer.py:3174 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:950 send IAC DO ATCP
INFO fingerprinting.py:746 connection for server fingerprint a8a260cc4662430c
INFO client_base.py:106 Connection closed to <Peer 67.224.119.26 5757>